漏洞概要
关注数(24)
关注此漏洞
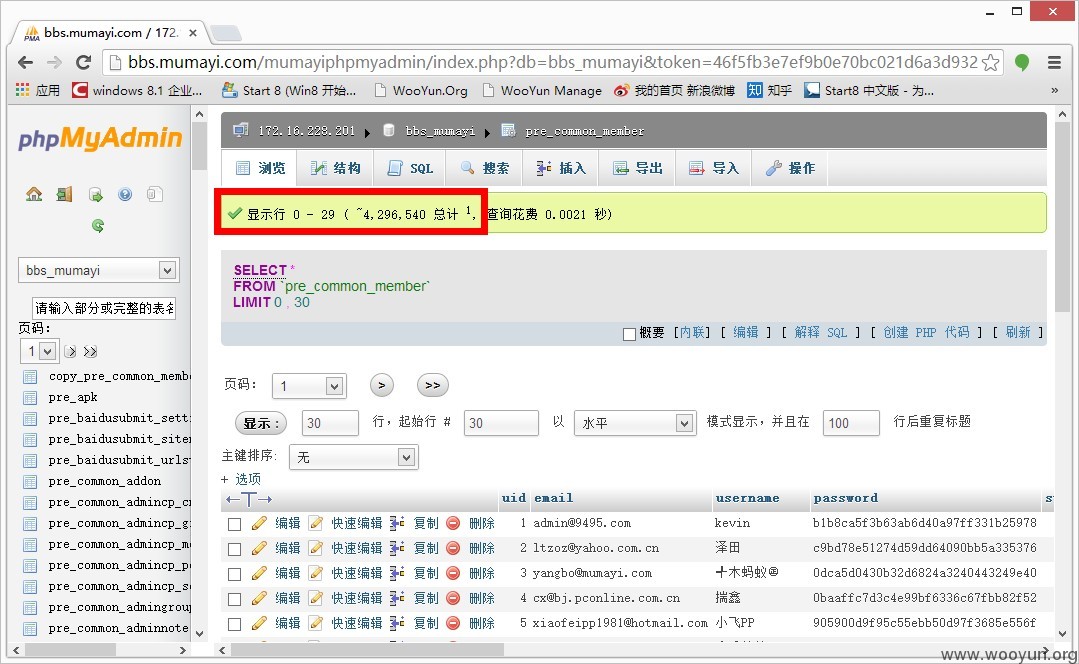
漏洞标题:敏感信息泄露系列#7 信息泄露导致木蚂蚁450万用户信息告急
提交时间:2013-11-07 01:55
修复时间:2013-12-22 01:56
公开时间:2013-12-22 01:56
漏洞类型:重要敏感信息泄露
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2013-11-07: 细节已通知厂商并且等待厂商处理中
2013-11-07: 厂商已经确认,细节仅向厂商公开
2013-11-17: 细节向核心白帽子及相关领域专家公开
2013-11-27: 细节向普通白帽子公开
2013-12-07: 细节向实习白帽子公开
2013-12-22: 细节向公众公开
简要描述:
