WooYun: Youyax V5.4.1 注入 (可修改其他用户的密码)#4
下个最新的程序来看看官方是怎么修补的。
可以看到是把$face进行了addslashes一次 转义后这里就不能注入了。
然后入库。
50个字符 足够了。
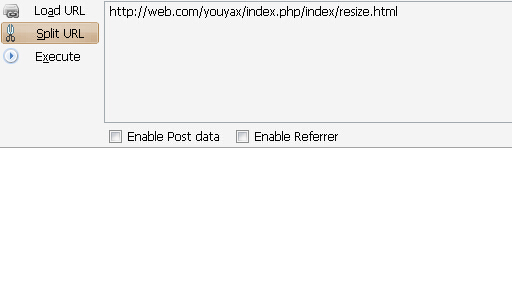
出库导致的任意文件删除。
在lib/indexaction.php中
这里$filename 是不可控的, $oldface2 出库来的 可控。
所以
要进这里
所以来让$oldface2 能匹配出/upload/ 就能进这个unlink。
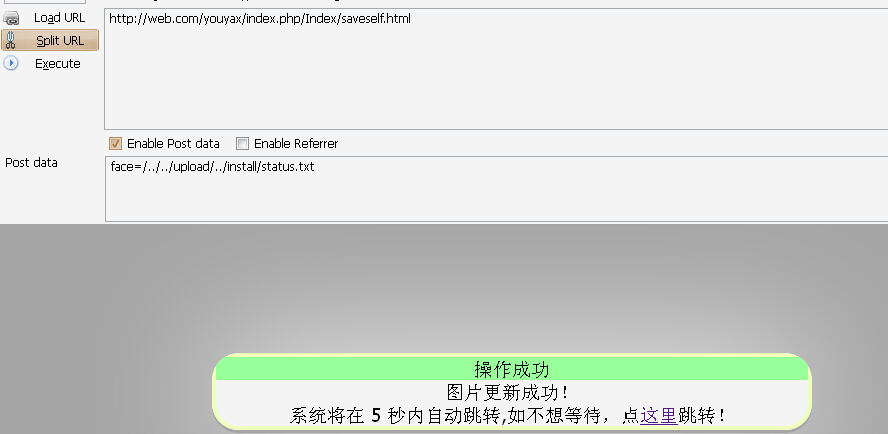
构造一下/../../upload/../install/status.txt