#1 一个越权 /e/master/build_static.aspx
#2 注入点
其中Table参数可构造:
且会产生错误回显:
#3 构造请求可得到login_key(见POC),鉴权cookie中的valicate由以下代码生成,且LoginKey被存入数据库login_key字段:
#4 利用本地pageadmin环境进行login_key的加密:
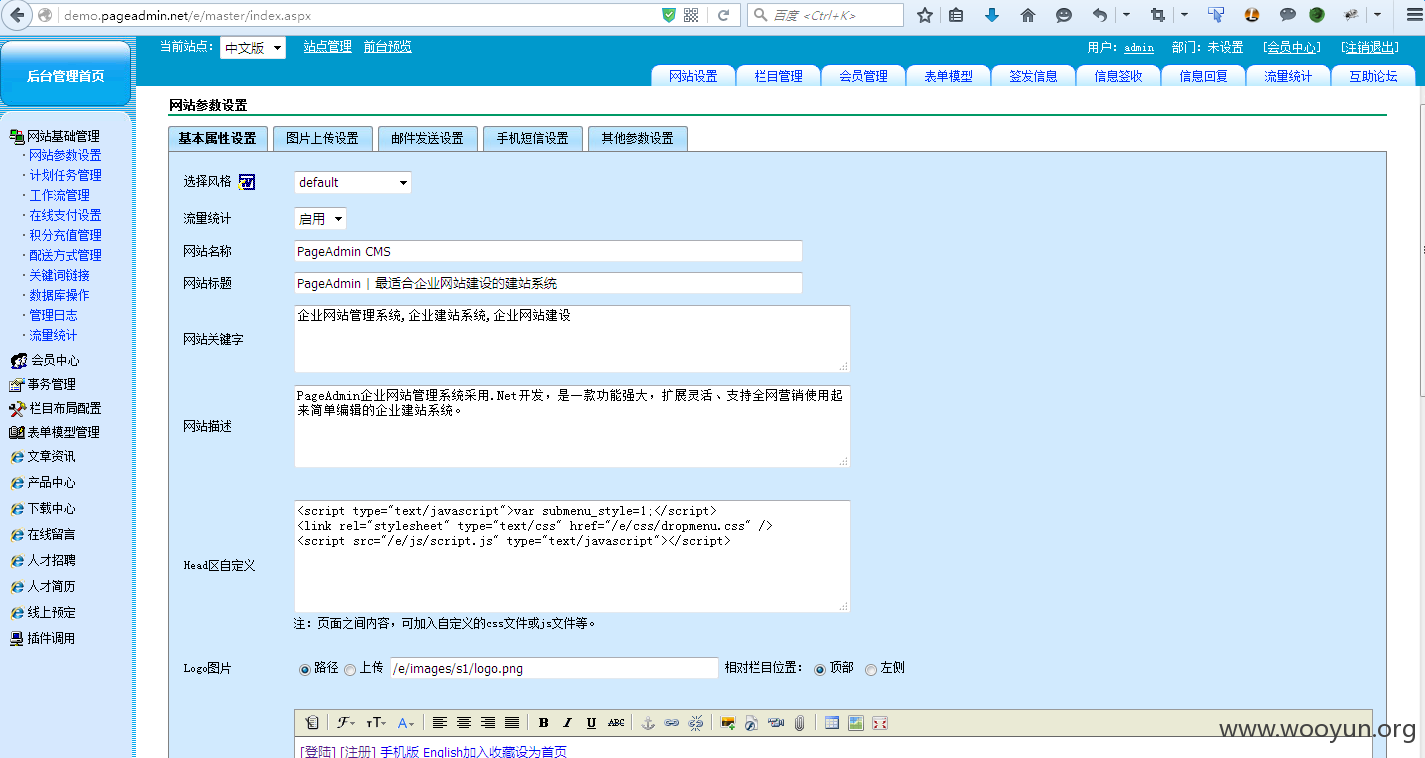
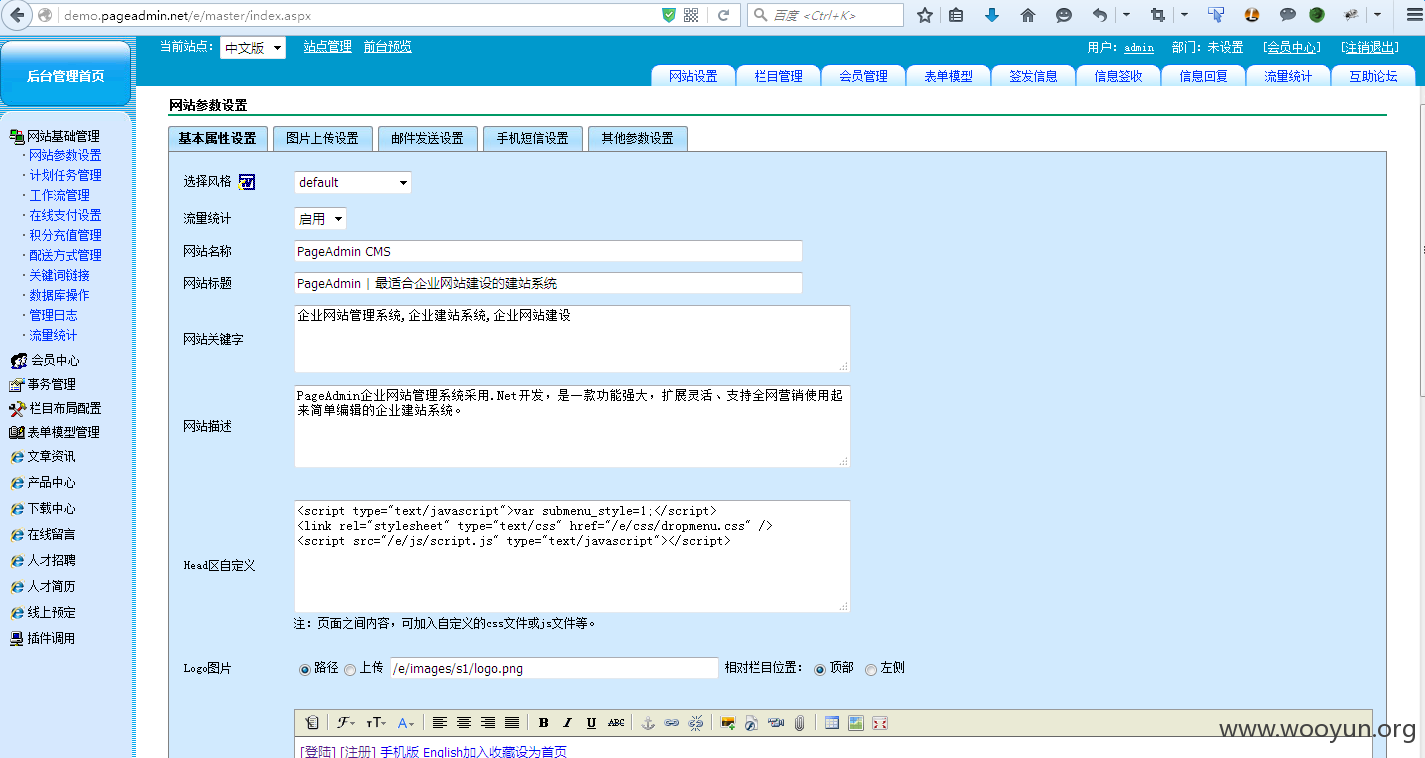
#5伪造cookie即可进入后台
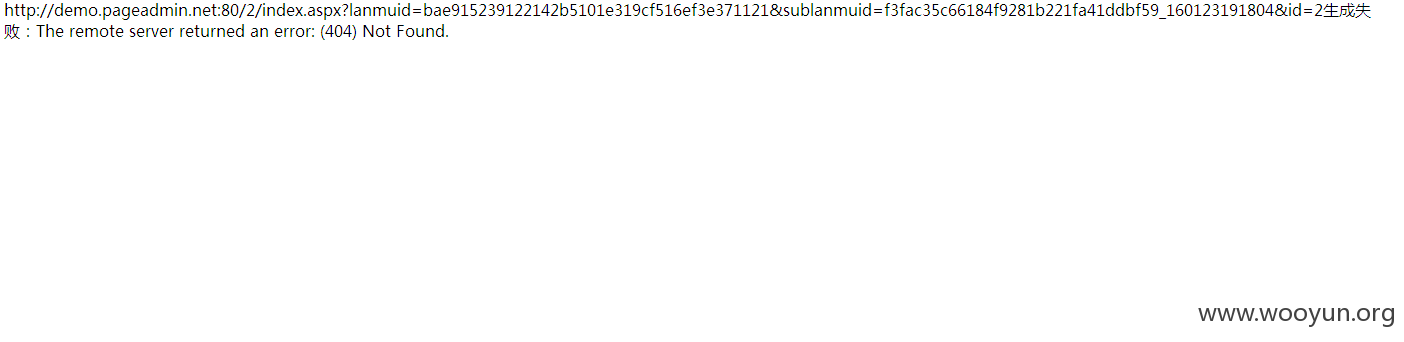
#1使用poc获取报错
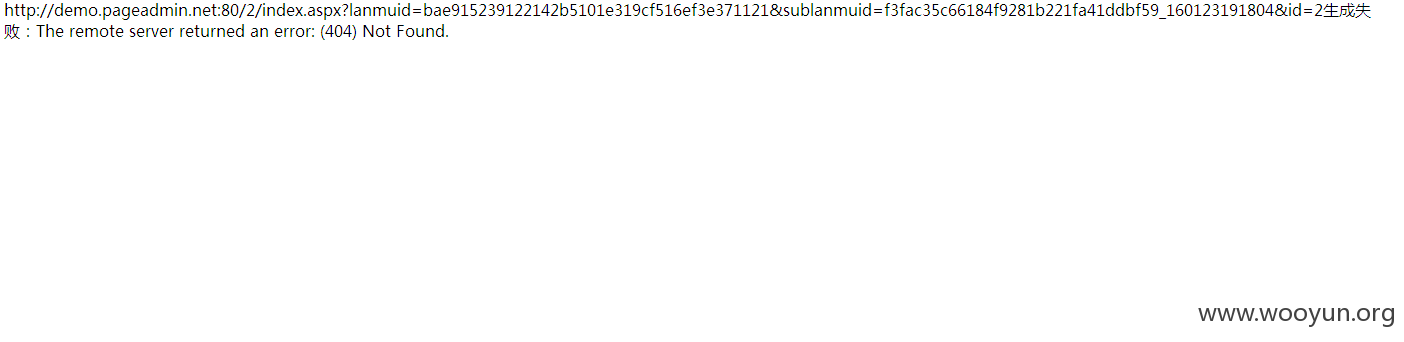