由于没有一个通用标准的防御规则保护好中间件配置信息、DNS信息、业务数据信息、用户信息、源码备份文件、版本管理工具信息、系统错误信息和敏感地址信息(后台或测试地址)的泄露,攻击者可能会通过收集这些保护不足的数据,利用这些信息对系统实施进一步的攻击。
详细说明:
#1 信息泄露原因
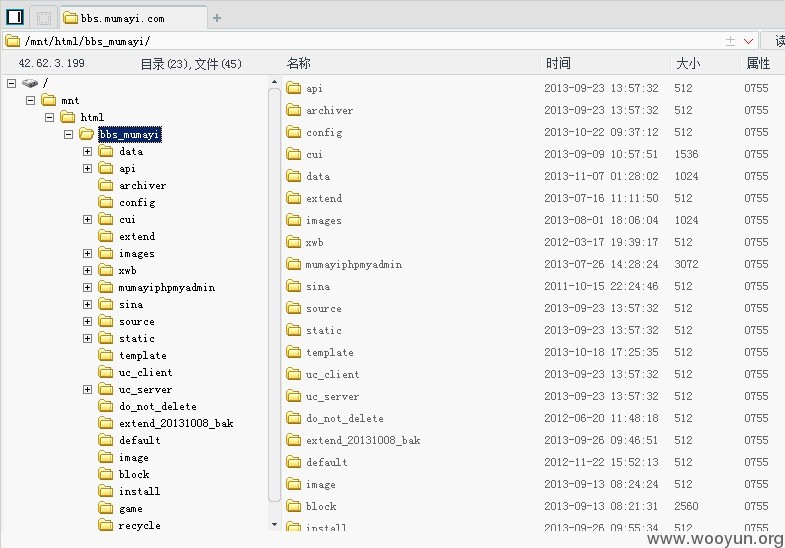
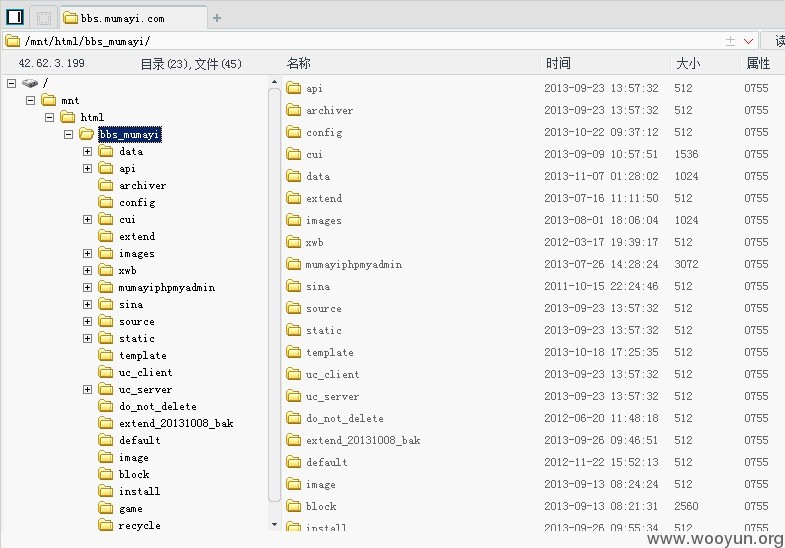
由于木蚂蚁论坛管理员在更新服务器文件时,未注意到编辑器会默认创建各种.bak文件用来规避错误编辑时引发的数据丢失风险,从而造成了更严重的信息安全问题。
同时使用了第三方数据库管理软件时,未能安全的隐藏路径,导致各种信息泄露被骇客组合,从而利用这些信息对系统实施攻击。
#2 泄露内容
网站:http://bbs.mumayi.com
泄露文件:http://bbs.mumayi.com/config/config_global.php.bak
