漏洞概要
关注数(24)
关注此漏洞
漏洞标题:腾讯某服务配置不当导致包括数据库文件、密码hash等任意文件可下载
相关厂商:腾讯
提交时间:2015-01-16 08:53
修复时间:2015-03-02 08:54
公开时间:2015-03-02 08:54
漏洞类型:系统/服务运维配置不当
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-01-16: 细节已通知厂商并且等待厂商处理中
2015-01-16: 厂商已经确认,细节仅向厂商公开
2015-01-26: 细节向核心白帽子及相关领域专家公开
2015-02-05: 细节向普通白帽子公开
2015-02-15: 细节向实习白帽子公开
2015-03-02: 细节向公众公开
简要描述:
RT
详细说明:
http://183.60.76.243:8003/root/.bash_history 可下载
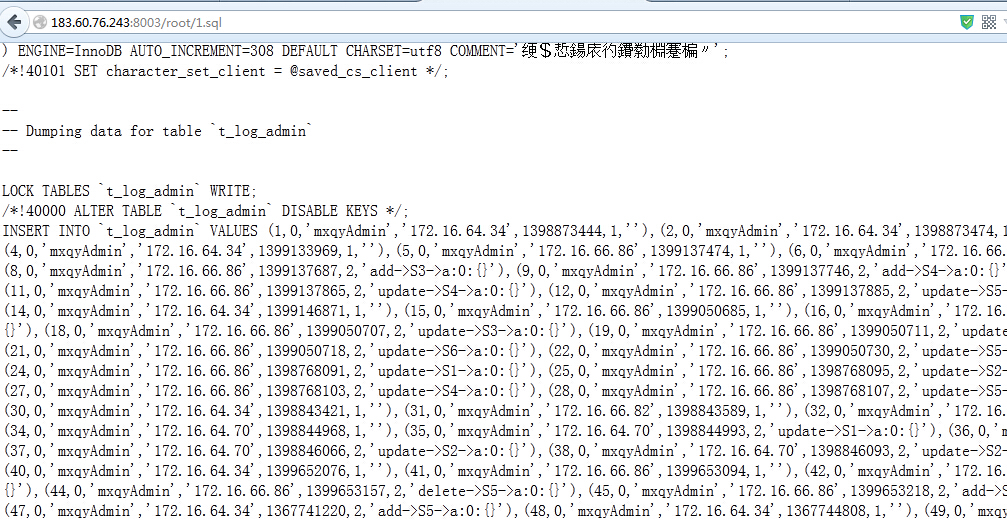
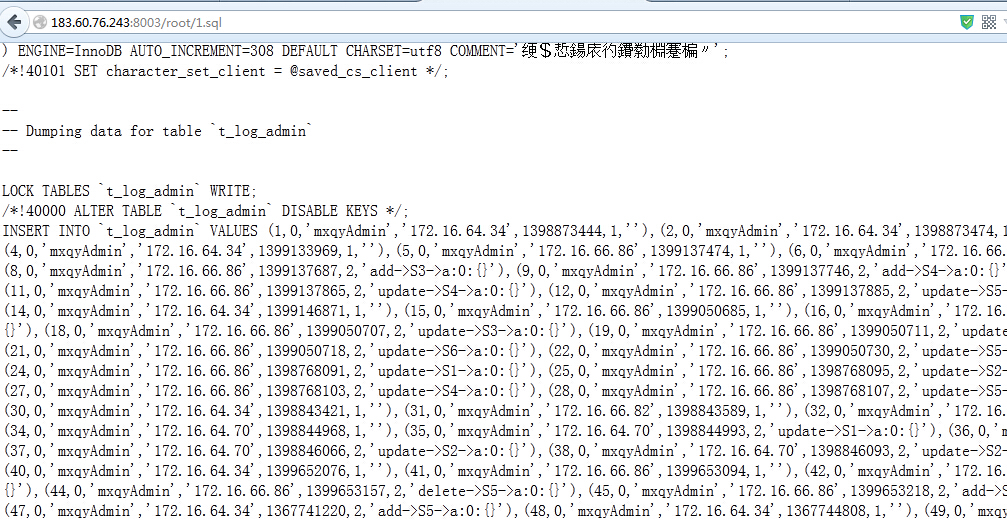
http://183.60.76.243:8003/root/1.sql 数据库备份文件
漏洞证明:
http://183.60.76.243:8003/root/.bash_history 可下载
