漏洞概要
关注数(24)
关注此漏洞
漏洞标题:土豆网某站sql注射及后台弱口令
漏洞作者: 卡卡
提交时间:2014-06-06 10:31
修复时间:2014-07-23 21:14
公开时间:2014-07-23 21:14
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2014-06-06: 细节已通知厂商并且等待厂商处理中
2014-06-06: 厂商已经确认,细节仅向厂商公开
2014-06-16: 细节向核心白帽子及相关领域专家公开
2014-06-26: 细节向普通白帽子公开
2014-07-06: 细节向实习白帽子公开
2014-07-23: 细节向公众公开
简要描述:
从前有三个男人要过河、河里有一个吃JJ的鳄鱼,但是路边只有一个瓶子,请问他们是怎么过去的?
详细说明:
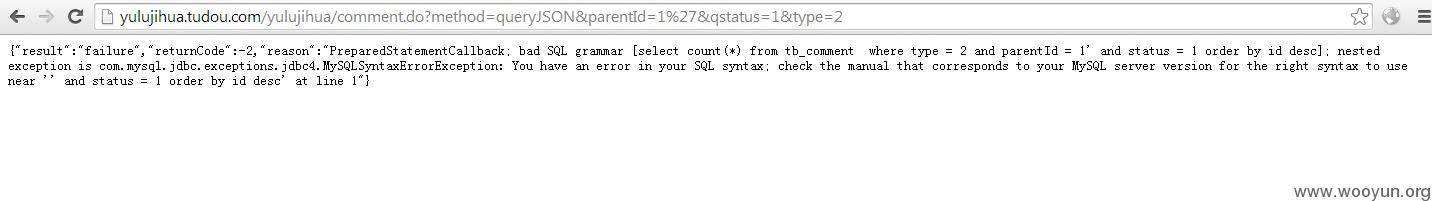
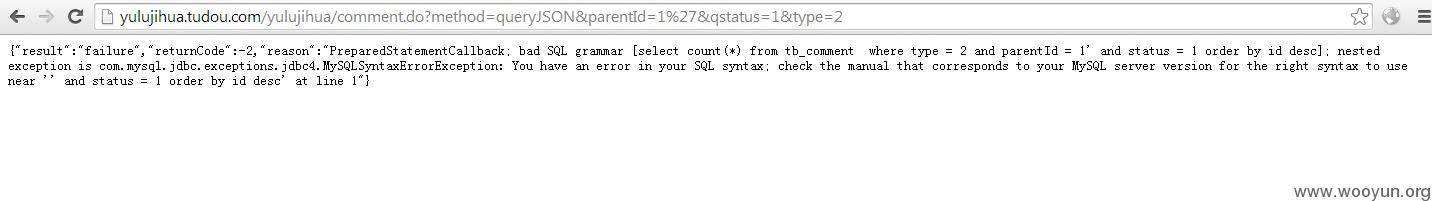
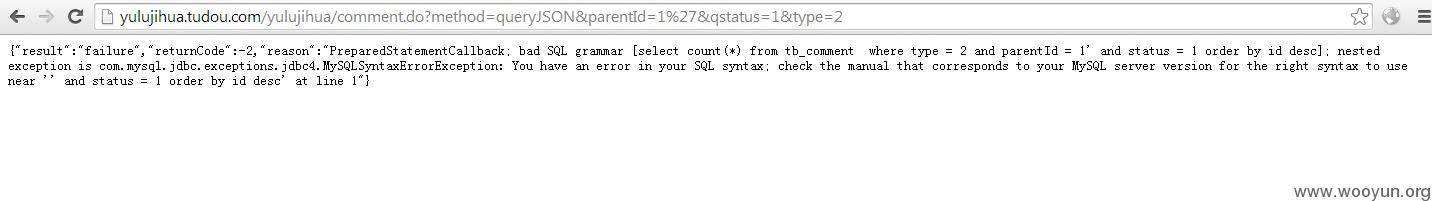
漏洞链接:
由于对参数parentId未过滤,造成sql注射
涉及88个库啊亲~而且可以跨库
只是检测,我就没继续下去了
后台弱口令:
账号密码 admin admin

漏洞证明:
库
后台弱口令:
账号密码 admin admin

修复方案:
版权声明:转载请注明来源 卡卡@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-06-06 14:33
厂商回复:
外包项目防不胜防,赞一个简要描述。
最新状态:
暂无