漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2011-01630
漏洞标题:PIPI播放器溢出漏洞
相关厂商:皮皮网
漏洞作者: 冰雪风谷[NNU
提交时间:2011-03-17 17:39
修复时间:2011-03-22 18:00
公开时间:2011-03-22 18:00
漏洞类型:远程代码执行
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2011-03-17: 细节已通知厂商并且等待厂商处理中
2011-03-22: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
皮皮播放器在处理用户输入的URL时,没有对其长度进行检测,从而造成溢出
详细说明:
皮皮播放器在处理用户输入的URL时,没有对其进行长度检测。
从而造成溢出。
不过,由于有GS,利用的时候有些困难
//////////////////////////////////////////////////////////////
对传入的url没有进行检测,直接调用sprintf(&CommandLine, "%s%s \"%s\"", dword_48AF30, "jfCacheMgr.exe", v32);
函数,然后把url的值赋给CommandLine值,从而造成溢出。
我们可以看到,在函数开始的地方,
text:00430C20 push ebp
.text:00430C21 mov ebp, esp
.text:00430C23 and esp, 0FFFFFFF8h
.text:00430C26 push 0FFFFFFFFh
.text:00430C28 push offset SEH_430C20
.text:00430C2D mov eax, large fs:0
.text:00430C33 push eax
.text:00430C34 mov large fs:0, esp
.text:00430C3B sub esp, 5F8h
//一共分配了0x5F8大小的栈。
漏洞证明:
我们构造如下URL:
“ppfilm://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA”
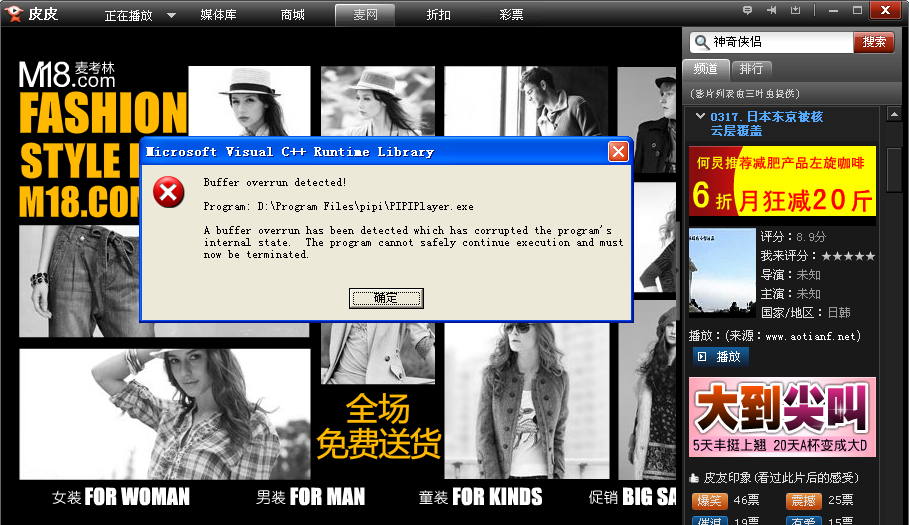
在皮皮播放器处点击,播放URL,将其输入,可以看到如下图:
修复方案:
对用户输入的URL进行长度限制
版权声明:转载请注明来源 冰雪风谷[NNU@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2011-03-22 18:00
厂商回复:
漏洞Rank:12 (WooYun评价)
最新状态:
暂无