http://183.60.76.243:8003/root/1.sql 数据库备份文件
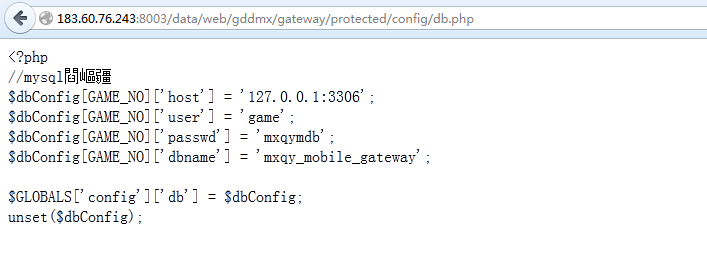
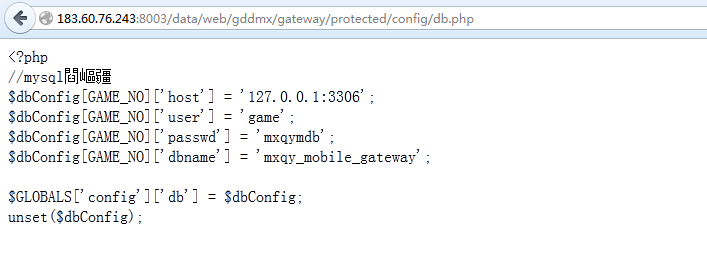
http://183.60.76.243:8003/data/web/gddmx/gateway/protected/config/db.php
数据库配置
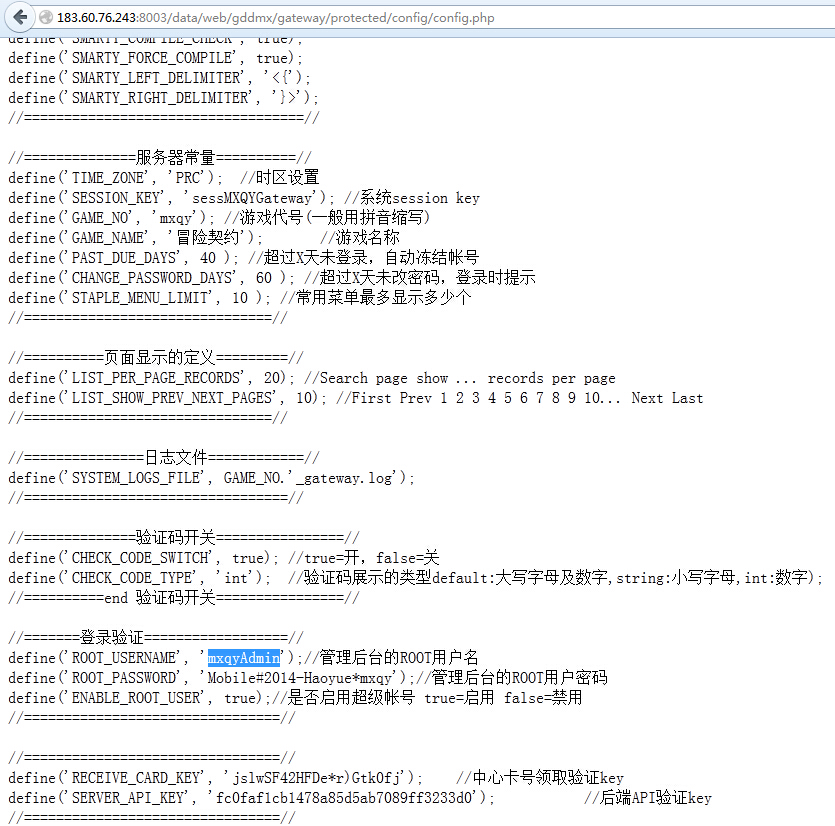
管理后台配置
http://183.60.76.243:8003/data/web/gddmx/gateway/protected/config/config.php
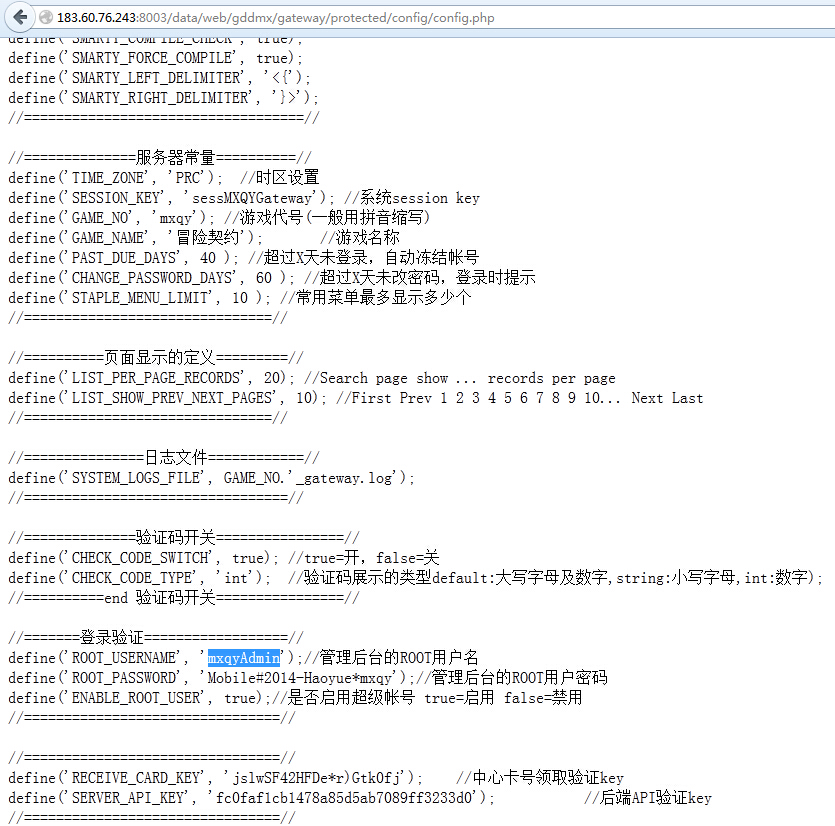
获取密码登陆后台

下载代码包
183.60.76.243:8003/data/server/trunk/code201501082218.tar.gz
等等,不搞了
修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-01-16 16:43
厂商回复:
非常感谢您的报告。这个问题我们已经确认,正在与业务部门进行沟通制定解决方案。如有任何新的进展我们将会及时同步。
最新状态:
暂无