PHPMYADMIN地址泄露:http://bbs.mumayi.com/{domain_name}phpmyadmin/
漏洞证明:
#3 风险利用
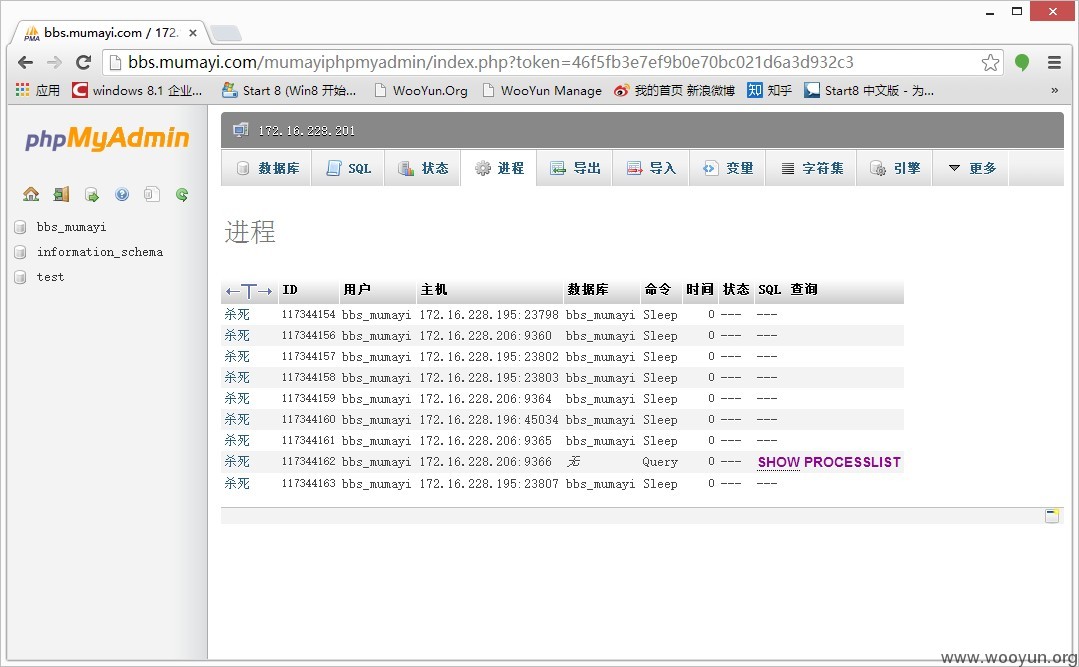
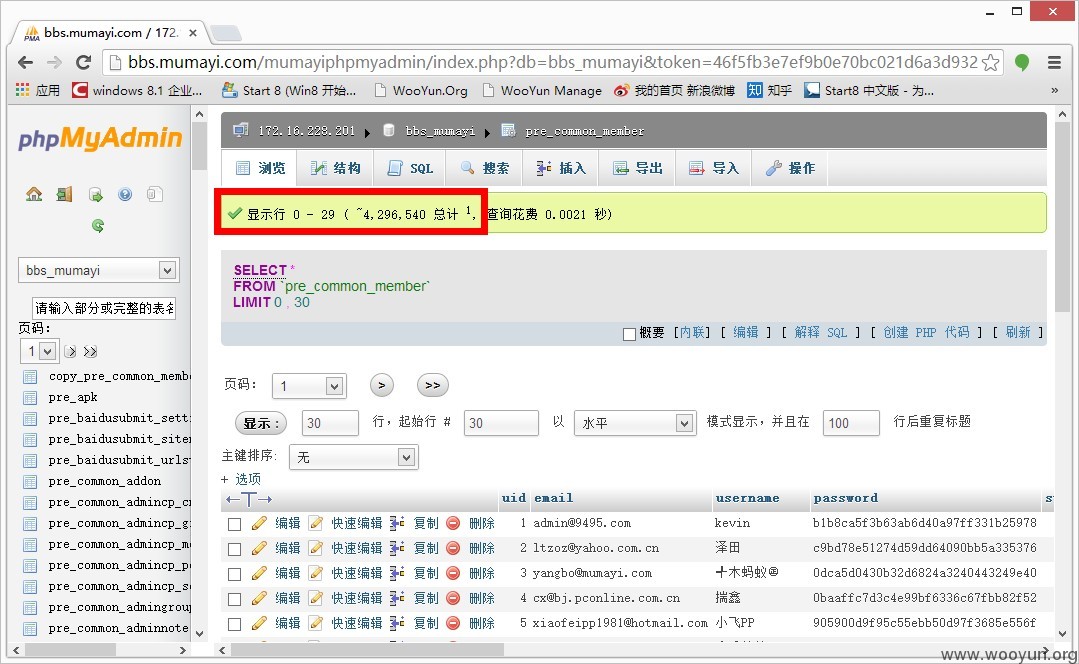
通过泄露的信息,结合PHPMYADMIN,刚好可访问到木蚂蚁的用户数据信息!
{没办法得到SHELL的风险都不算漏洞,测试后已删除}
修复方案:
#1 网络边界需要认真对待。
#2 杜绝为了方便而造成的不必要的信息泄露。
#3 安全是一个整体,保证安全不在于强大的地方有多强大,而在于真正薄弱的地方在哪里。
版权声明:转载请注明来源 猪猪侠@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2013-11-07 03:27
厂商回复:
立即对该文件进行了安全处理,确实是工作不够严谨导致,感谢漏洞发现者
最新状态:
暂无