其中sublanmuid的值为login_key,lanmuid的值为密码
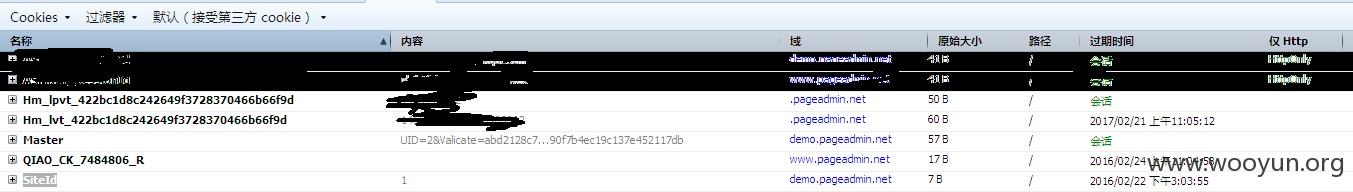
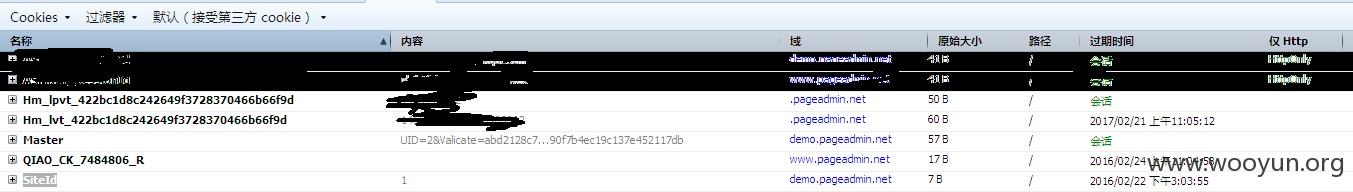
#2得到加密后的valicate
abd2128c766f990f7b4ec19c137e452117db
#3伪造cookie进入后台